News
Sophos to Acquire Secureworks to Accelerate Cybersecurity Services and Technology for Organizations Worldwide.
Two global cybersecurity leaders are joining forces to accelerate the delivery of advanced cybersecurity services and technology for organizations of all sizes around the world.
Sophos today has announced a definitive agreement to acquire Secureworks®, the developer of TaegisTM, the SaaS-based, open MDR/XDR platform built on more than 20 years of real-world detection data, security operations expertise, and threat intelligence and research. Our experience and reputation as a leading provider of managed security services and end-to-end security products, combined with Secureworks’ security operations expertise transformed into the Taegis platform, is expected to further deliver advanced MDR and XDR solutions for our customers.
In addition to integrating the Taegis MDR/XDR platform with Sophos’ industry leading MDR capabilities, Sophos also expects to leverage and combine additional solutions from Secureworks to provide a broader and stronger security portfolio. This includes Secureworks’ identity detection and response (ITDR), next-gen SIEM capabilities, operational technology (OT) security, and enhanced vulnerability risk prioritization. The breadth of the integrated portfolio will provide the fastest time to detect, investigate, and respond to threats, while the level of visibility across native and third-party tools will deliver improved customer ROI as they can better leverage existing investments.
“Secureworks offers an innovative, industry-leading solution with its Taegis XDR platform. Combined with our security solutions and industry leadership in MDR, we will strengthen our collective position in the market and provide better outcomes for organizations of all sizes globally, said Joe Levy, CEO of Sophos. “Secureworks’ renowned expertise in cybersecurity perfectly aligns with our mission to protect organizations from cybercrime by delivering powerful and intuitive products and services. This acquisition represents a significant step forward in our commitment to building a safer digital future for all.”
As two partner-centric organizations, the combination of Sophos and Secureworks will enable the combined company to expand its customer presence to create greater value with our channel partners and strengthen the overall security community. The transaction is expected to close in early 2025, subject to customary closing conditions. In the meantime, we will both operate business as usual with our shared unwavering mission to help businesses of all sizes defeat cyberattacks.
Source: Sophos
Not that we ever imagined the Cloud would be immune to ransomware, but Microsoft now reports how it observed a group of cybercriminals it tracks as Storm-0501 compromising hybrid cloud environments.
Storm-0501 has been associated with ransomware since it was first seen in 2021, when it used the Sabbath ransomware against a US school district. The Sabbath ransomware affiliate program targets mostly critical infrastructure in the United States and Canada. It uses a multifaceted extortion model that includes ransomware deployment, data theft, and destruction of backups. Mandiant says the same group previously operated under the names of Arcane and Eruption and was found deploying the ROLLCOAST ransomware.
Later they changed their activities to act as affiliates for Ransomware-as-a-Service (RaaS) groups like Hive, ALPHV, Hunters International, LockBit, and most recently, Embargo ransomware.
The preferred way to move laterally from on-premises systems to cloud environments are stolen credentials for accounts that have access to both. They use the stolen credentials to gain control of the network, eventually creating persistent backdoor access to the cloud environment, and deploying ransomware to on-premises systems.
Initial access is often provided by Initial Access Brokers (IABs) that use known remote code execution (RCE) vulnerabilities in Zoho ManageEngine, Citrix NetScaler, and ColdFusion 2016.
With the provided access, the group then engages in network discovery to find desirable targets, such as high-value assets and general domain information. Using living-of-the-land (LOTL) techniques, they go after Domain Administrator users and domain forest trust, which helps users to manage a segmented Active Directory Domain Services (AD DS) infrastructure.
Other open-source tools are used to query additional endpoint information, and for Active Directory reconnaissance.
In the next stage, the group deploys remote monitoring and management tools (RMMs) to interact with the compromised devices and maintain persistence.
By using the admin privileges on the compromised vulnerable devices, they go after additional credentials to access more devices in the network.
The credentials used to get to the cloud were specifically Microsoft Entra IDs that were stolen earlier during the attack.
Microsoft Entra Connect, previously known as Azure AD Connect, is an on-premises application that synchronizes an on-premises identity and the Microsoft Entra identity of a user account to allow the user to sign in to both realms with the same password.
Microsoft established that the attacker specifically located Microsoft Entra Connect Sync servers and managed to extract the plain text credentials of the Microsoft Entra Connect cloud and on-premises sync accounts, probably by using Impacket to steal credentials and Data Protection API (DPAPI) encryption keys.
The end goal here was the data theft and the deployment of Embargo ransomware. In the cases observed by Microsoft, the threat actor leveraged compromised Domain Admin accounts to distribute the Embargo ransomware via a scheduled task named SysUpdate that was registered via GPO on the devices in the network.
Protective measures
To decrease the attack surface, Microsoft recommends that organizations deploy Microsoft Entra Connect on a domain-joined server and restrict administrative access to domain administrators or other tightly controlled security groups.
You should also enable multi-factor authentication (MFA) for all users, starting with privileged administrators. Microsoft also urges users enable protection to prevent by-passing of cloud Microsoft Entra MFA when federated with Microsoft Entra ID.
An MDR service can spot suspicious behavior like the deployment of LOTL, RMM, and open-source tools, that regular endpoint protection might miss.
Consider using an Identity and Access Management (IAM) solution. IAM solutions control who has access to cloud resources and what they can do with them. This includes user authentication, authorization, and the enforcement of access policies.
A vulnerability and patch management solution can help stop the initial access through vulnerable internet facing devices, services, and software.
Security Awareness Training can educate employees about cloud security best practices and the potential risks associated with cloud computing.
Source: ThreatDown
We are delighted to announce that Sophos has been named a Leader in the IDC MarketScape: European Managed Detection and Response (MDR) Services 2024 Vendor Assessment (doc # EUR151172124, September 2024).
The IDC MarketScape study evaluates the capabilities and business strategies of managed detection and response service vendors with a market presence in Europe, and positions Sophos in the Leaders Category.
This latest recognition follows Sophos being named an MDR Leader in the Worldwide version of this evaluation – IDC MarketScape: Worldwide Managed Detection and Response (MDR) Services 2024 Vendor Assessment (doc #US49006922, April 2024).
With decades of experience and knowledge as a security technology vendor, Sophos has considerable expertise when it comes to how cyberattacks impact and unfold across enterprise infrastructure. Since the launch of its MDR ambitions with a series of acquisitions in 2019, the vendor has also put considerable emphasis on building teams of highly experienced and skilled security analysts to deliver its human-led service. The company’s unmetered and unlimited incident response offering is a compelling component of this. Where organizations are seeking an MDR provider with deep security expertise and a human-led service that engages with them from the outset until an incident has been resolved, Sophos represents a compelling option.
– IDC MarketScape: European Managed Detection and Response 2024 Vendor Assessment
A European MDR market leader
Sophos has built one of the biggest global managed detection and response (MDR) businesses in the world, and we believe it protects more customers than any other MDR service. This latest IDC MarketScape report noted Sophos “has more than 23,000 MDR customers worldwide, making it one of the biggest players on the market in terms of customer base. In Europe, it counted more than 5,000 unique MDR customers at the end of 2023, with the majority being under-250-employee organizations.”
The IDC MarketScape evaluation also highlights Sophos’ geographic presence in supporting European data residency requirements:
Regarding data residency, Sophos processes telemetry in the region in which the customer account is provisioned. For Europe, Sophos is hosted in the UK & Ireland, and Germany AWS regions.
Sophos MDR has highly skilled threat analysts based in the UK, Ireland, and Germany, in addition to dedicated teams in North America, India, and Australia. This enables us to provide 24/7/365 coverage to our European customers.
Unlimited incident response is a significant differentiator
The IDC MarketScape notes that a key differentiator for any MDR service is its incident response capabilities, and we agree. The two MDR service tiers available from Sophos – MDR Complete and MDR Essentials – are designed to align with the customer maturity journey. Sophos MDR Complete includes a unique, unmetered, full-scale incident response offering that eliminates threats.
Customers subscribing to the entry-level Sophos MDR Essentials service tier also benefit from a flexible range of incident response options, as described in the IDC MarketScape report:
MDR Essentials customers get a Threat Response service, which commits to stopping and containing all active attacks. MDR Essentials customers may also choose to purchase an IR retainer for the extra coverage on top of the core service components they receive. This means that customers that start out with MDR Essentials but decide they want or need more have two options: add the IR retainer or upgrade to the full MDR Complete service (with all the additional components that brings).
Both service tiers include 24/7 expert-led investigation and response and threat hunting.
Extensive partnerships, alliances, and integrations
The IDC MarketScape calls out Sophos’ strategic partnership with Tenable for Sophos Managed Risk, our new vulnerability and attack surface management service, and our partnership with backup provider Veeam, citing the benefits of our substantial partner and customer overlap.
The report noted,
In April 2024, Sophos announced a strategic partnership with Tenable to launch Sophos Managed Risk, a vulnerability and attack surface management service. With a dedicated Sophos team leveraging Tenable’s exposure management technology the companies aim to drive collaborative operation between MDR and vulnerability management. With extensive reporting and prioritization around vulnerabilities, this should help sort signal from noise and address use cases such as risk mitigation through attack surface visibility, patch prioritization, and rapid identification of new risks through alerts around new critical vulnerabilities.
The IDC MarketScape report states that Sophos has “worked on numerous use cases around Microsoft telemetry, such as email compromise, as it aims to deliver concrete security benefits to its clients.”
Reinforcing our credentials in the small business segment where many organizations use Google productivity solutions rather than Microsoft, Sophos also includes an integration with Google Workspace with Sophos MDR and Sophos XDR offerings at no additional cost.
Get the excerpt
To learn more about why Sophos was named a Leader in the 2024 IDC MarketScape for European Managed Detection and Response, read the excerpt here.
Source: Sophos
The Gartner®️ Magic Quadrant™️ for Endpoint Protection Platforms provides readers with a comprehensive evaluation of the industry’s most prevalent endpoint prevention, endpoint detection and response (EDR), extended detection and response (XDR), and managed detection and response (MDR) offerings.
We are delighted to announce that Sophos has been named a Leader, again, in this year’s report, marking our 15th time as a Leader in this category.
A Magic Quadrant Leader for the fifteenth consecutive time
Only vendors that can innovate as quickly and aggressively as the threat actors we defend against, can strive to retain a leadership position in the hyper-competitive endpoint security market. Sophos has been recognized in the Gartner® Magic Quadrant™ for Endpoint Protection Platforms (EPP) since its inaugural publication and, we feel, this confirms our commitment to continued innovation.
Stronger protection with adaptive defenses
We believe our continued focus on a protection-first approach is a key factor contributing to Sophos’ position as a Leader in this Gartner evaluation. As attackers continue to innovate in their approaches, we continue to extend the adaptive defenses in Sophos Endpoint to further protect customers against active adversaries.
Our adaptive attack protection capability dynamically enables heightened defenses on an endpoint when a hands-on-keyboard attack is detected, and critical attack warnings alert you if adversarial activity is detected across multiple endpoints or servers in your environment.
An expansive partner ecosystem and new technology alliances
Sophos’ third-party technology integrations and strategic partnerships provide unparalleled security, efficient and effective security operations, and greater return on investment for our customers. We have continued to expand our range of third-party integrations for the Sophos XDR solution and the Sophos MDR service, including a new Backup and Recovery category.
Sophos also launched a new alliance with Tenable with the introduction of Sophos Managed Risk, our new attack surface vulnerability management service.
A 2024 Gartner® Peer Insights™ Customers’ Choice vendor
In addition to this latest recognition as a Leader in the 2024 Gartner Magic Quadrant report, Sophos has also been named a Customers’ Choice vendor in the 2024 Gartner® Peer Insights™ Voice of the Customer Report for Endpoint Protection Platforms for the third consecutive year. Sophos scored a 4.8/5.0 rating based on 680 customer reviews as of April 2024 – the highest number of reviews among all endpoint security vendors in the report.
We believe these Gartner recognitions are an acknowledgement of the quality of the protection and service we provide to Sophos customers. To find out why Sophos was named a Leader in the Gartner® Magic Quadrant™ for Endpoint Protection Platforms for the fifteenth consecutive time, read the full report at https://www.sophos.com/en-us/report/magic-quadrant-endpoint-protection-platforms
Πηγή: Sophos
Sophos Firewall v21 brings exciting new enhancements to VPN, authentication, and routing functionality.
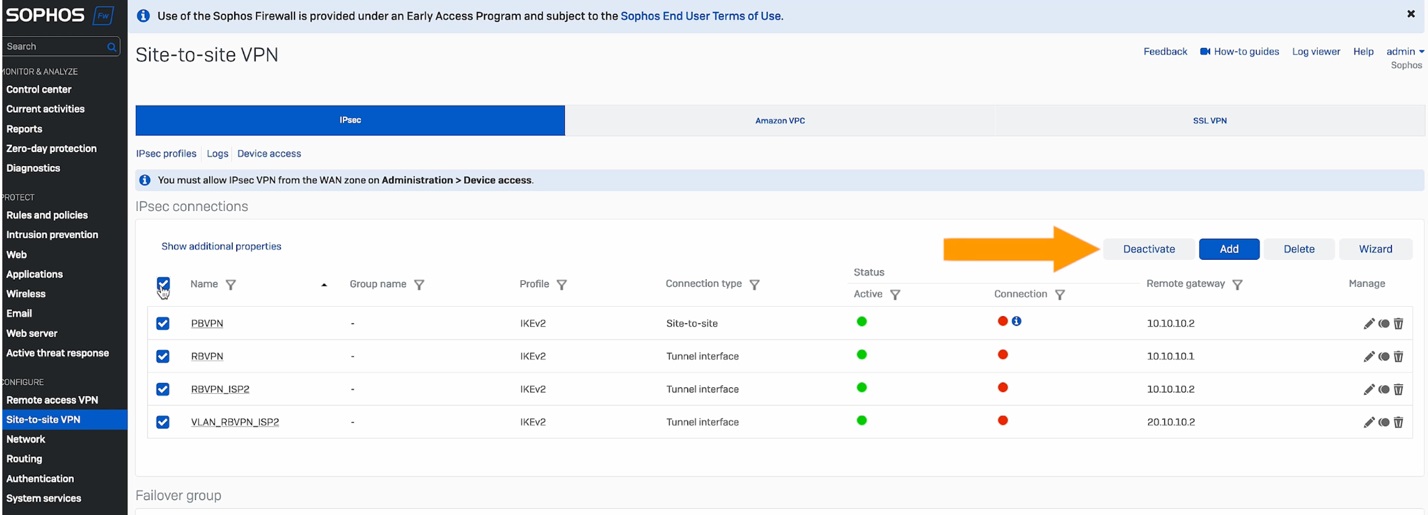
VPN enhancements
- Bulk activate and deactivate options are now available for connections (see screen shot below)
- Enhanced filtering on the VPN manage page now consolidates information across multiple pages
- Free text- and value-based search is now supported in VPN configurations for network, subnet, users for remote access and site-to-site VPNs
- An XFRM interfaces-specific view has been added on the Interfaces page for easy filtering of RBVPN interfaces
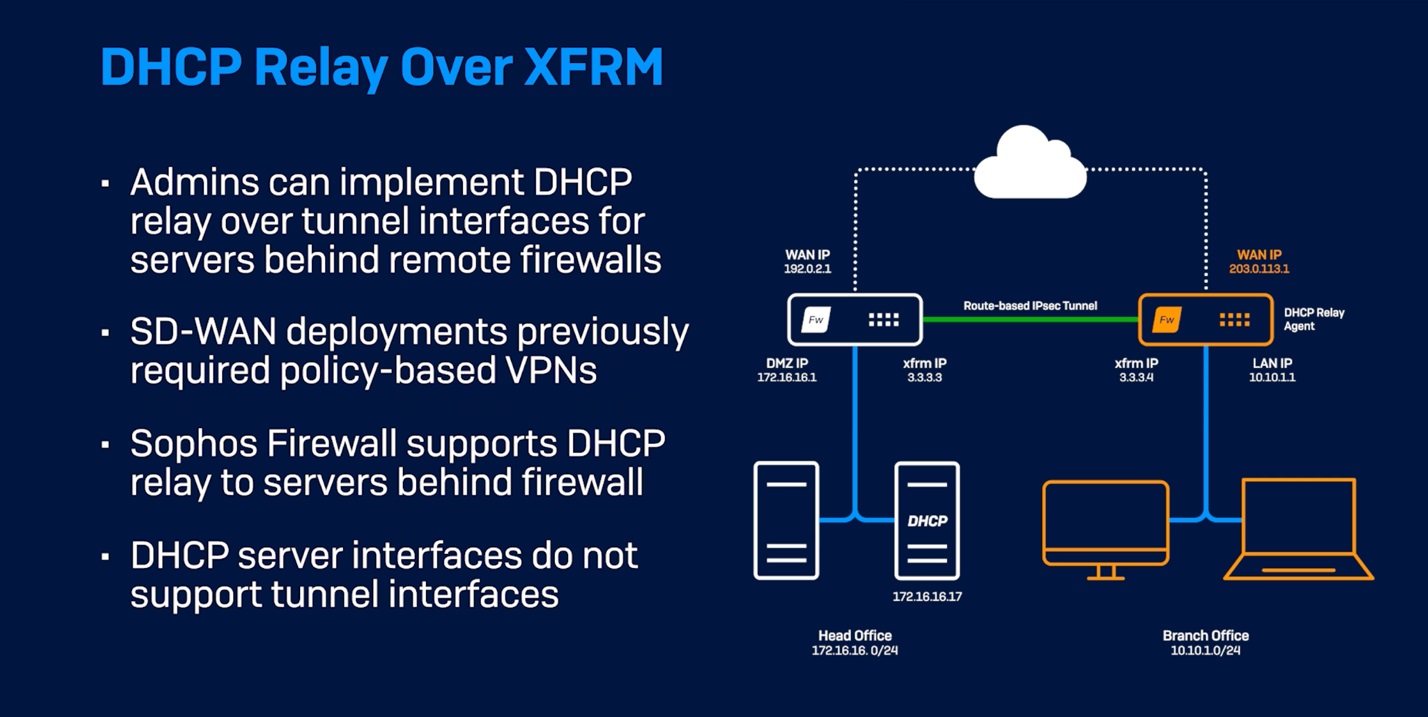
Site to site VPN enhancements
- FQDN-based remote gateways have been optimized to improve scalability for distributed deployments
- DHCP relays over XFRM interfaces are now supported for traffic to DHCP servers deployed behind a remote firewall (see illustration below)
- RBVPN deployments get an increase of up to 20x in XFRM interface up-time, significantly minimizing disruption during tunnel flap, HA failovers, or reboots
Authentication enhancements
- Google Workspace integration via LDAP clients and Google Chromebook SSO compatibility with LDAP server types enables SSO functionality for Google LDAP for Chromebook environments
- Performance for burst login handling is improved up to 4x for Radius SSO, STAS, and Synchronized User ID to enable the handling of thousands of simultaneous login requests even in multiple SSO environments (mix of STAS, Radius SSO, and Synchronized User ID)
- In addition, support has been added for a transparent AD SSO experience when HSTS is enforced, enabling Kerberos and NTLM handshakes over HTTP or HTTPS
Static and dynamic route management
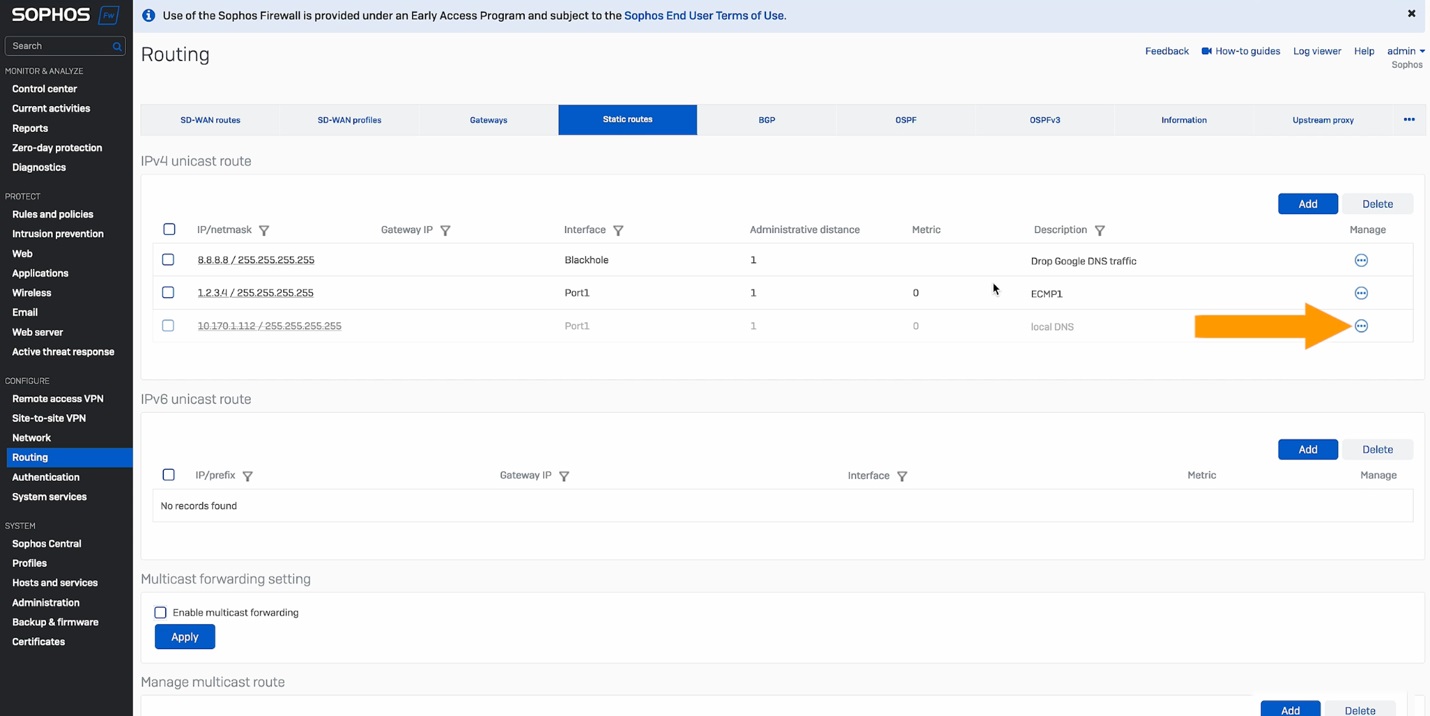
- Users can clone static routes, turn them on or off, and add descriptions via the new Manage option for each static route in the table (see screen shot below)
- There’s now a blackhole route option and support for equal-cost multi-path (ECMP) for load balancing
- Dynamic routing gets a new option to redistribute BGP routes into OSPFv3
- Dynamic routing now experiences zero impact during HA failover scenarios
Watch this short demo video to see how it works and how to set it up:
Start taking advantage of this great new capability in Sophos Firewall v21 by participating in the early access program. Simply register for the program, click the link in your email to download the firmware update package, and install it on your Sophos Firewall.
Source: Sophos
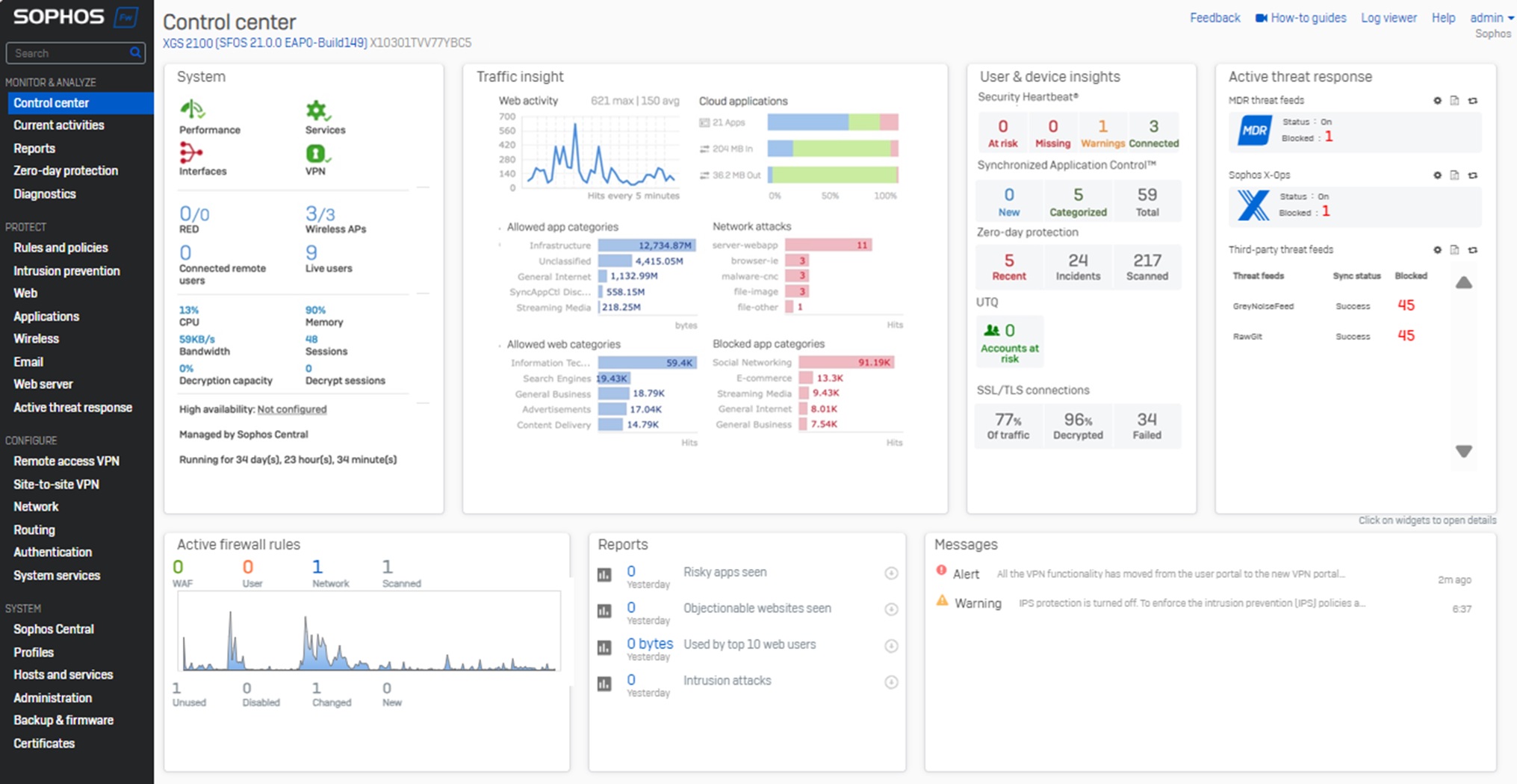
Sophos Firewall v21 brings several quality-of-life enhancements to streamline day-to-day management and improve the overall user experience.
User interface enhancements
- Significantly enhanced responsiveness
- Refreshed look and feel, integrating the latest Sophos style guidelines for consistency with Sophos Central and your other Sophos products
- Improved horizontal layout to better take advantage of widescreen displays
- New card views to further enhance visibility into important network events and data with the same flip and drill-down capabilities as before
- An all-new Active Threat Response card consolidates threat information from MDR, Sophos X-Ops, and third-party threat feeds into a single, easy-to-view section
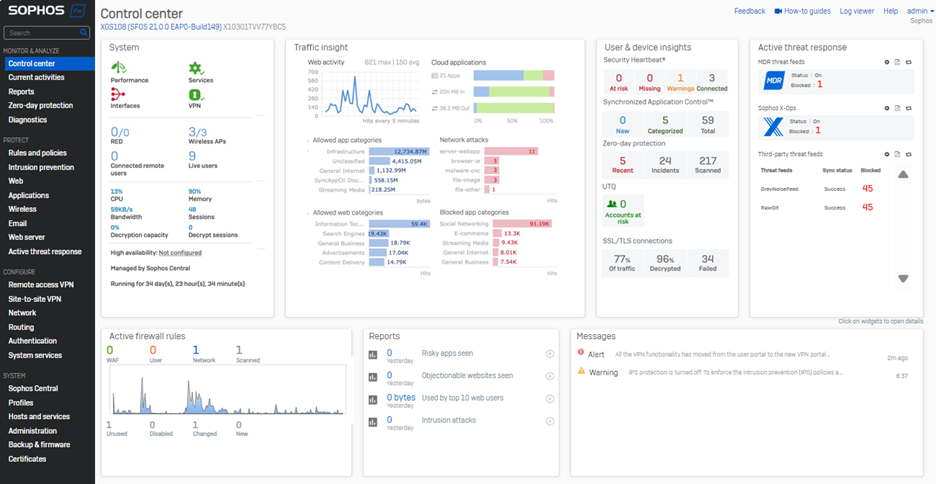
The refreshed Control Center includes a new card for Active Threat Response.
Network object references
- New visibility into network object usage is now provided for interfaces, zones, gateways, and SD-WAN profiles. Simply click the new “usage” indicator on any of these screens for a quick view of the associated network objects. You can then drill down to view or edit the object details and settings in place.
- A new XML API is also provided to retrieve object reference (usage) counts, offering visibility into unused objects. See the video below for details and a demo.
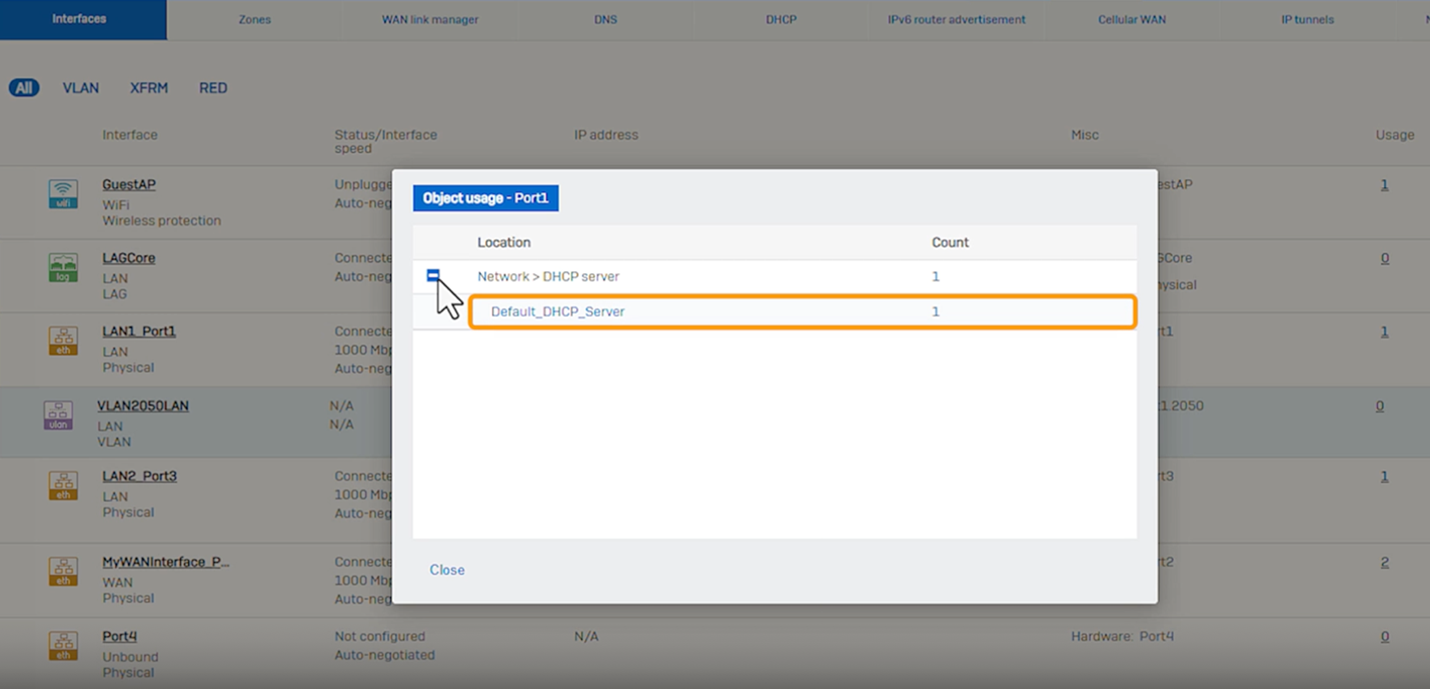 See which network objects are associated with interfaces, zones, gateways, and SD-WAN profiles with drill-down in place.
See which network objects are associated with interfaces, zones, gateways, and SD-WAN profiles with drill-down in place.Watch this short demo video to see the new quality of life enhancements in action:
Start taking advantage of this great new capability in Sophos Firewall v21 by participating in the early access program. Simply register for the program, click the link in your email to download the firmware update package, and install it on your Sophos Firewall.
Get the What’s New Guide for a complete overview of all the new features in Sophos Firewall v21.
Source: Sophos
Authenticator apps help keep our accounts safe from hacking attempts, but they can sometimes be inconvenient. A little-known benefit of using a password manager like Keeper is that it can generate and store Two-Factor Authentication (2FA) codes right in your Keeper Vault, acting as an authenticator app. To start using Keeper as an authenticator app, all you have to do is scan the QR code or input the secret key generated by the website or app you’re enabling Multi-Factor Authentication (MFA) on using Keeper.
Continue reading to learn how to use Keeper as an authenticator app to seamlessly log in to your accounts.
What is an authenticator app?
An authenticator app is an application that generates codes known as Time-Based One-Time Passwords (TOTP) every 30 to 60 seconds. To log in to your account using an authenticator app, you enter the TOTP code on the login page along with your username and password. Depending on the website or app you’re attempting to log in to, you’ll either enter the TOTP code before or after entering your username and password correctly.
While authenticator apps are more secure than email and SMS-based authentication, many people still choose the least secure methods of authentication because they find them easier to use and more convenient than having a separate application installed.
How you can use Keeper as an authenticator app
Before you can use Keeper as an authenticator app, you’ll need to be a Keeper user. If you’re not already, we offer a free 30-day trial so you can start securing your accounts immediately.
Once you’ve set up your Keeper Vault, you can begin using Keeper as an authenticator app by following the steps below.
1. Log in to your Keeper Vault.
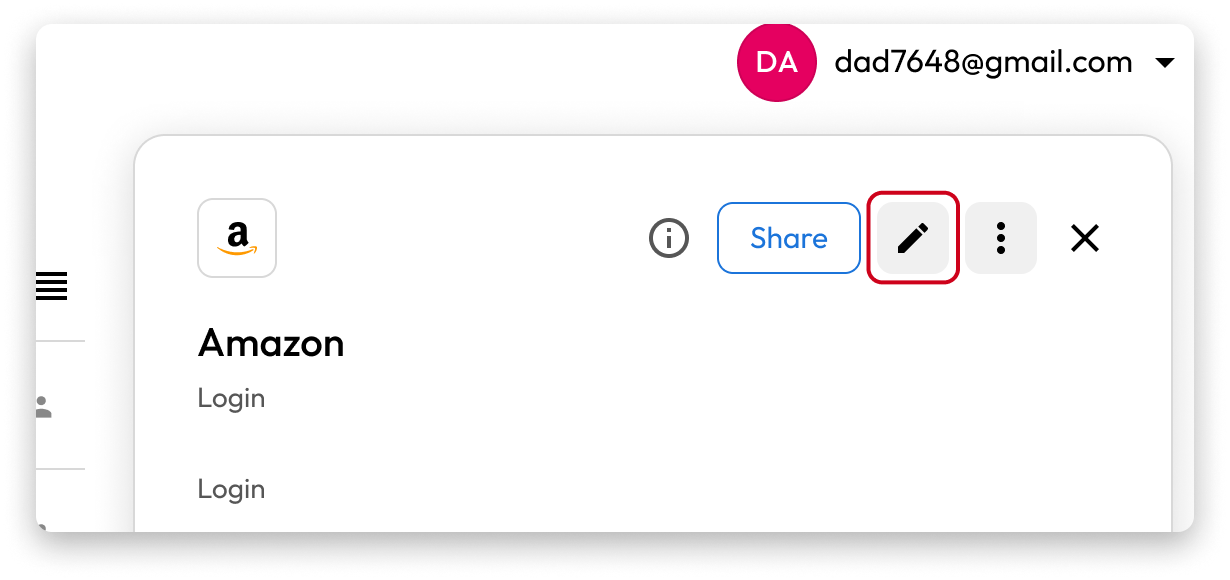
2. Locate the record for which you want to generate and store a 2FA code.
3. Click on the record.
4. In the record, click the edit button on the top right corner that looks like a pencil.
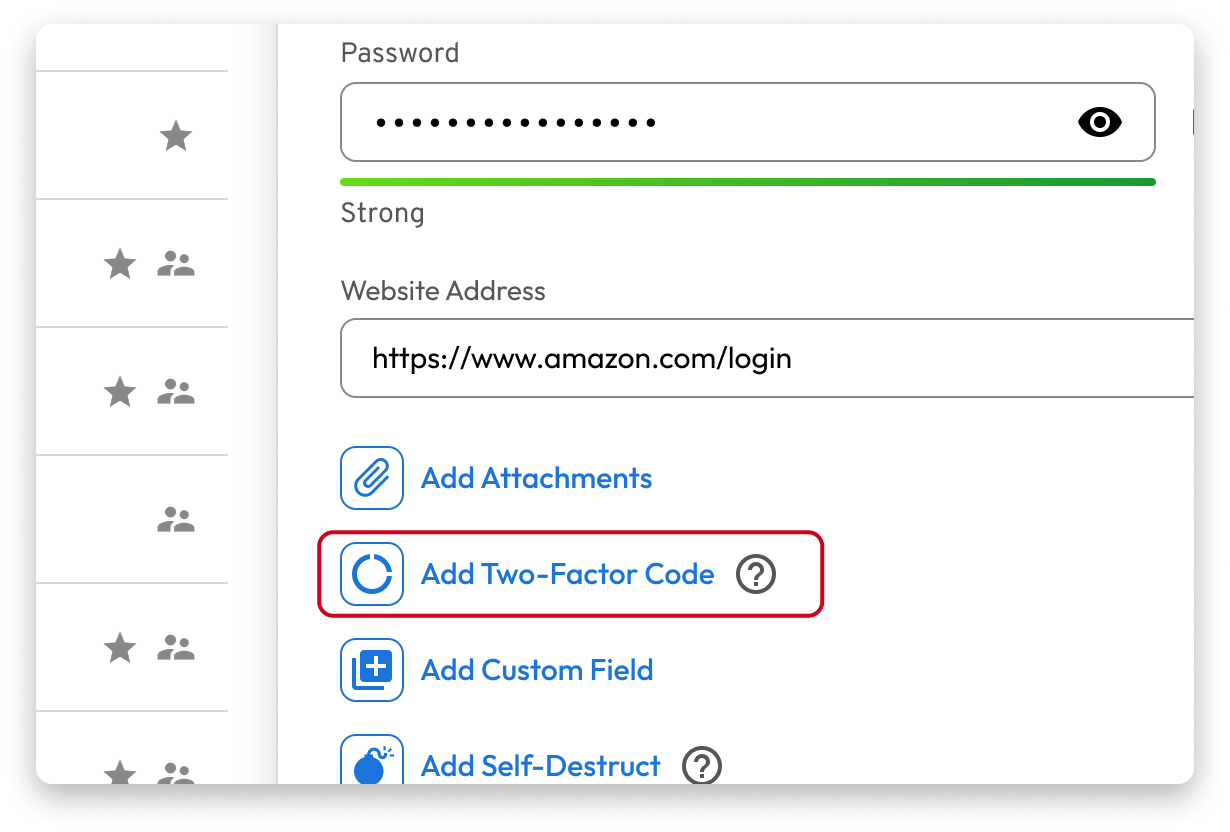
 5. Click where it says “Add Two-Factor Code.”
5. Click where it says “Add Two-Factor Code.”
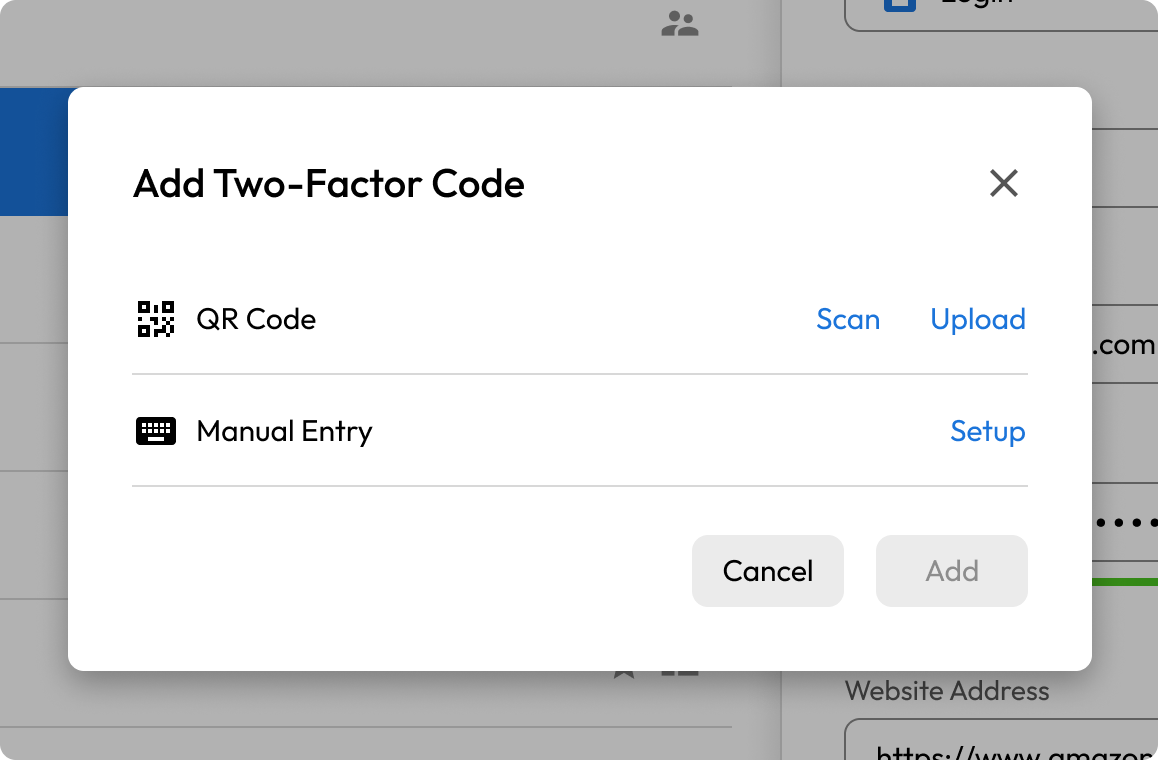
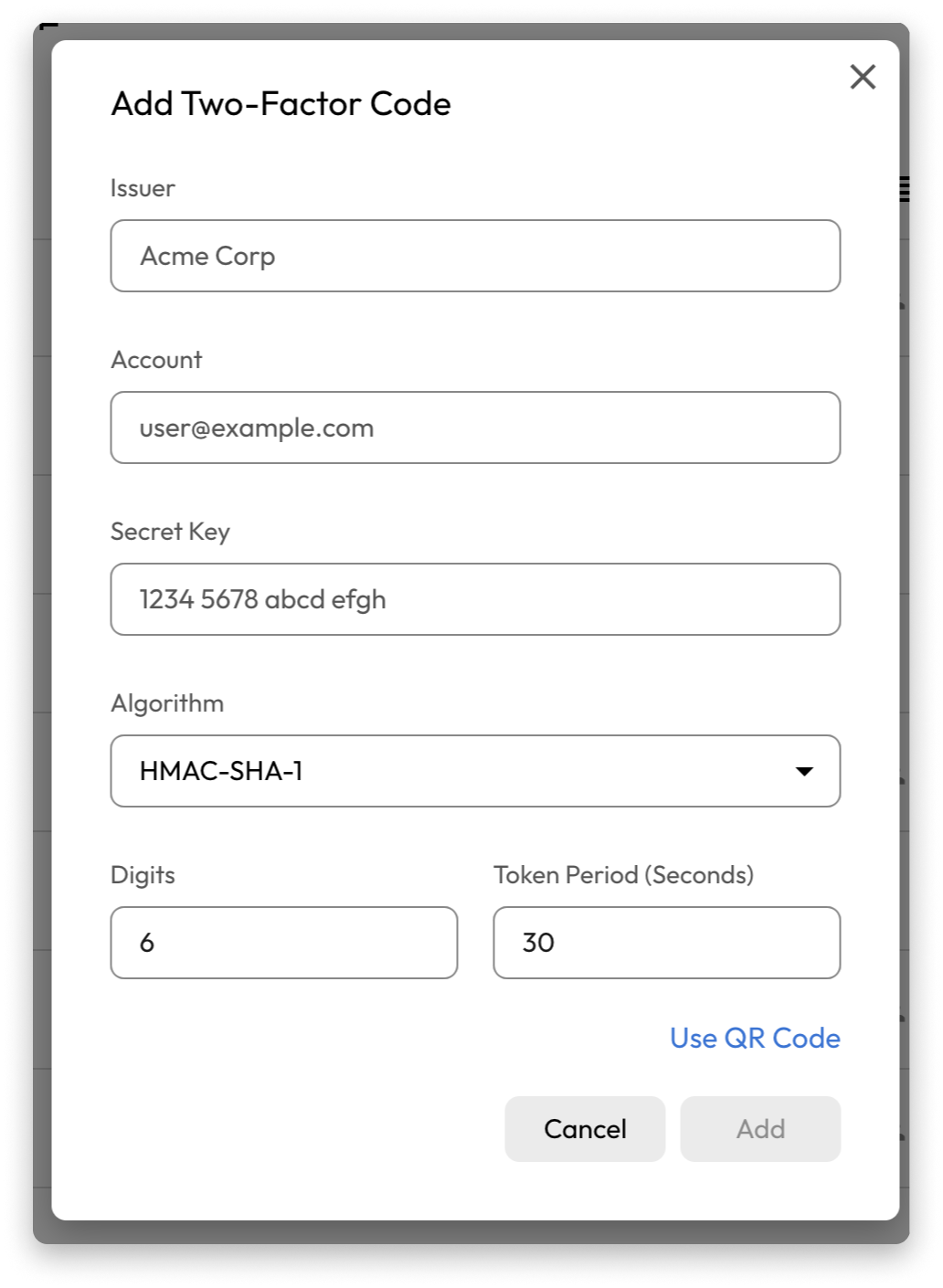
6. From here, you’ll have the option to scan a QR code or enter the code given to you manually.
7. Log in to the account for which you want to set up a 2FA code.
8. Find the option to enable two-factor authentication in your security settings (this will vary from account to account).
9. If you’re using Keeper on your phone, scan the QR code displayed during the setup process. If you’re using Keeper on a desktop, upload a screenshot of the QR code or copy and paste the code provided.
The benefits of using Keeper over other authenticator apps
Here are some of the benefits of using Keeper over other authenticator apps.
Accessible from multiple devices
Many authenticator apps, such as Google Authenticator and Microsoft Authenticator, are mobile applications that you have to install on your phone. This can pose an inconvenience if you want to log in to an account with MFA enabled and don’t have your phone with you. By using Keeper as your authenticator app, you’ll be able to access your 2FA codes from any device and browser to seamlessly log in to your accounts.
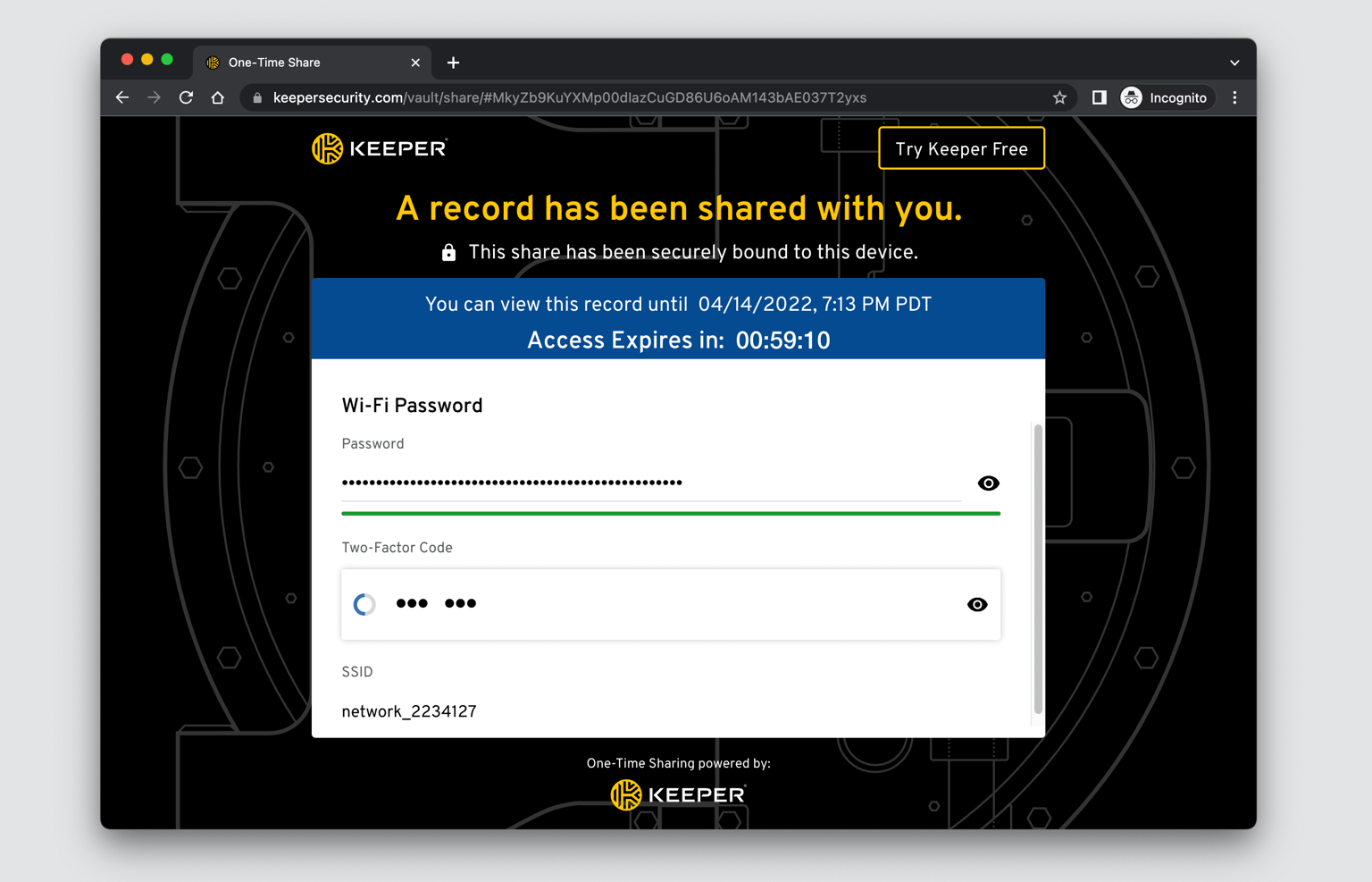
Enables 2FA record sharing
One of the disadvantages of using authenticator apps as an MFA method is that you can’t securely share your 2FA codes with your family, friends or colleagues. This makes it difficult to share login information with people you share accounts with, such as those for streaming services and subscriptions. With Keeper, you won’t have to worry about how to securely share your login information because you can easily do it with Keeper’s One-Time Share feature. Using One-Time Share, you’ll have full control over your login information since you’ll be able to choose how long the recipient has access to it, and you can revoke access to the record whenever you’d like. With One-Time Share, you can share your login information with anyone – they don’t even have to be a Keeper user themselves.
Offers the strongest encryption
Most authenticator apps on the market, like Google Authenticator, are not end-to-end encrypted. If a data breach were to occur or someone gained access to your device or Google account, your One-Time Password (OTP) secrets would be compromised, and the threat actor would be able to generate the same OTP codes as if they were you. With Keeper, you can rest assured that your 2FA codes are always secure because Keeper is zero trust and zero knowledge, and uses end-to-end encryption to secure all data stored in your vault.
Conveniently secure your accounts with Keeper
Protecting your online accounts against compromise goes beyond using strong passwords. You should ensure that each of your accounts has MFA enabled for additional security. With Keeper, you’ll be able to easily store your strong passwords and 2FA codes in one place, enabling you to seamlessly log in to accounts from wherever you are.
Start a free 30-day trial of Keeper Password Manager today to start securing your online accounts.
Source: Keeper
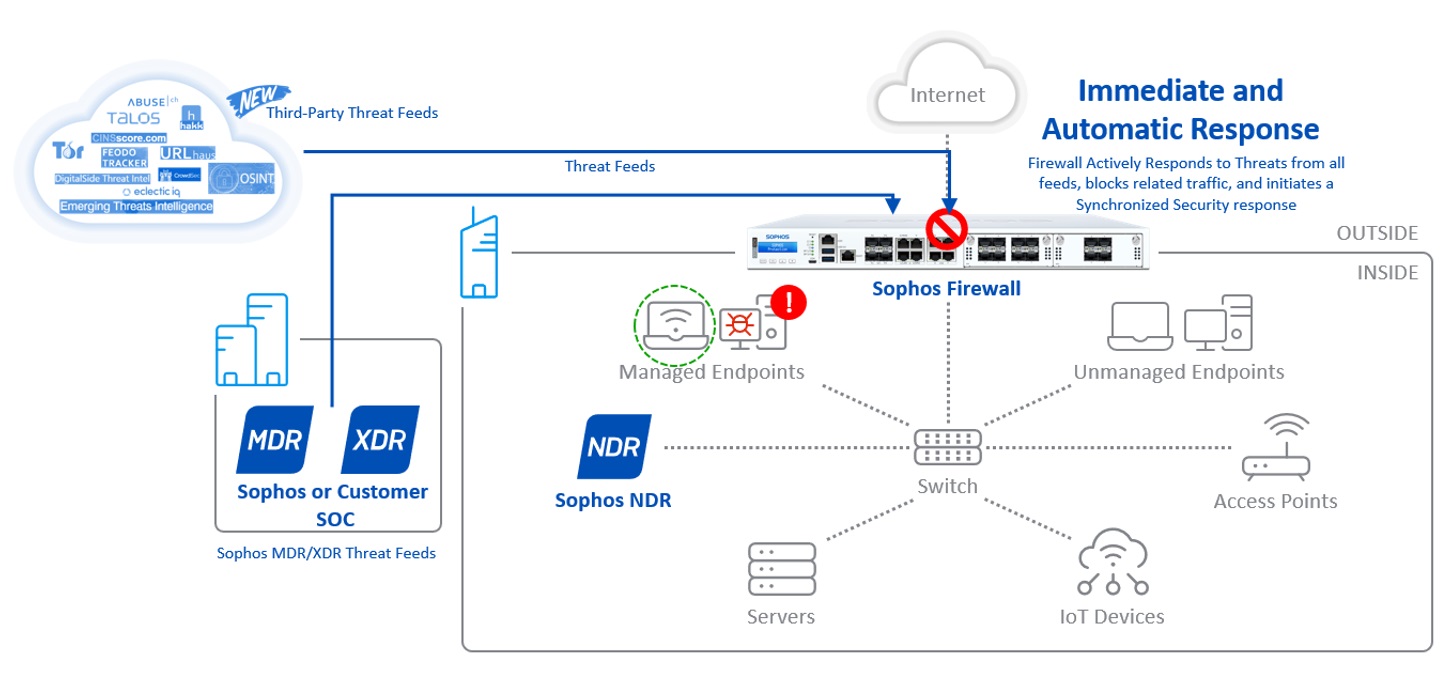
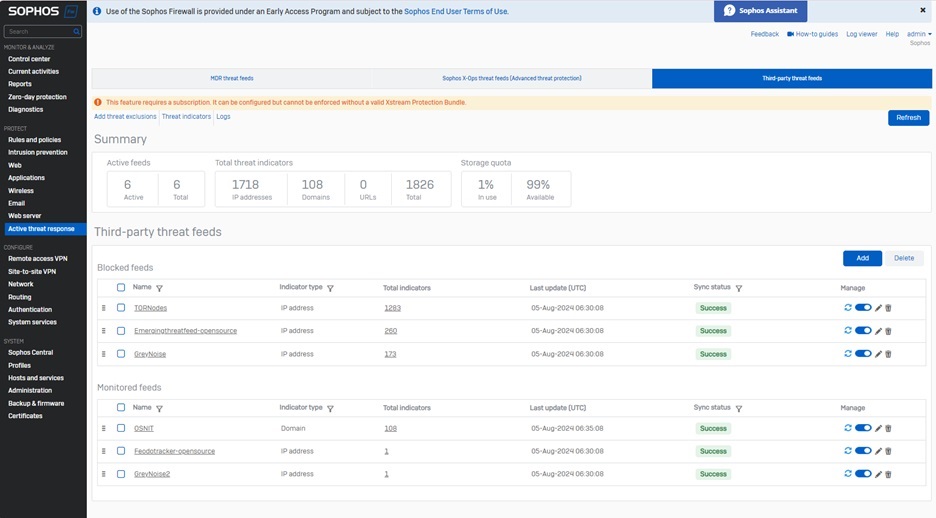
Sophos Firewall v21 adds third-party threat feed support for Active Threat Response.
Active Threat Response was first introduced in v20, implementing a new extensible threat feed framework in Sophos Firewall to automatically respond to active threats. Initial support was provided for dynamic threat intelligence feeds from Sophos X-Ops and Sophos MDR, enabling the firewall to automatically respond by blocking access to any threat published through this framework.
While this is all most customers will ever need, there are certain regions or vertical markets where specific custom threat feeds are encouraged or required. There has also been an interest by our partner community, SoC providers, and many customers for an extensible threat feed capability to support existing or new threat detection and response solutions and services.
To enable these use cases, Sophos Firewall v21 extends the threat feed framework to support third-party threat feeds. Now, you can easily add additional vertical or custom threat feeds to the firewall, which will monitor and respond in the same automatic way – blocking any activity associated with them – across all security engines (IPS, DNS, Web and AV) and without requiring any additional firewall rules.
Third-party threat feeds and Active Threat Response also trigger the same Synchronized Security response as any other red Security Heartbeat condition. Your Sophos Firewall will enforce any firewall rules that contain red Heartbeat conditions and the firewall will also coordinate Lateral Movement Protection with your Sophos Endpoints, which will inform all healthy managed endpoints that there is a compromised host on the LAN so they can block traffic from that device.
Check out the short video below a full demonstration on:
- How to set up third-party threat feeds
- How Active Threat Response and lateral movement protection work
- How to use the new dashboarding and reporting
For more information, consult the online documentation.
A variety of specialized and vertical threat feeds are supported, including those provided by security organizations, industry consortiums, and community-based or open-source threat intelligence sources. A good example is Greynoise, who is featuring the Sophos Firewall integration on their website.
Other great examples include:
- Cisco Talos
- Abuse.ch / URLhaus
- Hakk Solutions
- OSINT (Open-source Intelligence) / DigitalSide
- CINS Score
- CrowdSec
- EclicticIQ
- Feodo Tracker
- And more!
Start taking advantage of this great new capability in Sophos Firewall v21 by participating in the Early Access Program. Simply register for the program, click the link in your email to download the firmware update package, and install it on your Sophos Firewall.
Source: Sophos
Today we have released a new version of our email archiving solutions. Version 24.2.2 for MailStore Server, the MailStore Service Provider Edition and MailStore Home comes with two small but useful improvements that we didn’t want to keep from you until the next quarterly release. We recommend that all customers install this update.
The Improvements of MailStore Version 24.2.2
Firstly, the extraction of text from PDF attachments has been moved to a separate process. This improves the stability of PDF indexing when email attachments containing PDFs are archived.
Secondly, the bug has been fixed that users who have been synchronized from an Active Directory and have MailStore Multi-Factor Authentication (MFA) active cannot log in MailStore using Windows authentication.
Certification: Meeting Data Privacy Requirements
The existing GDPR certification for our software remain unaffected for MailStore Version 24.2.2. You can find all information on the certifications here.
Availability
You can download MailStore version 24.2.2 free of charge from our website.
If your MailStore Server Update & Support Service has expired, please contact us to purchase an upgrade that will allow you to use the latest version of MailStore Server. Read here to find out about other good reasons for having an active Update & Support Service in place.
Interested companies can also download MailStore Server as part of a free, 30-day trial. If you are an MSP and are interested in offering email archiving as a service based on the MailStore SPE, please contact our sales team at partners@mailstore.com. Alternatively, you can sign up as an authorized MailStore Partner with us right now for free.
Source: MailStore
We’re pleased to announce that the early access program (EAP) is now underway. The latest and greatest Sophos Firewall release brings exciting enhancements and top-requested features, including…
Added protection
- Active Threat Response has been extended with support for third-party threat feeds to enable easier integration with specialized and custom threat intelligence sources
- Synchronized Security’s automated response to active threats is also extended to third-party threat feeds
Enhanced scalability
- High-availability (HA) deployments gain added resilience and more seamless transitions for reduced down time
- IPsec VPN gains improved manageability, configuration, and performance
- Authentication and web enhancements
Seamless upgrades
- Any-to-any backup and restore for added flexibility when upgrading
- Port mapping support to make it easy to upgrade to an appliance with a different port configuration
Streamlined management
- Multiple user-experience enhancements, including the overall look and feel, Control Center cards, as well as VPN and static route configuration optimization
- Let’s Encrypt certificate support across many areas of the firewall
- Expanded network object visibility to see where objects are being used
And more!
Download the full What’s New Guide for a complete overview of all the great new features and enhancements in v21.
Getting started today
You can download the upgrade package or installer for v21 from the Sophos Firewall v21 EAP Registration Page. Simply submit your contact info and the download links will be emailed to you straight away.
Sophos Firewall v21 EAP is a fully supported upgrade from all supported versions of v20, v19.5 and v19.0; including the latest v20 MR2.
NOTE: Sophos Firewall v21 does NOT include support for XG and SG Series appliances. XG Series EOL is March 31, 2025.
All support during the EAP will be through our forums on the Sophos Firewall EAP Community.
Please provide feedback using the option at the top of every screen in your Sophos Firewall as shown below or via the Community Forums.

Source: Sophos
Double extortion ransomware is a type of cyber attack in which cybercriminals steal sensitive data and encrypt it. Then, cybercriminals threaten to release the stolen data unless the victim pays a ransom. The additional threat of exfiltration makes this type of cyber attack particularly damaging for organizations, as they face the risk of sensitive data being exposed to the public or sold on the dark web.
Continue reading to learn how double extortion ransomware works and how you can avoid this type of attack.
What is ransomware?
Ransomware is a type of malware – or malicious software – designed to prevent users from accessing their files, data and systems until a ransom is paid. Cybercriminals perform this attack by infecting a user’s device with this specific form of malware that purposefully encrypts the data on their device. In return for the user to gain back access, they demand a ransom.
When a cybercriminal is performing a double extortion ransomware attack, they are not only attempting ransomware but also extorting the data beforehand. They leverage this to increase the ransom payment by threatening to use the stolen data against them.
How double extortion ransomware works
Here is a step-by-step explanation of how a cybercriminal performs a double extortion ransomware attack.
1. Hacker gains access to an organization’s system
Before a cybercriminal can perform a double extortion ransomware attack, they must successfully gain access to an organization’s system. Various methods can be used to gain access to an organization’s systems such as phishing attacks, stealing login credentials, a brute force attack or exploiting a vulnerability in software or a device’s operating system.
2. Hacker moves laterally throughout the network
After a cybercriminal enters into an organization’s system, they move laterally throughout the network to gain increased privileged access to sensitive information and data. While doing so, they’ll also look for ways to prevent themselves from being detected.
3. Hacker steals the organization’s data
Once the cybercriminal gains the privileges needed to steal data, they will remove the data from the device and move it outside the organization’s network.
4. Hacker encrypts data and executes ransomware
The cybercriminal will then hold the data hostage and execute the ransomware attack. The data will become encrypted, making it unreadable and inaccessible to the owner.
5. Victim is notified of the attack
As the ransomware attack occurs, the victim will be notified of the attack on their system through a Distributed Denial-of-Service attack (DDoS) in which the victim’s system becomes disrupted. The user will be given instructions to pay a ransom in exchange for their data back. The data should be returned if the ransom is paid, but sometimes cybercriminals still don’t give the data back. If the ransom isn’t paid at all, the data will either be leaked to the public, deleted or sold.
How to avoid double extortion ransomware attacks
It’s always a security best practice to implement prevention techniques for cyber attacks like ransomware. Here are five ways you can protect your organization from becoming a victim.
Adopt zero-trust security
Zero-trust security is a cybersecurity framework that eliminates implicit trust, requiring all users to be authenticated and authorized before gaining access to network systems. By implementing this strategy in your organization, administrators will have full visibility of who’s connected to the network. More visibility and verification greatly reduce the risk of successful cyber attacks.
Invest in a Privileged Access Management (PAM) solution
Privileged Access Management (PAM) is a cybersecurity solution designed to organize, manage and secure accounts with privileged credentials. Since users with privileged credentials have access to highly sensitive information and data, they become valuable targets to cybercriminals. A PAM solution helps reduce this cyber risk as it allows administrators to securely control access to an organization’s most privileged accounts.
Keep software and Operating Systems (OS) up to date
Updating your device’s software and operating system as soon as an update becomes available ensures that your device will be up to date with the latest security features. If you don’t install a software update, you are more vulnerable to cyber attacks because the security flaws on your device are not patched.
Regularly back up data
By constantly backing up your data, your organization is well protected against human error, hardware failure, data loss, viruses and hackers. For instance, if your organization becomes a victim of double extortion ransomware, having your data backed up can help with recovery and potentially avoid having to pay the ransom.
Train employees on how to spot common cyber threats
Start protecting your organization by educating your employees on common cyber threats targeting your industry. For example, train your employees on how to spot phishing scams by sending them simulated phishing emails throughout their employment.
Stay protected against double extortion ransomware attacks
Falling victim to double extortion ransomware is not only frightening but it could lead to serious consequences for your organization. Fortunately, it’s not impossible for organizations to defend themselves against these ransomware threats.
Start protecting your organization from ransomware by implementing Zero-Trust KeeperPAM® to strengthen the management of your privileged users. To learn more about how Zero-Trust KeeperPAM can protect your organization, request a demo today.
Source: Keeper
Sophos ZTNA provides secure access to networked applications, RDP systems, and web management consoles. It provides a much better alternative to remote access than VPN, offering better security, easier management, and complete transparency for end-users.
To see what ZTNA is all about, we’re offering three free one-year licenses to Sophos Firewall customers, enabling you to start taking advantage of the integrated ZTNA gateway built into every firewall as of v19.5 MR3 and later. Feel free to use them however you like – maybe start with your IT admin staff for remote management and go from there.
The only qualifications for this free offer are that you’re a term Sophos Firewall customer, managing one or more of your firewalls in Sophos Central, and are running v19.5 MR3 or v20 (or later) on your Firewall. This offer will be extended to MSP customers soon.
To take advantage of this offer, simply click the button on the banner in the Firewall Management screen in Sophos Central as outlined below.
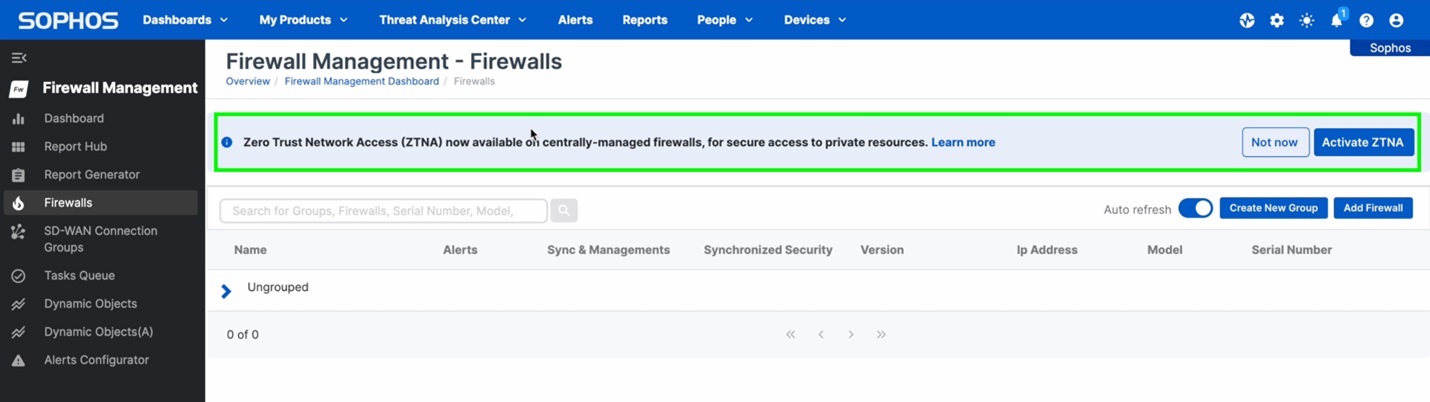
If you’re new to Sophos ZTNA, you can learn more about how it can help secure your application access at Sophos.com/ZTNA.
Check out the Deployment Checklist for other considerations when deploying ZTNA.
You can also access the latest online documentation, and the troubleshooting guide has been updated in case you encounter any issues during configuration.
Source: Sophos
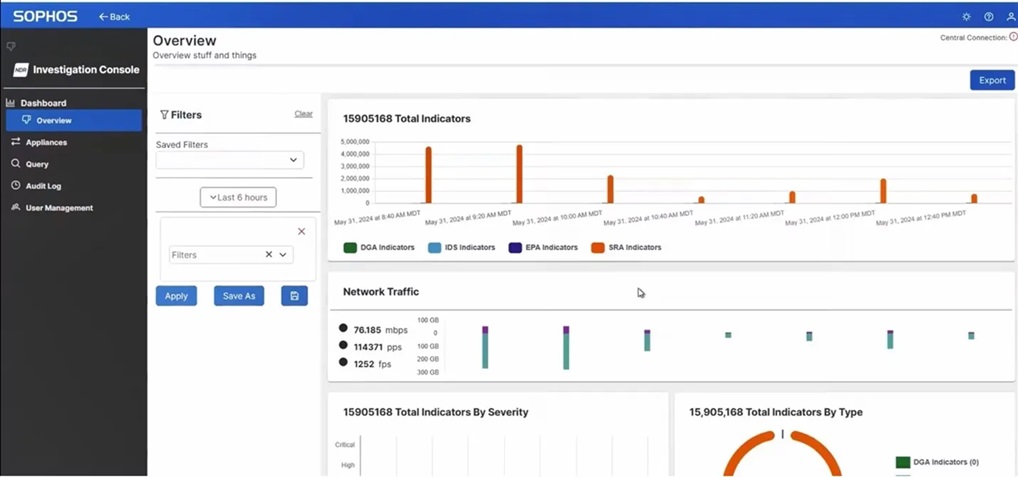
Elevate and extend your threat detection and response with deep network insights – available as a self-managed tool with Sophos XDR and with the 24/7 Sophos MDR service.
However skilled an adversary is at covering their tracks, they always need to cross the network. Sophos NDR sits deep within your network, monitoring network traffic using five real-time threat detection engines to identify signs of malicious or suspicious activity.
With Sophos NDR, you can see and stop attackers faster. Leveraging a combination of AI-powered machine learning, advanced analytics, and rule-based matching techniques, it identifies threats that often go undetected until it’s too late, including:
- Threats on unprotected devices like point-of-sale systems, IoT and OT devices, and legacy operating systems
- Rogue assets that adversaries exploit to launch attacks
- Insider threats such as sensitive data uploads to an offsite location
- Zero-day attacks, and more
Plus, when combined with other security telemetry, Sophos NDR enables threat analysts to paint a more complete, accurate picture of the entire attack path and progression, enabling a faster, more comprehensive response.
What’s new in v1.7
We continue to enhance Sophos NDR to further accelerate network threat detection and response. The rich graphical interface and forensic investigation tools in the new Investigation Console enable analysts to dive deeper into your network activity and pinpoint issues sooner. Use cases include:
- Gain comprehensive visibility into all network activity over the past 30 days
- Analyze application activity, flow risks, and communication on non-standard ports
- Monitor network activity over time to identify suspicious patterns and behaviors
- And much more
For maximum flexibility, Sophos NDR deploys as a virtual appliance on VMware or Microsoft Hyper-V, in the cloud on AWS, or on a range of certified hardware appliances. The latest version includes a refreshed certified hardware portfolio, including a new entry-level model.
To learn more about the latest enhancements, visit the Sophos NDR community forum
Explore Sophos NDR today
Existing Sophos NDR customers benefit from all the latest enhancements automatically and at no additional charge. To get started, visit the community forum and download the Investigation Console image from Sophos Central.
Sophos NDR is available with the self-managed Sophos XDR tool and our 24/7 fully-managed Sophos MDR service. All Sophos customers can now activate a 30-day free trial directly within their Sophos Central console. To learn more and explore your security operations needs, speak with your Sophos partner or account team.
Source: Sophos
The best ways to keep your sensitive data safe include using strong passwords for each of your online accounts, backing up your data regularly and investing in a password manager. Your data is important and should be protected to reduce the risk of identity theft and other cyber threats.
Continue reading to learn what is considered sensitive data, how to protect your sensitive data and how Keeper® can help.
What is considered sensitive data?
Sensitive data includes different types of Personally Identifiable Information (PII) that can reveal your identity.
Your personal, financial, health and business information is considered sensitive data because it is not available in public records and is kept confidential. However, when your sensitive data is compromised, it can lead to identity theft, unauthorized loans being applied for in your name and major credit card fraud.
6 tips to protect your sensitive data
Luckily, there are several steps you can take to protect your sensitive data and maintain your privacy online.
1. Create strong passwords for all online accounts
The first step to protecting your sensitive data is creating a strong and unique password for each of your accounts. A strong password should contain at least 16 characters and a combination of uppercase and lowercase letters, numbers and symbols. You should also never use personal information in your passwords because a cybercriminal can research this information and use it in their attempts at cracking your passwords. The best passwords are completely random and do not incorporate dictionary words like “password” or “dog” because the more common the words are, the easier your passwords are to guess.
2. Set up Multi-Factor Authentication (MFA)
Multi-Factor Authentication (MFA) is crucial in protecting sensitive data because it prevents unauthorized users from accessing your accounts when enabled. MFA adds an extra layer of security by requiring additional proof of your identity before logging in to your account. Some examples of MFA are a PIN, a code from an authenticator app and a fingerprint scan. One of the benefits of enabling MFA on all your accounts is that even if a cybercriminal gains access to your username and password, they still need the additional factor to log in.
3. Use a VPN on public WiFi
Something as simple as connecting to public WiFi can put your sensitive data at risk of being compromised, which is why you should use a Virtual Private Network (VPN). When you use public WiFi, you never know if a cybercriminal has manipulated the network to collect data from anyone who connects to it in what is called a Man-in-the-Middle (MITM) attack. To combat cyber threats like MITM attacks, using a VPN protects your online privacy by creating a private network to encrypt your data, even when you are connected to a public network. For example, if you connect to airport WiFi while traveling, you should use a VPN to ensure that no one in the airport can steal your private information.
4. Enable data encryption
Data encryption is the process that converts your sensitive data from plain text, which anyone can read, into ciphertext, which has random characters that neither people nor machines can read until it’s been decrypted with an encryption key. This process may sound confusing, but encrypting your data ensures that it isn’t read by another user.
You can enable data encryption on your smartphones, computers and online accounts by visiting your device’s settings. For Windows users, within your Settings, visit Privacy & security, then click on Device encryption. If this setting does not appear for you, use BitLocker encryption, which is a Windows security feature that encrypts an entire drive to protect data. Search for BitLocker in your Windows search box, then select BitLocker Drive Encryption and click Turn on BitLocker. For Apple users, your sensitive data is automatically encrypted when you set up a passcode and Touch/Face ID on your device. In the Face ID & Passcode section within your settings, you should see Data protection is enabled at the very bottom of your screen to indicate this.
5. Back up your data regularly
Not only is it important to back up your data regularly in case your device is ever lost or stolen, but you should also continuously back up your data in case your device suffers a malware attack. Imagine you never backed up your phone when, all of a sudden, it was infected with a virus. If you had backed up your data before the virus infected your phone, you could erase all the data on your phone and restore it using the backup made before the infection.
6. Invest in a password manager
Protecting your sensitive data is convenient and secure when you use a password manager like Keeper. Password managers can create strong and unique passwords, safely store your login credentials in an encrypted vault and make it easy to log in to accounts automatically. There are many benefits to using a password manager, such as its ability to generate random passwords, secure password-sharing features and storage of additional information beyond passwords (documents, PDFs, pictures, medical information, etc.). All you need to remember is your master password, which is the password you use to log in to your secure digital vault.
Trust Keeper to protect your sensitive information
The password manager you can trust to protect your sensitive data is Keeper. Keeper uses end-to-end AES-256 encryption to ensure that your sensitive data cannot be accessed by anyone except you. With our zero-knowledge security, Keeper cannot even see your encrypted data. Using Keeper Password Manager allows you to generate and store MFA codes, and it can even autofill these codes on their associated websites for an easier login process.
Start your free 30-day trial of Keeper Password Manager today to discover all that Keeper can do to protect your sensitive data.
Πηγή: Keeper Security
As we approach the October 2024 deadline for EU Member States to enact the NIS 2 Directive, organizations that do business in Europe must prepare for the significant changes it brings to cybersecurity compliance.
This article aims to shed light on the NIS 2 Directive, its necessity, key updates from the original NIS Directive, and how businesses can prepare for compliance. For an even deeper dive on the directive, download the Sophos NIS 2 Directive whitepaper.
What is the NIS 2 Directive?
The NIS 2 Directive is an evolution of the original Network and Information Systems (NIS) Directive, implemented to bolster the cybersecurity posture of EU member states. The initial NIS Directive, enacted in 2016, established guidelines for improving cybersecurity resilience across the EU. However, with the increasing sophistication and frequency of cyber-attacks, especially during and after the Covid-19 pandemic, there was a clear need for more stringent and comprehensive regulations.
Cyber threats have escalated to an industrial scale, with ransomware attacks becoming particularly prevalent. In June 2024, a hacking group known as Qilin, with ties to the Kremlin, carried out an attack on Synnovis, which is a pathology lab used by the UK’s National Health Service (NHS). The hackers demanded a £40 million ransom, and when the NHS refused to pay, hackers released the stolen data on the dark web.
Additionally, geopolitical tensions, such as the Russian invasion of Ukraine, have underscored the necessity for robust cybersecurity measures. The NIS 2 Directive aims to address these challenges by enhancing the security and resilience of essential and important entities across the EU.
Implications for non-EU Companies
While primarily aimed at EU Member States, non-EU companies operating within the EU or providing services to EU entities will also be impacted. Many national regulations are currently not as wide-ranging as the NIS 2 Directive; however, it would be prudent to expect further changes to local law as the plans for the EU legislation are developed further.
By proactively addressing the challenges outlined below, non-EU companies can better protect themselves and their customers from evolving cyber threats while avoiding severe penalties for non-compliance.
Key updates from NIS to NIS 2
The NIS 2 Directive introduces several critical updates and expansions from the original NIS Directive:
- Broader Scope of Covered Entities:
- Essential and Important Entities: NIS 2 categorizes entities into “essential” and “important” based on their sector and criticality. This expansion includes more sectors, such as wastewater, healthcare supply chains, postal and courier services, aerospace, public administration, and digital infrastructure.
- Supply Chain and Service Providers: Organizations involved in the supply chain and those providing critical support services are now explicitly covered, emphasizing the importance of securing interconnected networks.
- Enhanced Cybersecurity Standards:
- Mandatory Measures: Article 21 of the directive outlines mandatory cybersecurity measures, including basic cyber hygiene, vulnerability management, supply chain security, encryption, asset management, access control, and zero trust security.
- Incident Handling and Reporting: The directive mandates more rigorous incident reporting requirements, ensuring timely and consistent responses to cyber threats across the EU.
- Increased Accountability and Penalties:
- Senior Management Liability: Senior management can be held personally liable for non-compliance, underscoring the importance of executive involvement in cybersecurity governance.
- Fines and Sanctions: Organizations can face significant fines, up to €10 million or 2% of global turnover, for failing to comply with the directive.
The following 18 sectors are covered by the NIS 2 Directive:
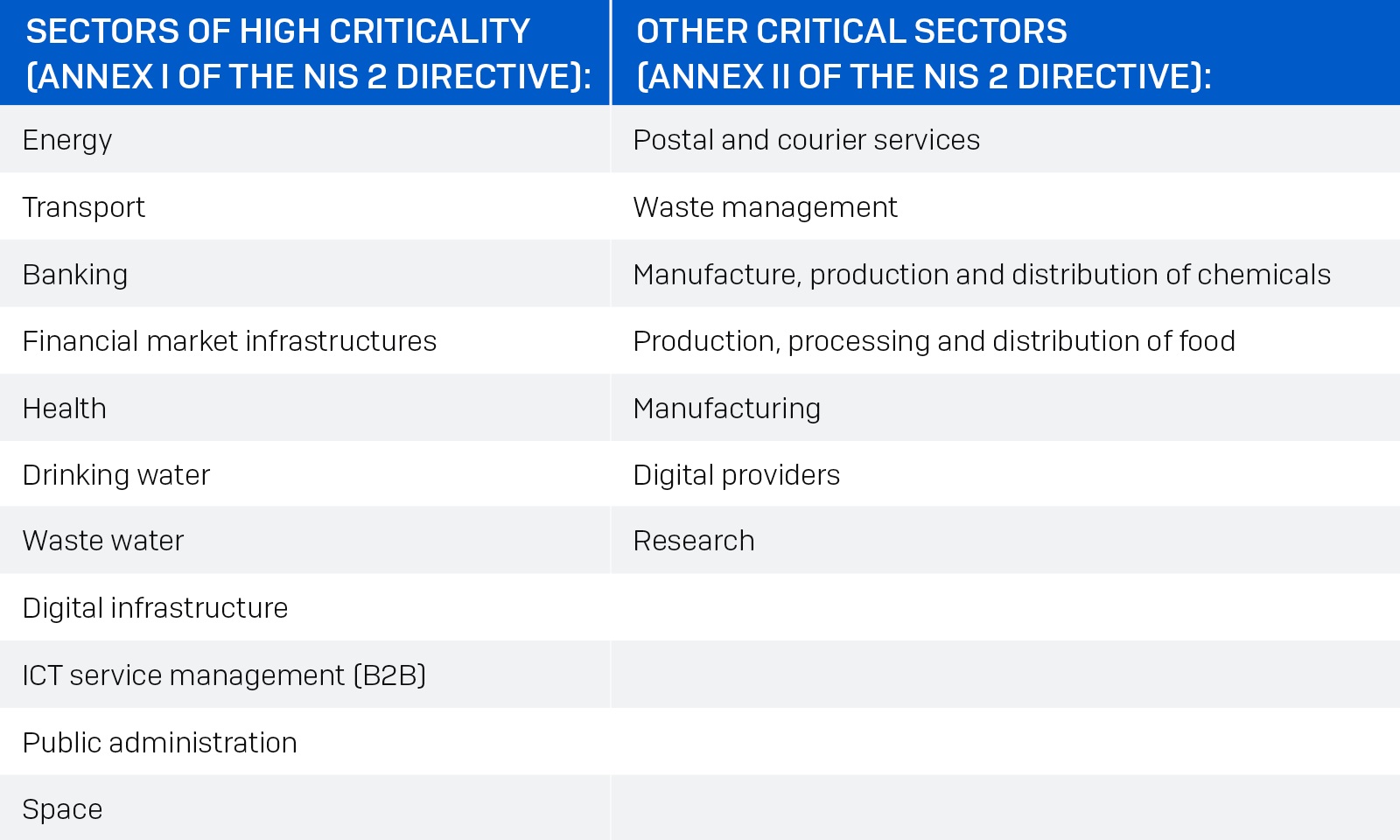
The following table illustrates the increase in sectors covered by the NIS 2 Directive as compared to the first NIS directive:

Impact on cybersecurity compliance
The NIS 2 Directive significantly impacts how organizations approach cybersecurity compliance. Businesses must adopt a proactive stance, integrating comprehensive risk management processes and ensuring adherence to the stringent standards set forth in the directive. The emphasis on mandatory measures and the potential for severe penalties necessitate a thorough review and enhancement of existing cybersecurity practices.
Organizations will need to allocate sufficient resources to meet these requirements. Estimates suggest that businesses already covered by the original NIS Directive may need to increase their cybersecurity budgets by up to 12%, while those newly covered could see budget increases of up to 22%, according to John Noble, former Director of the National Cyber Security Centre speaking on Sophos Spotlight: NIS2 Directive and Understanding Cybersecurity Compliance.
Preparing for NIS 2 compliance
To ensure compliance with the NIS 2 Directive, organizations should take the following steps:
- Assess Applicability:
- Determine whether your organization falls under the categories of essential or important entities. This involves evaluating your sector, the criticality of your services, and your operational footprint within the EU.
- Understand Jurisdiction:
- Identify which EU member states have jurisdiction over your operations for NIS 2 purposes. This is crucial for understanding specific national requirements and reporting obligations.
- Implement Cybersecurity Risk Management:
- Conduct a comprehensive risk analysis to identify potential cybersecurity threats and vulnerabilities.
- Implement the mandatory measures outlined in Article 21, mapping them against an appropriate security framework such as ISO 27001 or the NIST Cybersecurity Framework.
- Strengthen Supply Chain Security:
- Focus on mitigating risks within your supply chain, particularly concerning software and service providers. This includes ensuring that third-party vendors comply with NIS 2 standards.
- Develop an Incident Response Plan:
- Formalize an incident response plan that includes clear protocols for reporting cyber incidents to relevant national authorities. Ensure that significant incidents are reported within the 24-hour timeframe specified by the directive.
- Engage Senior Management:
- Secure formal high-level management sign-off on your compliance strategy. Senior management involvement is critical for demonstrating a commitment to cybersecurity and ensuring that necessary resources are allocated.
The NIS2 Directive represents a significant step forward in enhancing the cybersecurity resilience of organizations across Europe. By understanding the key updates and taking proactive measures to ensure compliance, businesses can better protect themselves against the growing threat of cyber-attacks.
As the October deadline approaches, it is imperative for senior management and IT security professionals to prioritize NIS 2 compliance, leveraging resources such as the Sophos whitepaper to guide their efforts.
Source: Sophos
The U.S. government recently announced that it is banning the sale of Kaspersky antivirus products due to national security concerns. If you’re in the U.S. and currently use Kaspersky products today, you have a tight deadline to switch to an alternative provider. After September 29, 2024, U.S. organizations will no longer receive updates or support from Kaspersky. Outside the U.S., many Kaspersky users are also re-evaluating their endpoint security provision.
Thankfully, wherever you are based, you can migrate to Sophos Endpoint in minutes.
Stronger endpoint security for small and midsize businesses
Sophos Endpoint is trusted by over 300,000 organizations worldwide, including thousands of small and midsize businesses. With Sophos Endpoint, you benefit from:
- Affordable threat protection | Enterprise-grade cybersecurity that’s cost-effective for businesses of any size.
- Quick and easy setup | Install and go with simple, one-time installation – including automatic removal of Kaspersky antivirus when you run the Sophos Endpoint installer.
- Simple management and reporting | A single cloud-based dashboard for security alerts, reporting, and management. Recommended security settings are enabled automatically when you install Sophos Endpoint; no complex configuration is required.
The ban on Kaspersky products in the U.S. provides an opportunity to uplevel your defenses. IT security teams around the globe are seeking replacement solutions that provide the best protection and usability, and less management burden. Moving to Sophos Endpoint enables you to leverage superior protection with additional capabilities and benefits that other solutions lack, including:
- Adaptive defenses | Industry-first dynamic defenses that automatically adapt in response to hands-on-keyboard attacks, reducing the attack surface and stopping sophisticated adversaries in their tracks. Watch this quick demo.
- Remote ransomware protection | Sophos provides the most robust zero-touch endpoint defense against remote ransomware. Alternative endpoint security solutions, including Microsoft, CrowdStrike, and SentinelOne, cannot protect against this increasingly pervasive threat.
- Automated account health check | Misconfigured policy settings can compromise your security posture. The Account Health Check identifies security posture drift and risky configurations, enabling administrators to remediate issues with one click.
Learn more about the advantages of Sophos compared to other cybersecurity solutions and watch the overview video to learn more.
Top-rated by customers, industry analysts, and independent testers
Don’t take our word for it! Customers have named Sophos a 2024 Gartner® Peer Insights™ Customers’ Choice for Endpoint Protection Platforms for the third consecutive year. Sophos stands tall with an impressive customer rating of 4.8/5 (as of April 30, 2024) and the highest number of independent Gartner-verified reviews of any vendor.
Analyst firm IDC evaluates how endpoint security solutions meet customers’ needs and named Sophos a Leader in the 2024 IDC MarketScape for Modern Endpoint Security for Small and Midsized Businesses. According to the IDC MarketScape evaluation, “Sophos is a strong consideration for small businesses, particularly those with large business security requirements that have little to no in-house security expertise.”
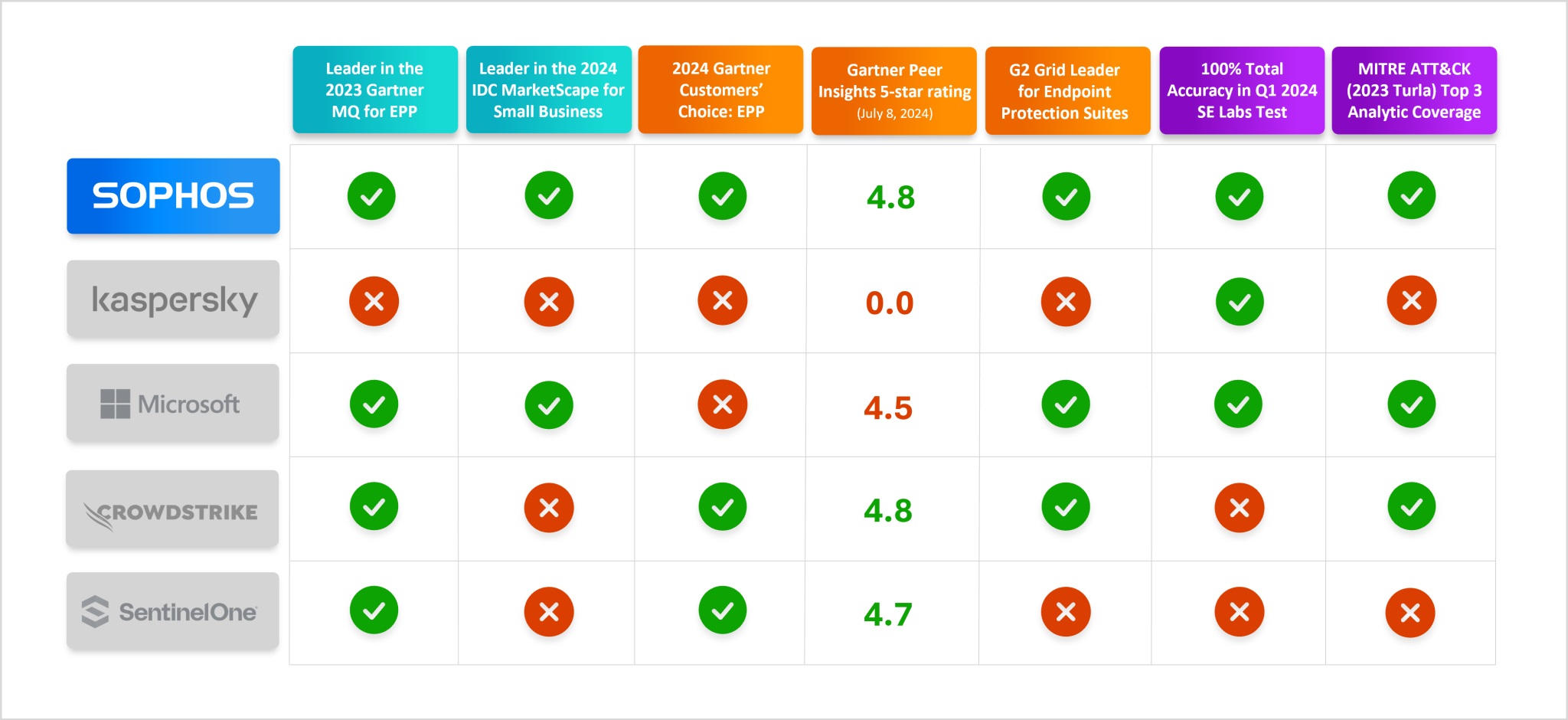
See our wide range of third-party endorsements and evaluations.
Time to upgrade to a fully managed security service?
Cybersecurity is becoming so complex that many small and midsize businesses can’t keep up. Replacing Kaspersky antivirus products could be the ideal opportunity to consider taking advantage of a 24/7 managed security service.
Trusted by over 23,000 organizations worldwide, Sophos Managed Detection and Response (MDR) enables you to reduce the risks and costs associated with potentially catastrophic security incidents. Moreover, all Sophos MDR subscriptions include the Sophos Endpoint product within the standard price.
Learn more about Sophos Endpoint on the Sophos website.
Source: Sophos
Sophos Firewall v20 MR2 includes important enhancements such as an exciting new backup and restore assistant, Active Directory SSO improvements, and web protection optimizations.
Backup and restore assistant
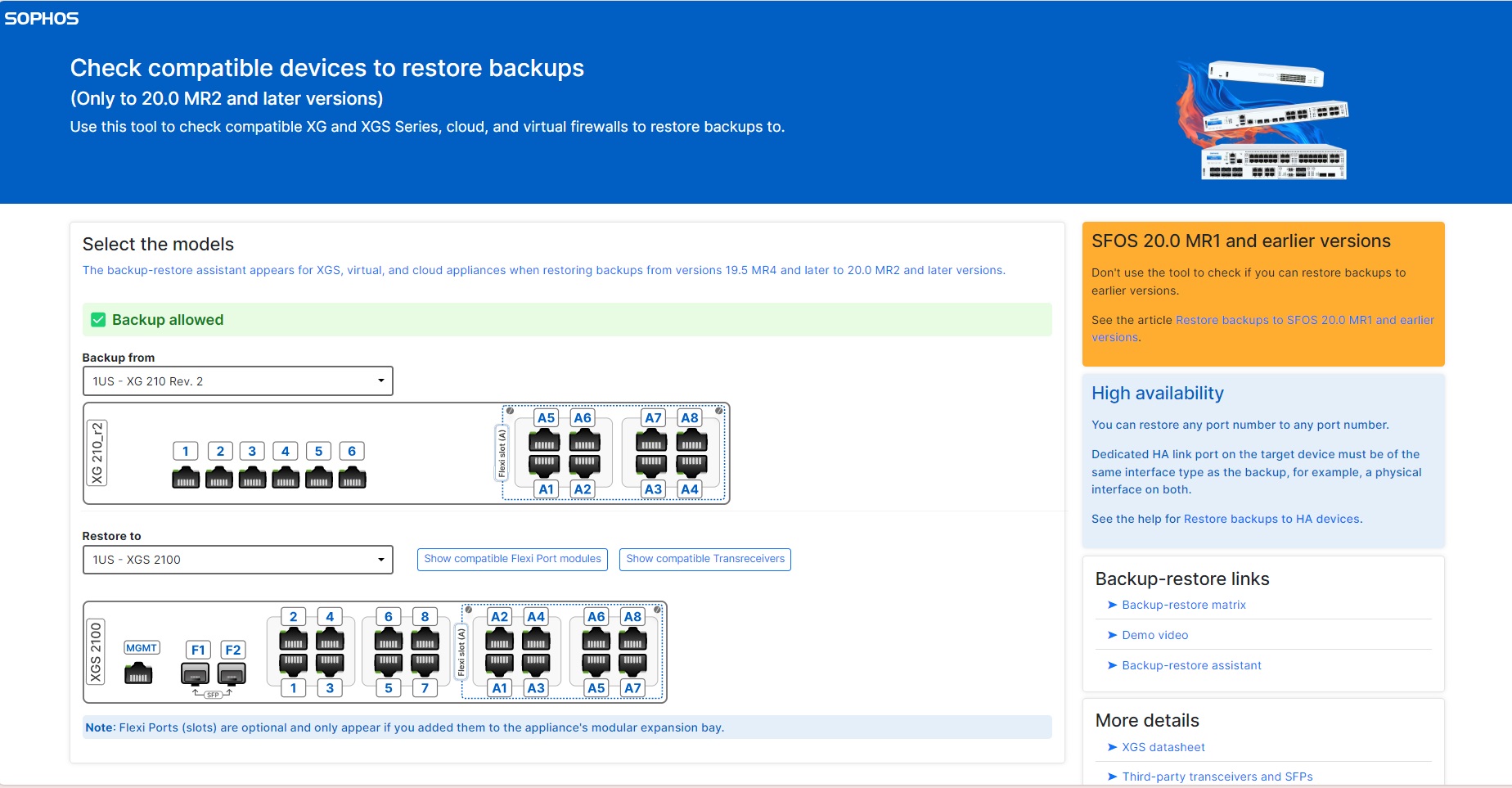
The new Sophos Firewall backup and restore assistant enables firewall configuration backups to be easily restored on a different firewall appliance with flexible interface mapping options.
This makes it easy to upgrade Sophos Firewall XG Series to XGS Series, upgrade any XGS Series model to any other XGS Series model, or even migrate to or from software or virtual appliances.
This also means you can easily migrate interfaces to higher-speed ports on your new or upgraded firewall.
You can also get creative and export a configuration template from a virtual appliance and then restore it on multiple hardware or virtual deployments to simplify repetitive configurations.
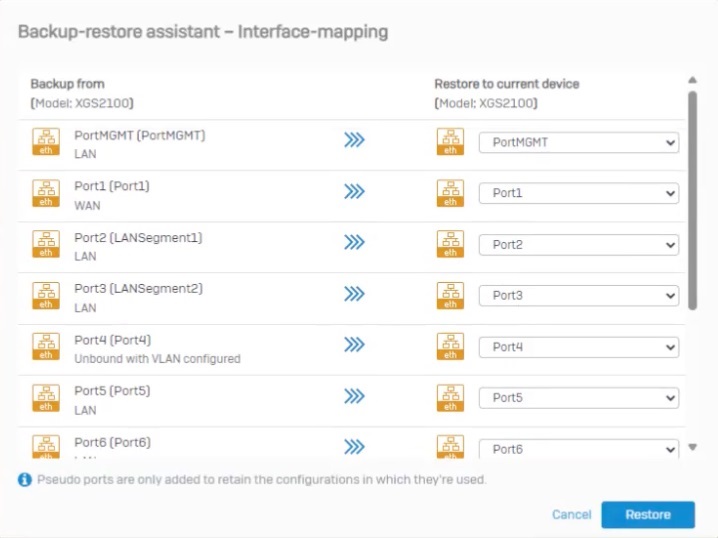
There are a few key dependencies or pre-requisites to take full advantage of this new assistant:
- Backups of XG Series appliances should be made using v19.5 MR4, v20, or later.
- Backups of XGS Series appliances need to be made using this release: v20 MR2 (or later)
This video covers the prerequisites and how to use this new assistant in more detail:
You can also check the compatibility of the appliances you plan to back up/restore and see the exact port configuration (including available Flexi Port modules) using a new tool that is available at https://docs.sophos.com/nsg/sophos-firewall/reference/backup_restore/port_mapping/en-us/
Additional enhancements in Sophos Firewall v20 MR2
- Active Directory Single Sign-on now provides improved support for high-availability failover situations
- Active Directory Single Sign-on adds support for performing the Kerberos/NTLM handshake over HTTP or HTTPS for a more transparent SSO experience when HSTS is enforced
- Web Protection performance is enhanced by reducing the system load when enforcing SafeSearch, YouTube restrictions, Google App login domain, or Azure AD tenant restrictions
- Web Protection cipher customization now enables you to strike the best balance for your network between cipher compatibility, security, and audit compliance
How to get the firmware and documentation
Sophos Firewall OS v20 MR2 is a free upgrade for all licensed Sophos Firewall customers and should be applied to all supported firewall devices as soon as possible to ensure that you have all the latest security, reliability, and performance fixes.
This firmware release will follow our standard update process. You can manually download SFOS v20 MR2 from Sophos Central and update anytime. Otherwise, it will be rolled out to all connected devices over the coming weeks. A notification will appear on your local device or Sophos Central management console when the update is available, allowing you to schedule the update at your convenience.
Sophos Firewall OS v20 MR2 is a fully supported upgrade from all previous versions of v20, v19.5 and v19.0. Please refer to the Upgrade Information tab in the release notes for more details.
Full product documentation is available online and within the product.
Source: Sophos
The latest annual Sophos study of the real-world ransomware experiences of energy, oil/gas and utilities sector – a core element of the critical infrastructure supporting businesses – explores the full victim journey, from attack rate and root cause to operational impact and business outcomes.
This year’s report sheds light on new areas of study for the sector, including an exploration of ransom demands vs. ransom payments and how often energy, oil/gas and utilities organizations receive support from law enforcement bodies to remediate the attack.
Download the report to get the full findings.
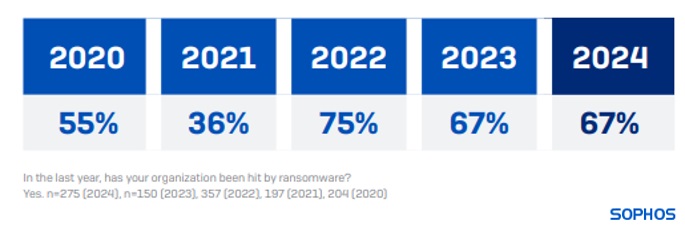
Attack rates and recovery rates have remained steady
67% of energy, oil/gas and utilities organizations were hit by ransomware in 2024, identical to the attack rate reported in 2023.
98% of energy, oil/gas and utilities organizations hit by ransomware in the past year said that the cybercriminals attempted to compromise their backups during the attack. Four in five (79%) of these backup compromise attempts were successful, the highest rate of successful backup compromise across all sectors.
80% of ransomware attacks on energy, oil/gas and utilities organizations resulted in data encryption in 2024, in line with the encryption rate reported by this sector in 2023 (79%) but higher than the 2024 cross-sector average of 70%.
The mean cost in energy, oil/gas and utilities organizations to recover from a ransomware attack was $3.12M in 2024, similar to the $3.17M reported in 2023.
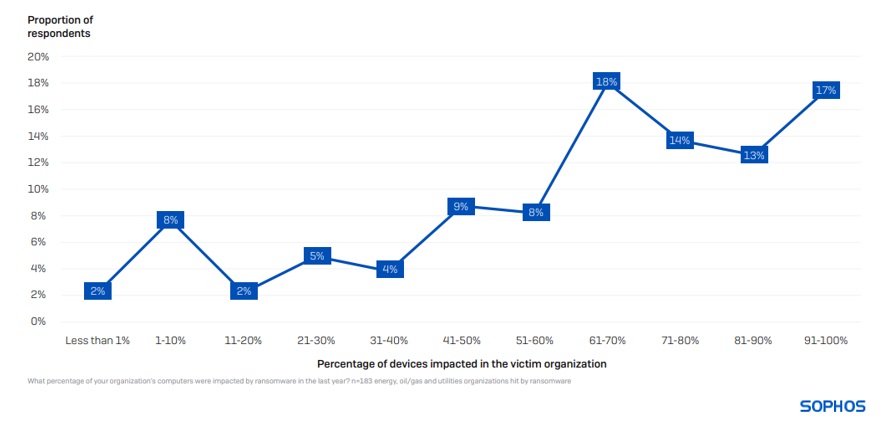
Devices impacted in a ransomware attack
On average, 62% of computers in energy, oil/gas and utilities are impacted by a ransomware attack, considerably above the cross-sector average of 49%. Unlike other sectors where only a small percentage of organizations have their full environments encrypted, approximately one in five energy, oil/gas and utilities organizations (17%) reported that 91% or more of their devices were impacted.
The propensity to use backups for data recovery has decreased
61% of energy, oil/gas and utilities organizations paid the ransom to get encrypted data back, whereas only 51% restored encrypted data using backups – the lowest rate of backup use reported across all sectors. This is the first time that energy, oil/gas and utilities organizations have reported a higher propensity to pay the ransom than use backups. In comparison, globally, 56% paid the ransom, and 68% used backups.
This year’s findings represent a marked change from the previous two years when the sector enjoyed impressive rates of backup use (70% in 2023 and 77% in 2022).
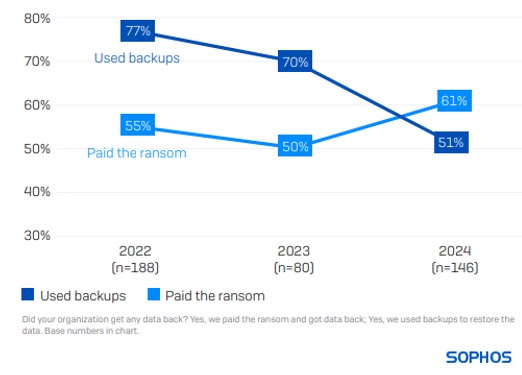
A notable change over the last year is the increase in the propensity for victims to use multiple approaches to recover encrypted data (e.g., paying the ransom and using backups). This time, 35% of energy, oil/gas and utilities organizations that had data encrypted reported using more than one method, higher than the 26% reported in 2023.
Critical Infrastructure victims don’t often pay the initial ransom sum demanded
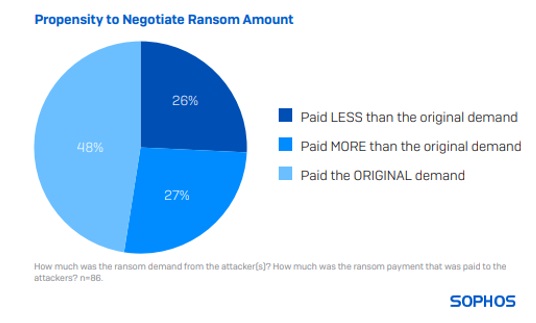
86 energy, oil/gas and utilities respondents whose organizations paid the ransom shared the actual sum paid, revealing that the average (median) payment was $2.5M in 2024.
A little less than half (48%) of respondents said their payment matched the original request. 26% paid less than the original demand, and 27% paid more.
Looking at the data by industry, energy, oil/gas and utilities has the highest propensity to pay the original ransom amount demanded by attackers. It is also the sector with the second lowest propensity to pay less than the original demand.
Download the full report for more insights into ransom payments and many other areas.
Source: Sophos
As a Sophos Firewall customer, your security is our top priority. We’ve not only invested heavily in ensuring Sophos Firewall is the most secure firewall on the market, but we continuously work to make it the most difficult target for hackers, all while helping keep your network and organization safe from future attacks through proactive monitoring.
Here are a few examples of how we have invested in making Sophos Firewall secure by design.
Best practices built in
Our goal is to ensure your firewall’s security posture is optimally configured right from the start by building in security best practices for easy out-of-the-box deployment. You get powerful protection for your network as soon as it’s connected and turned on.
It starts with strict and granular access controls and default firewall rules that provide security and control for your network traffic. Sophos Firewall also makes it quick and easy to set up additional features. ZTNA, for instance, protects your applications while allowing secure access for remote workers without opening any ports on the perimeter.
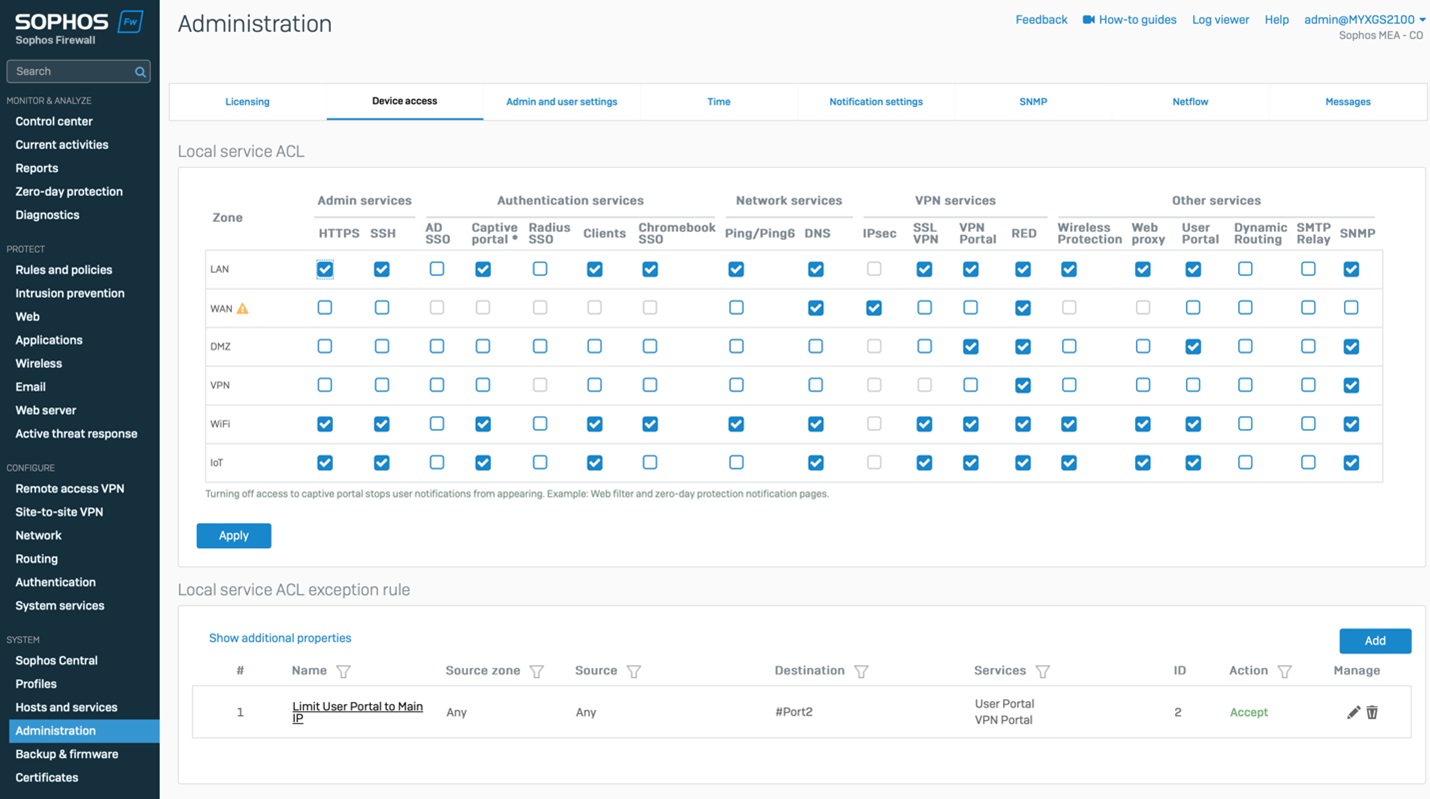
Hardened against attack
Taking measures to prevent attacks from targeting your firewall is critically important. Sophos Firewall has been designed from the start with security in mind and is continually being hardened against attacks with new technologies.
Sophos Central management offers the ultimate in secure remote management. Recent enhancements include improved multi-factor authentication, containerization for the VPN portal and other trust boundaries, strict default access controls, rapid hotfix support, and more, making Sophos Firewall a formidable opponent for attackers.
Automated hotfix response
Sometimes it’s important to patch urgent security issues quickly before the next regular firmware update. To that end, Sophos Firewall integrates an innovative hotfix capability that enables us to push urgent and important patches out to your firewall “over the air” to address any new zero-day vulnerabilities or other critical issues that arise between regular firmware updates.
While it’s still vitally important that you keep your firewall up to date with the latest firmware release (as every release includes important security fixes, as well as performance, stability, and feature enhancements), this enables a rapid fix to be applied without requiring any downtime normally associated with a firmware upgrade.
Proactive monitoring
You depend on Sophos to be proactive, transparent, and responsive. That’s why we continually monitor our global install base of customer firewalls and rapidly react to any incident.
This enables us to identify incidents before our customers thanks to telemetry collection and analysis. You can rest assured that if a single customer anywhere in the world has their firewall attacked, we’re working tirelessly to help shut the attack down and prevent it from happening elsewhere.
In addition, our mature vulnerability disclosure program ensures we’re transparent and communicative with every security vulnerability or incident, so you’re as well-equipped as possible to protect your network. We also offer the most active and well-funded bug bounty program in the industry to get ahead of any potential issues before they can become a problem.
Additional best practices
In addition to the best practices we build into your firewall, be sure to follow the Hardening Your Sophos Firewall Guide for additional best practices you should follow when setting up and administering your Sophos Firewall.
Download the Sophos Firewall Security Brief if you would like a PDF version covering these capabilities.
And if you’re new to Sophos Firewall, be sure to check out Sophos Firewall’s powerful protection features and take it for a test drive today.
Source: Sophos
600 IT/cybersecurity leaders share their ransomware experiences, revealing the realities facing education providers today.
Sophos’ latest annual study of the real-world ransomware experiences of educational organizations explores how ransomware’s impact has evolved in the last four years. It focuses on the full victim journey, from attack rate and root cause to operational impact and business outcomes.
This year’s report explores new areas of study for the sector, including an exploration of ransom demands vs. ransom payments and how often educational organizations receive support from law enforcement bodies to remediate the attack.
Download the report to get the full findings.
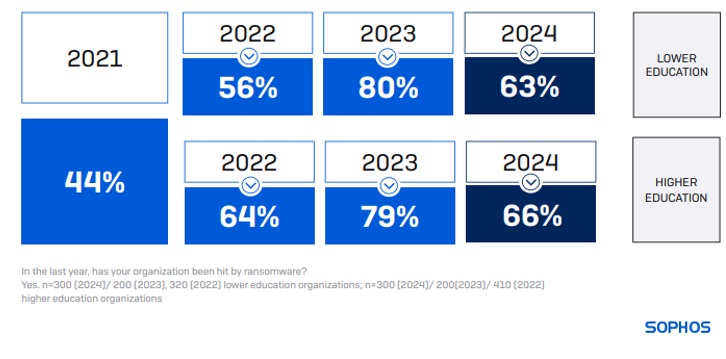
Attack rates have declined, but recovery costs have more than doubled
63% of lower education and 66% of higher education organizations were hit by ransomware in the last year, a considerable decrease from the 80% and 79% reported in 2023, respectively. However, the attack rates in education remain higher than the global cross-sector average of 59%.
95% of educational organizations hit by ransomware in the past year said that the cybercriminals attempted to compromise their backups during the attack. Of them, 71% were successful, which is the second highest rate of successful backup compromise across all sectors after the energy, oil/gas and utilities sector.
85% of ransomware attacks on lower education and 77% on higher education organizations resulted in data encryption in the last year, slightly higher than 81% and 73%, respectively, reported in the previous year. For lower education, this is the second consecutive year of an increase in encryption rate, with only state/local government (98%) more likely to have data encrypted in an attack.
The mean cost in 2024 for lower education organizations to recover from a ransomware attack was $3.76M, more than double the $1.59M reported in 2023. Higher education organizations reported a mean cost of $4.02M, almost four times higher than the $1.06M reported in 2023.
Devices impacted in a ransomware attack
On average, 52% of computers in lower education and 50% in higher education are impacted by a ransomware attack, slightly above the cross-sector average of 49%. Having a full environment encrypted is extremely rare. Only 2% of lower education organizations and 1% of higher education organizations reported that 91% or more of their devices were impacted.

The propensity to pay the ransom has increased
62% in lower education paid the ransom to get encrypted data back, while 75% restored encrypted data using backups. At the same time, 67% of higher education organizations paid the ransom to restore data, whereas 78% used backups.
Higher education reported the second-highest propensity to use backups for data restoration along with state/local government organizations. It also ranks second highest in the propensity to pay the ransom to restore encrypted data, whereas lower education organizations rank third.
The three-year view of the education sector reveals an increase in backup use. In 2023, higher education was among the bottom three sectors globally for backup use, jumping to second place in 2024, alongside state/local government. Unfortunately, the propensity to pay the ransom has progressively increased for both lower and higher education organizations in the last three years.

A notable change over the last year is the increase in the propensity for victims to use multiple approaches to recover encrypted data (e.g., paying the ransom and using backups). This time, 65% of lower education and 69% of higher education organizations that had data encrypted reported using more than one method, almost three times the rates reported in 2023 (23% in lower education and 22% in higher education organizations.)
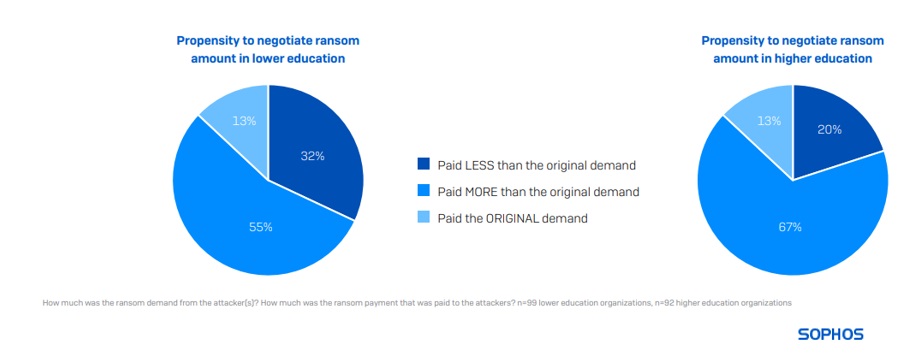
Victims rarely pay the initial ransom sum demanded
99 lower education and 92 higher education respondents whose organizations paid the ransom shared the actual sum paid, revealing that the average (median) payment in lower education was $6.6M last year. For higher education, the average (median) payment was $4.4M.
Only 13% of education victims said their payment matched the original request. 32% of lower education and 20% of higher education respondents paid less than the original demand, while 55% of lower education and 67% of higher education organizations paid more. Globally, higher education is the sector most likely to pay more than the original demand.
Download the full report for more insights into ransom payments and many other areas.
Source: Sophos