Organizations should implement the principle of least privilege to protect their sensitive data from unauthorized access. To implement the principle of least privilege, organizations need to define roles and permissions, invest in a Privileged Access Management (PAM) solution, enforce MFA, automatically rotate credentials for privileged accounts, segment networks and regularly audit network privileges.
Continue reading to learn more about the principle of least privilege, why it is important and how your organization can implement it.
What Is the Principle of Least Privilege and Why Is It Important?
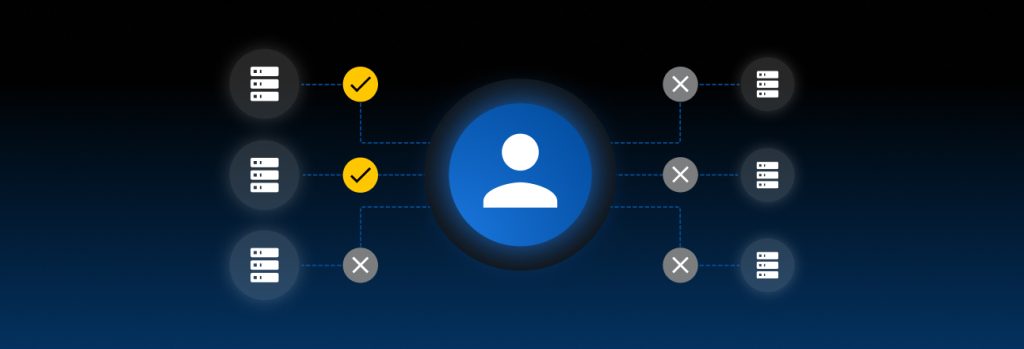
The Principle of Least Privilege (PoLP) is a cybersecurity concept in which users are granted just enough network access to data and systems to do their jobs, and no more. Least privilege access applies to users, processes, applications, systems and IoT devices. It prevents users from accessing resources they do not need and limits what they can do with the resources they do have access to.
Least privilege access is important because it:
- Reduces attack surface: Attack surface refers to the possible entry points where cybercriminals can access a system and steal data. By limiting privileges, organizations can reduce the possible entry points for unauthorized access and easily prevent any potential threats.
- Minimizes insider threats: Insider threats are cyber threats originating from within an organization when current or former employees, partners, contractors or vendors heighten the risk of sensitive data and systems becoming compromised. By limiting access, organizations can minimize insider threats from compromising sensitive data, whether by accident or intentionally.
- Prevents lateral movement: Lateral movement is when cybercriminals move deeper within an organization’s network after gaining initial access by escalating their privileges. Least privilege access prevents threat actors from moving laterally throughout a network. The cybercriminal will be restricted to the systems and data of the compromised account.
- Adheres to regulatory compliance: Least privilege access helps organizations protect sensitive data and adhere to regulatory and industry compliance frameworks such as GDPR, HIPAA and SOX.
6 Ways Organizations Can Implement the Principle of Least Privilege
The principle of least privilege will help organizations improve their security and protect their sensitive information from unauthorized access. Here are six ways organizations can implement the principle of least privilege.
Define roles and permissions
The first step of implementing the PoLP is to define roles and permissions. Organizations need to determine the level of access to specific sensitive data and systems – who should be accessing these resources, why they are accessing them and how long they should have access to them. They then need to define what role each member of the organization has and what permissions each member has based on their role. They should use Role-Based Access Control (RBAC) to help define roles and permissions.
RBAC grants specific network permissions based on a user’s defined role. Users will have limited network access to specific data and systems based on their role within the organization and what they need to do their jobs. They should not have access to any resources outside of their assigned job duties. RBAC restricts what users can do with a system or file they have access to. For example, marketing employees need access to customer data but not developer environments, and IT administrators need access to developer environments but not financial records.
Invest in a PAM solution
To help manage and keep track of privileged accounts, organizations need to invest in a PAM solution. PAM refers to securing and managing accounts with access to highly sensitive systems and data. These privileged accounts can range from local administrator accounts to non-human service accounts to privileged user accounts. With a PAM solution, organizations can implement least privilege access since they have full visibility into their entire data infrastructure and how much access users have to sensitive data. They can determine who can access privileged accounts and how much access each user should have. PAM solutions help prevent privileged accounts from being misused by insider threats and compromised by threat actors.
Enforce MFA
Multi-Factor Authentication (MFA) is a security protocol that requires additional authentication. To access a privileged account protected by MFA, authorized users must provide the login credentials to the account and an extra form of verification. Organizations need to enforce MFA on all privileged accounts to add an extra layer of security and ensure that only authorized users can access them. Even if the login credentials to the privileged account were compromised, cybercriminals could not access the account because it’s protected by MFA and they cannot provide additional authentication.
Automatically rotate credentials for privileged accounts
Password rotation is a cybersecurity practice in which passwords are regularly changed on a predetermined schedule. Organizations should use automated password rotation to protect privileged accounts from unauthorized access. Since privileged accounts provide access to sensitive information, organizations need to regularly change their passwords for these accounts. This locks out users who do not need access to the accounts anymore and prevents cybercriminals from cracking the passwords. Using automated password rotation ensures that privileged accounts are protected with strong and unique passwords after every rotation.
Segment networks
Network segmentation divides and isolates parts of an organization’s network to control access to sensitive information. These segments are divided based on the type of sensitive information stored and the users who need access. Segmentation limits access to the entire network and only allows users to access resources within their respective segments. It helps prevent cybercriminals who have gained unauthorized access to an organization’s network from moving laterally across the network because the cybercriminal is limited to only the network segment they accessed. To provide better security to their network, organizations can create micro-segments which are isolated parts of the network within a segmented network.
Regularly audit network privileges
Organizations need to regularly audit network privileges to ensure the right users have the necessary access they need to do their jobs and remove any users who do not need access to specific resources anymore. Regularly auditing network privileges and access prevents privilege creep, which is when users have accumulated higher levels of access than they need. It helps prevent misuse by potential insider threats and unauthorized access by cybercriminals.
Use Keeper® To Implement the Principle of Least Privilege
The best way to implement the principle of least privilege is with a PAM solution. With a PAM solution, organizations can see who has access to their network and limit user access to sensitive data. They can secure privileged accounts by ensuring employees are protecting them with strong and unique passwords and MFA.
KeeperPAM™ is a privileged access management solution that helps simplify privilege management by combining Keeper Enterprise Password Manager (EPM), Keeper Secrets Manager (KSM) and Keeper Connection Manager (KCM) into one, unified solution. With KeeperPAM, organizations can achieve complete visibility, security and control over every privileged user on every device.
Source: Keeper