News
In a 2023 study commissioned by Datto, Forrester Consulting surveyed 421 cloud strategy decision-makers at small and medium-sized businesses (SMBs) about their organizations’ current IT infrastructures and how leveraging external partnerships streamlines operations, saves money and contributes to organizational success.
Although the past five years have posed many different challenges for small businesses, the most notable among these organizations has been the move to the public cloud. While the 2020 pandemic accelerated this move as businesses adapted to work-from-home needs, it was not the primary reason for its adoption. In fact, many organizations were already looking to the public cloud for potential cost savings and as a solution to meeting tougher global compliance regulations prior to the pandemic shutdowns.
Today this adoption continues, and according to the study’s findings, many IT professionals expect 61% of their workloads to be in the cloud within the next two years. Interestingly, the other 39% of infrastructure and applications were still expected to operate on-premises, with many respondents not expecting a full cloud transformation. In this blog we will further examine what has led to this adjustment.
Public cloud: expectations vs. reality
Streamlining operations and increasing speed, modernizing existing apps and services, and cost-effectiveness are three of the top expectations businesses cite when positioning a transition of their IT infrastructure into the cloud. For many survey respondents, it appears the cloud has had less of an impact than once thought.
Potential cost-effectiveness was cited as the primary decision for the transition by 93%. But for many SMBs migrating to the cloud is a significant undertaking, and our study found only 47% of respondents said their organization had seen greater cost optimization. Additionally, respondents cited other challenges that have offset the benefits of migration. Only 33% reported seeing increased speed of setup or buildouts and only 31% saw improved ability to meet compliance regulations. With cloud service costs continuing to rise, more SMBs will need to consider the expected benefits of migration. Furthermore, many organizations will need to ask if this lackluster performance is due to the cloud or the limitations of their IT organizations.
Complex technology and a skill set challenge
SMBs had painted the cloud as a “promised land,” and at first glance this study shows us that few of the cloud’s expectations have been met. The question we ask is — is it the capabilities and structure of the cloud that has not met our expectations or is it something else?
The harsh reality is that cloud infrastructures are complex, and as mentioned earlier, 39% of many SMBs’ infrastructure remains on-prem, meaning that many of these cloud migrations are hybrid, leading to even further complexity. Decision-makers noted that one of their biggest challenges was maintaining interoperability between cloud and on-prem infrastructures. This creates a complex disjointed hybrid environment and opens concerns around security.
Yet 52% of the respondents stated that a lack of in-house staff expertise is challenging their organization’s operations in the public cloud and 74% felt that their organization does not have the capability or capacity to train employees as the cloud grows in complexity. This may be the answer to why cloud migrations are not meeting business expectations.
Leveraging partnerships
Managing both public cloud and on-premises infrastructures is becoming increasingly complex and expensive for SMBs. The cloud can only enable transformative outcomes if organizations are willing to undertake careful groundwork and planning and accept expert advice. Without a skilled and experienced staff, SMBs will continue to struggle to get the most out of their hybrid deployments. Leveraging partnerships with managed service providers (MSPs) will enable SMBs to manage their hybrid IT environments with skilled partners, enhance performance, increase security and keep their costs more predictable.
To learn more, download the Forrester study “SMBs: The Future Is Co-Managed.”
Source: Datto
Sophos is excited to announce a new partnership with Cysurance, a next-generation risk mitigation company that insures, warranties and certifies security solutions.
The partnership provides unique, fixed-price cyber insurance to U.S.-based organizations using Sophos Managed Detection and Response (MDR). The policies are the first of their kind to recognize organizations for having a layer of threat detection and response services.
As cyberthreats increase in complexity and velocity, MDR is quickly becoming an essential requirement for organizations to manage their cybersecurity posture. Most organizations simply can’t keep up with the evolving threat landscape, as evidenced by the 59% of U.S. security defenders who say today’s threats are too advanced for their organizations to deal with on their own.
Cysurance recognizes this and the value that Sophos’ 24/7 threat detection and response experts provide to mitigate cyber risk. Cysurance’s fixed-price coverage is a testament to Sophos’ MDR capabilities and the effective security services we provide to organizations.
Kirsten Bay, co-founder and CEO at Cysurance, says:
“The lack of comprehensive and integrated security strategies largely explains why cyber insurance policy fees are rising while coverage limits are declining. Those without defense in depth strategies are at increased cyber risk. However, cybersecurity is a manageable challenge, and Sophos can help. Together, we’re focused on helping organizations take responsible steps to implement proper cybersecurity to protect their business and digital assets. Sophos’ proven MDR solution allows Cysurance to offer a range of best-in-class coverage plans that reward customers for their smart cybersecurity investments.”
The Cysurance policies for Sophos MDR users supports all industry sectors in the U.S., regardless of number of employees or endpoints. Four plans, ranging from $275,000 to $3.2 million in total coverage – including ransomware coverage – are available. To learn more and sign-up, visit https://enroll.cysurance.com/sophos/
This is the latest in a series of cyber insurance partnerships for Sophos, which already this year announced deals with Cowbell and Measured Analytics and Insurance. Its partnership with Cysurance uniquely benefits organizations using Sophos MDR, one of the industry’s most widely used services with more than 17,000 customers.
Source: Sophos
Combining the best of Kaseya Connect and DattoCon, the first joint event since the acquisition of Datto will showcase technical insights, solutions updates and growth strategies with the European IT community.
Kaseya, the leading global provider of unified IT management and cybersecurity software for managed service providers (MSPs) and small to mid-size businesses (SMBs), has commenced its first combined Kaseya DattoCon Europe event taking place at the Convention Centre Dublin, Ireland from 26-28 June.
Bringing together more than 1,000 IT industry leaders over three days of sessions, exclusive certified trainings and networking, the event is a key opportunity for attendees to learn in-depth about Kaseya’s IT service solutions – including the recently launched IT Complete 2.0, the industry’s only purpose-built platform for multi-functional IT professionals.
Leading industry experts will discuss current trends in IT and cybersecurity and share impactful growth strategies for the IT community. A plethora of networking opportunities, actionable sales and marketing advice and hands-on, expert-led product training complete the three-day programme.
New capabilities in IT Complete 2.0
“Organisations ‘powered by Kaseya’ are the most successful in their industries,” said Fred Voccola, CEO, Kaseya. “IT Complete is already the most integrated and comprehensive suite of solutions for IT professionals. With this latest version, we’ve taken its capabilities to the next level by adding another 350 integrations, including all Datto products. We are proud to present IT Complete 2.0 to our European partners.”
- Following the acquisition of Vonahi, Kaseya has added automated network penetration testing to its Security Suite and lowered the pricing for Vonahi solutions by 10%.
- Kaseya has also expanded its MSP Enablement Suite to include the audIT automated sales presentation solution, with five free licenses for every customer.
- The ConnectBooster integration is now available to European partners, simplifying billing processes for MSPs.
Other product updates within IT Complete 2.0 include:
- Datto Endpoint Backup for Servers, a highly anticipated solution giving MSPs the option to protect servers directly to the secure Datto Cloud – no local appliance or IT hands required – while still including all the advanced features Datto BCDR users have come to expect.
- Microsoft 365 Management in Datto RMM, a new feature combining user management and device management to simultaneously give new users everything they need during the onboarding phase. It also revokes access at once when they are offboarding.
- The relaunched Datto Networking Appliance (DNA), a high-performance network router for ‘always on’ Internet connections thanks to fully integrated 4G LTE failover.
New Kaseya Business Services for European customers
Kaseya is also growing its Remote IT and Security Management (RITSM) training programme with a new Professional course. The new 40-hour certification course is designed to address the growing demand for tech talent, with modules covering critical MSP functions such as remote IT and security management, working in sandbox environments and customer service skills.
Key sessions at Kaseya DattoCon Europe included:
- Fred Voccola, CEO, Kaseya will deliver a keynote on the state of the MSP and SMB industry and opportunities ahead.
- Dr. Lior Zoref, Researcher, Advisor, TED Speaker, Former Vice President at Microsoft and author of the best-selling book, Mindsharing: The Art of Crowdsourcing Everything will delve into using collective intelligence to make better decisions and find new solutions to business challenges.
- Ranjan Singh, Chief Product Officer, Kaseya will give an overview of the latest Kaseya and Datto product innovations.
- Jason Manar, CISO, Kaseya will discuss the real threats that keep CISOs up at night.
- Nadir Merchant, General Manager and CTO, IT Glue will present integrated IT management with Kaseya One.
Source: Kaseya
Keeper Security has released its latest research, Password Management Report: Unifying Perception with Reality, which assesses the password habits of individuals across the United States and Europe.
For the report, Keeper surveyed over 8,000 people. The survey focuses on the differences between what people say they do to ensure their cybersecurity, and what they actually do. The survey revealed that many people are overconfident in their overall security health and that there is a clear disconnect between people’s actions and their perception. The report also found that older generations are more likely to practice good password security than their younger peers. Overall, cybersecurity and password best practices were revealed to be an enigma. Individuals think they are protected, but based on the actions those same individuals take, that confidence may be misplaced.
People Overestimate Their Security
The majority (51%) of respondents in the survey reported that “Cybersecurity is easy to understand.” Additionally, a full quarter of respondents reported that not only was cybersecurity an easy concept to grasp, but they actively take steps to protect themselves. Only 10% of all respondents admitted to feeling overwhelmed by cybersecurity. For anyone who works in the field, that may jump out as a shockingly low number. After all, new threat vectors are being exposed every day, major ransomware gangs dominate newscycle on a regular basis and the sheer number of breaches has grown at a seemingly exponential rate. How then, could people feel so confident in their security posture?
The answer, worryingly, could be simple ignorance. For example, the survey found that only 25% of people are using strong, unique passwords for all their accounts, which leaves 75% of individuals with dangerously weak password practices. A third of respondents (34%) use strong passwords but repeat variations of them (for example Hockeyfan123 and 123Hockeyfan), a practice which is vulnerable to credential-stuffing attacks. Finally, a jaw dropping 14% of all respondents use simple, repeated passwords across their accounts.
Creating and remembering hundreds of unique passwords is a mammoth task, and one most people neither have the time or energy to tackle. As a result, people tend to ignore advice from cybersecurity experts, government bodies and other experts, instead choosing to imagine that cyber risk does not apply to them.
Older Demographics Have Better Password Management
Not all individuals are hopelessly vulnerable, and contrary to popular belief, it is not the younger generation that has the best password management practices. In fact, 29% of Baby Boomers (aged 59-77 years) use strong, unique passwords versus only 20% of Gen Z (aged 16-26 years) respondents.
Older generations may be more in tune with the reality of sophisticated and ever present cyberthreats, or they may just have more to lose should a breach occur. Either way, we as an industry need to do more to educate users and improve their understanding of the tactics that can help people avoid a costly attack.
Bridging the Knowledge Gap
While advice on cybersecurity is abundant, Keeper’s survey reveals it is too overwhelming for over a third of people. Although respondents claim that strong passwords are the most effective way for personal cybersecurity, the majority do not follow the industry-recommended password protection practices in their day-to-day lives. Keeper’s findings show that three-quarters of people fail to follow password best practices, yet almost everyone considers cybersecurity to be easy to comprehend.
Cybersecurity is essential to effectively protect our increasingly dependent online presence, yet many ignore the value of proper digital safety protocols. People should confront their overconfidence, fear, and apathy to secure their devices, identities, and accounts. A first step is using a password manager like Keeper to create and store strong, unique passwords and passkeys for all of your accounts.
Source: Keeper Security
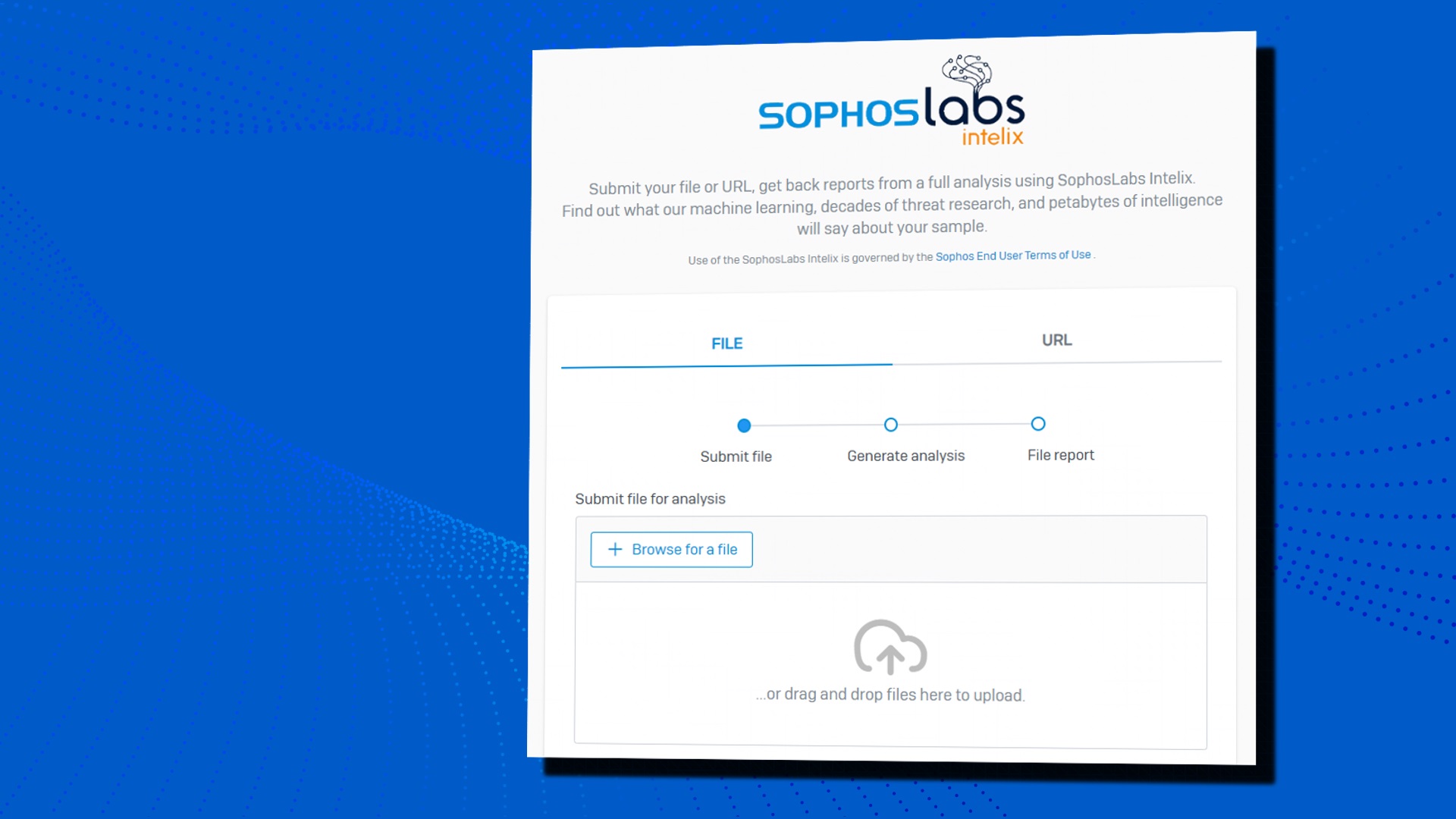
The SophosLabs Intelix portal is an excellent resource for staying informed about the latest cyber threats.
We are pleased to announce the launch of the SophosLabs Intelix portal, a web-based interface allowing anyone to submit suspicious threat artifacts for threat intelligence and classification. This free service is an excellent resource for individuals, researchers, and organizations looking to stay up to date with the latest cyber threats.
Intelix provides detailed, explainable, and proven threat intelligence, allowing people to make informed decisions. Submitted files and URLs undergo detailed threat analysis, including cloud lookups, static analysis, and dynamic analysis (cloud sandboxing).
From the rich reports generated, users can understand the verdict and the features and/or behaviors that led to the verdict.
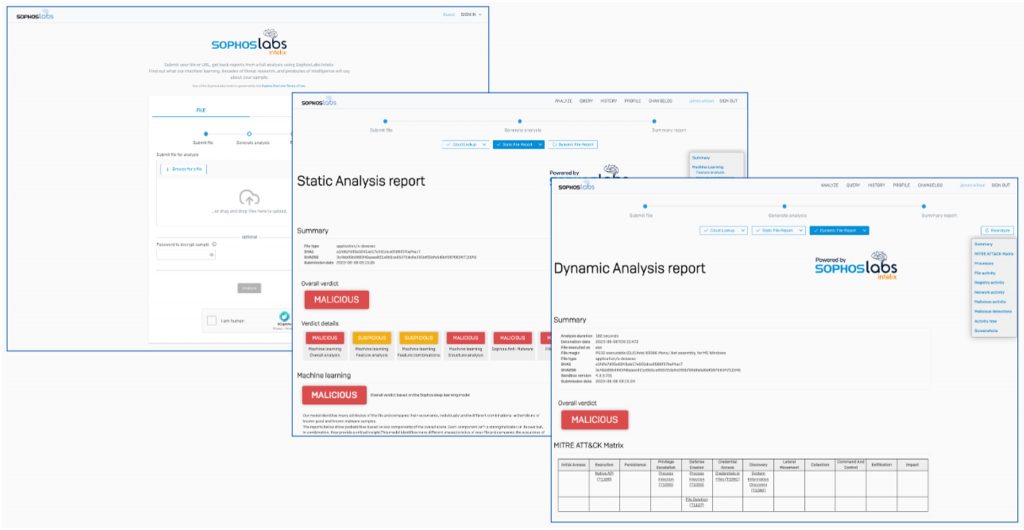
The Intelix portal showcases the power of the SophosLabs detection technologies and the Sophos X-Ops threat intelligence platform used by Sophos products.
If you’re a registered Sophos customer, the Intelix Portal offers additional features. By signing in with your Sophos ID, you can access the results of all previous analyses for up to one year. You can also instantly escalate an analysis to Sophos Support or SophosLabs for human review of the verdict.
The SophosLabs Intelix portal is an excellent resource for staying informed about the latest cyber threats. Whether you’re a researcher, an individual, or a business, the portal provides a wealth of information to help you stay one step ahead of cybercriminals. Intelix is also available in the AWS Marketplace and for OEM use cases.
Try it out today or visit Sophos.com/Intelix to learn more.
Source: Sophos
Cybercriminals often use phishing emails to get you to click on malicious links or attachments. Clicking on these scams can trigger a malware infection that places all your sensitive data at risk of becoming compromised. Before deciding to click on an attachment, you should make sure it’s safe to open.
You can check if an email attachment is safe by having antivirus software scan the attachments in your emails, double-checking who the sender is and not opening any attachments that are marked as spam. Keep reading to learn more about unsafe email attachments and how you can keep yourself from falling victim to them.
The Risks of Opening Unsafe Email Attachments
One of the biggest risks of opening unsafe email attachments is having your device become infected with malicious software called malware. When malware is successfully installed onto your computer, it can log your keystrokes, take screenshots of your activity and compromise your computer’s camera or microphone. All of this data is then sent to the cybercriminal who targeted your device.
Cybercriminals use malware to steal your sensitive data such as your account login information or credit card numbers. Depending on the type of malware that is installed on your computer, what the cybercriminal can get away with varies.
3 Tips To Check If an Email Attachment Is Safe
Here are tips you can use to check if an email attachment is safe.
Double-check who the sender is
Checking the sender’s email and name is a very important step to take before deciding to click on an email attachment. However, you cannot just rely on the sender’s name to verify an email. Many cybercriminals spoof the names of senders to make it look like they’re coming from a trusted source, when in reality, they’re not. Even if you use an email provider like Gmail, which released an update that shows a blue checkmark next to “verified” senders, don’t trust it fully. Cybercriminals have already found a way to exploit Gmail’s blue checkmark verification.
Instead, rather than clicking on the attachment, contact the sender yourself through another communication method to confirm that it is really the person or organization who sent it.
Don’t open any email attachments that are marked as spam
Many email providers flag spam emails and automatically place them into your spam folder. If your email provider does this, ensure you don’t open any attachments from those flagged emails as they’re likely to be phishing attempts.
Use antivirus software to scan attachments
Antivirus software is a type of program you install on your computer that detects, isolates and removes viruses and other malware before cybercriminals can successfully infect your computer. An added benefit to some antivirus software is that it can also scan the attachments in your email to check if they’re safe. If they’re not safe, your antivirus software will let you know.
Which Email Attachments Are Generally Safe To Open?
Some email attachments that are considered generally safe to open are:
- .JPEG
- .JPG
- .PNG
- .GIF
- .TIF
- .TIFF
- .MPEG
- .MPG
- .MP3
- .MP4
- .WAV
- .MOV
While these types of attachments are considered safe, we still recommend being cautious about clicking them, especially when they’re unsolicited or from an unknown sender.
Which email attachments are less safe to open?
Some email attachments that are considered less safe to open include:
- .EXE
- .DOC
- .DOCX
- .XLS
- .XLSX
- .PPT
- .DMG
- .ZIP
- .RAR
- .HTML
Before deciding to click on these types of attachments, we recommend taking precautions such as using antivirus software and confirming the sender. If it’s a file from a sender you were expecting, there’s most likely nothing to worry about.
What To Do If You Click an Unsafe Email Attachment
Here are the steps you can take if you accidentally click on an unsafe email attachment.
1. Disconnect your device from the internet
One of the first things you need to do is disconnect your device from the internet. Malware can spread through your WiFi and infect other devices connected to the same network if it remains connected. Disconnecting your device from the internet can also lessen the amount of damage the malware causes.
2. Change your passwords and enable MFA
After disconnecting your device from the internet, you should use a different device to change the passwords for all of your accounts, most importantly, your email. You can use a password manager to help you change the passwords quickly. Keeper Password Manager offers a free 30-day trial that you can start using right away. A password manager will help you create strong, unique passwords for each of your accounts and securely store them so you never forget them.
Along with changing your passwords, enable Multi-Factor Authentication (MFA). MFA adds an extra layer of security to your account to prevent anyone but you from being able to access it. An added benefit to using a password manager is that it can also store your 2FA codes and autofill them when you log in.
3. Scan your device for viruses and other malware
Most antivirus software programs work without having to be connected to the internet. If you already have antivirus installed on your infected computer, run a scan so the malware is removed from your device. If you don’t already have antivirus software, you’ll need to connect to the internet and download an antivirus program.
Some malware and viruses may prevent you from being able to download antivirus software. If this is the case, you’ll need the help of a professional. If you already have everything on your device backed up, another approach you can take is completely wiping your computer. Remember, wiping your computer will remove everything from it, including your files, pictures and other data, so only take this approach if you know all of your data is backed up.
4. Keep an eye out for suspicious activity
After taking the steps above, it’s important to keep an eye on your accounts. You never know what the cybercriminal could have gotten away with in a short period of time. Watch out for any suspicious activity such as purchases you didn’t make or unusual login attempts on any of your accounts.
Protect Yourself From Unsafe Email Attachments
One of the best ways you can stay safe from falling victim to phishing email scams is by knowing how to spot them. This means knowing the red flags to look for, like unsolicited email attachments. As a preventative measure, always use strong passwords on each of your accounts and always have MFA enabled. The stronger your cyber hygiene is, the safer you and your data will be, even if you accidentally fall for a scam and click on an unsafe email attachment or link.
Start a free 30-day trial of Keeper Password Manager today to start protecting your accounts and data from cybercriminals.
Source: Keeper
Sophos rated 4.7/5 in Network Firewalls. Customers have recognized Sophos for the second consecutive year.
Over the last two years, customers have recognized Sophos with an average overall rating of 4.7/5 based on 462 reviews, as of March 31, 2023. What’s more, Sophos is the only vendor to be named a Customers’ Choice for BOTH the 2021 Endpoint Protection Platforms and 2023 Network Firewalls market categories. In addition, we are the only vendor to be named a Customers’ Choice for the Network Firewalls Public Sector, Gov’t, Edu segment.
Based solely on independent customer reviews that have been rigorously evaluated by Gartner, we believe this recognition is a testament to the unparalleled value that Sophos Firewall delivers thanks to its industry leading protection, superior visibility, and easier management.
Access the full report here.
Gartner Peer Insights shares the independent voices of verified enterprise customers. Recent feedback on Sophos Firewall includes:
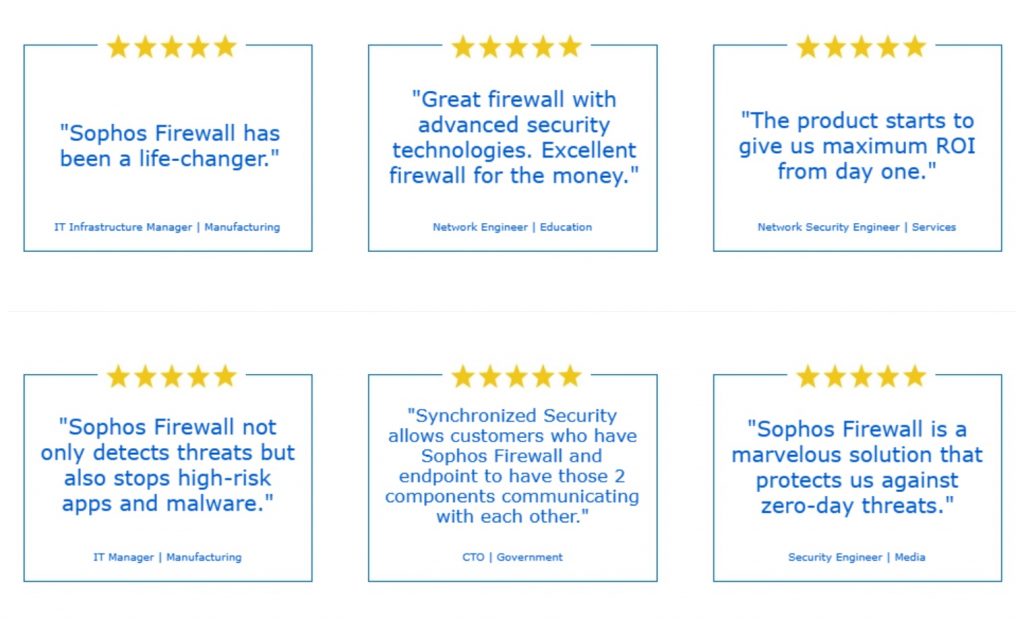
These are just a few of the hundreds of Sophos network firewall customer reviews available on the Gartner Peer Insights site. I would like to take this opportunity to thank our customers who have shared their feedback; we truly appreciate your time and your trust.
Sophos Firewall optimizes your network protection
Sophos Firewall delivers the ultimate value for your network security investment by providing powerful protection and performance for even the most demanding network environments, with benefits you just can’t get with any other firewall:
Expose hidden risks – Sophos Firewall does a far better job exposing hidden risks than other solutions through a visual dashboard, rich on-box and cloud reporting, and unique risk insights.
Block unknown threats – Sophos Firewall makes blocking unknown threats faster, easier, and more effective than other firewalls with advanced high-performance TLS inspection and a full suite of advanced protection capabilities that are very easy to set up and manage.
Automatically respond to incidents – Sophos Firewall with Synchronized Security automatically responds to incidents on the network thanks to Sophos Security Heartbeat, which shares real-time intelligence between your Sophos endpoints and your firewall.
Sophos Firewall is just part of the best cybersecurity ecosystem
Sophos Firewall is tightly integrated with our full line of secure access network security products, including Sophos Switches, Wireless, SD-RED and ZTNA – along with the rest of the Sophos cybersecurity ecosystem of endpoint, XDR, MDR, and messaging security solutions.
Whether you want to manage it yourself with our easy and integrated Sophos Central cloud manager, or have us manage it for you with our 24/7 managed threat detection and response service, we’ve got you covered.
Source: Sophos
Many organizations know they need to improve their approach to cybersecurity or grow their security ecosystem, but they don’t know where to begin. If this sounds familiar, you’re in the right place. Getting started with cybersecurity or bolstering your existing infrastructure can often be an arduous process. We’re here to help.
Fortra Offers a Comprehensive Approach to Cybersecurity
Fortra is ready to support your organization’s unique needs as you work to enhance your security posture on multiple fronts. We offer a robust security portfolio that spans both infrastructure and data protection to provide a comprehensive approach from a single trusted partner.
Vulnerability Management
Identify, evaluate, prioritize, and report on security weaknesses that may be putting your organization at risk. Easy to deploy, simple to use, and scalable, these solutions help streamline your security efforts in these areas:
- Vulnerability Management
- Web Application Scanning
- Application Security Testing
Offensive Security
Prioritize the risks that truly pose the biggest threat to your infrastructure. Monitor for weaknesses in the infrastructure and defensive processes of your organization with tools that help you evaluate the potential consequences of cyberattacks:
- Automated Pen Testing
- Adversary Simulations
- Red Team Operations
Data Protection
Protect sensitive information and comply with regulatory requirements. Identify and classify data and root out policy violations by leveraging:
- Data Classification
- Rights Management
- Endpoint DLP
Digital Risk Protection
Safeguard critical digital assets through expert-curated threat intelligence and complete mitigation against brand impersonation, data leakage, social media threats, account takeover, and other digital risks in one complete solution. This encompasses:
- Account Takeover Protection
- Social Media Protection
Secure File Transfer
Simplify, secure, and automate enterprise file transfer through a single intuitive interface that enables employees, partners, and customers to move data easily without the need for programming skills. Solutions span:
- Managed File Transfer
- Electronic Data Interchange (EDI)
- File Acceleration
Email Security
Keep emails, brands, and data protected with minimal disruption. Reduce the chance of cyberattacks starting with inbound email as well as outbound data loss prevention with these capabilities:
- Brand Protection
- Business Email Compromise (BEC)
- Secure Email Gateway
Source: Fortra
While some people have returned to working in an office, it seems that the majority have not. Looking back, the pandemic will likely have been a turning point for many things around the world, and the rhythms of office-centered worklife will be something that will never return to the old ways.
With this increased flexibility employees are not just working from home behind consumer-grade Wi-Fi routers; they are also spending part of the day at the park or coffee shop, or perhaps even having a “working holiday.” Those in charge of protecting enterprise assets have to assume these endpoints are always in hostile territory.
Even before the pandemic, organizations working toward improving their security maturity were often trying to “push left.” What is pushing left? At its most basic level it means moving things closer to the start. It originates from software development where the stages of the development process are conceptualized from left to right, left being the beginning. In applied security we also use the term “pushing left,” but rather than referring to the software development process we are referring to the attack chain, which moves from reconnaissance on the left through action (exfiltration or other attacker goal) on the right.
For many years, the most comprehensive security strategies have involved defense in depth. The idea is that not all technologies are suitable for detecting a given threat type, so it is best to deploy them in layers. These layers often directly correspond to how far “left” something is in the attack chain. If you can detect something at the network border through your firewall, email, or web filters, you have contained the threat before it has any negative impact on operations.
Ideally you want to detect and block an attacker as far left as possible, i.e., as early as possible. Pushing detections left also alerts security analysts that an intrusion may be underway, initiating more focused threat hunting to anticipate gaps in defenses your attacker may be attempting to exploit.
For employees at the office, you can centralize control of these defenses and provide optimum protection. The question is, are you able to provide the same protection for remote workers regardless of their location? Can you monitor and respond to threats being detected on those assets when they are out of the office? As many have observed, this did not work as well as we would have liked when we all went into lockdown, many of us without a plan.
While there are still many benefits to monitoring the network when you have control of it, including reduced endpoint overhead and the ability to keep threats at a distance from sensitive assets, we need to ensure we can take as much of this protection as possible with us when we are out and about.
We must ensure not only that protection is optimized, but also that we don’t lose our ability to monitor, detect, and respond to attacks targeting these remote assets. Most organizations have moved to utilizing EDR/XDR solutions (or plan to in the very near future) , which is a great start, but not all solutions are comprehensive.
In the remote-work era, insufficiently protected remote users can encounter plenty of issues – malicious URLs and downloads, and networks attacks, to name only the most mundane – that in the Before Times would have been handled by machines guarding the corporate “fort.” The biggest missing components when users are “outside the fort” are HTTPS filtering and web content inspection of the sort that is typically implemented within next-generation firewalls. When you add these technologies to pre-execution protection, behavioral detection, machine learning models, client firewalls, DLP, application control, and XDR, you are starting to look at a comprehensive stack of defenses for attackers to overcome – even if the endpoints themselves are now free-range.
For initiatives like zero trust network access (ZTNA) to be effective, we must not only wrap the applications we interact with, but we must also wrap the endpoints that connect to them. Simple checks like whether the OS up-to-date and whether it has security software installed may be a good start, but not all protection is created equal.
With most devices being connected to the internet whenever they’re in use, we can leverage the power of the cloud to help provide ubiquitous protection and monitoring. Modern security solutions must assume the endpoint device or phone is in a hostile environment at all times. The old idea of inside and outside is not only outdated, it’s downright dangerous.
Source: Sophos
These Apps -Known as Fleeceware- Take Advantage of App Store Policy Loopholes and Coercive Tactics to Overcharge Users for AI Assistants.
Sophos, a global leader in innovating and delivering cybersecurity as a service, today announced that it had uncovered multiple apps masquerading as legitimate, ChatGPT-based chatbots to overcharge users and bring in thousands of dollars a month. As detailed in Sophos X-Ops’ latest report, “FleeceGPT’ Mobile Apps Target AI-Curious to Rake in Cash,” these apps have popped up in both the Google Play and Apple App Store, and, because the free versions have near-zero functionality and constant ads, they coerce unsuspecting users into signing up for a subscription that can cost hundreds of dollars a year.
“Scammers have and always will use the latest trends or technology to line their pockets. ChatGPT is no exception. With interest in AI and chatbots arguably at an all-time high, users are turning to the Apple App and Google Play Stores to download anything that resembles ChatGPT. These types of scam apps—what Sophos has dubbed ‘fleeceware’—often bombard users with ads until they sign up for a subscription. They’re banking on the fact that users won’t pay attention to the cost or simply forget that they have this subscription. They’re specifically designed so that they may not get much use after the free trial ends, so users delete the app without realizing they’re still on the hook for a monthly or weekly payment,” said Sean Gallagher, principal threat researcher, Sophos.
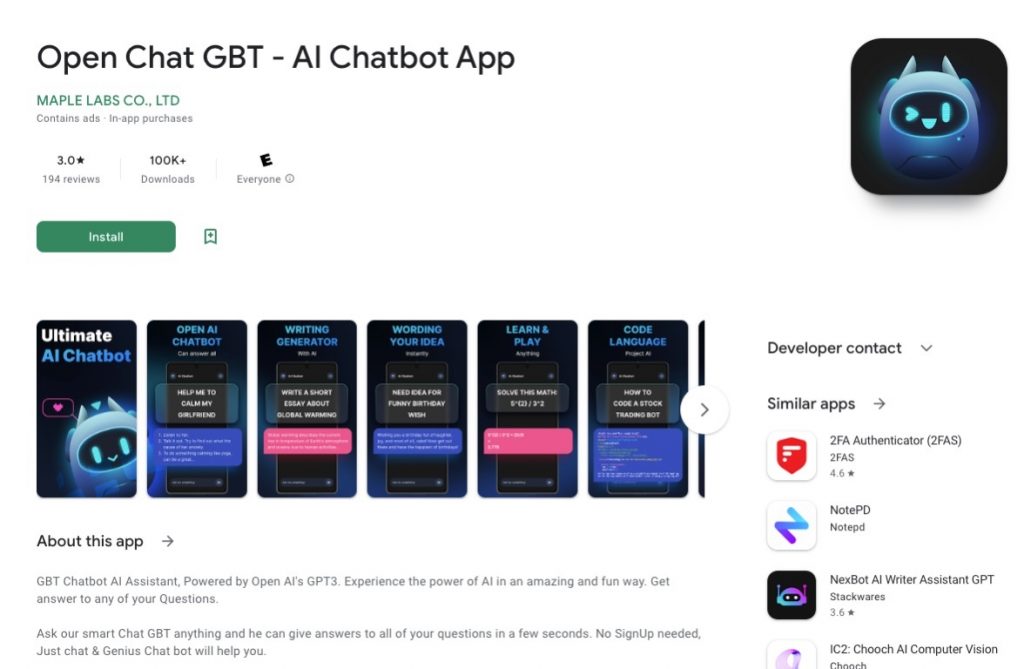
In total, Sophos X-Ops investigated five of these ChatGPT fleeceware apps, all of which claimed to be based on ChatGPT’s algorithm. In some cases, as with the app “Chat GBT,” the developers played off the ChatGPT name to improve their app’s ranking in the Google Play or App Store. While OpenAI offers the basic functionality of ChatGPT to users for free online, these apps were charging anything from $10 a month to $70.00 a year. The iOS version of “Chat GBT,” called Ask AI Assistant, charges $6 a week—or $312 a year—after the three-day free trial; it netted the developers $10,000 in March alone. Another fleeceware-like app, called Genie, which encourages users to sign up for a $7 weekly or $70 annual subscription, brought in $1 million over the past month.
The key characteristics of so-called fleeceware apps, first discovered by Sophos in 2019, are overcharging users for functionality that is already free elsewhere, as well as using social engineering and coercive tactics to convince users to sign up for a recurring subscription payment. Usually, the apps offer a free trial but with so many ads and restrictions, they’re barely useable until a subscription is paid. These apps are often poorly written and implemented, meaning app function is often less than ideal even after users switch to the paid version. They also inflate their ratings in the app stores through fake reviews and persistent requests of users to rate the app before it’s even been used or the free trial ends.
“Fleeceware apps are specifically designed to stay on the edge of what’s allowed by Google and Apple in terms of service, and they don’t flout the security or privacy rules, so they are hardly ever rejected by these stores during review. While Google and Apple have implemented new guidelines to curb fleeceware since we reported on such apps in 2019, developers are finding ways around these policies, such as severely limiting app usage and functionality unless users pay up. While some of the ChatGPT fleeceware apps included in this report have already been taken down, more continue to pop up—and it’s likely more will appear. The best protection is education. Users need to be aware that these apps exist and always be sure to read the fine print whenever hitting ‘subscribe.’ Users can also report apps to Apple and Google if they think the developers are using unethical means to profit,” said Gallagher.
All apps included in the report have been reported to Apple and Google. For users who have already downloaded these apps, they should follow the App or Google Play store’s guidelines on how to “unsubscribe.” Simply deleting the fleeceware app will not void the subscription.
Learn more about these scam ChatGPT apps and how to avoid them in ’FleeceGPT’ Mobile Apps Target AI-Curious to Rake in Cash on Sophos.com.
Source: Sophos
With the threat landscape expanding and criminals taking advantage of security gaps, organizations are turning to controls that can help them limit their exposure. Among other controls, penetration testing stands out because it simulates attackers’ malicious activities and tactics to identify security gaps in business systems or applications. A penetration test aims to understand what vulnerabilities are in business systems, how they could be exploited, and the potential impact if an attacker were successful. Because pen tests thoroughly investigate vulnerabilities, the scope of each pen test must be limited and may differ from test to test. Pen tests take on two different types of perspectives: internal and external. In this blog, we will examine what internal and external penetration testing is, who conducts these tests, and why organizations need both.
Getting Past the Perimeter: External Pen Testing

The 2023 Pen Testing Report revealed that 77% of security professionals pen test their external infrastructure. Essentially, external networks encompass all public-facing assets—including the internet at large. Additionally, many organizational applications, like mail servers, websites, or even customer portals maintain a connection to these external networks and can also provide a doorway from which a threat actor can pivot.
External penetration tests are typically what people think of when they hear about pen testing. These tests use the same techniques as adversaries to attempt to exploit weaknesses in an organization’s front facing perimeter or attempt to bypass them altogether with strategies like a phishing campaign or other social engineering methods.
Thinking Beyond the Initial Breach: Internal Penetration Testing
This year’s report also showed that 73% of security professionals pen test their external infrastructure. Internal penetration tests take on the role of an adversary who has already gained a foothold within the corporate network and is looking to elevate privileges to move laterally, gain further control and cause more damage. These assumed breach scenarios also deal with security gaps that such an attacker could exploit.
Internal attacks can originate from malicious insiders or compromised users like careless employees, insecure third-party vendors, and even clients or customers. Internal threats can be anything from bad hygiene habits, like weak passwords and poor access controls, to system and app misconfigurations and insecure endpoints. The Verizon 2022 Data Breach Investigations Report indicates that human errors are responsible for 13% of data breaches.
Though many think pen tests concentrate on an initial breach, it’s just as important to deploy tests that focus on what happens once someone is already inside the perimeter. Since such attacks start with internal access, they may attempt to achieve more high-value objectives including acquiring high-level privileges, compromising the Domain, or accessing other valuable assets and/or information. Because of this, it is crucial to identify and prioritize these threat vectors.
Who Should Be Conducting These Pen Tests?
Though it’s easy to think that in-house teams would handle all internal tests and external/third party teams would handle external tests, this is not the case. Both teams can conduct internal and external pen tests.
The one exception may be physical pen tests. These external tests involve attempting to gain entry to a physical facility, system, or network by exploiting weaknesses like doors, locks, cameras, or other access controls. Third parties tend to be the only teams that complete such assessments. 36% of respondents to the pen test report used third-parties for such services.
Otherwise, using both types of teams simply provides the capability to conduct more tests. Internal teams can conduct routine tests more often, while third-party services are solicited to provide a fresh prospective and different skill sets.
Creating a Holistic Pen Testing Strategy
Though organizations have to make tough choices when deciding what tests they have the time and resources to run, one of the most important criteria to consider is whether you’re balancing internal and external tests.
Only testing externally overlooks vulnerabilities that can be exploited by a malicious insider or a compromised account. With strategies like phishing more popular than ever, it’s critical to remember how easily insider access can be attained. However, only testing internally can inadvertently leave a door wide open for an attacker to get in without much difficulty.
Ultimately, by conducting both internal and external pen testing, organizations can gain full visibility into their security posture and ensure that they are adequately protected. The pen test report showed that in 2022, internal environments were regularly tested 14% less than external environments. With a gap of only 4% in 2023, it’s encouraging that this year’s pen testing report show that organizations are better understanding this balance.
Source: Core Security
Security adviser Roger Grimes once famously wrote, “To beat hackers, you have to think like them.” Grimes explained that security professionals should step into the attackers’ shoes and seek how to break into corporate systems, discover weaknesses, and create robust security countermeasures. Walking the walk of an attacker is what penetration testing is all about.
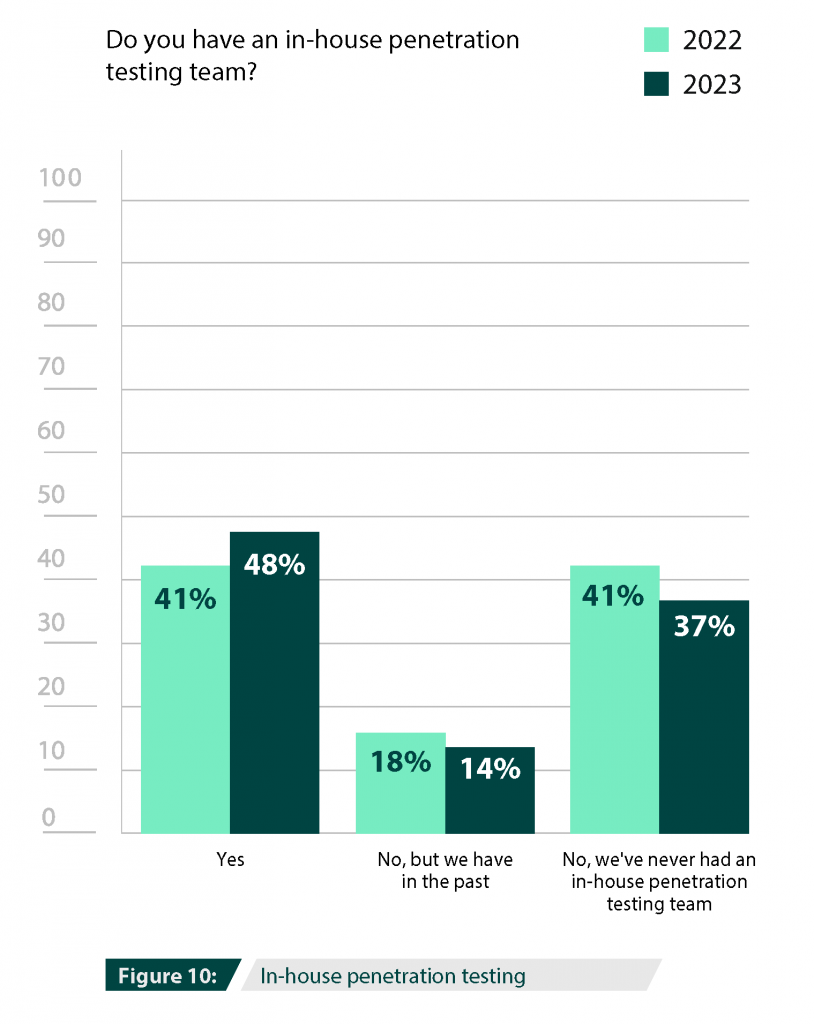
What is In-House Pen Testing?
In-house pen testing is, quite simply, when any pen testing efforts are deployed from within an organization. Instead of (or in addition to) hiring a third-party service, businesses can run their own pen tests to assess the state of their security.
Though some think a full, dedicated in-house pen testing team is needed in order to run a successful pen testing program, organizations can start small, with just one employee or security teams taking on pen testing duties. Organizations can utilize penetration testing tools that have automated features which can be used by security team members who may not have an extensive pen testing background. These tools can be used for tests that are easy to run, but essential to perform regularly, like validating vulnerability scans, network information gathering, privilege escalation, or phishing simulations.
According to the 2023 Penetration Testing Report, it’s clear organizations realize the importance of internal penetration testing since 48% of the 2023 Penetration Testing survey respondents have in-house teams. This percentage marks a 7% increase compared to the 2022 results.
Why Do Organizations Have In-House Pen Testing?
Having in-house pen-testing capabilities can quickly expand efforts, allowing for more frequent tests and coverage of a broader scope of the IT infrastructure. It also ensures that changes to the infrastructure are more efficiently assessed to ensure new security gaps aren’t created.
According to the report, organizations conduct penetration testing for multiple reasons. 69% report that they perform pen tests for risk assessment and remediation prioritization. By having internal knowledge of the organization, teams can tailor remediation plans knowing what the available resources are and their limitations. They can outline the best and most effective changes that are also achievable and help implement them.
58% reported using in-house pen testing for regulatory compliance mandates and 40% for company policy requirements. Having an in-house pen testing capabilities ensures that these standards will be met and won’t fall through the cracks. With continuous testing, organizations can far exceed the bare minimum conditions of a mandate or regulation.
Reasons for Penetration Testing
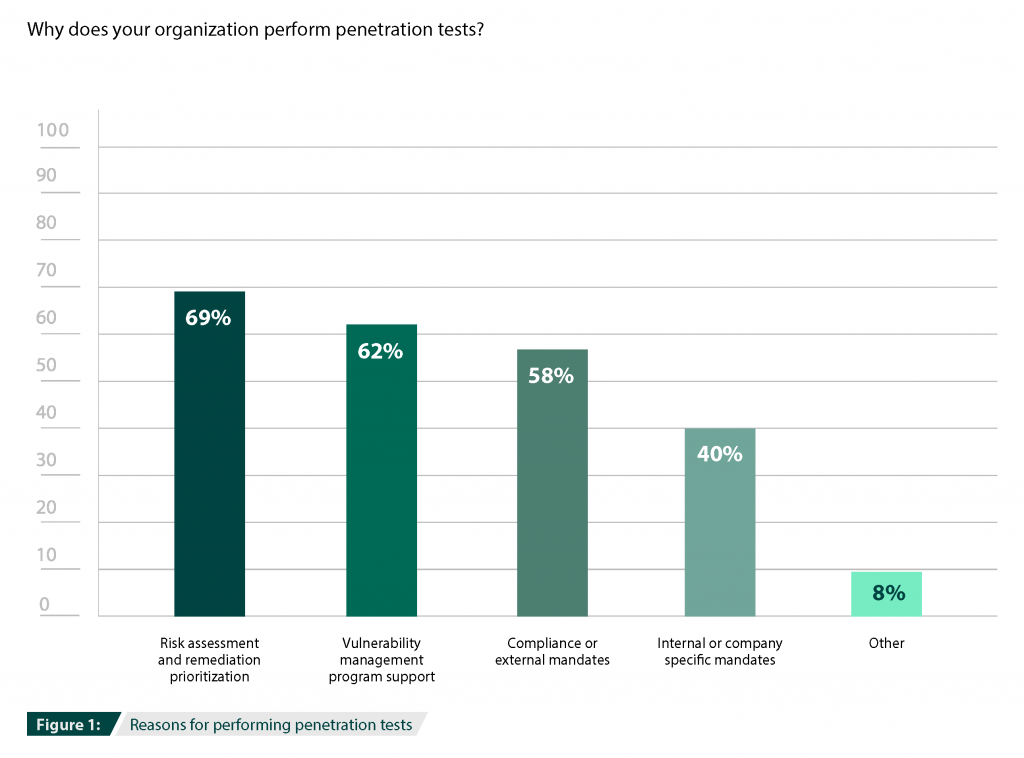
No matter the driving reason, it is essential not to pen test to check a box. Businesses should take the next step forward and take all necessary steps to mitigate identified weaknesses. A pen test program does not end with discovering vulnerabilities; a formalized program can help organizations achieve maximum coverage and impact.
Every pen test involves several steps, from scoping and intelligence gathering to threat modeling, analysis, and reporting. However, the specific goals, methodology, conditions, and targets can differ quite a bit depending on whether the organization chooses in-house or external penetration testing.
The Challenges of In-House Pen Testing
While in-house pen testing appears to be on the rise, 52% of organizations do not have an in-house penetration testing team. Many factors contribute to this finding, the most important being the lack of required talent.
The skills gap is a persistent issue in the cybersecurity industry, affecting the establishment and staffing of penetration testing teams. In fact, according to the (ISC)² 2022 Cybersecurity Workforce Study, the cybersecurity workforce gap has grown more than twice as much as the workforce, with a 26.2% year-over-year increase.
In addition, the tech and cybersecurity sectors have been massively affected by The Great Reshuffle, which created further challenges in retaining staff. In a field with so many job openings, there wouldn’t be uncommon to be more turnover and instability in any team building.
Other factors affecting the organization’s ability (or decision) to maintain a pen-testing capacity are the lack of leadership buy-in and the consequent lack of required funding. These findings, coupled with the response that there is insufficient need, may indicate a lack of perception and prioritization.
Using Tools to Deploy In-House Pen Tests
Using pen testing solutions can help organizations overcome many of these challenges. While the skills gap may prevent an organization from being able to find and hire advanced testers, security or IT professionals don’t need have much experience with pen testing if they’re aided by effective tools. An automated commercial pen testing tool, like Core Impact, can guide them through routine tests and techniques. These tools can also be deployed without adding to your headcount, making them a cost-effective way to show the benefits of in-house pen testing efforts.
Source: Core Security
Sophos has released its annual State of Ransomware 2023 report, revealing deep insights into the ransomware challenges facing businesses today based on a survey of 3,000 IT/cybersecurity professionals across 14 countries.
Attack rates remain level, but data encryption has increased
66% of organizations surveyed said they were hit by ransomware in the last year. This is the same attack rate as reported in our 2022 study, suggesting that the rate of ransomware attacks has remained steady despite any perceived reduction in attacks. The education sector reported the highest level of ransomware attacks, with 79% of higher education organizations surveyed and 80% of lower education organizations surveyed saying that they were victims of ransomware.
Data encryption from ransomware is at the highest level in four years with adversaries succeeding in encrypting data in 76% of attacks. Furthermore, in 30% of cases where data was encrypted, data was also stolen, suggesting this “double dip” method (data encryption and data exfiltration) is becoming commonplace.
The most common reported root cause of attack was an exploited vulnerability (involved in 36% of cases), followed by compromised credentials (involved in 29% of cases). This is in line with recent, in-the-field incident response findings from Sophos’ 2023 Active Adversary Report for Business Leaders report.
Paying the ransom doubles recovery costs
Overall, 46% of organizations surveyed that had their data encrypted paid the ransom and got data back. Larger organizations were far more likely to pay with more than half of businesses with revenue of $500 million or more admitting that they paid the ransom.
However, the survey also shows that when organizations paid a ransom to get their data decrypted, they ended up doubling their non-ransom recovery costs ($750,000 in recovery costs versus $375,000 for organizations that used backups to get data back).
Moreover, paying the ransom usually meant longer recovery times, with 45% of those organizations that used backups recovering within a week, compared to 39% of those that paid the ransom.
“Incident costs rise significantly when ransoms are paid. Most victims will not be able to recover all their files by simply buying the encryption keys; they must rebuild and recover from backups as well. Paying ransoms not only enriches criminals, but it also slows incident response and adds cost to an already devastatingly expensive situation.”
Chester Wisniewski, field CTO, Sophos
Mitigating the ransomware risk
Megan Stifel, executive director of the Ransomware Task Force and chief strategy officer, Institute for Security and Technology comments:
“Sophos’ latest report is a clarion reminder that ransomware remains a major threat, both in scope and scale. This is particularly true for ‘target-rich, resource-poor’ organizations that don’t necessarily have their own in-house resources for ransomware prevention, response and recovery.
One way to boost security, which is aligned with Sophos’ findings in the report, is to implement the Ransomware Task Force’s Blueprint for Ransomware Defense, a framework of 48 safeguards based on the CIS IG1 Controls. It’s past time for the private and public sector to band together and collectively fight ransomware, which is why we are excited to work with cybersecurity providers like Sophos.”
Additionally, Sophos recommends the following best practices to help defend against ransomware and other cyberattacks:
1. Strengthen defensive shields, including:
- Security tools that defend against the most common attack vectors, including endpoint protection with strong anti-exploit capabilities to prevent exploitation of vulnerabilities, and Zero Trust Network Access (ZTNA) to thwart the abuse of compromised credentials
- Adaptive technologies that respond automatically to attacks, disrupting adversaries and buying defenders time to respond
- 24/7 threat detection, investigation and response, whether delivered in-house or by a specialist Managed Detection and Response (MDR) provider
2. Optimize attack preparation, including making regular backups, practicing recovering data from backups and maintaining an up-to-date incident response plan
3. Maintain good security hygiene, including timely patching and regularly reviewing security tool configurations
About the survey
Data for the State of Ransomware 2023 report comes from a vendor-agnostic survey of 3,000 cybersecurity/IT leaders conducted between January and March 2023. Respondents were based in 14 countries across the Americas, EMEA and Asia Pacific. Organizations surveyed had between 100 and 5,000 employees, and revenue ranged from less than $10 million to more than $5 billion.
Read the State of Ransomware 2023 report for global findings and data by sector.
Source: Sophos
We’re delighted to share that Sophos Intercept X Endpoint Protection ranked as the industry best in SE Labs’ protection tests in the first quarter of 2023, achieving AAA ratings across the board. In both the Enterprise and SMB categories, we achieved the following:
- 100% rating for Protection Accuracy
- 100% rating for Legitimate Accuracy
- 100% rating for Total Accuracy
Here are the links to the latest reports: Endpoint Security: Enterprise | Endpoint Security: Small Business
Sophos Endpoint: world-leading protection against advanced threats
With decades of cyberthreat intelligence, Sophos designs endpoint protection for real-time defense against modern-day advanced attacks. With a focus on preventing attacks as early as possible, Sophos strategy is to deliver multiple layers of protection to defend the entire attack chain against the many different threat vectors that attackers use to escalate and carry out attacks.
This prevention-first approach reduces breaches and improves detection and response. These SE Labs results testify to the superior cybersecurity outcomes enjoyed by over 300,000 organizations that trust Sophos for their endpoint security.
“Sophos produced extremely good results due to a combination of their ability to block malicious URLs, handle exploits and correctly classify legitimate applications and websites”
–SE Labs
The need to simulate modern-day attacks
Reputable third-party testing is an important tool to help organizations make informed decisions about their technology stacks and security investments. However, as attacks increase in volume and complexity, meaningful results can only be achieved when the tests reflect organizations’ real-world realities.
SE Labs is one of the few security testers in the industry that simulates modern-day attack tools and the tactics, techniques, and procedures (TTPs) that cybercriminals and penetration testers use in the real world.
As Simon Edwards, CEO of SE Labs, explains:
“It is essential for organizations to be able to rely on credible, full attack chain tests that duplicate real-world scenarios. It is not only about throwing a wider range of attacks at the products, but each step of the attack must be realistic too. You can’t just make up what you think attackers are doing and hope you’re right. This is why SE Labs tracks cybercriminal behaviors and builds tests based on how attackers try to compromise victims.”
Test drive Sophos Endpoint for yourself
Sophos Endpoint secures over 300,000 organizations worldwide from active adversaries, ransomware, phishing, malware, and more. Please speak to our security advisers to discuss how we can help you, and take a test drive today.
Source: Sophos
From generating strong passwords to monitoring the security policies and practices of a company, password managers are powerful solutions that defend companies against cyberthreats and improve employee productivity.
Continue reading to learn more about why password management is critical to every organization’s cybersecurity strategy.
What is a Cybersecurity Strategy?
A cybersecurity strategy is a plan for organizations to secure their assets, reduce their cyber risk and protect against cyberthreats. An effective cybersecurity strategy incorporates multiple layers of security and has solutions in each layer to fortify an organization’s defenses.
Improving Your Cybersecurity Strategy Starts With Employees
Employees often store passwords on sticky notes, in a spreadsheet or other unencrypted electronic documents. These unsafe practices stem from the challenge of trying to remember strong, unique passwords for every online account.
When creating passwords, many employees use birthdays, addresses, names of their pets, their favorite sports team or any number of easily guessable combinations. Employees often give up trying to remember unique passwords and repeat the same password – or a version of it – across several accounts. The danger of reusing passwords is if any account is breached, then cybercriminals immediately have access to every other account that uses the same password.
Password managers are cybersecurity tools that aid employees in generating strong, unique passwords and storing them in an encrypted digital vault, accessible from any device. It removes the burden of having to remember multiple passwords and eliminates the risk of employees using weak passwords or the same password across multiple accounts, which places all company accounts and data at risk.
Make Password Management a Part of Your Cybersecurity Strategy
Here are a few reasons why businesses need to incorporate password management as a part of their cybersecurity strategy.
Provides password visibility
Most businesses have limited visibility into the password practices of their employees which greatly increases cyber risk. Password managers enable organizations to have visibility over the password hygiene and risk factors that can result in a data breach.
Provides secure password-sharing capabilities
Each user can securely and easily share password records with varying levels of permissions. Shared information is fully encrypted in transit and at rest, ensuring that the record is not exposed at any point.
Increases employee productivity
Password managers increase employee productivity as they eliminate common password-related issues such as excess time searching for passwords, resetting forgotten passwords and contacting the helpdesk for assistance in resetting a password.
A password manager allows employees to take control of their passwords and use a unique, random and high-strength password for each and every site, system and application. Every employee is provided a secure, cloud-based digital vault that stores passwords and any other critical information such as encryption keys and digital certificates. A password manager will also generate strong, random passwords and automatically fill them in for users, which saves time and frustration.
Streamlines onboarding and offboarding processes
Businesses are constantly changing with new employees starting and current employees moving departments or leaving. It’s impossible for IT teams to manually provision, maintain and log all of the activities needed to keep systems secure and meet compliance standards. As people move throughout the organization, a password manager keeps their access updated. This includes locking an account when an employee leaves and the ability to transfer their vault to a trusted admin.
Enhances SSO solutions
A password manager can enhance Single Sign-On (SSO) by covering gaps such as legacy apps or platforms that don’t function with an organization’s SSO solution.
Helps meet compliance requirements
Password managers are key to meeting global compliance standards and best practices for strong cybersecurity policies. Strong password hygiene and password management systems are integral to any company’s InfoSec policy, regardless of size or industry.
Companies can spend millions on cybersecurity, and many do, but a world-class password manager should be the first investment for formidable, proactive protection.
Source: Keeper Security
Most password managers are very secure and safe to use. Depending on the password manager in question, some offer more security than others. To fully understand the security of password managers you’ll first have to understand what a password manager is.
What is a Password Manager?
A password manager is a cybersecurity tool that aids users in generating strong, unique passwords and storing them securely in an encrypted vault. The greatest benefit of using a password manager is that users no longer have to rely on memory or insecure means of storage to remember passwords for all of their accounts. The only password they’ll have to remember is their master password, which acts as the key to enter a user’s password vault.
Are Password Managers Actually Secure?
While password managers are created to be secure, not all password managers are created equal. The reason the security of password managers has recently come into question has to do with the LastPass password manager. LastPass has been in the news a great deal because of a series of security breaches, including this latest breach.
LastPass isn’t new to breaches. In 2015, LastPass suffered an attack that exposed user email addresses and security information. It’s important to note that unlike more secure password managers, LastPass does not encrypt website URLs and other metadata, which can result in stolen information being used to target users who were a part of the breach.
While LastPass’s history may be concerning to hear, there are password managers that have never been hacked– one of many reasons that password managers are still a cybersecurity best practice recommended by industry and government experts alike. Understanding the security architecture of specific password managers can give users peace of mind that their passwords are secure. Remember, a good password manager protects user data, even in a worst case scenario.
What About Browser Password Managers?
Browser password managers differ from standalone password managers for many reasons. One reason, in particular, is that browser-based password managers are not as secure. Here are a few reasons why.
- A compromised browser will lead to compromised passwords. If your device were to be infected with spyware, a cybercriminal would be able to see all the passwords you have stored in your browser. Passwords stored in browser password managers are stored in plaintext, so about all the cybercriminal would have to do is access your browser settings to view them.
- Browsers are often left logged in. Most people don’t usually log out of their browsers because it’s simply more convenient to stay logged in. However, this poses a major security risk as it makes it easy for anyone to retrieve passwords saved to your browser by just getting their hands on your device. If your device were to get stolen, this makes your accounts even more vulnerable to becoming compromised.
Most people use browser-based password managers due to the convenience of being able to access their passwords. However, not many people realize that convenience doesn’t always mean security – making browser-based password managers a dangerous option for storing passwords.
What is the Safest and Most Secure Password Manager?
The safest and most secure password management solution is Keeper Password Manager. Keeper Security is fanatical about data protection and was built with security as its top priority from day one. Customers are always kept up-to-date on all the steps being taken to secure their data and the improvements being made to the user-friendly platform.
Keeper’s zero-trust and zero-knowledge encryption model ensures that all contents in a user’s vault are protected with multiple layers of safeguards and encryption. Keeper is also the most certified, tested and audited password security platform – holding the longest-standing SOC 2 and ISO 27001 certifications in the industry.
What differentiates Keeper from its competitors, apart from having the most security certifications, is that we implement a multi-layered encryption system. All contents in a vault are encrypted in transit and at rest, including website URLs and other metadata. This is not the case for all password managers.
Learn more about Keeper’s commitment to data protection and why it’s the most secure password management solution available. You can also get started with a free 30-day trial to begin securing your passwords with the safest and strongest password manager on the market.
Source: Keeper Security
All examples of social engineering take advantage of human nature, such as the willingness to trust others, to trick individuals into divulging sensitive information.
Despite its prevalence, social engineering can be challenging to distill into a single formula. It’s one of the reasons 82% of data breaches involve the human element.
Social engineering has become the backbone of many cyber threats, from phishing emails to smishing and vishing attacks. This blog post will outline many popular social engineering techniques and the emotions hackers use to dupe their victims.
9 Most Common Examples of Social Engineering Attacks
In no particular order, here are nine common cyber threats that leverage social engineering tactics to gain access to sensitive information. While most of these attacks occur online, several can rear their heads in physical spaces like offices, apartment buildings, and cafes.
1. Phishing
The most pervasive way of implementing social engineering, hackers will use deceptive emails, websites, and text messages to steal sensitive personal or organizational information from unsuspecting victims.
Despite how well-known phishing email techniques are, 1 in 5 employees still click on those suspicious links
2. Spear Phishing
This email scam is used to carry out targeted attacks against individuals or businesses. Spear phishing is more intricate than your average mass phishing email, as it requires in-depth research on potential targets and their organizations
3. Baiting
This type of attack can be perpetrated online or in a physical environment. The cyber criminal usually promises the victim a reward in return for sensitive information or knowledge of its whereabouts.
4. Malware
A category of attacks that includes ransomware, victims are sent an urgently worded message and tricked into installing malware on their device(s).
Ironically, a popular tactic is telling the victim that malware has already been installed on their computer and that the sender will remove the software if they pay a fee.
5. Pretexting
This attack involves the perpetrator assuming a false identity to trick victims into giving up information. Pretexting is often leveraged against organizations with an abundance of client data, like banks, credit card providers, and utility companies.
6. Quid Pro Quo
This attack centers around an exchange of information or service to convince the victim to act. Normally, cyber criminals who carry out these schemes don’t do advanced target research and offer to provide “assistance,” assuming identities like tech support professionals.
7. Tailgating:
This attack targets an individual who can give a criminal physical access to a secure building or area. These scams are often successful due to a victim’s misguided courtesy, such as if they hold the door open for an unfamiliar “employee.”
8. Vishing
In this scenario, cyber criminals will leave urgent voicemails to convince victims they must act quickly to protect themselves from arrest or another risk. Banks, government agencies, and law enforcement agencies are commonly impersonated personas in vishing scams.
9. Water-Holing
This attack uses advanced social engineering techniques to infect a website and its visitors with malware. The infection is usually spread through a website specific to the victims’ industry, like a popular website that’s visited regularly.
How Does Social Engineering Happen?
Social engineering happens because of the human instinct of trust. Cyber criminals have learned that a carefully worded email, voicemail, or text message can convince people to transfer money, provide confidential information, or download a file that installs malware on the company network.
Consider this example of spear phishing that convinced an employee to transfer $500,000 to a foreign investor:
- Thanks to careful spear phishing research, the cyber criminal knows the company CEO is traveling.
- An email is sent to a company employee that looks like it came from the CEO. There is a slight discrepancy in the email address, but the spelling of the CEO’s name is correct.
- In the email, the employee is asked to help the CEO by transferring $500,000 to a new foreign investor. The email uses urgent yet friendly language, convincing the employee that he will be helping both the CEO and the company.
- The email stresses that the CEO would do this transfer herself, but she can’t make the fund transfer in time to secure the foreign investment partnership since she is traveling.
- Without verifying the details, the employee decides to act. He truly believes that he is helping the CEO, the company, and colleagues by complying with the email request.
- A few days later, the victimized employee, CEO, and company colleagues realize they’ve been the targets of a social engineering attack, resulting in a loss of $500,000.
Examples of Social Engineering Attack Scenarios
Savvy cyber criminals know that social engineering works best when focusing on human emotion and risk. Taking advantage of human emotion is much easier than hacking a network or looking for security vulnerabilities.
The following are some familiar notes successful social engineering attacks hit again and again.
Fear
You receive a voicemail saying you’re under investigation for tax fraud and must call immediately to prevent arrest and criminal investigation. This social engineering attack happens during tax season when people are already stressed about their taxes.
Cyber criminals prey on the stress and anxiety of filing taxes and use these fear emotions to trick people into complying with the voicemail.
Greed
Imagine if you could transfer $10 to an investor and see this grow into $10,000 without any effort on your behalf. Cyber criminals use the basic human emotions of trust and greed to convince victims that they really can get something for nothing.
A carefully worded baiting email tells victims to provide their bank account information, and the funds will be transferred the same day.
Curiosity
Cyber criminals pay attention to events capturing a lot of news coverage and then take advantage of human curiosity to trick social engineering victims into acting. For example, after the second Boeing MAX8 plane crash, cyber criminals sent emails with attachments that claimed to include leaked data about the crash.
The attachment installed a version of the Hworm RAT on the victim’s computer.
Helpfulness
Humans want to trust and help one another. After researching a company, cyber criminals target two or three employees with an email that looks like it comes from the targeted individuals’ manager.
The email asks them to send the manager the password for the accounting database—stressing that the manager needs it to ensure everyone gets paid on time.
The email tone is urgent, tricking the victims into believing they are helping their manager by acting quickly.
Urgency
You receive an email from customer support at an online shopping website that you frequently buy from, telling you they need to confirm your credit card information to protect your account.
The email language urges you to respond quickly to ensure that criminals don’t steal your credit card information.
Without thinking twice, you send the information, which results in the recipient using your details to make thousands of dollars of fraudulent purchases.
How to Protect Your Information from Social Engineering Attacks
Though social engineering tactics are common, the examples in this blog post underscore how difficult they can be to spot and, more importantly, resist. Reacting based on human nature pushes many people toward a cyber criminal’s desired outcome.
To safeguard against the prevalence of social engineering tactics, it’s essential to arm yourself with the right tools and knowledge. Our Cyber Security Hub offers a comprehensive cyber security resource, including the latest information on social engineering threats.
By staying informed and empowered with our hub, you can proactively protect yourself and your sensitive data from malicious cyber attacks. Access our Cyber Security Hub for free today to secure your digital assets and stay ahead of potential threats.
Cyber Security Hub: Access Exclusive Cyber Security Content
White Paper – How to Protect Your Data from Social Engineering
Source: Terranova
Sophos Intercept X with Extended Detection and Response (XDR) has been rated the #1 XDR solution by G2 users in their spring 2023 reports (March 2023). G2 distinctions and rankings are based solely on independent, verified customer reviews on G2.com, the world’s largest software marketplace and peer-review platform.

Check out the full reviews on G2.com and how Sophos was named a leader in several other categories, including Endpoint, EDR, Firewall, and MDR.
XDR for the real world
Designed for security experts and IT administrators alike, Sophos Intercept X with XDR enables analysts to detect, investigate, and respond to threats across their entire security environments quickly and accurately.
Building on the strong protection foundation of Sophos Intercept X Endpoint technology, our XDR solution brings together telemetry from endpoints, servers, mobile devices, network, email, and cloud solutions for optimal visibility and accelerated response. Alternatively, organizations looking just for Endpoint Detection and Response (EDR) capabilities can utilize the same detection and response tools, focusing solely on their endpoints.
The G2 rating endorses our commitment to a prevention-first approach that reduces breaches and improves detection and response.

Sophos Intercept X with XDR has had several impressive and innovative updates that enable customers to enjoy superior cybersecurity outcomes:
- Third-party integrations enable customers to extend their visibility into threats and conduct more complete investigations to swiftly eject attackers from their environments. Customers can already leverage telemetry from Microsoft Security Graph API, Office365 Audit and Cloud App Security, Azure Activity and Flow, AWS Security Hub, and Google Cloud Platforms to accelerate threat detection and response, and we have a strong 2023 roadmap to match the integrations offered by the Sophos Managed Detection and Response (MDR) service.
- Aggressive classification (security posture adjustment) allows admins to select a more aggressive detection threshold for alerting when they suspect an active adversary is present.
- Alert-only mode gives admins a greater choice over whether to automatically stop-and-prevent vs. allow-and-alert, based on the customer’s unique risk tolerance.
- On-device behavior analytics for suspicious process activity extends existing heuristic and ML model-based detections to leverage an on-device behavior engine. This level of analytics is run on the endpoint instead of in the cloud to ensure that devices are secure even when offline or unable to send data to the data lake.
- Document access activity tracking that can be used for threat hunting and investigations when suspicious files have been in your environment.
Check out Sophos Intercept X with XDR for yourself at Sophos.com/XDR and see why it’s the number one XDR solution rated by G2 customers.
Source: Sophos
The manufacturing sector is witnessing the “Industry 4.0” era: smart factories equipped with industrial IoT devices, robotics, and advanced analytics to revolutionize manufacturing operations.
But rapid digitalization, lack of cybersecurity standards to match the growth, IT/OT convergence, and the sector’s low tolerance for operational downtime are increasing its attack surface. Manufacturers are looking to find solutions to risks such as vulnerability exploitation, data spillage, and production sabotage that plague the industry today.
It’s not surprising that cybersecurity challenges for manufacturers are growing in volume and complexity: 55% of manufacturing organizations were hit by ransomware in 2021 – a 52% increase from 2020. 61% of manufacturers reported an increase in attack volume, 66% reported an increase in attack complexity, and 51% reported an increase in the impact of attacks.
Manufacturing’s evolving threat landscape
In addition to the growing professionalism and evolving tactics, techniques, and procedures employed by criminal groups, there are a few other factors that are pushing forward the cybersecurity challenge in this sector:
- Manufacturers need to secure access to their critical industrial control systems and data
- Phishing scams – more specifically spear-phishing attacks – are easy ways for attackers to gain access to manufacturing systems and valuable data
- Theft of intellectual property like product designs, formulas, process patents, and other unique know-how of a manufacturing organization by cybercriminals, competitors, and ex-employees
- Risk of insiders who have authorized access to proprietary data or controls to critical manufacturing operations, misusing their privileges to steal trade secrets, sabotage manufacturing processes, or damaging equipment via remote access
- Manufacturers rely on a vast and complex supply chain network that is vulnerable to cyber attacks
- Manufacturers need to protect their legacy or unpatched manufacturing control systems and processes
- Cybercriminals are targeting the cloud to exploit less established cybersecurity practices than in traditional on-premises environments
Sophos can help
Download our Cybersecurity Guide for Manufacturing Industry to learn how Sophos can help address the most common cybersecurity challenges facing the manufacturing sector.
Sophos MDR is our fully-managed, 24/7 service delivered by experts who specialize in detecting and responding to sophisticated cyberattacks that technology solutions alone cannot prevent. As the world’s most trusted MDR provider and with many hundreds of manufacturing sector customers, we have unparalleled depth and breadth of expertise when it comes to threats facing the manufacturing sector. Sophos MDR applies learnings from defending one manufacturing organization to all others in the sector, generating “community immunity” and elevating everyone’s defenses.
“With Sophos MDR we have reduced our threat response time dramatically.”
Tata BlueScope Steel
“Sophos MDR’s ability to remediate or remove threats in a swift manner and bring them to our attention frees us up to focus on high-value tasks.”
Tomago Aluminium
“Sophos releases the IT teams to undertake more proactive tasks instead of being drawn into managing security challenges.”
AG Barr
Sophos ZTNA eliminates vulnerable VPN clients, enabling you to offer secure and seamless access to resources for your remote users defined by policies. It removes implicit trust in your environment’s applications, users, and devices, allowing segmented access to your systems and resources to just those who need it.
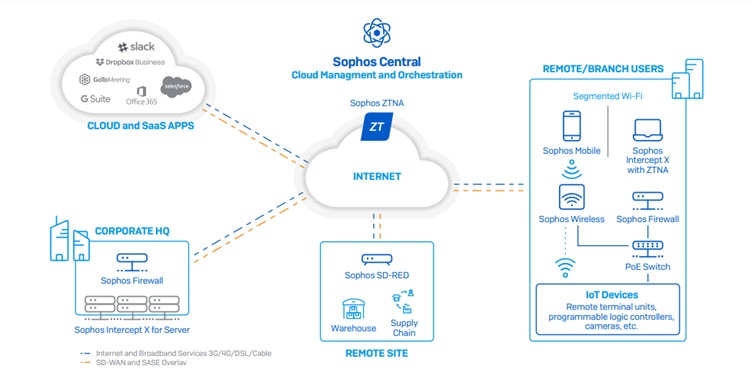
Sophos Secure Access Portfolio enables manufacturers to connect remote and branch sites, deliver critical cloud and SaaS applications such as Dropbox, Salesforce, and others, and share data and information between sites.
It includes:
- Sophos ZTNA to support secure access to applications
- Sophos SD-RED remote Ethernet devices to safely extend your network to branch locations and remote devices
- Sophos Wireless access points for easy and secure wireless networking
- Sophos Switch for secure access on the LAN
Everything is managed through a single cloud-based security platform, Sophos Central.
Speak with an expert
To learn more and discuss how Sophos can help you, contact your Sophos representative or request a call-back from our security specialists.
Source: Sophos
Less of a cyber security threat and closer to a scam, vishing refers to attempts to steal information or money over the phone by convincing the victim. These calls often use personal data acquired through previous cyber attacks to gain their victim’s trust.
This type of threat is definitely on the rise. Like many other hacks and scams, vishing is a popular attack type because it is simple to carry out, scales well and is often successful. It also requires very low technological investment and requires virtually no real coding knowledge beyond basic information that can be found online.
According to a recent Truecaller survey, 26% of Americans lost money due to a phone scam in 2022. This number shows that this type of attack is on the rise and that people are largely undereducated about them.
The most common type of vishing is impersonating an authority figure such as a government official, client, or coworker. The scammer’s goal is to obtain sensitive information such as a social security number. Still, these calls can become global threats if the victim is convinced to provide something with wider ramifications, such as a computer password.
In rare cases, the scammers will attempt to convince the employee to wire money or pay for a fake invoice to steal the company’s funds. No matter the goal or method used by the scammer, the only way to foil these attacks is through proper user awareness programs.
This article will look at seven common examples of vishing and explain them thoroughly so your users don’t fall into the trap.
1. AI-Based Vishing
AI is starting to become a tool to carry out wicked agendas, and we’re seeing it play out in social engineering scams like Vishing. AI works by detecting patterns and producing iterations of them without the need for constant human input—which means that it can automatically deploy processes once it has detected a pattern in its algorithm.
There is AI software now that can mimic a person’s voice, easily fooling employees into thinking that they’re speaking to their superiors or managers. In fact, in 2021, a large-scale cyber attack was carried out through voice cloning.
The attacker used AI to mimic the company director’s voice, convincing a bank manager through a phone call to transfer $35 million as part of the bank’s acquisition process.
This incident is one of the firsts that directly links AI to cyber threats, using deep voice technology to clone an executive’s speech, voice, and melodies to carry out a cyber attack. With voice patterns readily available from social media, YouTube, interview recordings, etc., AI poses a significant threat to all organizations.
2. Robocall
These attacks feed a prerecorded call to every phone number in a specific area code through computer software. The automated voice asks the victim to state their name and other information. The answers are recorded and used to steal money or open fraudulent credit cards.
Thankfully, these calls are becoming so common that most people know them and hang up when they receive them. Another telltale sign of these attacks is international or blocked numbers since the scammers have to cycle numbers to keep authorities off their trail regularly.
3. VoIP
While VoIP is a great technology that has allowed fantastic business innovations, scammers can easily create fake numbers to carry out attacks. This technique can be combined with a robocall but is often carried out by human callers.
The best way to thwart these calls is by asking for more information to be sent via email, where attacks are easier to detect, or by asking to carry out the rest of the call in person since the attacker won’t be able to do it.
4. Caller ID Spoofing
This attack can be especially pernicious because it uses software to fake a legitimate caller ID. Scammers will usually try to pass for an institution such as a tax agency, police department, or hospital to create urgency and get the victim to surrender information they usually wouldn’t.
These attacks are hard to spot, and the best way to evade them is the same as with VoIP by taking the call to another medium. Certain phones and physical security measures can detect these fake caller IDs and automatically reject them.
5. Dumpster Diving
As the name says, these attacks are carried out using information gathered through a business’ trash. Official company documents often contain enough personal data to launch a successful vishing attack.
The best way to counter dumpster diving is simple. Every company should shred all sensitive company documents before throwing them out. Whether using an external company or buying shredders for the office, it’s a worthwhile investment considering the potential risks.
6. Tech Support Call
This attack is widespread in large companies where employees might not know or have met members of the tech support department. Scammers will pretend they need to do a computer update or repair and ask for the victim’s password to do it.
Education is key to beating these attacks. Frequently remind users that you will never ask them to divulge their password over the phone and that they shouldn’t do so under any circumstance.
7. Voicemail Scam
This attack is different and involves voice mail notifications. Many smartphones and apps send emails to their users to notify them of stored voicemails. These emails will contain a link to listen to a voicemail. These fraudulent emails will lead users to a website that downloads malware onto their devices.
This scam can be evaded by ensuring users are adequately trained to notice phishing emails. These emails often have spelling mistakes and improperly sized logos and aren’t sent from official domain names.
8. Client Call
Often done by finding old invoices via dumpster diving, scammers perpetrating these attacks will pretend to be your company’s client and ask for an invoice to be paid. They’ll rely on a sense of urgency to convince the victim to wire funds and steal company money.
This scam is an excellent example of why every company should have a two-person approval for any invoice payment or wires. That way, another person not involved in the attack has to review the process and can detect fraudulent attempts.
Education Is Key
Vishing is definitely on the rise. The best way to counter this scam is by ensuring your users know they exist so they can recognize them. Vishing simulations are just as simple as phishing simulations and should be a core part of your cyber security awareness training campaigns.
The best way to see if your organization is at risk will always be to run some tests and adjust your defenses accordingly. Hackers will always rely on mundane situations and scenarios that make people let their guard down.
Reminding users of how these situations unfold and the telltale signs to look for is the most effective course of action to prevent vishing attacks. Once people are well trained in this regard, the steps to avert vishing attacks are simple and have a high success rate.
These attacks are the same whether they target a person or an entire business. Training your staff about vishing protects their whole life, at the office and at home.
Source: Terranova