News
A password generator is an online tool that automatically creates strong, random passwords at the click of a button. To create unique passwords, a password generator combines a variety of uppercase and lowercase letters, numbers and symbols. Password generators dramatically ease the process of creating strong passwords by automatically producing random, lengthy ones – two qualities that make passwords more challenging for cybercriminals to crack.
Keep reading to learn why you should use a password generator and how you can use it to strengthen your online security.
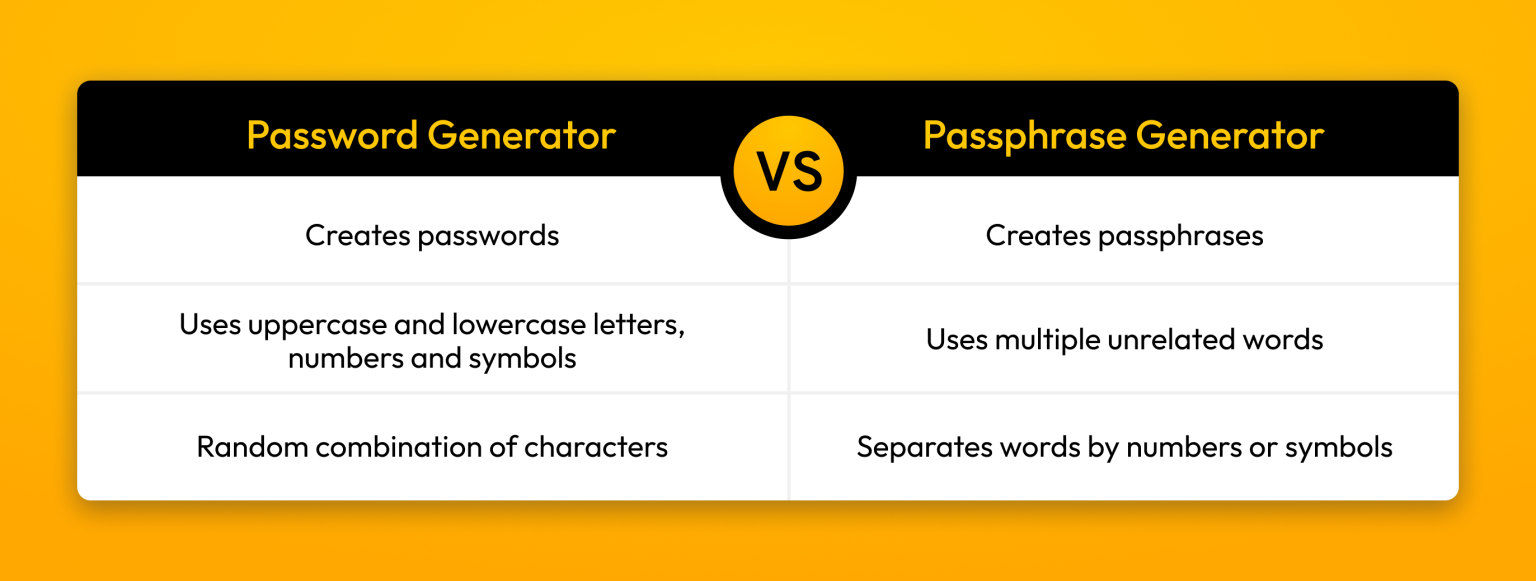
Password vs passphrase generator: What’s the difference?
The main difference between a password generator and a passphrase generator is that a password generator creates a password, while a passphrase generator creates a passphrase. Password generators create strong passwords, which contain at least 16 characters, including uppercase and lowercase letters, numbers and symbols. For example, this would be a strong password produced by a password generator: B^F<>8=>56qXUQCkhN?$.
A passphrase is a combination of words separated by numbers or symbols that are used as a password. Therefore, a passphrase generator produces multiple unrelated words, making passphrases more difficult for cybercriminals to crack. An example of a strong passphrase created with a passphrase generator could look something like this: Leaf-Banana0-Joy_Friend4-Sunlight.
Why use a password generator?
You should use a password generator because it guarantees strong and unique passwords, eliminates the chances of using weak or reused passwords and makes updating your passwords convenient.
It ensures your passwords are always strong
Password generators naturally create strong passwords by randomly combining letters, numbers and symbols. This random combination of characters contributes to the strength and uniqueness of any password you create with a password generator. Strong passwords are essential in reducing your chances of a cybercriminal hacking into your online accounts, which, in turn, minimizes your risk of becoming a victim of fraud or identity theft.
You don’t have to rely on yourself to create passwords
Maybe you believe that you can come up with strong passwords on your own just fine. However, a recent study commissioned by Keeper® found that 41% of people admit to reusing the same password across multiple accounts. Password generators eliminate dangerous human tendencies by creating passwords that are completely random and unrelated to personal information, such as a pet’s name or birthdate. If you only rely on yourself to create strong and memorable passwords, you will likely start to reuse the same password or slight iterations of the same password on multiple accounts. Using weak or reused passwords increases the likelihood of a cybercriminal cracking your passwords and stealing your private information.
It makes changing your passwords easy
If you need to change your password following a data breach or hacking, using a password generator makes updating your passwords simpler while ensuring the new ones are secure. All you have to do is hit a button to receive a new, strong and random password that will be very difficult for a cybercriminal to crack. Rather than racking your brain to come up with a password you haven’t used before, a password generator makes this process quick and convenient.
It helps you avoid dictionary attacks
A dictionary attack targets passwords that use common words or phrases found in dictionaries. Since common words or phrases are easy for a cybercriminal to crack in a password, using a password generator combats dictionary attacks because your password will contain a random combination of letters, numbers and symbols rather than easy-to-guess words or phrases. If each of your passwords to your many online accounts is a 16-character password with unique letters, numbers and symbols, a cybercriminal will have a very difficult time cracking them.
How to use a password generator
You may be wondering how simple it is to use a password generator after hearing all its benefits. Follow the steps below to learn how you can use a password generator to create strong and unique passwords.
1. Find a secure password generator to use
Luckily, there are many free password generators you can use online to create passwords. However, you should consider the benefits of using a password manager with a built-in password generator, like Keeper Password Manager. Having a built-in password generator makes it easy to create or update passwords that are strong and unique. Then, you can save your randomly generated passwords directly in your Keeper Vault to ensure your passwords are encrypted and protected from cybercriminals.
2. Adjust the password generator settings
After finding the best password generator for you, you can customize its settings to fit a specific website or app’s password requirements. For example, if an online account requires your password to contain both uppercase and lowercase letters, at least two numbers and one symbol, you can adjust your password generator’s settings so it creates a password based on those criteria. An app might require your password to contain at least 16 characters, which means your password must contain a minimum of 16 letters, numbers and symbols combined. Regardless of what requirements a website or app may have for your password, you can change your password generator’s settings to suit your password needs.
3. Generate your strong password
Once you’ve set your password generator’s settings, you can create your random password. After the password generator produces a strong and unique password, you can either try to remember it or save it in a password vault. Saving your passwords in a password vault like Keeper ensures your passwords are protected and saves you the hassle of remembering the password. Keeper has an autofill feature that works on all devices and browsers, so the next time you need to input your password, Keeper will do it for you.
Generate strong, unique passwords with Keeper
Using a password generator is not only convenient but also safe for strengthening your passwords and protecting your private information. Keeper Password Manager’s built-in password generator is easy to use and eliminates the risk of using weak or reused passwords.
Start a free 30-day trial of Keeper Password Manager to experience the ease of a built-in password generator and a safe place to store your passwords.
Source: Keeper Security
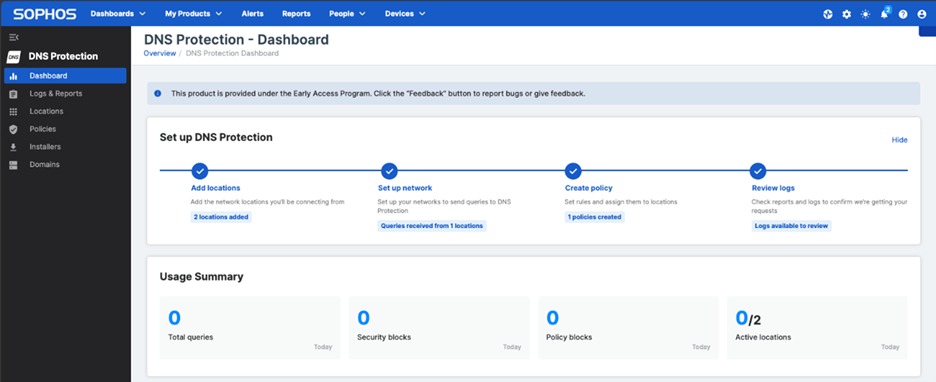
Sophos DNS Protection is now available for Sophos Firewall customers with Sophos Central accounts outside of the standard US and EU regions, adding five new management regions: Australia, Brazil, India, Japan, and Canada.
This matches similar regional expansions for other Sophos Central managed products including ZTNA, Sophos Switch, and our AP6 Wireless line. For a full list of Sophos Central products and which regions are supported, see this article.
If you currently manage Sophos Firewalls in one of these regions, you can now easily add Sophos DNS Protection to your account. Your Sophos Firewalls with Xstream Protection include DNS Protection at no extra charge (see below for how to get started).
Note that Sophos DNS Protection already provides a global network of DNS resolver points-of-presence (POPs) and DNS traffic is automatically directed to the nearest location using unicast routing technology to ensure the fastest response. This new release now enables management of DNS Protection from all Sophos Central locations as well.
Get started with Sophos DNS Protection
If you are a Sophos Firewall customer with Xstream Protection and are not already using Sophos DNS Protection, you can get started for free. Check out our online documentation and video resources.
Source: Sophos
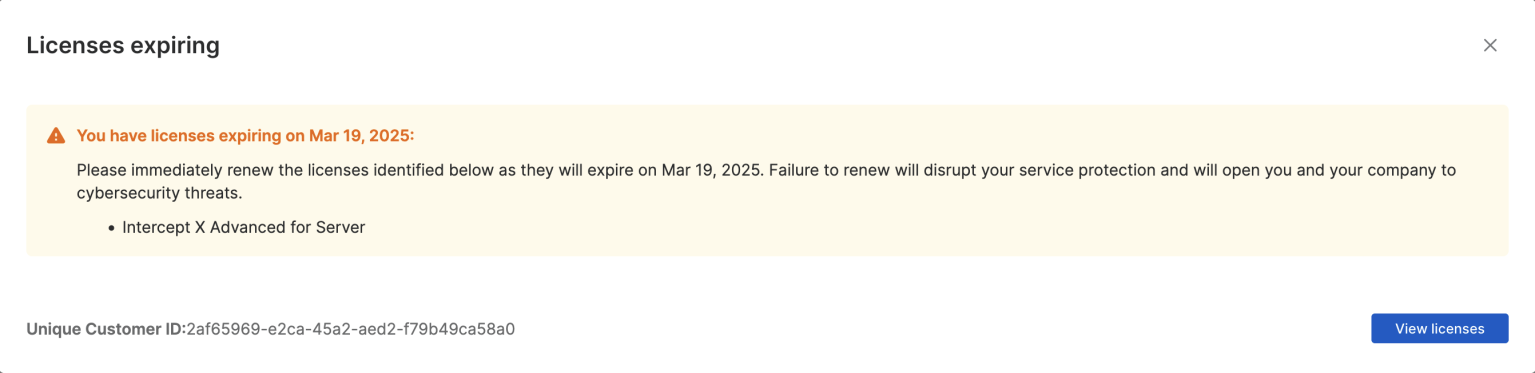
Juggling daily demands can make it difficult to keep up with the renewal dates on your Sophos subscriptions. To help you avoid any gaps in your protection, we are improving expiration alerts in Sophos Central so you can enjoy seamless protection against the latest threats.
What to expect?
30 days before your renewal date we will begin notifying you of your upcoming license expiration when you log-in to Sophos Central. Expect to see a pop-up message like the image above that shows:
- Which license(s) are due for renewal
- The license expiry date(s)
Select “View licenses” to go to the “Licensing” page where you can apply a new license key, access your partner’s contact details, find additional contact information, or dismiss the notification for that log-in session. The messages will stop displaying once you renew your license.
If you do not renew your license before it expires, the alerts will let you know that you do not have an active subscription and that access to your products and services will be restricted after a period of time. Should you have no active Sophos licenses, access to your Sophos Central account will be restricted as well.
Is there anything else I should know?
The new license expiry notifications:
- Are only available in Central Admin
- Do not apply to free trials
- Do not change the behavior of Sophos products when licenses expire i.e., they are notification only. Details on individual product behaviors can be found within the Licensing Guide
Source: Sophos
Sophos Firewall OS v21 MR1 brings several scalability, resiliency, and stability enhancements to your Sophos Firewall.
What’s new
- SSL VPN – Now supports key sizes of 3072 or 4096 bits for the Diffie-Hellman key exchange to enhance secure communication and compliance requirements. Enhanced UDP-based SSLVPN tunnel resiliency has also been added using a granular dead peer detection timeout configuration.
- IPsec VPN – Improved stability for offloaded policy-based VPN IPsec traffic that eliminates slow browsing issues.
- NAT64 – The firewall enables IPv6-only clients to access IPv4 websites through an explicit proxy. Also added support for an IPv4 upstream proxy for IPv6-only clients.
- DHCP – Implemented added resiliency to the DHCP service which now auto-restores if it gets into an error state.
- Cellular WAN – The firewall now offers enhanced cellular WAN monitoring by automatically setting “8.8.8.8” as the second probe target. This addresses the issue of ISPs blocking gateway pings, reducing the need for manual configuration.
- SD-RED support – SD-RED devices now support remote troubleshooting and diagnostics by Sophos Support.
How to get the firmware and documentation
Sophos Firewall OS v21 MR1 is a free upgrade for all licensed Sophos Firewall customers – including XGS Series, cloud, virtual, and software firewalls.
Note: XG Series devices are soon to be end-of-life and need to be upgraded to XGS Series devices immediately and are not supported by v21 or v21 MR1.
This firmware release will follow our standard update process. You can manually download SFOS v21 MR1 from Sophos Central and update any time. Otherwise, it will be rolled out to all connected devices over the coming weeks. A notification will appear on your local device or Sophos Central management console when the update is available, allowing you to schedule the update at your convenience.
You should update your Sophos Firewall firmware at your earliest opportunity.
Sophos Firewall OS v21 MR1 is a fully supported upgrade from all previous versions of v21, v20, v19.5 and v19.0. Please refer to the Upgrade Information tab in the release notes for more details.
Full product documentation is available online and within the product.
Source: Sophos
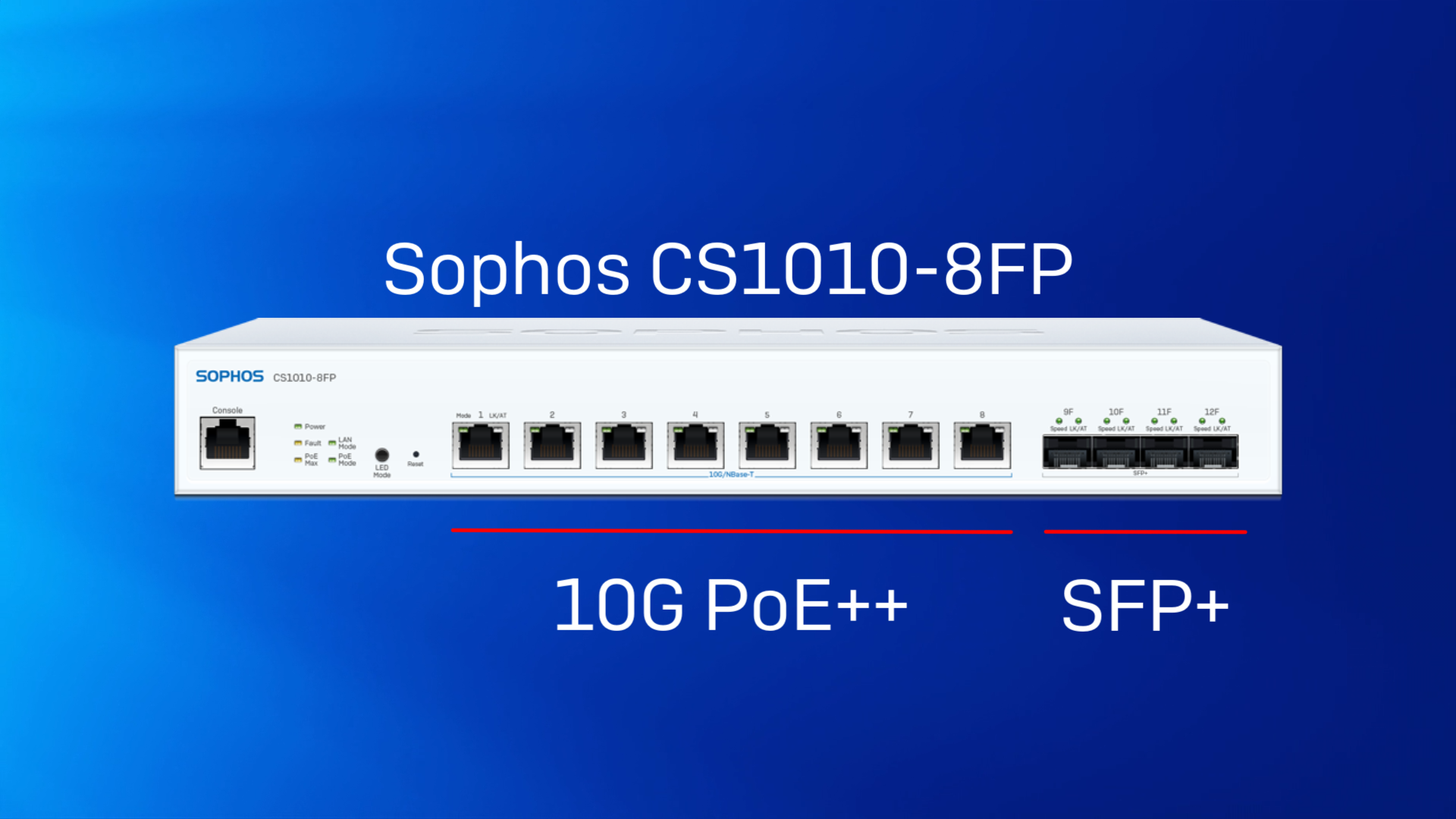
With the explosion of cloud computing, video streaming, AI, and other data-hungry technologies, traditional gigabit Ethernet (GE) networks are struggling to keep up. Bottlenecks and latency issues are hampering application performance and the overall user experience.
The newest addition to the Sophos Switch portfolio, CS1010-8FP, provides a cost-effective way to support the high-speed, low-latency requirements of modern networks and applications, such as:
- High-definition media streaming
- Large file content transfer, e.g., Computer-Aided Design (CAD), video editing
- Server-to-server and server-to-NAS data backups
- Communication with 10-gigabit servers
- Linking multiple 1-gigabit switches for improved performance
- Higher-speed LAN to reap the potential of high-speed internet, e.g., Fiber to the premises
Product highlights
For a brief overview of the new model, watch this video:
The CS1010-8FP offers eight 10-gigabit PoE-capable ports (PoE++/802.3bt) and four SFP+ interfaces. The 410W Power over Ethernet budget is sufficient to power up to six 60W devices or eight PoE++ devices with slightly lower power consumption, such as our AP6 840E access points
CS1010-8FP connectivity
- 8 x 1/2.5/5/10 GE multi-gigabit copper ports
- 4 x 1/10G SFP+ fiber ports
- 410W PoE budget [Ports 1-8 (max. 60W per port), 802.3bt/PoE++]
10 GE is fully compatible with earlier Ethernet standards, making it easy to integrate into existing networks (provided the required Cat6 cables are used).
Sophos multi-gig connectivity across your firewalls, access points, and switches gives you a future-proof solution to avoid network bottlenecks and the necessary throughput to handle evolving connectivity requirements. This allows you to scale your operations and seamlessly support emerging technologies, keeping your employees productive, and your business agile.
Find out more at Sophos.com/Switch.
Source: Sophos
In IT service management, every second counts. When you’re handling countless tickets, managing client relationships and overseeing intricate projects, an inefficient PSA tool can be your biggest roadblock.
If your system is slow, clunky or frustrating to use, it isn’t just an inconvenience -it’s a drain on your productivity and profitability. A PSA tool should work for you, not against you. But if navigating your current system feels like an uphill battle, it’s time to consider the impact of a poor UI.
10 reasons why your PSA needs a better UI
Here are the top reasons why upgrading your PSA’s interface is a necessity.
1. Faster workflows
An optimized UI minimizes unnecessary clicks, improves navigation and streamlines workflows so your team can accomplish tasks quickly and efficiently.
2. Reduced training time
A user-friendly interface ensures that new hires can learn the system faster, reducing the time and cost associated with onboarding and training.
3. Improved accuracy
A well-designed UI eliminates confusion, making key actions clear and logical, which helps reduce errors and misplaced data.
4. Increased technician satisfaction
Your team deserves a PSA tool that works with them, not against them. A modern UI reduces frustration, improves morale and keeps technicians happy and engaged.
5. Seamless multidevice use
Technicians aren’t always at their desks. A PSA tool with a responsive, mobile-friendly UI ensures productivity whether they’re in the office or on-site.
6. Enhanced customer interactions
When information is easy to find, your team can respond to customer or user inquiries faster and more effectively, improving service quality and satisfaction.
7. Greater customization
A PSA tool should adapt to your business, not the other way around. A flexible UI allows users to customize dashboards and layouts to fit their unique workflows.
8. Accessibility for all
A great UI ensures usability for everyone, including those who rely on keyboard navigation, screen readers or other accessibility tools.
9. Lower error rates
A cluttered or unintuitive UI leads to mistakes. A streamlined, well-designed interface helps prevent costly errors and miscommunications.
10. Future-proofing your business
Technology evolves fast, and so should your PSA tool. A PSA with a modern, continuously improving UI ensures you stay ahead of industry trends and efficiency standards.
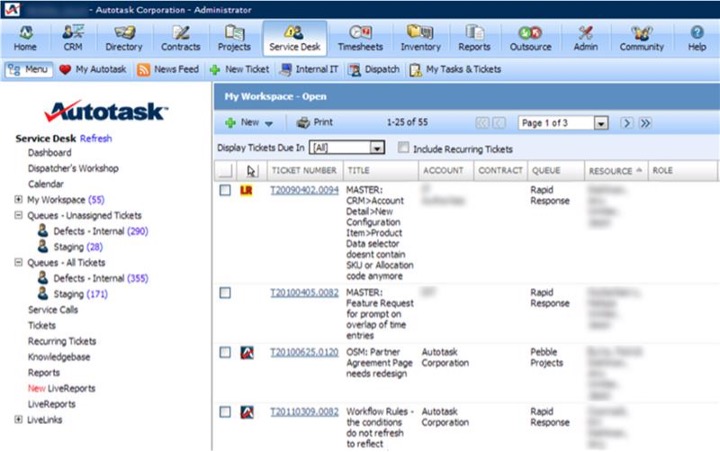
Autotask PSA’s Next-Generation UI: A Case Study in Good UX
If you’re looking for a PSA tool that embraces all these UX principles, Autotask’s latest UI update is worth exploring. With the 2025.1 release, Autotask PSA is taking its user experience to the next level with:
- Enhanced navigation: A collapsible left navigation menu, cleaner top navigation and a revamped search bar for a smoother experience.
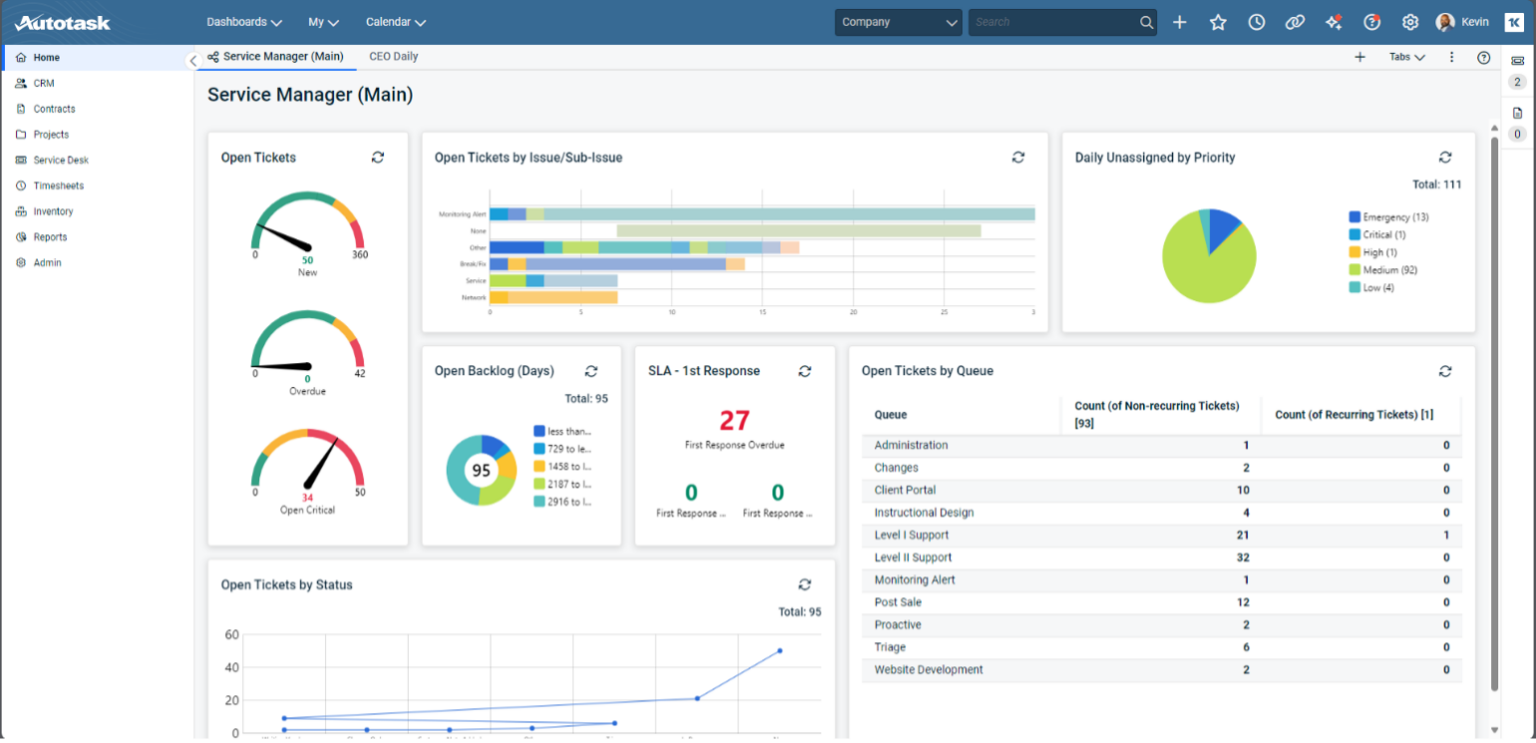
- Refreshed dashboards: Customizable layouts with resizable widgets to tailor the interface to your workflow.
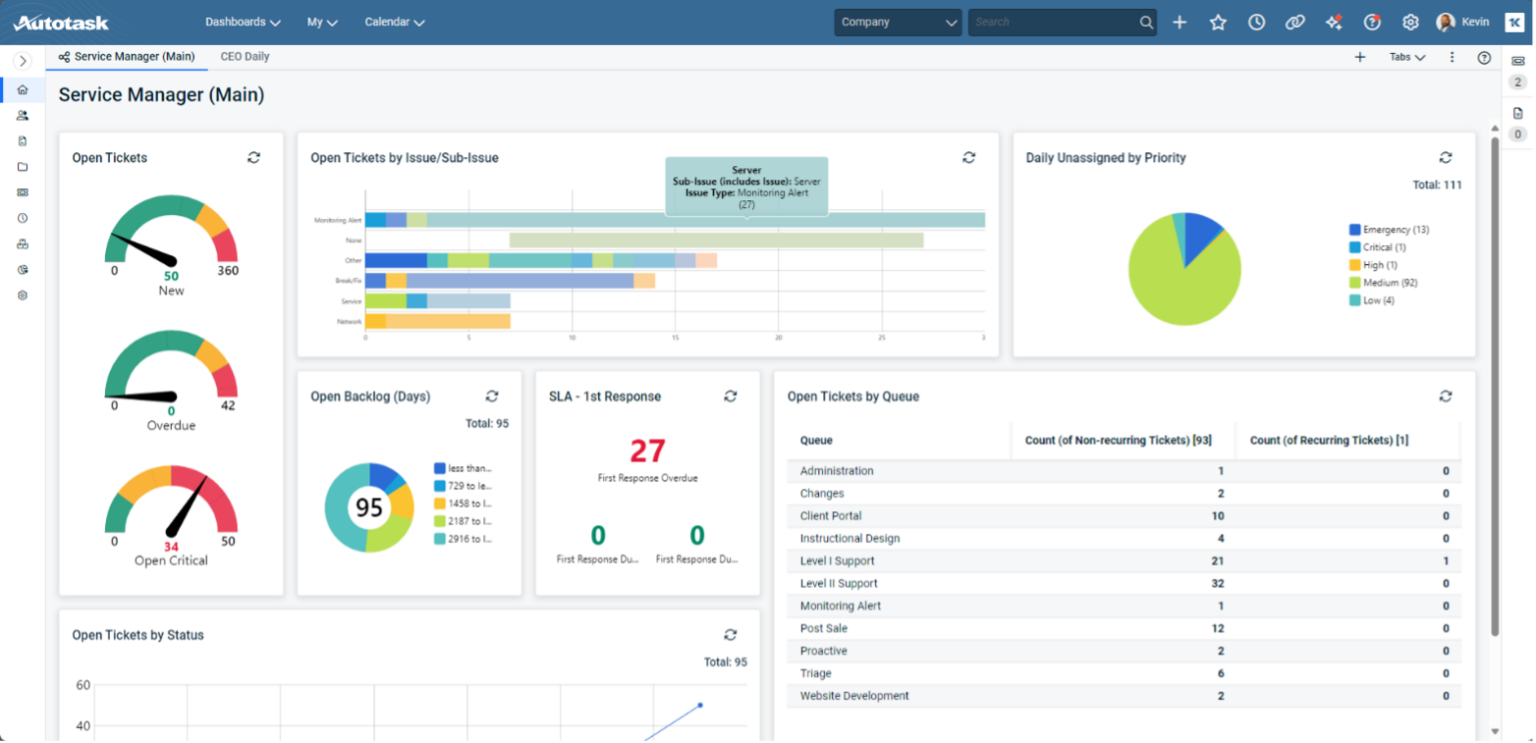
- Streamlined Worklist panel: Pinned tickets and tasks remain front and center, reducing distractions and keeping priorities clear.
- Improved accessibility: Enhanced keyboard navigation, mobile usability and screen reader support to ensure everyone can work efficiently.
- Unified UI across Kaseya IT Complete: A consistent design across Autotask, IT Glue and other Kaseya tools for easy cross-platform navigation.
And this is just the beginning. Future updates will include in-line editing, bulk actions, preview panels for related items and even more ways to improve usability and efficiency.
Don’t let a poor UI hold you back
Your PSA tool should make your job easier, not harder. If your current system is slowing you down, frustrating your team or making simple tasks unnecessarily complicated, it’s time for a change.
Autotask’s next-generation UI is designed to maximize efficiency, accessibility and user satisfaction. If you’re ready to see how a modern PSA interface can transform your workflow, it’s time to experience Autotask for yourself.
Ready to stop wasting time? Learn more about Autotask’s new UI today by booking a one-on-one call with one of our PSA experts.
Source: Datto
You can share your WiFi password safely by using a strong password, creating a guest network, enabling your router’s encryption and regularly updating your router. Sharing your WiFi password safely is important because someone with bad intentions could use it to hack into your network, steal your personal information or infect your devices with malware.
Keep reading to learn about the consequences of insecurely sharing your WiFi password, ways to securely share it and best practices for sharing it with others.
The risks of insecurely sharing your WiFi password
When guests visit your house for the first time, one of the first things they might ask for is your WiFi password. Here are several insecure ways you could share your WiFi password with friends, family or other guests:
- Leaving your WiFi password on a sticky note
- Sending it via unencrypted methods, such as emails or text messages
- Sharing it in a group chat on a messaging app
- Saying it during a phone call
- Showing guests the default password on your router
Imagine inviting a few friends over to watch a movie, and they ask for your WiFi password. You may have never changed your WiFi network’s default password, or you might be using a very weak WiFi password because it’s easier for people to type. Regardless of how secure your WiFi password is, sharing it with your friends through a group chat, individual text messages or email can leave your router vulnerable to hacking. Since emails and text messages are unencrypted, a cybercriminal could intercept your messages, revealing your WiFi password.
With your password, a cybercriminal could access your WiFi network, launch a malware infection and potentially infect other Internet of Things (IoT) devices connected to your network. By sharing your WiFi password via text with one of your friends, you risk a cybercriminal gaining unauthorized access to your WiFi network and potentially spying on you through any devices with cameras that are also connected to it.
How to securely share your WiFi password
Now that you know several insecure ways of sharing your WiFi password, let’s dive into how you can securely share it between Apple devices, Android devices and other devices.
Sharing your WiFi password between Apple devices
Before sharing your WiFi password with someone using an Apple device, make sure that both of your devices’ software is updated with the latest iOS version, WiFi and Bluetooth are turned on and you are signed in to your iCloud account with your Apple ID. Once you’re ready to share your WiFi password, unlock your device and connect to your WiFi network. A pop-up will appear at the bottom of your screen asking if you want to share your WiFi password with the other person. Tap Share Password, and the screen will indicate that the sharing was successful.
Sharing your WiFi password between Android devices
One way to share your WiFi password from one Android device to another is by turning your password into a scannable QR code. On Pixel and other Android phones, visit Settings, tap Network & Internet, then select Wi-Fi. Tap the settings icon next to your network, then tap Share. A screen will appear with a QR code displaying the name of your WiFi network and your WiFi password.
Not all Android devices follow the same steps, but the process is relatively similar. For example, if you use a Samsung phone, you will need to visit Settings, tap Connections, then select Wi-Fi. Tap the settings icon, then select QR Code in the bottom-left corner of your screen. On Samsung devices, you will not see your WiFi password written out.
How to safely share your WiFi password between any device
For a safe way to share your WiFi password between devices, consider using a password manager like Keeper®. Although you may think password managers only store passwords, you can use Keeper Password Manager to send passwords safely through its One-Time Share feature without jeopardizing your privacy. If your WiFi password is saved as a record in your digital vault, you can share that record for a limited time using the One-Time Share feature, even if the recipient doesn’t have a Keeper account. One-Time Share encrypts your WiFi password and other login credentials with zero-knowledge security, reducing the risk of someone intercepting your WiFi password while it’s being shared.
Best practices to follow when sharing your WiFi password
Whenever you share your WiFi password with someone, follow best practices to do so safely and minimize your chances of allowing a hacker access to your network or connected devices.
Use a strong, unique WiFi password
Change your default WiFi router’s password, if you haven’t already, to a strong, unique password that you don’t use for any other account. Even if you have changed the default password but it is weak or reused, update it with a randomly generated, secure password. A strong password for your WiFi should consist of at least 16 characters, with a combination of uppercase and lowercase letters, numbers and symbols. An easy way to create a strong, unique password for your WiFi network is by using a password generator, which produces random passwords based on customizable criteria.
Create a guest network
Instead of having guests use your primary WiFi network, create a guest WiFi network with a limited connection that won’t affect your devices. Your guest WiFi network should have a different password than your primary network, but it should be just as strong to keep your guests’ devices secure. Creating a guest network is a smart practice because you never know if any of your guests’ devices might be infected with malware. If an infected device connects to your primary WiFi network, malware could spread to other devices connected to your network.
Enable your router’s encryption
Make sure your WiFi router is encrypted to prevent cybercriminals from stealing transferable information by hacking into your network. Enable your router’s encryption with WPA3, which is the newest and best type of encryption protocol for WiFi. To enable encryption on your router, update it through your Internet Service Provider (ISP) settings.
Keep your router up to date
It’s important to keep your WiFi router up to date with the latest software because software updates equip your router with the most recent security patches, bug fixes and improved features. Keeping your WiFi router updated ensures it remains secure and stable, protecting your network and devices from cyber threats.
Securely share your WiFi password using Keeper
Instead of jeopardizing your network’s privacy by sending your WiFi password via email or SMS, securely share it using Keeper’s One-Time Share feature. With Keeper Password Manager, you can create a strong WiFi password, update it to be more unique, store it in a secure vault and share it with anyone you choose for a limited time to protect its safety.
Start your free 30-day trial of Keeper Password Manager today to protect your WiFi password and securely share your other login credentials.
Source: Keeper Security
For over two decades, Autotask has been a trusted go-to solution for IT professionals worldwide. As technology has evolved, so has Autotask — from client-server beginnings to a cloud-based powerhouse. Now, with the release of the 2025.1 update, we’re excited to usher in the next chapter: a reimagined user interface (UI) designed to modernize, simplify and empower.
Whether you’re a long-time Autotask power user or new to the platform, this update delivers a refreshed experience that adapts to your workflow, reduces friction and introduces a consistent design philosophy across the Kaseya IT Complete platform. Let’s take a closer look at the journey and what you can expect.
The philosophy behind the UI refresh
“Revamping the Autotask UI has been one of our biggest initiatives yet,” says Kevin Sequeira, General Manager of Kaseya’s PSA Suite. “We’ve invested heavily to make it not just visually appealing, but truly intuitive and efficient, so our customers can work smarter and get more done with less hassle.”
At the heart of the new UI refresh, our commitment is to create a more intuitive, streamlined and empowering user experience. You will see it kickstart starting in the 2025.1 release. This UI update is a thoughtful reimagining of how Autotask serves you in your day-to-day tasks. By focusing on user feedback and real-world workflows, we’ve developed a philosophy that prioritizes consistency, accessibility and ease of use.
Unified consistency across IT complete
The new Autotask UI is built on the Kaseya Design System (KDS), which ensures consistency across the IT Complete suite. Whether you’re switching between Autotask, IT Glue or other Kaseya tools, the familiar layout and functionality make the transition seamless. Think of it as learning one tool and being able to navigate them all effortlessly.
User-centric modernization
Our mission with this refresh is to make Autotask align seamlessly with your workflow. By minimizing clicks and maintaining context, features like collapsible navigation and inline editing simplify tasks, boost efficiency and improve usability. This update ensures you can stay focused on what truly matters, without unnecessary distractions.
Accessibility for all
We’ve enhanced keyboard navigation, improved mobile usability and made strides in screen reader support to ensure that Autotask is accessible to everyone, regardless of environment or ability. From the desk to on-the-go scenarios, we’re making it easier to stay productive.
Empowerment through simplicity
Autotask’s new UI strikes the perfect balance between simplicity and capability. Designed to help you get started quickly, it eliminates the overwhelm often associated with advanced tools. As you grow more comfortable, the intuitive interface allows you to self-discover Autotask’s powerful features, unlocking its full potential at your own pace.
A look back: Autotask’s evolution
Autotask has undergone three major UI overhauls in its history, each building upon the last to meet the needs of modern IT professionals.
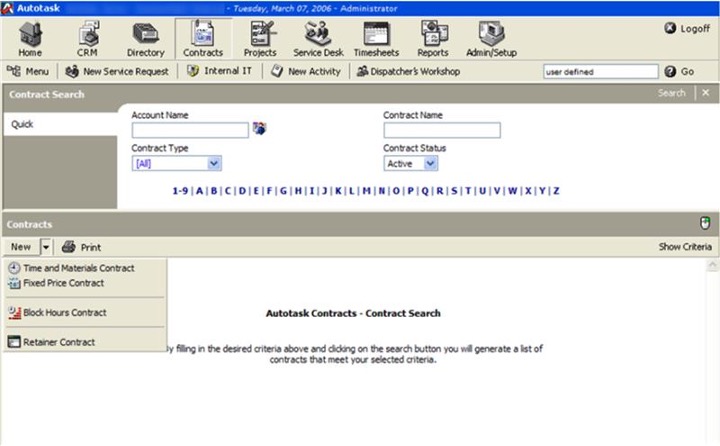
From its client-server roots to its web-based iteration and cloud-based transition, every evolution has brought new features and opportunities.

The 2025.1 release marks the beginning of Autotask’s new UI, laying the foundation for even more transformative updates in the coming months and years.
What’s new in the 2025.1 release?
The phased rollout of the 2025.1 release begins January 22, 2025, and will be complete by February 6, 2025.
Here’s what’s included:
Enhanced navigation
Navigating Autotask has never been smoother. With thoughtful updates to both the top and left navigation menus, users can expect a cleaner, more intuitive experience that minimizes clicks and maximizes productivity.
- Left navigation: A collapsible left navigation menu replaces the previous top hover-navigation, offering more screen space and flexibility.
- Top navigation reordering: Icons have been introduced for a cleaner and more intuitive interface.
- Search bar improvements: Now located on the right-hand side, with plans for a global search feature later this year.
Refreshed dashboards
Dashboards now feature a modern look and improved layout capabilities. You can resize and rearrange widgets directly on the screen for a personalized experience.
Streamlined Worklist panel
The updated Worklist panel makes it easier than ever to access pinned tickets and tasks, keeping your priorities front and center.
What’s next?
The 2025.1 release is just the beginning. Future updates will focus on key areas in Autotask such as contracts (including umbrella contracts), devices, tickets, projects and scheduling with core changes to the user experience:
- Refreshed grids and filters
- In-line editing
- At-a-glance preview panels for related items
- Bulk updates
We’re taking a progressive approach to the rollout, actively gathering feedback from users to refine and improve. If something feels new or unfamiliar, know that we’re here to listen and evolve.
Why change is worth it
Change can be uncomfortable, especially when it’s with a tool as central to your workflow as Autotask. However, history shows that every Autotask refresh has ultimately delivered greater value and usability. This update is no different. It’s about resetting how Autotask serves you in your day-to-day work, removing unnecessary steps and creating a platform that grows with your needs.
Share your feedback
We’re committed to making Autotask the best it can be. Help shape the future by sharing your thoughts through our UX Research Interest Form.
Together, we’re building the next generation of Autotask, one click at a time.
Source: Datto
In 2024, we introduced Generative AI features in the Sophos Extended Detection and Response (XDR) platform, empowering security analysts to operate confidently and make smart decisions fast.
Today, we are excited to extend these capabilities with the launch of the Sophos AI Assistant.
Crafted by experts, created for everyone
Designed and developed by Sophos experts for your in-house team, the Sophos AI Assistant guides security professionals of all skill levels through each stage of a case investigation, maximizing efficiency to identify and neutralize threats fast.
Feature video: Introducing the Sophos AI Assistant
The Sophos AI Assistant makes it easy for all users — from IT generalists to Tier 3 SOC analysts — to get the information they need to progress threat investigations and rapidly neutralize threats.
- Conduct an extensive range of SecOps tasks: Identify impacted entities, check URL reputation, analyze suspicious and complex commands, enrich data with the latest threat intelligence, and more.
- Accelerate investigations with accessible insights: The AI Assistant provides clear explanations and summarized information to help you understand context — and recommends next steps.
- Get the data you need quickly, without complex SQL: Ask your own questions using everyday language or use pre-defined prompts provided by Sophos’ threat detection and response experts.
- Create detailed case reports: Communicate with stakeholders with clear, focused reports that summarize investigations, highlight issues, and outline protective measures.
SecOps expertise — from our team to yours
Our people are at the heart of our AI-powered cybersecurity solutions. The Sophos AI Assistant isn’t just another AI tool — it’s expertise from the team behind the world’s leading Managed Detection and Response service, distilled into an intelligent agent.
- Designed in partnership with Sophos’ frontline security analysts, enabling your in-house team to benefit from real-world workflows and the experience of Sophos MDR experts.
- Developed by the Sophos AI team who apply their extensive AI expertise to design, build, and maintain over 50 AI models specific to cybersecurity. Our robust development processes — following secure-by-design principles — allow you to use Sophos AI with confidence.
- Continually updated based on the evolving threat landscape, ensuring you have access to the latest investigation techniques and current threat intelligence from Sophos X-Ops, our cross-functional cybersecurity task force.
Demo: See the new Sophos AI Assistant in action in this end-to-end real-world scenario
Outcome-focused AI
We’ve been elevating cybersecurity with AI since 2017, with deep learning and GenAI capabilities embedded across Sophos products and services and delivered through the largest AI-native platform in the industry. We know how to deliver real-world impact. While other vendors focus on the AI technology itself, we focus on the benefits and security outcomes it can deliver.
Our robust, battle-proven AI-powered solutions make a material difference by neutralizing threats faster and empowering analysts to make smart decisions. In addition to the new Sophos AI Assistant, GenAI capabilities in Sophos XDR enable your security team to neutralize adversaries faster, increasing both analyst and business confidence:
- AI Case Summary provides an easy-to-understand overview of detections, helping analysts make smart decisions fast.
- AI Command Analysis delivers insights into attacker behavior by examining commands that create detections.
- AI Search uses natural language search to accelerate day-to-day tasks and lower the technology barrier to security operations.
Sophos’ GenAI features are included with Sophos XDR subscriptions and are available on an opt-in basis, giving you full control over their use.
Elevate your cybersecurity with GenAI today
To explore how GenAI capabilities in Sophos XDR can help your organization better defend against active adversaries, speak with a Sophos adviser or your Sophos partner.
Already using Sophos XDR? Learn more about the GenAI features available to you, and how to activate them, on the Sophos Community.
Source: Sophos
Making sure your password is strong yet memorable can be challenging and stressful. However, following best practices – like using passphrases, incorporating acronyms and relying on a password manager – will ensure your passwords are strong and safe. A strong password should contain at least 16 characters, with a combination of uppercase and lowercase letters, numbers and symbols. Never use common phrases or personal information in your passwords, as these can be easily guessed by cybercriminals. Also, do not reuse the same passwords across multiple accounts because they can become compromised due to poor password practices.
Continue reading to learn the best practices for creating strong and memorable passwords.
1. Use passphrases
Passphrases are made up of multiple unrelated words, making them longer than typical passwords. The longer your password is, the harder it is for a cybercriminal to crack. Since passphrases are random words rather than random letters, numbers and symbols, they are easier to remember and provide more security benefits than a normal password due to their length and complexity.
You can create a strong passphrase by including a combination of words that have uppercase and lowercase letters, numbers and symbols, but make sure the words you use are completely random. For example, if you enjoy going to the beach and create a passphrase using words related to the beach (ocean, dolphin, sunshine, etc.), those words are not completely random, making the passphrase unsafe. A strong passphrase could look like this: Mixture-Pie-Met-State-Planning6. None of these words have anything in common, and this passphrase also includes a variety of characters and symbols separating the words.
2. Incorporate acronyms
Remember when you needed to learn a complex subject or study for an exam? You probably used an acronym to help you remember a concept. Acronyms are still useful when it comes to creating strong and memorable passwords. To incorporate acronyms into your password creation process, think of a sentence or phrase that holds meaning for you. Take the first letter of each word and turn it into a password, but don’t forget to still include numbers and symbols.
Let’s create a strong password using acronyms together. Imagine the sentence “I like going to the diner to eat strawberry chocolate cheesecake with my best friend Amy” is very meaningful to you. As an acronym, that sentence would be “IlgttdtesccwmbfA,” but you still need to incorporate a mixture of uppercase and lowercase letters, numbers and symbols to make it stronger; more on that below.
3. Replace letters for numbers and symbols
Following our example above, we still need to swap out letters for numbers or symbols to make our password strong. After making these changes, your password has gone from the acronym “IlgttdtesccwmbfA” to something like “I1g2tD2eSccWmbfA!.” To anyone who didn’t know your original sentence or phrase, this password would be challenging to guess since it contains random letters, numbers and symbols.
You can also replace letters with numbers and symbols in a passphrase. For example, if you have the words “cheese,” “sofa,” “motorcycle” and “sapling,” you can incorporate numbers and symbols to turn these random words into a strong passphrase. The outcome of replacing some letters with numbers and symbols could look like this: Ch3e5e_s0fA!Mot0rcYc1E-5ap1iNg. Because this password is long, contains a variety of characters and is completely random, it is a very strong passphrase.
4. Avoid common dictionary words and related phrases
Make sure to avoid using common dictionary words and phrases in your passwords. You may be thinking, “Doesn’t the dictionary have the kinds of words I’d use in a password? How am I supposed to avoid using common words?” Your password can still incorporate commonly used words; however, they should include a variety of characters or have letters replaced by numbers and symbols to make them more secure. Make sure your password does not contain the word “password” or the phrase “qwerty,” since cybercriminals expect people with poor password practices to use these for convenience. Common dictionary phrases might also include “iloveyou,” “goodmorning” or other popular sayings that could be cracked in a dictionary attack.
Dictionary attacks occur when a cybercriminal cracks your login credentials by guessing familiar phrases or words found in dictionaries. Even if you think adding “123456” to the end of your password makes it unique and more secure, it does not, because cybercriminals know this is a popular pattern. A good way to avoid using common dictionary words or phrases is to use a password or passphrase generator, which provides random combinations of characters and words, making it much harder for cybercriminals to crack your credentials.
5. Start using a password manager
In addition to using a password or passphrase generator, you should start using a password manager, which not only creates strong passwords but also stores them in a safe place. Keeper Password Manager offers a built-in passphrase generator, allowing you to replace any weak or reused passwords with strong, random passphrases at the click of a button. Keeper Password Manager can also automatically fill in your login credentials using KeeperFill®, which enters the username and password from your digital vault into websites by recognizing which website or account you need the login credentials for. To access your password manager, all you need to remember is your master password, which is a single password or passphrase that unlocks your digital vault.
How Keeper® helps you create strong passwords
By following these best practices for creating strong and memorable passwords, you will protect your online accounts and private information from potential cyber threats. Using Keeper Password Manager helps you create and store strong passwords and passphrases in a secure digital vault, making it a helpful tool for maintaining password security.
Start your free 30-day trial today to explore the convenient and safe features that Keeper Password Manager has to offer.
Source: Keeper Security
We’re excited to announce that Sophos has officially acquired Secureworks.
Please watch the video from Sophos CEO Joe Levy to hear why we’ve brought these two industry pioneers together and how we intend to transform cybersecurity for small, midmarket and enterprise organizations.
While today is our first day as a combined company, we already have a full and clear roadmap for the way ahead together. By integrating the combined expertise and technologies of Sophos and Secureworks, we will accelerate our mission to deliver cybersecurity products and services that solve the most critical problems for organizations of all sizes amid persistent and constantly changing cyberattacks.
To share just one example, we will combine the MDR/XDR and other key capabilities of both organizations into a single, unified security operations platform that enables us to deliver unparalleled cyber defenses for today’s diverse IT environments, including hundreds of built-in integrations. This advanced platform will further enhance visibility, detection and response for mitigating cyberattacks, setting a new standard for security operations.
Extending the threat intelligence that powers our defenses
Cyber threats never sleep. With the acquisition, the Secureworks’ Counter Threat Unit (CTU), renowned for intelligence about advanced persistent threats (APT) and state sponsored attackers, will join the Sophos X-Ops advanced threat response joint task force. This expanded unit will deliver unrivalled and diverse threat intelligence, further extending our customers’ defenses through expert insights into today’s complex threat landscape.
Customers remain fully protected at all times
We deeply value the trust that customers have placed in Sophos and Secureworks and we are unwavering in our commitment to continue to defend them against today’s advanced threats while maintaining the high levels of service they already value. In addition to continuing to deliver our current set of services and technologies to Sophos and Secureworks customers, our customer experience teams will ensure seamless, continued support during the integration period. Please reach out to your Sophos representative with any questions.
Source: Sophos
While AI brings many advantages, like all technological capabilities, it also introduces a number of risks. The survey revealed varying levels of awareness of these potential pitfalls.
AI risk awareness
Defense risk: Poor quality and poorly implemented AI
With improved protection from cyber threats jointly at the top of the list of desired benefits from GenAI, it’s clear that reducing cybersecurity risk is a strong factor behind the adoption of AI-powered defense solutions.
However, poor quality and poorly implemented AI models can inadvertently introduce considerable cybersecurity risk of their own, and the adage “garbage in, garbage out” is particularly relevant to AI. Building effective AI models for cybersecurity requires extensive understanding of both threats and AI.
Organizations are largely alert to the risk of poorly developed and deployed AI in cybersecurity solutions. The vast majority (89%) of IT/cybersecurity professionals surveyed say they are concerned about the potential for flaws in cybersecurity tools’ generative AI capabilities to harm their organization, with 43% saying they are extremely concerned and 46% somewhat concerned.

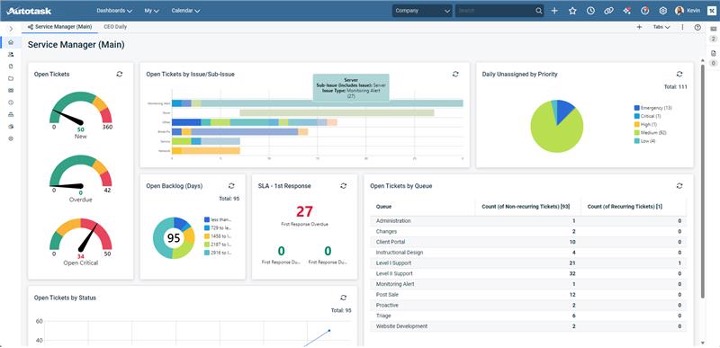
It is therefore unsurprising that 99% (with rounding) of organizations say that when evaluating the GenAI capabilities in cybersecurity solutions, they assess the caliber of the cybersecurity processes and controls used in the development of the GenAI: 73% say they fully assess the caliber of the cybersecurity processes and controls and 27% say they partially assess the caliber of the cybersecurity processes and controls.
While the high percentage that report conducting a full assessment may initially appear encouraging, in reality it suggests that many organizations have a major blind spot in this area.
Assessing the processes and controls used to develop GenAI capabilities requires transparency from the vendor and a reasonable degree of AI knowledge by the assessor. Unfortunately, both are in short supply. Solution providers rarely make their full GenAI development roll-out processes easily available, and IT teams often have limited insights into AI development best practices. For many organizations, this finding suggests that they “don’t know what they don’t know”.
Financial risk: Poor return on investment
As previously seen, improved return on cybersecurity spend (ROI) also tops the list of benefits organizations are looking to achieve through GenAI.
High caliber GenAI capabilities in cybersecurity solutions are expensive to develop and maintain. IT and cybersecurity leaders across businesses of all sizes are alert to the consequences of this development expenditure, with 80% saying that they think GenAI will significantly increase the cost of their cybersecurity products.
Despite these expectations of price increases, most organizations see GenAI as a path to lowering their overall cybersecurity expenditure, with 87% of respondents saying they are confident that the costs of GenAI in cybersecurity tools will be fully offset by the savings it delivers.
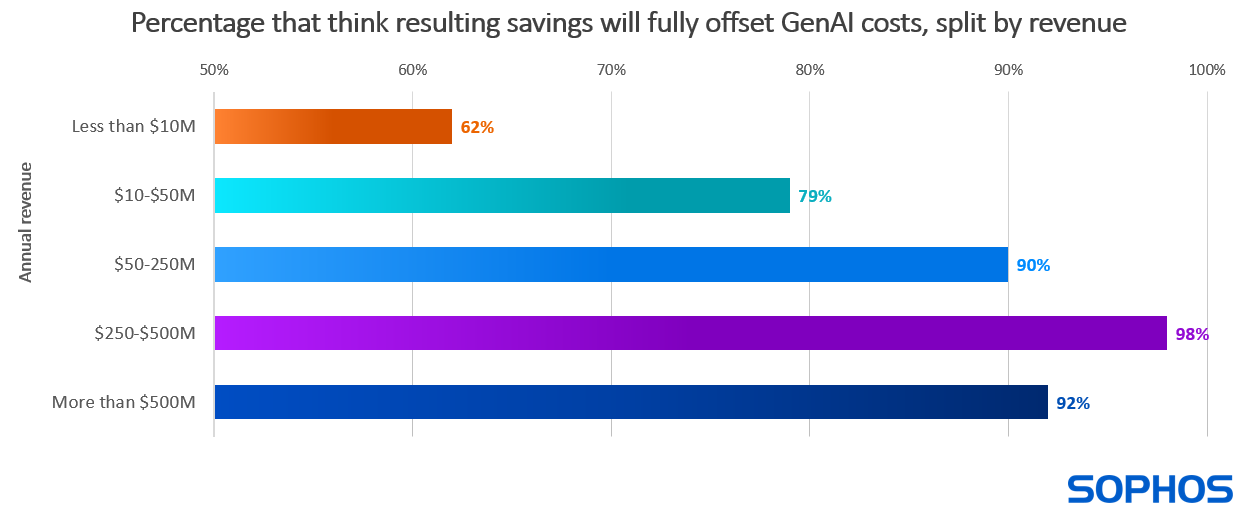
Diving deeper, we see that confidence in gaining positive return on investment increases with annual revenue, with the largest organizations ($500M+) 48% more likely to agree or strongly agree that the costs of generative AI in cybersecurity tools will be fully offset by the savings it delivers than the smallest (less than $10M).
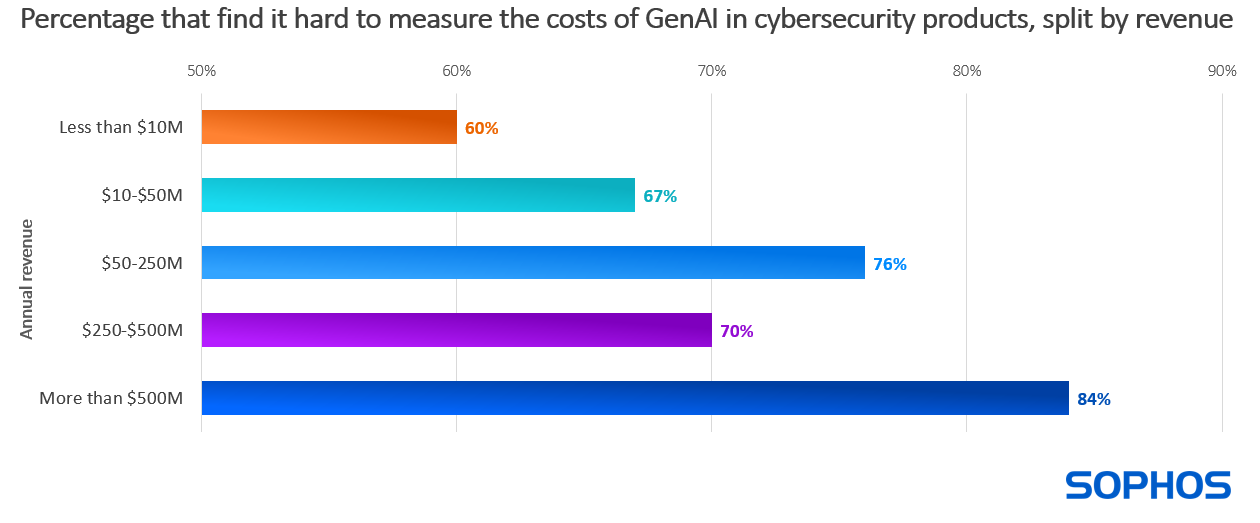
At the same time, organizations recognize that quantifying these costs is a challenge. GenAI expenses are typically built into the overall price of cybersecurity products and services, making it hard to identify how much organizations are spending on GenAI for cybersecurity. Reflecting this lack of visibility, 75% agree that these costs are hard to measure (39% strongly agree, 36% somewhat agree).
Broadly speaking, challenges in quantifying the costs also increase with revenue: organizations with $500M+ annual revenue are 40% more likely to find the costs difficult to quantify than those with less than $10M in revenue. This variation is likely due in part to the propensity for larger organizations to have more complex and extensive IT and cybersecurity infrastructures.
Without effective reporting, organizations risk not seeing the desired return on their investments in AI for cybersecurity or, worse, directing investments into AI that could have been more effectively spent elsewhere.
Operational risk: Over-reliance on AI
The pervasive nature of AI makes it easy to default too readily to AI, assume it is always correct, and take for granted that AI can do certain tasks better than people. Fortunately, most organizations are aware of and concerned about the cybersecurity consequences of over-reliance on AI:
- 84% are concerned about resulting pressure to reduce cybersecurity professional headcount (42% extremely concerned, 41% somewhat concerned)
- 87% are concerned about a resulting lack of cybersecurity accountability (37% extremely concerned, 50% somewhat concerned)
These concerns are broadly felt, with consistently high percentages reported by respondents across all size segments and industry sectors.
Recommendations
While AI brings risks, with a thoughtful approach, organizations can navigate them and safely, securely take advantage of AI to enhance their cyber defenses and overall business outcomes.
The recommendations provide a starting point to help organizations mitigate the risks explored in this report.
Ask vendors how they develop their AI capabilities
- Training data. What is the quality, quantity, and source of data on which the models are trained? Better inputs lead to better outputs.
- Development team. Find out about the people behind the models. What level of AI expertise do they have? How well do they know threats, adversary behaviors, and security operations?
- Product engineering and rollout process. What steps does the vendor go through when developing and deploying AI capabilities in their solutions? What checks and controls are in place?
Apply business rigor to AI investment decisions
- Set goals. Be clear, specific, and granular about the outcomes you want AI to deliver.
- Quantify benefits. Understand how much of a difference AI investments will make.
- Prioritize investments. AI can help in many ways; some will have a greater impact than others. Identify the important metrics for your organization – financial savings, staff attrition impact, exposure reduction, etc. – and compare how the different options rank.
- Measure impact. Be sure to see how actual performance relates to initial expectations. Use the insights to make any adjustments that are needed.
View AI through a human-first lens
- Maintain perspective. AI is just one item in the cyber defense toolkit. Use it, but make clear that cybersecurity accountability is ultimately a human responsibility.
- Don’t replace, accelerate. Focus on how AI can support your staff by taking care of many low-level, repetitive security operations tasks and providing guided insights.
About the survey
Sophos commissioned independent research specialist Vanson Bourne to survey 400 IT security decision makers in organizations with between 50 and 3,000 employees during November 2024. All respondents worked in the private or charity/not-for-profit sector and currently use endpoint security solutions from 19 separate vendors and 14 MDR providers.
Sophos’ AI-powered cyber defenses
Sophos has been pushing the boundaries of AI-driven cybersecurity for nearly a decade. AI technologies and human cybersecurity expertise work together to stop the broadest range of threats, wherever they run. AI capabilities are embedded across Sophos products and services and delivered through the largest AI-native platform in the industry. To learn more about Sophos’ AI-powered cyber defenses visit www.sophos.com/ai.
Source: Sophos
AI is firmly embedded in cybersecurity. Attend any cybersecurity conference, event, or trade show and AI is invariably the single biggest capability focus. Cybersecurity providers from across the spectrum make a point of highlighting that their products and services include AI. Ultimately, the cybersecurity industry is sending a clear message that AI is an integral part of any effective cyber defense.
With this level of AI universality, it’s easy to assume that AI is always the answer, and that it always delivers better cybersecurity outcomes. The reality, of course, is not so clear cut.
This report explores the use of AI in cybersecurity, with particular focus on generative AI. It provides insights into AI adoption, desired benefits, and levels of risk awareness based on findings from a vendor-agnostic survey of 400 IT and cybersecurity leaders working in small and mid-sized organizations (50-3,000 employees). It also reveals a major blind spot when it comes to the use of AI in cyber defenses.
The survey findings offer a real-world benchmark for organizations reviewing their own cyber defense strategies. They also provide a timely reminder of the risks associated with AI to help organizations take advantage of AI safely and securely to enhance their cybersecurity posture.
AI terminology
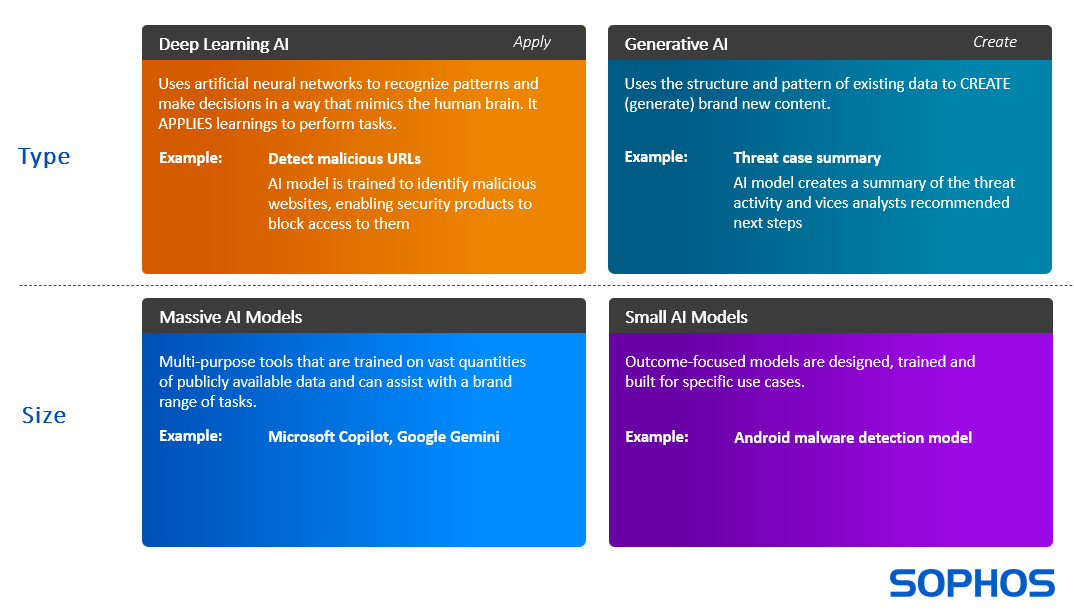
AI is a short acronym that covers a range of capabilities that can support and accelerate cybersecurity in many ways. Two common AI approaches used in cybersecurity are deep learning models and generative AI.
- Deep learning (DL) models APPLY learnings to perform tasks. For example, appropriately trained DL models can identify if a file is malicious or benign in a fraction of a second without ever having seen that file before.
- Generative AI (GenAI) models assimilate inputs and use them to CREATE (generate) new content. For example, to accelerate security operations, GenAI can create a natural language summary of threat activity to date and recommend next steps for the analyst to take.
AI is not “one size fits all” and models vary greatly in size.
- Massive Models, such as Microsoft Copilot and Google Gemini, are large language models (LLMs) trained on a very extensive set of data that can perform a wide range of tasks.
- Small models are typically designed and trained on a very specific data set to perform a single task, such as to detect malicious URLs or executables.
AI adoption for cybersecurity
The survey reveals that AI is already widely embedded in the cybersecurity infrastructure of most organizations, with 98% saying they use it in some capacity:

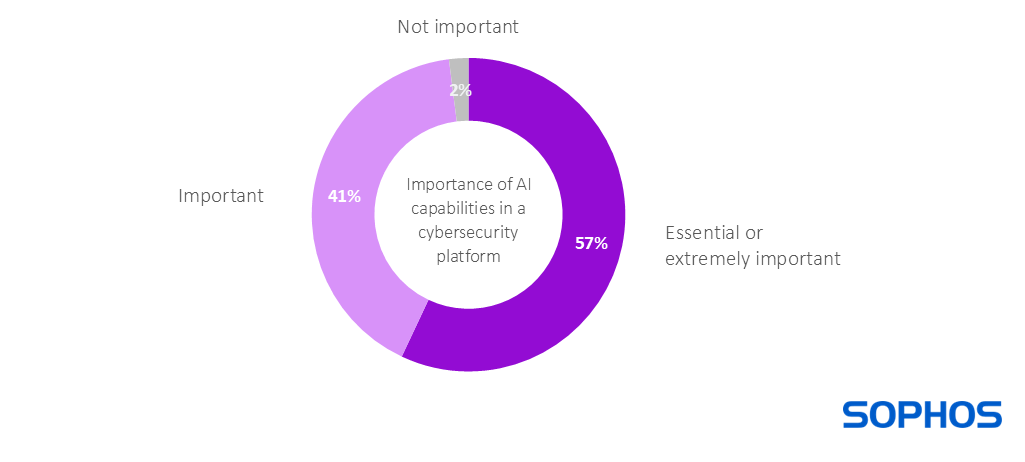
AI adoption is likely to become near universal within a short time frame, with AI capabilities now on the requirements list of 99% (with rounding) of organizations when selecting a cybersecurity platform:
With this level of adoption and future usage, understanding the risks and associated mitigations for AI in cybersecurity is a priority for organizations of all sizes and business focus.
GenAI expectations
The saturation of GenAI messaging across both cybersecurity and people’s broader business and personal lives has resulted in high expectations for how this technology can enhance cybersecurity outcomes. The survey revealed the top benefit that organizations want genAI capabilities in cybersecurity tools to deliver, as shown below.
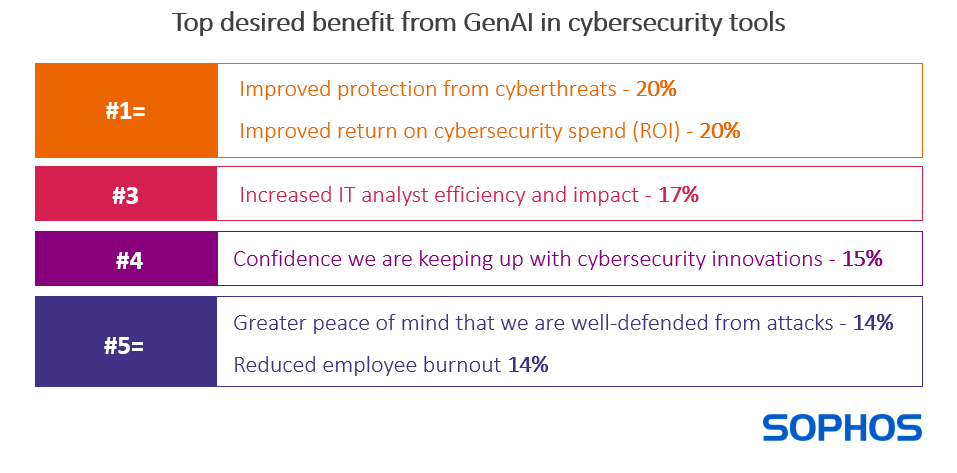
The broad spread of responses reveals that there is no single, standout desired benefit from GenAI in cybersecurity. At the same time, the most common desired gains relate to improved cyber protection or business performance (both financial and operational). The data also suggests that the inclusion of GenAI capabilities in cybersecurity solutions delivers peace of mind and confidence that an organization is keeping up with the latest protection capabilities.
The positioning of reduced employee burnout at the bottom of the ranking suggests that organizations are less aware of or less concerned about the potential for GenAI to support users. With cybersecurity staff in short supply, reducing attrition is an important area for focus and one where AI can help.
Desired GenAI benefits change with organization size
The #1 desired benefit from GenAI in cybersecurity tools varies as organizations increase in size, likely reflecting their differing challenges.
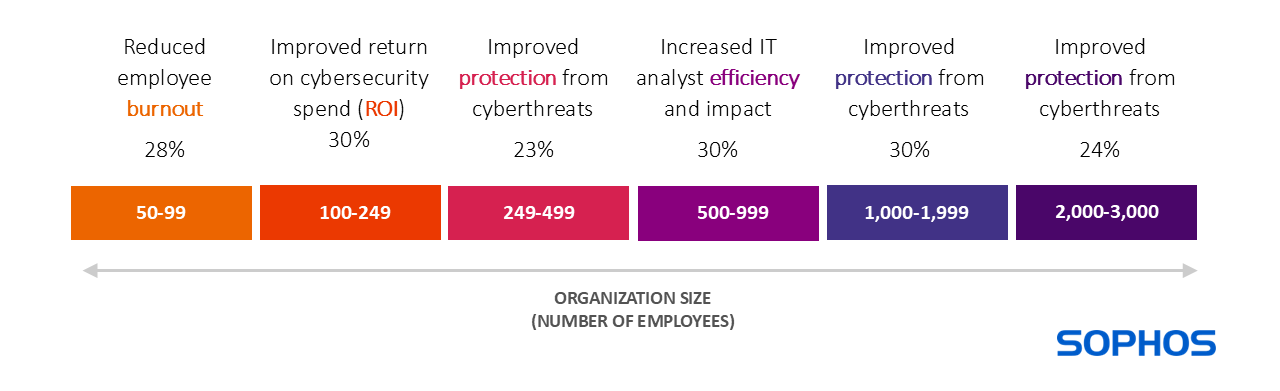
Although reducing employee burnout ranked lowest overall, it was the top desired gain for small businesses with 50-99 employees. This may be because the impact of employee absence disproportionately impacts smaller organizations who are less likely to have other staff who can step in and cover.
Conversely, highlighting their need for tight financial rigor, organizations with 100-249 employees prioritize improved return on cybersecurity spend. Larger organizations with 1,000-3,000 employees most value improved protection from cyberthreats.
About the survey
Sophos commissioned independent research specialist Vanson Bourne to survey 400 IT security decision makers in organizations with between 50 and 3,000 employees during November 2024. All respondents worked in the private or charity/not-for-profit sector and currently use endpoint security solutions from 19 separate vendors and 14 MDR providers.
Sophos’ AI-powered cyber defenses
Sophos has been pushing the boundaries of AI-driven cybersecurity for nearly a decade. AI technologies and human cybersecurity expertise work together to stop the broadest range of threats, wherever they run. AI capabilities are embedded across Sophos products and services and delivered through the largest AI-native platform in the industry. To learn more about Sophos’ AI-powered cyber defenses visit www.sophos.com/ai
Source: Sophos
Sophos, a global leader of innovative security solutions for defeating cyberattacks, today announced that its Sophos Managed Detection and Response (MDR) service has reached a major milestone, now protecting more than 26,000 organizations globally, growing its customer base by 37% in 2024. This achievement highlights the increasing demand for Sophos’ proactive, expert-led security solutions, which help organizations of all sizes stay protected 24/7 against increasingly sophisticated cyber threats, including the most advanced ransomware, business email compromise (BEC) and phishing attacks.
Sophos MDR offers a comprehensive suite of capabilities that go beyond standard threat containment to include full-scale incident response, such as root cause analysis, the removal of malicious tools or artifacts used by attackers, and investigations across customers’ environments to ensure adversaries are fully ejected to prevent another attack. What further differentiates Sophos is that these incident response services are included with Sophos MDR on an unlimited basis, meaning customers are not additionally charged and there is no limit on the number of incident response hours. Sophos MDR Complete also includes a breach protection warranty covering up to $1 million USD in incident response expenses. Sophos provides flexibility for how customers can work with the MDR analysts, including the ability to pre-authorize them to contain an active threat.
Sophos Investment in MDR and New Features
Sophos has made significant investments into its MDR offering with increased analyst capacity, AI assisted workflows, new features and expanded integrations to help deliver the best possible outcomes through improved protection, detection and investigation of threats. Sophos has added the following new features:
- Proof of Value: New Sophos MDR service insights to explain the MDR team’s actions including highlighting the human hours spent threat hunting and creating and tuning detections. High-value dashboard enhancements include details of MITRE ATT&CK tactics uncovered in proactive threat hunts conducted by Sophos’ MDR team, MDR analyst coverage, case investigation summaries and an account health check status.
- Enhanced Security for Microsoft Customers: New Sophos-proprietary detections for Microsoft Office 365 identify threats including business email compromise and adversary in the middle account takeover attacks, independent of the customer’s Microsoft license level.
- Expanded Compatibility with Third Parties:This expanded ecosystem of turnkey integrations with third-party cybersecurity and IT tools includes a new Backup and Recovery integration category.
- Proactive Vulnerability Mitigation:Sophos Managed Risk powered by Tenable provides attack surface vulnerability management as a new managed service option for Sophos MDR customers.
- Efficiencyand Automation:Sophos MDR has added AI-powered workflows to streamline the operational processes and drive better security outcomes for our customers. This innovation delivers a reduced mean time to respond (MTTR) through more efficient triage, while also ensuring that all legitimate threats are rapidly investigated. This enables analysts to concentrate on other tasks such as threat hunting, account health monitoring and detection engineering.
“Attackers are continuously advancing their tactics to out manoeuvre traditional security defenses,” said Rob Harrison, senior vice president of product management at Sophos. “Our customers rely on Sophos MDR to help their organizations tackle today’s threats 24/7 with full-scale incident response to remove active adversaries and conduct root cause analysis to identify the underlying issues that led to an incident. We’re consistently evolving our solutions with new offerings and integrations, just like attackers are constantly evolving their tactics, so customers can disrupt threats before they escalate into destructive attacks.”
Better Together: Sophos MDR Integrations
Sophos has invested significantly in third party integrations for its MDR customers to ingest and analyze events and alerts from an even broader range of tools and products, while also expanding propriety detections based on suspicious behaviour identified in Microsoft environments. This includes:
- A new Backup and Recovery integration pack with Acronis, Rubrik and Veeam integrations to strengthen defenses against ransomware.
- Microsoft Office 365 Management Activity integrations, enabling the ingestion of audit logs and security alerts across the Microsoft ecosystem. More than 9,000 customers have this integration in the Sophos MDR solution.
Sophos MDR Accolades
Sophos MDR has received multiple recognitions and accolades from customers, analysts and media in 2024:
- Sophos named a Leader in the IDC MarketScape: Worldwide Managed Detection and Response (MDR) 2024 Vendor Assessment *
- Sophos named a Leader in the IDC MarketScape: European Managed Detection and Response (MDR) Services in 2024 Vendor Assessment **.
- Sophos named a Leader in Frost & Sullivan’s 2024 Frost Radar™ forGlobal Managed Detection and Response (MDR)
- Sophos MDR declared the Winner of the “Best Managed Detection and Response Service” award in the 2024 SC Awards, and“Best Managed Security Service” award in the 2024 SC Awards Europe
- Sophos named a Gartner® Peer Insights™ Customers’ Choice for MDR Services for the 2nd year in a row
- Sophos MDR named CRN 2024 Products of The Year for Revenue and Profit
Threat Landscape from Sophos MDR
In the last 12 months, Sophos shared findings from the following MDR cases it analyzed for customers:
- In December 2024, Sophos released The Bite from Inside: The Sophos Active Adversary Report that provides an in-depth look at the changing behaviors and attack techniques that adversaries used in the first half of 2024. The data is derived from nearly 200 IR and MDR cases and found that attackers are looking for ways to hide in plain sight by abusing trusted applications or “Living off the Land” binaries or LOLbins. Sophos saw a 51% increase in abusing these applications.
- Sophos X-Ops released information that it is seeing an uptick of Akira ransomware cases across its MDR and Incident Response customers with eight cases since November 2024 across Akira’s 127 victims disclosed in the past six months.
- In June 2024, Sophos MDR published details on a nearly two-year long cyber espionage campaign they uncovered against a high-level government entity in Southeast Asia. The operation, which Sophos named Crimson Palace, involved three separate clusters of threat activity that overlapped with several well-known Chinese nation-state groups.
What Sophos MDR Customers Are Saying
Sophos was named a Customers’ Choice vendor in the second Gartner® Peer Insights™ Voice of the Customer Report for MDR. Sophos scored the highest overall customer rating of 4.9/5, based on 344 reviews, as of Sept. 30, 2024, with verified customer reviews celebrating Sophos MDR’s innovation.
Here’s what customers are saying about Sophos MDR:
- “Earlier it was very difficult for us to manage the alerts and incidents generated by the tools and technology but after MDR deployment we have complete peace of mind. We also have other products from Sophos so our overall experience from a manageability point of view is also good,” from assistant director of IT in the healthcare and biotech industry (Review link)
- “Sophos MDR is a wonderful product and services by Sophos, you don’t need a SOC after getting MDR,” from an IT manager in the IT services industry (Review link)
- “Sophos MDR is one of the best in the market. It’s a good service to have good sleep at night, as the burden of threat hunting is offloaded,” from an IT infrastructure specialist in the retail industry (Review link)
- “We have had an incredibly positive experience using Sophos MDR. We rest more easily knowing that their team is acting as an extension of our own team in doing threat hunting/detection/remediation in our environment on a 24/7 basis,” from an operations associate (Review link)
For more information about Sophos MDR, visit https://www.sophos.com/products/managed-detection-and-response
Source: Sophos
Kaseya, the leading global provider of AI-powered cybersecurity and IT management software, released today its 2025 State of the MSP Industry Look Ahead: Trends, Growth and Strategies for Success. MSPs reported profitability as a top focus in 2025 and are optimistic about their future growth. The report observes trends among top-earning MSPs that can be emulated by those looking for competitive advantages in the new year. The results of the survey are featured in the State of the MSP Industry 2025 Look Ahead: Trends, Growth and Strategies for Success.
“Small and medium-sized businesses are becoming more and more tech savvy – and MSPs are reaping the rewards,” said Gary Pica, Founder, TruMethods, a Kaseya Company. “They’re seeing revenue growth and want to continue that momentum long into the future. MSPs are an essential service and they’re making the right moves to build sustainable, high-margin businesses. By streamlining their operations and utilizing automation, MSPs are preparing to capitalize on big opportunities in 2025.”
Profitability
Looking ahead to 2025, 91% of MSPs cited profitability as a priority. When asked their concerns, new customer acquisition (43%), revenue growth (37%) and profitability (36%) topped the list. These results show that MSPs are shifting their focus toward growing their businesses to help them excel financially this year. This is a good time for them to take a look at their pricing structures, as well as their spending, to ensure they’re not undercharging, which hinders their ability to deliver exceptional results to their clients.
Growth and Competition
Despite their concerns about profitability, 64% of MSPs reported revenue increases last year and 67% of them expect further growth over the next three years. While the landscape remains competitive, MSPs are finding ways to stand out in the crowd. Smaller MSPs are often able to find success over larger ones by leveraging their niche expertise. Further, 83% of MSPs offer co-managed services, helping internal IT teams with business continuity and disaster recovery (38%), cloud-based infrastructure design and management (37%) and data backup & protection (36%). Client apathy toward cyber-risks as a barrier to offering cybersecurity solutions rose from 7th last year to 1st this year – with nearly half of respondents citing it as a concern.
“It can be difficult to get small businesses to understand the importance of investing in security when they often don’t see themselves as a target,” said Pica. “While educating clients is important, it’s pivotal for MSPs to invest in platforms and tools that allow their customers to be better protected without breaking the bank.”
The Opportunity and Threat of AI
In the drive for increased growth and profitability, MSPs can utilize AI-driven tools that increase efficiency by automating repetitive and time-consuming tasks. Unfortunately, AI is a double-edged sword that both enables and threatens businesses. More than two-thirds of MSPs saw an increase in AI-driven attacks in the last 12 months. In 2024, more MSPs were affected by AI-supported attacks (32%) than supply chain attacks (29%) or endpoint threats (29%). This shouldn’t scare technicians away from AI – ironically, the best soldier in the battle against AI is AI itself. Top-earning MSPs are leveraging AI-driven security tools to stay ahead of emerging threats.
Lessons from Top Earners
The survey analyzes what sets MSPs making $10 million or more a year apart and offers guidance to smaller MSPs who want to grow. First and foremost, they are proactive in adopting new technologies and delivering remarkable service. More than half of the top earners have migrated their client workloads to the cloud and a whopping 97% offer managed security services. These high earners are focused on smart growth and always expand their services in alignment with their clients’ needs and leverage automation to improve their efficiency.
To download the State of the MSP Industry 2025 Look Ahead: Trends, Growth and Strategies for Success, click here.
Source: Kaseya
Sophos ZTNA has received a couple of important updates to improve deployment ease and flexibility. These changes are part of updates to Sophos Central and don’t require any updates to your gateways or clients.
Let’s Encrypt certificates
 Sophos ZTNA now adds Let’s Encrypt certificate support for your gateways.
Sophos ZTNA now adds Let’s Encrypt certificate support for your gateways.
As you probably know, Let’s Encrypt is a non-profit open certificate authority run by the Internet Research Group (ISRG) that provides X.509 certificates for TLS encryption at no charge.
Let’s Encrypt makes certificates free and easy but comes with the inconvenience of only being valid for 90 days. This means they require more frequent maintenance than other certificates, which often have a duration of 12, 24, or 36 months.
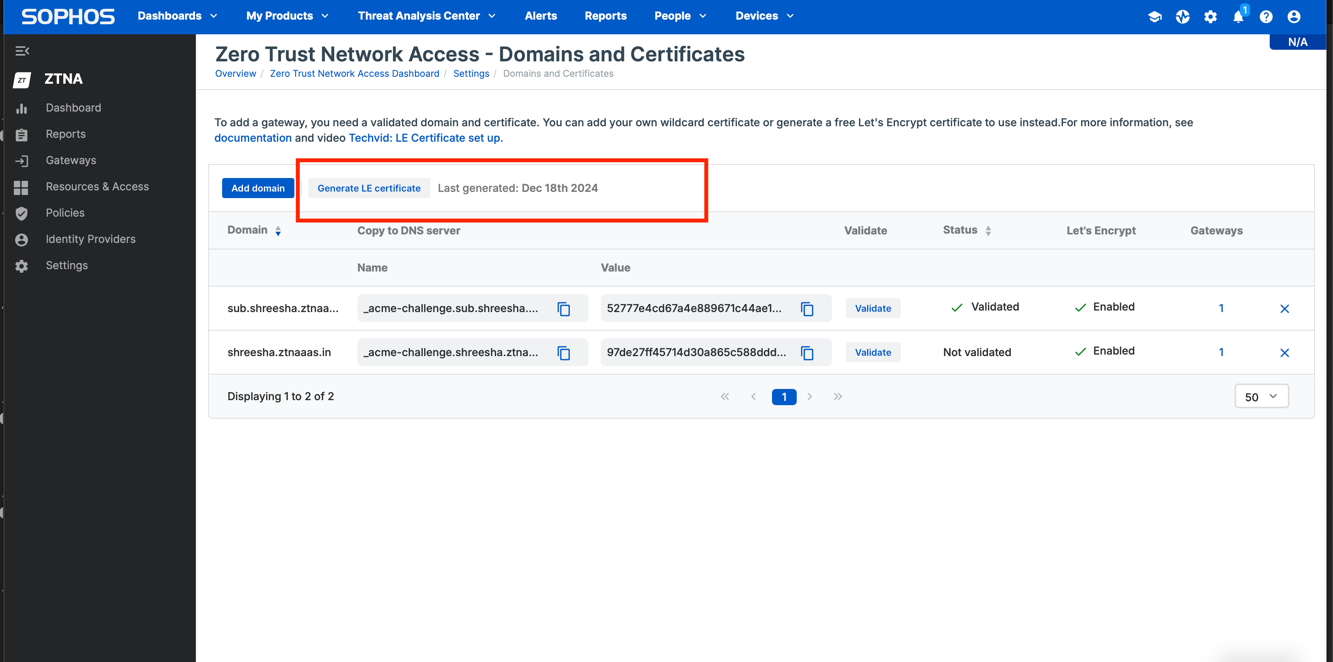
Fortunately, Sophos ZTNA helps overcome this issue with support for auto-renewal 30 days prior to expiry.
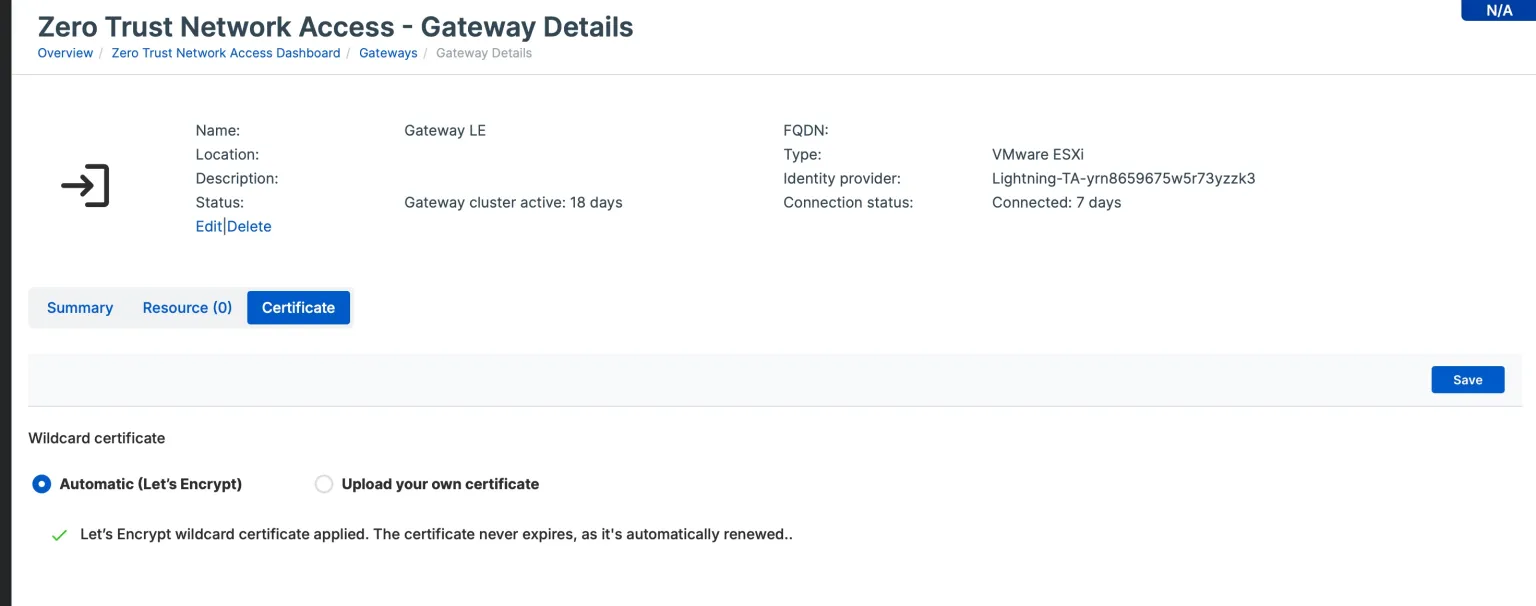
You can take advantage of this with your existing gateways anytime, regardless of your deployment mode (cloud or on-premises).
Added Sophos Central regions
Sophos ZTNA central management is now supported beyond the standard US and EU regions, adding five new regions: Australia, Brazil, India, Japan, and Canada.

If you currently manage your Sophos Firewall and/or Endpoints in one of these regions you can now easily add Sophos ZTNA to your account.
Get started with ZTNA for free
If you’re not already using Sophos ZTNA, you can get started for free. There’s a free trial available via Sophos Central, and if you’re already a Sophos Firewall customer, you can get three free one-year licenses and take advantage of the ZTNA gateway integrated into your firewall.
Check out the Deployment Checklist for other considerations when deploying ZTNA and the latest online documentation.
Πηγή: Sophos
You can protect your IP address by hiding it and masking your location to prevent cybercriminals from impersonating or tracking you. An IP address, also called an Internet Protocol address, is a series of unique numbers that identifies your device on the internet or the network it’s connected to. Your IP address allows information to be sent across a network and distinguishes your device from others on the internet. Since your IP address reveals identifying information about you, it is important to protect it because cybercriminals can use it to track you or target you with scams.
Continue reading to learn what may happen if you don’t protect your IP address and how to hide it from people with bad intentions.
What happens if you don’t protect your IP address?
If you don’t protect your IP address, cybercriminals can do the following:
- Track your location: Someone with your IP address can determine your geographical location, narrowing it down to your state, city or even ZIP code. Even though your IP address will not reveal your exact location, cybercriminals can use the information it provides to conduct further research. They may publish the information they find about you online in a process called doxxing.
- Exploit your IP address: Using your IP address, a cybercriminal can download illegal content, including pirated games or inappropriate videos. If that illegal activity is traced to your IP address, it could be difficult to prove that you were not responsible for those actions.
- Target your network: Failing to protect your IP address can also lead to your home WiFi network being hacked. For example, if the IP address of your computer is compromised, a cybercriminal may be able to find other devices connected to your same home WiFi network and attempt to hack them.

How to hide your IP address from cybercriminals
The best way to protect your IP address from falling into cybercriminals’ hands is to hide your device’s private IP address and mask your location. You can hide your device’s IP address by using a Virtual Private Network (VPN), a proxy server, the Tor web browser or your phone’s mobile data.
Use a Virtual Private Network (VPN)
A Virtual Private Network (VPN) protects your internet connection, online privacy and IP address by encrypting your connection. VPNs mask your IP address and allow you to use public WiFi without jeopardizing your privacy. Although there are many benefits to using a VPN, most charge a subscription fee, and some websites may block access when you use a VPN.
Use a proxy server
A proxy server is an in-between server so you can access online resources with enhanced privacy and security. Using a proxy server is an effective way to hide your IP address from cybercriminals because it retrieves data from the internet without exposing your identity to any websites you visit. Unlike most VPNs, proxy servers are generally free to use. If you need to access a website and want your IP address concealed, a proxy server is often a more convenient option.
Use the Tor browser
Even if your default web browser is Chrome or Safari, you can use the Tor browser specifically when you want to hide your IP address. Tor is a unique web browser that lets you browse the internet anonymously by scrambling data about your online activity, making it very challenging for anyone to track your browsing. The browser hides your IP address by routing your internet traffic through different nodes. However, because this process requires significant resources, using Tor may slow your internet connection, and some websites you attempt to visit may be blocked.
Connect to your phone’s mobile data
By turning off WiFi on your phone and relying on mobile data, you make your IP address much more challenging for cybercriminals to track because your IP address will change as you move. Even though connecting to your phone’s mobile data does not completely hide your IP address, it will change frequently, making your location harder to detect since you are not connected to a set WiFi network.
Should I be worried if someone has my IP address?
You don’t need to panic if someone has your IP address, but you should take the necessary steps to change it to maintain your privacy. Changing your IP address is as simple as unplugging your WiFi router for several minutes and then plugging it back in. When you reconnect your device to the router, it will have a refreshed IP address, making it easier to protect your identity from anyone with malicious intent.
Keep your IP address protected
Because your IP address can reveal private information about you, you should stay safe by hiding your device’s IP address and masking your location. Using a VPN, proxy server or Tor browser helps prevent your online activity from being tracked and keeps your IP address out of the wrong hands.
Source: Keeper Security
G2, a major technology user review platform, has just released its Winter 2025 Reports, and Sophos ranks as the #1 overall Firewall, MDR, and EDR solution.
Sophos is – once again – the only vendor named a Leader across the G2 Overall Grid® Reports for Endpoint Protection Suites, Endpoint Detection and Response (EDR), Extended Detection and Response (XDR), Firewall Software, and Managed Detection and Response (MDR). Based on user feedback, Sophos was ranked the #1 solution in 36 individual reports spanning the Antivirus, EDR, Endpoint Protection Suites, XDR, Firewall, and MDR markets.
It’s written in the stars
Customer review platforms like G2 are crucial in empowering buyers, holding businesses accountable, and driving market innovation and competition. These platforms allow customers to leave honest, unfiltered feedback about products and services, providing potential buyers access to actual user experiences rather than just marketing and messaging. The transparency and visibility of reviews encourage companies to improve their products and customer experiences continuously.
Managed Detection and Response
Sophos MDR enables more than 26,000 customers to maximize the value of their cybersecurity investments. In addition to the #1 overall ranking among MDR solutions, Sophos MDR is also rated the top solution in seven additional report segments for the category, including the Overall, Enterprise, and Mid-Market Grids, as well as earning the Best Results and Best Usability distinctions for the Enterprise and Mid-Market segments.
Endpoint Detection and Response/Extended Detection and Response
Sophos EDR/XDR was named a Leader across five different segments in the Winter 2025 Reports, including the Overall, Enterprise, Mid-Market, and Small Business Grids, as well as an Overall Momentum Leader.
Firewall
In addition to being named the #1 Overall Firewall solution, Sophos Firewall was also rated as the #1 firewall solution by Mid-Market and Enterprise users. All 4 user segments (Overall, Small Business, Mid-Market, and Enterprise) named Sophos Firewall a Leader in their respective G2 Grid Reports.
Independent Third-party Validation
The accolades from the G2 Winter 2025 Reports come off the heels of another major user review-based report in Gartner’s 2024 Voice of the Customer for Managed Detection and Response, where Sophos was the highest rated Customers’ Choice vendor to go along with the most user reviews featured in the report.
With this latest distinction, Sophos was the only cybersecurity vendor named a Customers’ Choice across the Endpoint Protection Platforms, Network Firewalls, and MDR markets in 2024 on Gartner Peer Insights – a testament to Sophos’ capabilities of providing end-to-end security for organizations of all sizes.
Furthermore, it’s not just our customers raving about Sophos protection. MITRE ATT&CK Evaluations, one of the world’s most respected independent security tests, just released their 2024 MITRE ATT&CK® Evaluations: Enterprise. Sophos XDR detected 100% of the adversary behaviors in attack scenarios targeting Windows and Linux platforms, mimicking malware strains from ruthless ransomware-as-a-service gangs LockBit and CL0P. All of Sophos’ responses to these ransomware attack scenarios were marked “technique” – the highest possible rating that denotes who, what, when, where, why and how attacks were carried out.
What Sophos customers are saying
“Sophos MDR: 360 degree MDR solution for endpoint security” said a user in the Enterprise segment
“Sophos MDR helps us sleep at night knowing our environment is monitored 24/7” said a user in the Mid-Market segment
“Sophos Firewall is a robust and user-friendly security solution that provides comprehensive protection through advanced threat detection, deep packet inspection, and synchronized security with other Sophos products” said a Head of IT in the Mid-Market segment
“Sophos Firewall automatically identifies and blocks active threats, prevents the lateral movement of attacks, and delivers immediate insights into compromised devices, users and application” said a user in the Small Business segment
“What stands out the most is how effortlessly Sophos Firewall streamlines security tasks, allowing users to focus on protecting their networks without getting bogged down in complex configurations” said a user in the Mid-Market segment
“We can rest easy knowing that Sophos Intercept X is continuously guarding our endpoints from ransomware assaults, which are the kind of thing that keep IT administrators up at night” said a SOC Analyst in the Mid-Market segment
Elevate your cyber defenses with Sophos
As the G2 ratings illustrate, Sophos provides unparalleled breadth and depth of protection. Our world-leading endpoint, network, email, cloud, and security operations solutions defend over 600,000 organizations from advanced cyberthreats, including ransomware.
For more information on our services and products, speak to your Sophos partner or representative and visit our website.
Source: Sophos
The best way to adjust your Privileged Access Management (PAM) strategy for growth is to choose a cloud-based PAM solution that scales with your organization. You may face many challenges when adjusting your PAM strategy as your organization grows, including more complex infrastructure, a higher number of login credentials to manage and increased security risks, so you need to have a flexible PAM solution.
Continue reading to learn more about the challenges your organization may face when adjusting its PAM strategy and why you should choose a cloud-based PAM solution that grows with you.
Challenges in adjusting your PAM strategy as you grow
As your organization grows, your PAM strategy must scale and evolve to address increased complexity, manage access, balance security with usability, meet compliance requirements and overcome scalability issues with your current PAM solution, if you have one. However, for organizations that aren’t prepared, these challenges can become significant obstacles to maintaining a secure and efficient infrastructure.
Infrastructure becomes more complex
As your organization grows, your infrastructure becomes more complex because you may have an increased number of users, devices and resources across different regions. You may need to shift to cloud services or combine on-premises with cloud solutions, which can bring its own set of challenges.
The more employees your organization hires, the more endpoint devices your IT team will need to manage and secure. Having diverse endpoints, such as laptops, tablets, phones and other Internet of Things (IoT) devices, makes it difficult for your IT team to manage and track access across all platforms and devices. In addition to an influx of new employees, your organization will likely need to grant new users privileged access to sensitive data. With each new privileged account, there is a greater need to ensure these accounts are secure across all systems.
Credential management
When you hire more employees, managing credentials becomes more challenging, especially for users who require privileged access, such as those in key roles like IT or HR. As your organization expands, it’s not just about adding accounts but about managing who needs access to what and when. It’s important to have a PAM strategy in place that allows you to track who has privileged access, both permanently and temporarily. With a strong system in place that follows the Principle of Least Privilege (PoLP), you can more easily audit privileged accounts and determine whether they still require the same access as they once did.
Balancing security with usability
Your organization must keep its systems secure and usable to ensure employees can do their jobs productively. However, this can be challenging with more employees, since they have varied access needs. Overly strict security can hinder productivity, while lenient controls can increase the risk of breaches. Role-Based Access Control (RBAC) ensures that each employee can access only the sensitive data they need to perform their job within your organization. By assigning access based on roles, RBAC helps control who can access specific data and limits which employees can access certain sensitive systems without preventing them from accessing the systems and data they need to do their jobs. Single Sign-On (SSO), on the other hand, enables employees to log in once and gain access to all authorized systems without needing to log in separately each time. This not only improves security by reducing the need to manage multiple sets of credentials but also improves productivity by saving employees time and streamlining their access to necessary resources. As you adjust your PAM strategy, ensure that your PAM solution supports both RBAC and SSO.
Overcoming scalability issues with your current PAM solution
The PAM solution you currently use may work well for a smaller team or fewer systems, but as your organization continues to grow, it may fail to scale with you. Your organization should adopt a cloud-based PAM solution that can grow with you and won’t sacrifice security or performance while adapting to more privileged users, systems, platforms and data.

Keeping up with compliance requirements
As your organization expands into new regions or countries, it will face new challenges regarding regulatory and compliance requirements. Since each jurisdiction has its own requirements for securing privileged data, you must ensure your organization complies with a variety of regulations based on location.
Some common compliance requirements that vary based on industry and location include:
-
- General Data Protection Regulation (GDPR): Applies to organizations that sell to customers located in the European Union.
- Health Insurance Portability and Accountability Act (HIPAA): Applies to the healthcare industry in the United States.
- Service Organization Control Type 2 (SOC 2): A voluntary compliance framework primarily relevant to companies that sell cloud-based products and services, emphasizing data security, availability, processing integrity, privacy and confidentiality.
These frameworks require your organization to enforce strict controls over who can access sensitive data. Ensuring that your PAM solution scales with your organization’s growth and provides a centralized dashboard for managing and auditing privileged access is needed for meeting compliance requirements and minimizing risks.
Choose a cloud-based PAM solution that grows with you
To address the growing pains that your organization may face, you need to choose a cloud-based PAM solution that grows with you, like KeeperPAM®: a cloud-based, zero-trust and zero-knowledge security solution.
KeeperPAM is highly scalable, making it the best solution for growing organizations. As your organization adds new users or departments, IT administrators can quickly provision new accounts with RBAC, ensuring that employees only have access to the data and systems they need. Additionally, features like Just-In-Time (JIT) access make it seamless to grant temporary access only when needed and automatically revoke that access once a task is complete. As you continue to add to your infrastructure and tech stack, Keeper has hundreds of integrations that allow teams such as security and DevOps to continue using their preferred solutions securely.
For a growing organization, KeeperPAM’s scalability helps you maintain high security standards while supporting increased access demands. Users can access their Keeper Vaults from anywhere, providing a better experience across locations and devices, ensuring your PAM solution grows with your business needs.
Future-proof your PAM strategy with KeeperPAM
Prepare for the future of your growing organization by switching to a scalable PAM solution like KeeperPAM. By future-proofing your PAM strategy with KeeperPAM, you can overcome the challenges most organizations face when adjusting their PAM strategies, including complex infrastructure, managing more privileged accounts, balancing security with usability and overcoming scalability issues.
Request a demo of KeeperPAM today and enhance your PAM strategy.
Source: Keeper
Most password managers on the market require only the user’s master password to access their password vault. If the master password is compromised, a cybercriminal could use it to log in to the user’s account from any device. This would mean that the cybercriminal would have access to all of that user’s saved passwords.
In contrast, Keeper requires device-level approval. Even if a cybercriminal has your master password, they would first need to have physical access to one of your approved devices to log in. This adds an extra layer of security against cyber threats like password spraying or data breaches on the dark web.
Continue reading to learn how Keeper’s device-level approval feature makes it much harder for attackers to gain unauthorized access to your Keeper account.
What is device-level approval in Keeper?
In Keeper Password Manager, device-level approval means that each new device attempting to access a Keeper Vault must be explicitly approved before gaining access. This device approval process occurs before an attempt to use a master password. In Keeper’s security architecture, the backend system does not allow an attempt to log in without first approving a device. This means that the existence of an account is never confirmed or denied by the application until a user proves their identity. This also means that the attacker would not know if a master password is correct.
When a user attempts to access their Keeper Vault from a new device, that device needs to be approved by one of the following:
- The account owner
- An administrator (in enterprise environments)
- Through an existing trusted device
Each new device receives a unique device ID, preventing unauthorized devices from accessing a user’s vault even if the login credentials have been compromised. This provides an additional layer of security that goes beyond Two-Factor Authentication (2FA).
How device-level approval protects against password stuffing attacks
Device-level approval requires both the user’s password and an authorized device to access their vault. Even if a cybercriminal manages to steal a user’s master password, they still wouldn’t be able to access the vault, as the cybercriminal’s device is not approved. This prevents common password attacks, such as password stuffing and brute force attempts, from succeeding.
When data is in transit, Keeper’s encryption model also stops other types of cyber attacks, like Man-in-the-Middle (MITM) attacks, because each approved device is double-encrypting traffic on top of Transport Layer Security (TLS). Cybercriminals cannot simply intercept and decode traffic between your device and Keeper’s servers. Even if they capture the data, it’s useless without the device-specific keys.
The device approval system further helps protect against social engineering attacks. Even if someone convinces you to reveal your password through phishing, they won’t be able to use it because none of their devices are approved.
How Keeper differs from other password managers
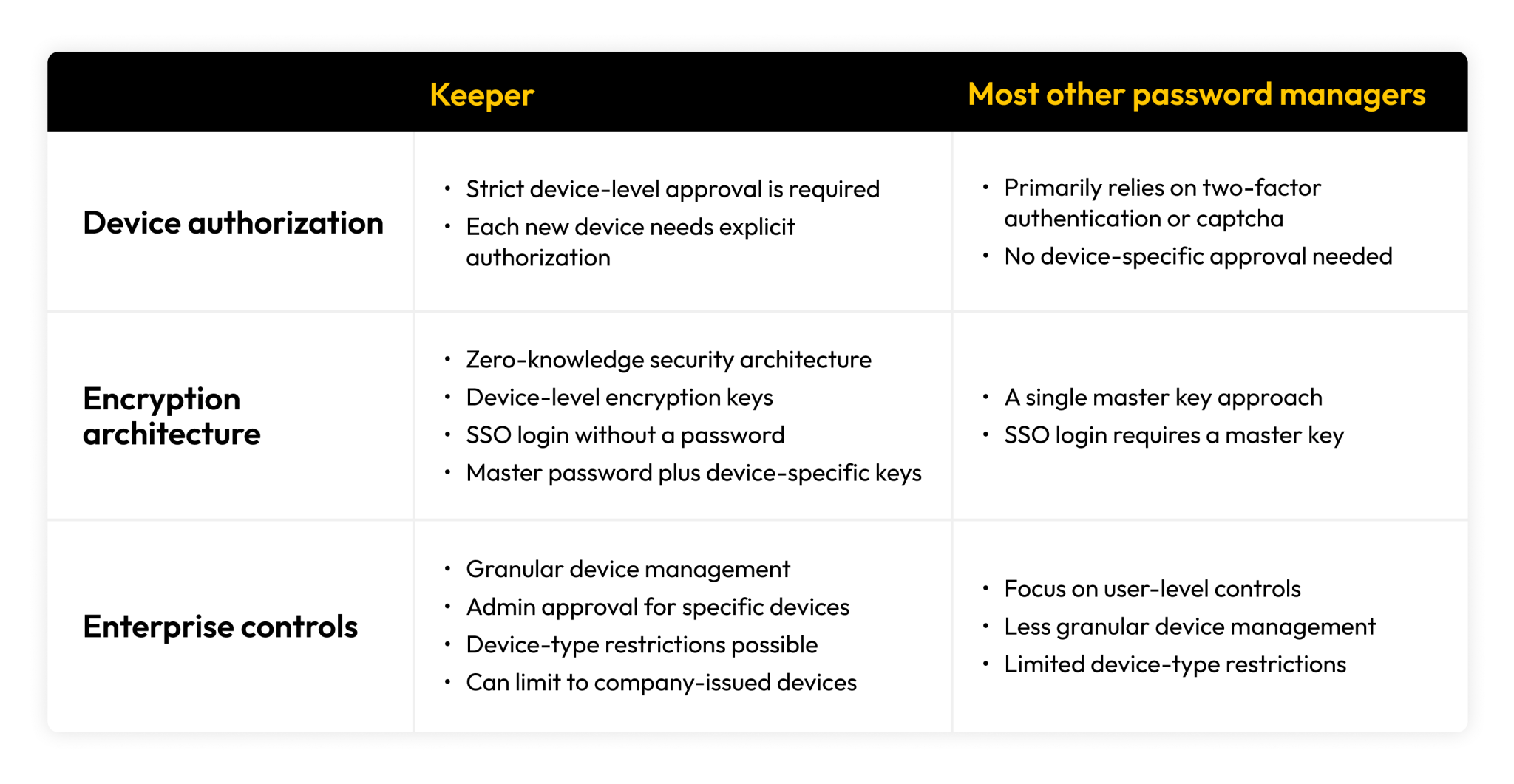
Device authorization model
Unlike most other password managers that typically rely on 2FA without device-specific approval, Keeper uses strict device-level approval. This requires that each new device be explicitly authorized, making Keeper more secure against unauthorized device access.
Encryption architecture
Keeper uses a zero-knowledge security architecture with device-level keys. Each device has its own encryption key in addition to the master password. This differentiates Keeper from most competitors, which use only a single master password.
Enterprise controls
Keeper offers more granular device management for organizations with multiple users and multiple devices. Administrators can approve or reject specific devices and enforce device-type restrictions (e.g., only company-issued devices). Most password management competitors focus more on user-level rather than device-level controls.
Get peace of mind over your passwords with Keeper
Keeper’s unique security architecture, which uses device-level approval and zero-knowledge encryption, is superior to other password managers. By requiring both the correct password and explicit authorization for each new device, Keeper makes unauthorized access significantly more difficult. This helps protect against common cyber threats, such as password spraying, brute force attacks and social engineering.
Source: Keeper