News
“This demands your attention no matter what size your organization.”
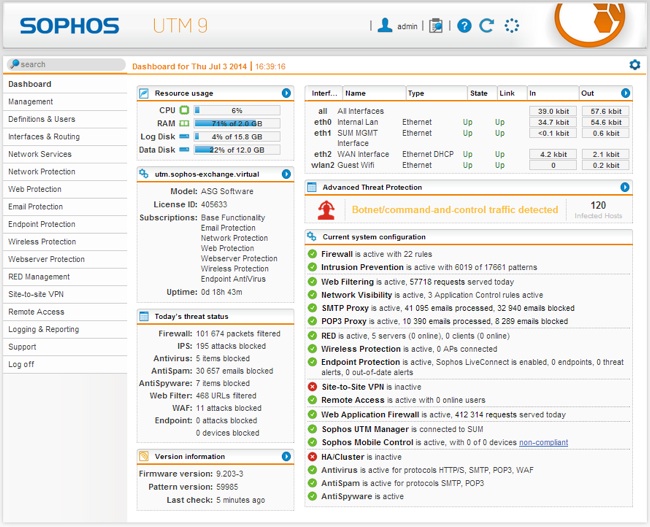
SC Media has given XG Firewall its top five-star rating across all areas including features, documentation, performance, support, ease of use, and value. They had tons of great things to say about it, including comments such as: “Very creative convergence of a lot of solid functionality.”
The reviewer, Peter Stephenson, examined the key protection areas XG Firewall provides, such as IPS, application security, web protection and advanced threat protection. He highlighted the unique Sophos Security Heartbeat that facilitates endpoint communication and information exchange as well as Sophos Sandstorm’s sandboxing of suspicious files and User Threat Quotient for identifying risky users.
The reviewer also commented that “editing rules is easy” and “policies are equally easy to work with”.
We weren’t surprised that SC Media cited XG Firewall’s reporting as being a strong suite for the product. We are the only vendor to include more than 1,000 reports at no extra charge as an integral part of the product.

SC Media also reviewed the documentation and support, noting that: “Documentation is presented in a novel way on the web portal … there is a large collection of very focused articles and lots of instructions and community discussions.”
But I think SC Media’s reviewer summed XG Firewall up accurately when he said: “This demands your attention no matter what size your organization.”

Learn more about XG Firewall at sophos.com/xgfirewall.
You can read the original article, here.
Phishing isn’t an unfamiliar term in these parts. In a previous blog post, we tackled the many ways hackers use phishing emails to trick users into downloading malicious attachments or visit malicious websites. In 2016 alone, phishing attacks have increased by a staggering 400%, and this year, the trend is likely to progress. So today, we’ll continue the campaign to end phishing by tackling another mode of attack in the form of phishing websites.
Sending malicious emails is only one part of the phishing process. The aspiring phisher usually also builds a fake website with the intention of tricking victims into entering login credentials, banking information or both, which the phisher then has access to. Phishing has victimized millions of users over the years. To prove how effective it is, consider this curious case from back in 2013. A trio of hackers were arrested in the UK for attempting to phish almost £60 million from unsuspecting customers by crafting over 2,600 fake banking websites.
To help you avoid falling victim to these attacks, we’ve compiled some of the most common scenarios in which you could encounter phishing sites and also some tips for how to spot them so you can avoid handing over your info.

How Do Phishing Websites Reach You?
Scenario 1: Opening a phishing email
Let’s start with a scenario that you’re already familiar with. Nick is a proud earner. He worked very hard over the years to earn $1 million dollars for his retirement. Just a few months before his retirement party, Nick was receiving emails from his “bank”, telling him to update his banking information. He logged in to the “bank’s website” and changed his credentials. The very next day, he found out his savings were wiped clean, just like what happened to a woman from the UK in 2012.
Scenario 2: Clicking a suspicious ad
Ads serve as another medium to carry out phishing attacks. Mary, for instance, was searching for easy-bake recipes online. She typed “easy cake recipes” on Google and without examining the link, she clicked on a Google Ad that reads “Easy Cake Recipes Today”. The ad led her to a webpage asking for credit card details in exchange for recipes. Luckily, Mary was suspicious of the payment request, so she promptly closed the webpage. She dodged a bullet there because these fake Google Ads were being used to carry out phishing attacks back in 2014.
Scenario 3: Accessing a fake login page
Phishers will stop at nothing to steal information. Take the case of Sophia who is looking to update her passport, as an example. Sophia types the name of the passport agency she’s looking for into her search engine and clicked the first link she saw. Everything looked good to her since the login page had nothing weird about it. She typed in her login credentials and her passport information. After submitting, she wondered why she didn’t receive any response from the agency. She found out the next day that her accounts have been compromised, similar to Singaporean citizens last year who fell for phishing attacks that spoofed government login pages.
Scenario 4: Engaging in social media
Ron had a problem with his bank, and thinking he could get a faster response via Twitter, he tweeted his concern to the bank’s Twitter handle. Within a few hours, a “bank representative” replied by providing him a link to the “bank’s support page”. Ron was smart enough not to trust the “representative” because he knows not to trust unverified Twitter accounts. Ron just encountered, and fortunately avoided, one of the most popular types of phishing attacks on social media.
Tips for Spotting a Phishing Website
In case you haven’t figured out the pattern, all the scenarios were based on real-life phishing attacks and scams. Nick, Mary, Sophia and Ron may be fictional, but the threats they faced are very real. Here are some helpful tips to avoid getting phished by these harmful websites. Let’s divide our solutions into two.
Before Clicking
Always check and study the URL before you click it. Whenever someone sends you a link via email or social media, or in any platform for that matter, take time to study the URL before you click. You don’t have to be an expert in spotting a suspicious URL. You should also make sure to hover over any hyperlinked text before clicking.

Identify the source of the link. Did you know the person who sent you the link? If you have even a drop of doubt, don’t click the link.
After Clicking
Check and study the URL BEFORE logging any information. Let’s say you accidentally clicked a phishing link. You shouldn’t panic just yet. As mentioned above, study the URL of the webpage and look for the obvious red flags.

Scan the page for a Trust Seal. Most legitimate sites takes advantage of trust seals, small badges issued by third party companies that show how safe a site is (e.g. by showing a trust score, sales sites, or whether the site is encrypted with SSL/TLS). Pages that collects login or payment information should have a trust badge or a Secure Site Seal in order to assure visitors that the website is legitimate.
Check the address bar for the organization’s details. SSL/TLS Certificates play an essential role in web security by encrypting sessions and protecting information sent between browsers and web servers. Extended Validation (EV) SSL, the highest level of SSL, adds another important element by presenting the website operator’s verified identity, usually in a dedicated green address bar.

Check the website address isn’t a homograph. Some major browsers do not understand foreign languages such as the Cyrillic alphabet. A hacker can register a domain such as xn--pple-43d.com, which is the equivalent of apple.com and purchase an SSL for it. This is also known as script spoofing.

There is one way you can catch this type of attack. If you feel the link is suspicious, copy and paste it into another tab
![]()
It’s as simple as that. The true nature of the domain is revealed right away and you know that the website cannot be trusted. You can also spot these homographs by clicking through the certificate details to see which domain is covered by the certificate.
In the example above, you’d see the certificate was actually issued to https://www.xn--80ak6aa92e.com/’ and not ‘apple.com’.
Phishing attacks may see a rise in the coming years, but as long as you’re educated in preventing them, these cheap methods of stealing will claim fewer and fewer victims in the future. Your best defense against hackers is your extensive knowledge of their dirty tricks.
You can read the original article, here.
Ransomware has been on the computer security radar for some time now but are you aware that it’s increasingly targeting servers?
Servers are the treasure trove of an organization’s data and the applications that access it. As senior vice president and general manager of Sophos’ Enduser and Network Security Groups Dan Schiappa explains, “Servers are considered the jackpot for cybercriminals, since they can store confidential corporate and employee information, medical records with social security numbers or private customer documents.”
We understand that servers differ from user endpoints, with higher performance and availability requirements. Therefore, we’ve enhanced our server capabilities with two technologies to assist Server Admins in meeting these needs:
CryptoGuard
Much like you’ve seen with Intercept X for endpoints, Sophos Server Protection now has signature-less detection capabilities in the form of CryptoGuard. This additional layer of defense detects and reverses unsolicited encryption of data on servers, so that cyber criminals don’t get the chance to hold organizations captive for extortion. Even if ransomware on a rogue endpoint connects to a server and attempts to encrypt files on a server, Sophos Central Server Protection Advanced protects the organization.

Sophos Security Heartbeat for Windows Servers
We have also broadened our Synchronized Security by adding Sophos Security Heartbeat capabilities to Sophos Central Server Protection Advanced, which includes:
- The Destination Heartbeat feature, introduced in XG Firewall, was designed with Servers in mind. Should a server become infected, the XG Firewall can isolate it and prevent other endpoints from accessing it.
- Positive identification of compromised servers: To alert an admin that a key asset may be compromised. Machines are explicitly labelled as servers in the Sophos XG Firewall Control Center, helping admins to prioritize their response efforts.
- The Missing Heartbeat capability is another valuable feature for server admins. Because servers should always send a heartbeat, a missing beat could indicate that it’s been compromised.

You can read the original article, here.
We know that a firewall is the first line of defense against external threats. It can block hackers, isolate potentially harmful information and stop targeted malware attacks from getting into your network and affecting your users.
But, what are the defining characteristics of a great firewall? We think it comes down to four critical areas: Security, Insight, Simplicity and Performance.
That’s why you’ll find all of these and more in the Sophos XG Firewall. Sophos XG it’s easier to use, with new navigation, enhanced logging and troubleshooting tools, and streamlined workflows.
It’s more powerful, with new policy tools that make it easy to build sophisticated web, email, and routing policies custom tailored to your needs.
It’s got more innovative, with new Synchronized Security features like dynamic app identification and new Security Heartbeat options that improve protection, response, and visibility into what’s happening on your network. See for yourself what makes our firewall great.

Looking for a new firewall?
As firewalls become more complex deciding which one to buy can be a daunting task. We’ve created a Firewall Buyers Guide to make finding the right firewall easy. It will help you establish your firewall needs, shortlist suitable vendors and provide you with key questions to ask your vendor.
You can read the original article, here.
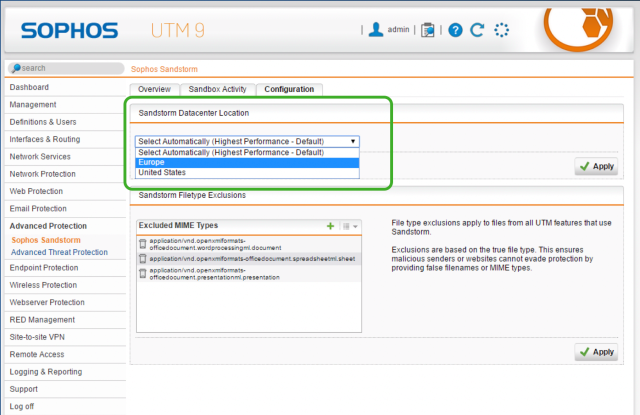
UTM 9.5, including many new features you’ve asked us for, is just around the corner – and we’d like to invite you to join the beta test of the release.
This version builds on our industry-leading protection and performance, with several new features for Web Application Firewall, Sophos Sandstorm sandboxing and to make management and reporting even easier, faster and more flexible.
Here’s a brief overview of what’s new:
Web Application Firewall Enhancements
- WAF URL Redirection gives you the ability to redirect traffic for a WAF protected URL to a different backend system or URL.
- Configure minimum allowed TLS version to improve security.
- WAF protection and authentication policy templates were added for common Microsoft services for protection and authentication.
- True File Type Scanning to be able to block uploads and downloads based on MIME type.
- WAF Proxy Protocol Support to use the client IP info inside the ProxyProtocol header to make policy decisions and improve logging.

Sophos Sandstorm Enhancements
- Datacenter location selection option for Sophos Sandstorm without relying on DNS-based location detection.
- Scan exceptions for Sophos Sandstorm to exclude specific filetypes from being sent to Sophos Sandstorm analysis.
- Sandstorm activity reporting expanded to include email attachments for improved visibility
Management and Reporting Enhancements
- 64-bit PostgreSQL Database to generate reports with big datasets faster.
- Download all UTM logs in a single archive.
- Certificate Expiration Notification 30 days before expiration date via WebAdmin and e-Mail to be able to react early on certificate renewal.
- Support Access with SSH is extending the existing Support Access feature.
- SNMP Monitoring of full filesystem to integrate UTM filesystem monitoring in regular SNMP based monitoring solutions.
- RESTful API to configure Sophos UTM 9

Where to get the beta firmware and provide feedback
The full release notes along with the beta firmware files are in the UTM 9.5 Beta Forums on the Sophos Community Site, where you can also give us your feedback. As usual, we don’t recommend you run beta firmware in a production environment but we highly value and appreciate your contribution in testing the beta and helping make this release the best it can be.
We’re expecting to start rolling out the update to UTM 9.5 at the end of April, so don’t delay if you’d like to be part of the beta test – and we’d really value your input. Click here to join us in the beta test!
You can read the original article, here.
Insider activity—both malicious and simple error—accounts for a growing share of data breaches. Statistics are difficult to come by because requirements for reporting security incidents are not consistent across sectors. But some studies show they account for more than half of those breaches analyzed.
According to the Protenus Breach Barometer for February, a monthly analysis of reported breaches in the healthcare industry, 58 percent were related to insiders. This was divided about evenly between intentional wrongdoing and error. Outside hacking accounted for just 13 percent. The problem is not confined to any single industry. New York State Attorney General Eric T. Schneiderman reported in March that his office received a record number of data breach reports in 2016, nearly 1,300. Employee negligence and wrongdoing were blamed for 37 percent.
Because the insider doesn’t have to penetrate perimeter defenses, these breaches can be difficult to discover. According to the Protenus report, breaches reported in February were on average 478 days old at the time of discovery. In two instances, it was more than five years before breaches were discovered.
Dealing with the insider threat is difficult for any organization. But it is imperative, and you can guard against it with the right tools if know what to look for.
The Weakest Link
Organizations invest substantial resources in procuring, updating and securing the IT enterprise, but the human element is a wild card. “The weakest link for any organization is not its systems, but rather the human factor,” the latest Verizon Data Breach Digest concludes. The challenge of defending against the insider is compounded by the mistakes of well-meaning employees. “It is important to note that these incidents are not always the result of a malicious employee and often stem from carelessness and lack of awareness regarding sound IT protocol.”
Employees are on the network as legitimate users with legitimate credentials and user privileges, generally using the network in the ways that are intended. This can make it easy for a malicious insider to cover his or her tracks, and honest mistakes might not trigger alerts for the security staff.
Defending against this threat requires more than traditional perimeter defenses. Organizations need to be continually aware of who their privileged users are and what they can access, and the privileged accounts and credentials must be managed throughout their lifecycle. In one recently reported incident, a former systems administrator at a healthcare facility was charged with hacking the facility’s systems using administrative credentials that had not been revoked more than two years after he had resigned.
Self Defense
Defending against insider threats requires having visibility into your network and knowing what to look for.
From our experience in securing privileged accounts, we have identified behaviors and anomalies that help companies identify malicious or damaging behavior. In a recent blog we shared 10 commands that are frequently associated with risky behavior. As my colleague notes in the blog, “It’s always worth noting that no two situations are the same, so an action that may be harmless in one situation may create a major security issue in another.” But this list provides a starting point in monitoring your network for suspicious activity.
We also recently announced the latest release of the CyberArk Privileged Account Security Solution with advanced insider threat detection. A new data feed from CyberArk Privileged Session Manager to CyberArk Privileged Threat Analytics lets security teams receive customizable, prioritized alerts about possible high-risk privileged activity. You can watch suspicious sessions in progress and terminate malicious sessions, all from one platform.
You can read the original article, here.
In the UK we have recently seen lots of headlines about cyber security and incidents at various NHS organisations, which have had varying impacts on day to day operations. Some of this information has been accurate, but a great deal of it has not – often because it takes time for the full facts of an incident to become known. This is causing added pressure to organisations, beyond the ongoing scrutiny they are already under.
Whilst these incidents are generally unhelpful, they have at least raised awareness and highlighted the importance of cyber security right up to board level, which is a positive thing.
Board members could be forgiven for thinking that a substantial investment is needed in order to provide better protection against today’s cyber threats, particularly as the effects of a successful attack are immediate. In actual fact, NHS organisations should initially make sure that they are following the best practice advised by their security vendors. (I recently gave five tips for securing NHS organisations.)
Once best practice is in place, you can begin to build in additional layers of security to provide defence in depth via next-generation functionality and further enhance protection. These include anti-exploit and anti-ransomware protection, such as Sophos Intercept X at the endpoint and sandboxing such as Sophos Sandstorm at the gateway.
The problem is that whilst there’s a lot that can be done technically, NHS organisations often lack sufficient staff to carry out this work. In an investment bank, there will be large-scale security teams looking after the tools that keep confidential data secure, whereas NHS resources are spread across a variety of different tasks. This means that systems need to be simple to implement and manage, and they need to be able to work systematically to automate the tasks as much as possible, not just pumping information into a SIEM (security information and event management).
In addition, NHS organisations must start to look at security across all areas of the network – rather than staff just focusing on their own silos – as today’s prevalent threats seek to access the network through multiple entry points.
Sophos Central enables organisations to monitor security across the whole organisation and allows those responsible to manage our award-winning synchronized security solutions. Advanced attacks are more co-ordinated than ever before and synchronized security means that your defences must be too. Sophos’s Security Heartbeat ensures your endpoint protection and firewall are talking to each other. It’s a simple yet effective idea that means you get better protection against advanced threats and spend less time responding to incidents. What’s more, the process is automated.
Following best practice and adding extra layers to increase your defences means that your board will sleep easier at night and you will have greater visibility into the health of your estate.
If you’d like to learn more about security best practice or if you would like to learn how Sophos’s synchronized security platform could help your NHS organisation please contact us at healthcare@sophos.com.
You can read the original article, here.
It’s widely understood that cyber intruders and internal threat actors seek and exploit privileged accounts to help them achieve their goals. Security experts advise organizations to know what’s on their networks and know it better than any potential adversary.
But discovering and locking down all of the privileged accounts within your enterprise is easier said than done—especially when you consider there are typically 3-4x more privileged accounts than people in the average organization. These accounts “live” in hard-to-reach places within your network including applications, endpoints, servers, databases and the cloud.
Here are some challenges organizations encounter when working to simply understand—let alone protect—privileged accounts in their environments, for example:
On premises and some cloud environments:
- There are often multiple accounts associated with one person and all of them have admin privileges.
- Many passwords are set to never expire to mitigate the risk of an interruption or issue.
- Many privileged accounts are mistakenly thought to be unused, but in reality, are used to log into systems regularly. Worse, it’s hard to pinpoint who is currently using them.
- Service accounts with “recently created” passwords have actually been using the same passwords for years—sometimes even a decade.
- It’s often difficult to locate hard-coded or embedded credentials stored within applications.
Specifically in cloud environments:
- In AWS, Elastic Cloud Compute (EC2) instances can be accessed using both EC2 private keys and individual AWS accounts.
- AWS root account credentials can be shared among multiple users, putting these highly sensitive credentials at an increased risk of loss or theft.
- In the cloud environment, it can be challenging to manage roles-based and temporary access.
How can you determine where all of your privileged accounts are before your attackers do? Take the first step by scanning your network with our CyberArk Discovery & Audit™ (DNA) tool available at no charge. One scan will help you discover the privileged attack surface of your organization by identifying where privileged accounts exist on-premises and in the cloud, your current privileged account security risks, accounts with local administrator rights, and machines that are vulnerable to credential theft attacks (such as credential harvesting, Pass-the-Hash, Overpass-the-Hash and Golden Ticket). Last year, our CyberArk DNA tool scanned more than 21 million machines, helping organizations take the first step towards reducing privileged account risks.
Enterprises that fail to prioritize the security of their privileged accounts are at risk of becoming victims of a cyber attack—which can mean major damage to business, reputation and even the ability to operate. Take the first step toward securing your privileged account environment. Run the CyberArk DNA scan today.
You can read the original article, here.
For one more year, NSS has a strong presence at the 7th Infocom Security congress, along with Sophos, Cyberark and Sealpath. The conference will be held at the Divani Caravel on 29 and 30 of March and it is entitled “On the IT Roadmap – Expect the Unexpected”.
The dynamic presence of NSS, Sophos, Cyberark and Sealpath includes three speeches along with workshops. The speech of Bogdan Tobol of Cyberark (Regional Sales Executive, South-East Europe) will take place on March 29th and the speeches of Chester Wisniewski (Senior Security Advisor will take place) and Luis Angel del Valle (Chief Executive Officer and Co-founder ) of Sophos and SealPath respectively will take place Thursday, the following day. Furthermore, workshops with Sealpath and Sophos will be held on the same day (Thursday). Also, a “special event with Cyberark” wilbe held with partners of NSS.
While designing an IT roadmap for the development of digital technologies, necessary to support strategy and operations in every organization, small business or enterprise, the most important factor to mind these days, is data protection.
It’s also obvious that what absolutely identifies threats in the digital world, in a constantly changing environment, is the element of unpredictability. The dangers for IT infrastructures of businesses and organizations are usually unexpected. That’s why the number of victims of attacks launched by cybercriminals is constantly on the rise, and consequences are especially damaging.
So, a major challenge for security experts worldwide, is for one to detect risks in time, developing and implementing contemporary security strategies, new generation technologies and preventive check techniques. On the other hand, they have to keep businesses properly updated and prepared, in order to efficiently tackle unexpected threats, by training users to focus their attention on risks out there.
The 7th InfoCom Security Conference which takes place on 29 & 30 March 2017, titled “On the IT Roadmap – Expect the Unexpected”, aims to highlight this challenge and is once more expected with great interest. For years, it’s been a point of reference for developments on Business IT & Cyber Security. It’s also a top annual summit for IT professionals who specialize in IT security, among other things.
The three themed sessions for each day of the conference will cover the issue of digital security, combining a business approach for IT Security, along with a wider scientific and technological content on Cyber Security. About the structure of the three themed sessions, on each of the two days of the Conference, we’ll take a closer look at:
- Strategies, trends, consulting services and implementation of IT Security projects.
- Challenges and solutions for the protection of data, devices and infrastructures.
- Methodologies and research projects for Cyber Security, as well as Ethical Hacking techniques.
SCHEDULE DAY 1 – 29 MARCH
12:30 – 14:30 | 2nd Session: Advanced Protection Against Next-Gen Threats
The new generation of threats is definitely more dangerous these days. Attacks on networks of businesses and organizations are upgraded and targeted, aiming mostly at monetary gain as well as theft and sale of personal data. Preventing and repelling the new generation of attacks, as well as responding and restoring an infected system, require security solutions with advanced technology for networks and endpoints, with A.I. and effective protection, not only against threats of today, but of the future as well. Such solutions will be presented in the 2nd session of the conference.
Stop them before they stop your business
Bogdan Tobol – Regional Sales Executive – South-East Europe, CyberArk
SCHEDULE DAY 2 – 30 MARCH
12:30 – 14:30 | 2nd Session: Intelligent Security Made Simple
One of the most significant things businesses today demand from companies that provide security solutions and services, are for protection products installed on their IT ecosystems to offer security for one, and also be able to align as a whole with operational functions, supporting productivity and application flexibility. Smart solutions that offer effective protection from current and future threats, through a simple way and unified approach, that remove complexity and align with the demands of any organization, will be presented in this session of the conference.
When your toys attack – Securing the IoT is harder than it looks
Chester Wisniewski – Senior Security Advisor, Sophos
Data Protection Beyond the Perimeter
Luis Angel del Valle – Chief Executive Officer and Co-founder, SealPath
WORKSHOPS DAY 2 – 30 MARCH
10.00 – 11.00
Your documents, protected and under control. Wherever they travel – Luis Angel del Valle, Chief Executive Officer and Co-founder, Sealpath
13.30- 14.30
When your toys attack – Securing the IoT is harder than it looks – Chester Wisniewski – Senior Security Advisor, Sophos
LogPoint is proud to announce LogPoint 5.6!Since the last large upgrade back in April 2016 (5.5.0), we have had minor releases and in parallel worked on this release.
New Features
Policy Based Routing
The feature allows your organization to:
- Reduce costs of storage: Filter messages before they are stored.
- Optimize workflows: Store logs in repositories based on urgency and severity
- Take the outputs of alerts and store them with enhanced meta data for efficient long-term correlations.
How it works:
- During collection and after normalization, we define a filter
- Based on the contents of the logs, an action will be taken:
- Drop the log?
- Keep only key-value pairs?
- Keep everything
- Where to store the logs
We walk through the configuration in the video below, so check out how to set this up in a few simple clicks.
Enhancements
LogPoint 5.6.0 contains numerous important enhancements. However, the exhaustive list of enhancements can be found in the release notes, we would like to highlight some of them here.
Syslog Collector has been enhanced to provide sequence numbers on messages received. The sequence number is assigned per device per protocol to each log message. With this feature, you can sort log messages by the order at which they arrive.
Read the original article, here.
The Internet of Things (IoT) continues to be a boon to hackers and a bane to IT security professionals. IoT security is usually an oxymoron because the vast majority of IoT devices have poor security architecture. The manufacturers are often in a rush to get products to market, therefore security is an afterthought. And, once the device falls into the hands of a consumer, it’s unlikely that the device manufacturer will send out security patch updates, and even less likely that the end-user will take the time to install such security patches.
According to a PCWorld article, hundreds of thousands of IoT devices are infected with the Mirai botnet code, and hackers are manipulating strains of the Mirai code so they can infect hundreds of thousands more devices. Furthermore, malware infections happen within minutes of a device going online, according to Rob Graham, CEO of Errata Security. The potential for infecting millions of devices is very real, given that 8.4 billion devices will be connected to the Internet by the end of 2017, according to Gartner.
Why Should We Care?
That sea of IoT devices is the source for current and future multi-terabit distributed denial of service (DDoS) attacks. No one should forget that the now-infamous 1.2Tbps DDoS attack on domain name service provider Dyn in October 2016 was fueled by IoT devices infected with the Mirai botnet. It made life difficult for Dyn; it not only cost Dyn a lot of time and money, it tarnished the company’s reputation and caused great inconvenience for Dyn customers and their customers. Terabit-sized DDoS attacks like that will become common in the near future, and no enterprise is immune to the threat.
What Should Be Done?
There is no silver bullet for DDoS protection. However, Step 1 in the war on DDoS is to stem the rising tide of infected IoT devices. Manufacturers should build better security into the devices, and consumers should update the password on each device from the manufacturer’s default setting. Those are important steps in the right direction, but how likely will those steps be taken, universally? Not likely at all. Before the world can make any substantial progress down that road, hackers will have launched many more crippling DDoS attacks that companies (and consumers) can ill-afford.
Step 2 in the war on DDoS is to improve your defenses. No one can control the security of IoT devices that they don’t own, but you can control your own destiny by implementing real-time, automated DDoS protection. So check with your Internet service provider to find out if it offers DDoS protection as a service (DDPaaS); the investment is more affordable than ever.
Read the original article, here.
When Sophos Phish Threat was released in January, we pointed out that:
- Email remains one of the most problematic sources of infection; and
- It’s the ordinary, well-meaning people who often let poisonous emails into their organizations.
Phishing is an old problem, but news stories continue to show that people remain easy prey.
New attacks, old tactics
A recent Naked Security article outlined the bad guys’ efforts to infect their prey using scams centered around tax season, with the Internal Revenue Service (IRS) warning of fresh email schemes targeting tax professionals, payroll staff, human resources personnel, schools and average taxpayers. In another scam, attackers polluted Amazon listings with links that redirected victims to a very convincing Amazon-looking payment site.
Now come fresh reports that attackers are using malicious PDF attachments and messages that appear to be from their company’s HR departments, as well as bogus Facebook friend requests. [For the full story, read Latest phishing tactics: infected PDFs, bogus friend requests, fake HR emails.]
Microsoft Malware Protection Center team member Alden Pornasdoro warned of the malicious PDF files. Unlike in other spam campaigns, he wrote, the PDF attachments in question don’t contain malware or exploit code. Instead, they rely on social engineering to lead people to phishing pages where they are asked to divulge sensitive information.
In another case, ZDNet reported that sending a bogus friend request was the best way to get someone to click on a link – even when the email was being sent to a work email address.
In one simulation conducted by MWR Infosecurity, a quarter of users who were tested clicked the link to be taken through to a fake login screen, with more than half going on to provide a username and password. Four out of five then downloaded the sinister file. Meanwhile, a spoof email claiming to be from the HR department referring to an appraisal system also proved effective.
Successful attacks through social engineering
Recent developments show that the ancient technique of social engineering is alive and well. Understanding it is the first step in mounting a better defense. We previously wrote:
Social engineering is the act of manipulating people into taking a specific action for an attacker’s benefit. You might think it sounds like the work of a con artist – and you’d be right. Since social engineering preys on the weaknesses inherent in all of us, it can be quite effective. And without proper training it’s tricky to prevent. If you’ve ever received a phishy email, you’ve seen social engineering at work. The social engineering aspect of a phishing attack is the crucial first step – getting the victim to open a dodgy attachment or visit a malicious website.
As the blog post noted, phishing can’t work unless the first step – the social engineering – convinces you to take an action.
To help raise awareness, security vendors have offered a number of products and services companies can use to launch simulations – essentially phishing fire drills — which can show employees up close how easy it is to be duped by social engineering.
For Sophos customers, that product is Phish Threat.
How it works
With Phish Threat, users choose a campaign type, select one or more training modules, pick a simulated phishing message, and decide which users to test. Reporting tells you how many messages have been sent out, who’s clicked, and, of those, who’s gone through the required modules.
Security awareness programs are not new, and some security experts have questioned their effectiveness, since users continue to make the same mistakes.
In our opinion, simulations give awareness programs more teeth. The more employees get caught on the phishing hook during a simulation, the less likely they are to forget the lesson.
That may sound like a self-serving statement. But the proof is in the never-ending avalanche of news headlines.
Read the original article, here.
It’s no secret these days that cyber threats are rampant and varied. Ransomware, malware and distributed denial of service (DDoS) attacks are not frequently mentioned in the mainstream press, but they are everyday news in technology and finance trade publications.
Cyberattacks are an everyday occurrence for some companies, a rare occurrence for others. Some companies are keenly aware of attacks on their networks, but other companies are not. Even in some companies that have dedicated IT security staff and systems in place, major security breaches have occurred. It can take months or even years for an organization to realize that it has been breached.
Yes, a DDoS Attack Could Happen to You
Some professionals may be in a state of denial, psychologically; i.e., they believe that “no one would try to hack our site because we’re not high-profile, or we have nothing that a hacker would want.” To make such an assumption is definitely a big mistake, and could cost your company a lot of time and money. The vast majority of organization networks include data that is valuable to someone, somewhere. Besides credit card numbers and email addresses, sensitive data may include medical records or social security numbers.
Hackers’ Money Motivation: DDoS Extortion & Ransomware
The market price for stolen sensitive data has been decreasing, but data is still priceless to its owners, so hackers are increasingly committing cyber extortion to extract money from victims. The message they convey is basically, “Pay the ransom or I’ll steal and expose your sensitive data.” Alternatively, hackers sometimes threaten to launch a DDoS attack unless a ransom is paid. Or, they actually launch a DDoS attack and promise to stop the attack if the ransom is paid. (Would you trust the promise of a cybercriminal?)
What does Extortion Have to do with DDoS attacks?
A DDoS attack is not a security breach. But recently there are reports of multi-layered cyber-attacks that combine ransomware and DDoS attacks. The hacker method is to use DDoS to take down the first layer of defense, such as a firewall or intrusion prevention system (IPS), and then map the floor plan of their target’s environment, and determine any weak points and vulnerabilities that can later be exploited through other methods, such as ransomware. How do they do that without getting noticed, you may ask? Via small, sub-saturating attacks that cause temporary, minor network outages to mask a more nefarious malware infiltration or data theft.
DDoS Attacks Big or Small
It’s interesting that DDoS attacks are getting larger in volume; we have entered a new era, with terabit-sized DDoS attacks like the one on Dyn and Krebs Security are becoming common. Yet the smaller, hard-to-detect DDoS attacks are much more common and can be just as—if not more—damaging. The fact is, enterprises nowadays must worry about all types and sizes of DDoS attacks. Companies have to assume that they will most likely experience a DDoS attack (if they haven’t already!)
What Should Enterprises Do?
Defense is essential but, admittedly, not every enterprise can afford DDoS mitigation solutions. Fortunately, more and more service and hosting providers are rolling out DDoS protection as a service (DDPaaS), which makes DDoS protection more affordable for organizations of all sizes. So, ask your Internet service provider whether they offer DDoS protection as a service; thanks to Corero’s DDPaaS enabling technology.
To learn more about how DDoS attacks and protection are evolving, download the Evolution of DDoS Report.
Read the original article, here.
Doctors sometimes make mistakes that harm the patient. Police often fail to protect and serve. When that happens, people rightly demand the failures be analyzed and fixed. But no one ever calls for the elimination of all doctors and police.
Why then, do some call for the end of antivirus and anti-malware when failures happen? It’s a question that has vexed us for a long time.
Researchers uncover vulnerabilities in security products on a regular basis. A recent example is Trend Micro, which faced scrutiny in January after researchers reported some 223 vulnerabilities across 11 of the vendor’s products. Tavis Ormandy, a prolific and gifted Google Project Zero researcher who most recently discovered Cloudbleed, regularly targets security products, including those produced by Sophos and such vendors as Kaspersky and Symantec.
Along the way, someone either declares it the end of antivirus, anti-malware and endpoint protection, or calls for its demise. Last year, during another disclosure of Trend Micro vulnerabilities, security experts even declared antivirus a threat to security.
Can we all do better? Absolutely. Like all technology created since the dawn of time, antivirus sometimes falls short of its mission. As an industry, we need to continue to find weaknesses and fix them as quickly as possible.
Does doing better mean we set aside antivirus and anti-malware, just as some believe vaccines should be shelved? Hardly.
To help frame the issue, I sat down with Sophos CTO Joe Levy.
Iatrogenesis happens, followed by schadenfreude
“In responding to the occasional question about the claims of harm from endpoint security products, it occurred to me how strikingly similar such a belief system is to the anti-vaxxer movement. Both mean well, but unfortunately have the potential to do more harm than those they indict. Nonetheless, those who point out problems with antivirus make valid points,” Levy said. “All software has flaws.”
Levy offers two other observations:
1. This is a case of yelling ‘iatrogenesis’ (harm caused by the healer) in a crowded theater. It is particularly sensational because of the irony, and in many cases, a source of schadenfreude (pleasure derived from the misfortune of others).
2. The attack surface of security software is often enlarged by the level of privilege needed to operate efficiently (i.e. in the kernel) and to do the kind of work that it needs to (file/network interception, process termination, system cleanup, etc.)
Just as patients sometimes develop complications after surgery, security technology sometimes fails, creating unintended harm for the user, Levy said. When that happens, detractors love to swoop in and bludgeon the offender.
Levy noted that when medical care goes wrong, we don’t see the masses calling for the end of doctors and hospitals. Sometimes police make mistakes and do harm in the line of duty. When that happens there’s public outrage, but no one calls for the end of police.
Like modern medicine and law enforcement, the security industry has a very high obligation to protect their users from harm. That means not only demonstrating effectiveness against attacks targeting operating systems and applications, but also against attacks targeting themselves. Despite this awareness, prevalent security software, like all other software with a large enough install base, is still sometimes found to be far from ironclad.
But just as we still need hospitals and police officers, we still need those security tools, Levy said. While Microsoft continues to make great strides in the security of their operating systems and applications year over year, a look at the number of Microsoft vulnerabilities per year illustrates the continuing need for additional protections. Microsoft security holes between 2009 and 2016, as catalogued on the Common Vulnerabilities and Exposures (CVE) website, are as follows:
2009: 74
2010: 106
2011: 103
2012: 83
2013: 106
2014: 85
2015: 135
2016: 155
In five of the last eight years, Microsoft released more than 100 security bulletins in a 12-month period. The number of bulletins each year haven’t fallen below 75 since 2009. Antivirus remains the first line of defense when attackers work to exploit vulnerabilities in either software or the software’s human operators.
“We take our obligation to protect very seriously, and we make continuous investments in the tools and programs to improve the security of our products, from our SDLC (secure development lifecycle), to static/dynamic/runtime security tools, to our bug bounty program, to name a few,” Levy said. “We are genuinely grateful to those security researchers who practice responsible disclosure. All of us in the security industry, whether software vendors or researchers, seek to make information systems more secure.”
He added: “We should all take a sort of Hippocratic Oath to do no harm, and that means both holding ourselves to a higher standard for building secure software, as well as putting end users before glory or sensationalism. Failure at either is a form of negligence, but calls for extermination are silly and irresponsible. The focus should not be on kicking the other when they’re down, but on making each other better.”
Read the original article, here.
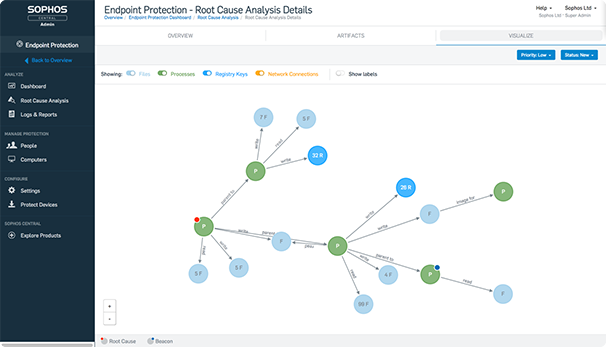
The protection capabilities of Intercept X are now available to Endpoint Protection deployments managing their endpoint policy in Sophos Enterprise Console. Stop malware, prevent exploit vulnerabilities and get a deep clean on any potentially hidden malware using the Endpoint Exploit Prevention add-on.
Highlights
- Stops crypto-ransomware and automatically rolls any impacted files back
- Exploit Prevention mitigates the methods attackers use to exploit software vulnerabilities
- Forensic-level system cleanup
Stop ransomware before it takes hold
The proven CryptoGuard capabilities in Sophos Intercept X are now being used in Endpoint Exploit Prevention. The technology blocks ransomware as soon as it attempts to encrypt your files, returning your data to its original state.
- Brings the protection technology of Intercept X to Enterprise console-managed endpoints
- Protects endpoints from ransomware attacks
- Automatically rolls back encrypted file changes
- Stops both local disk and remote file-share encryption
Exploit technique mitigations
Our anti-exploit technology stops threats before they become an issue by recognizing and blocking common malware delivery techniques. This process protects your endpoints from exploit kits and malicious payloads looking to exploit both known and unknown software vulnerabilities.
Advanced threat removal
Removing malware is no longer just a case of quarantine and delete. If malware is detected on an endpoint, how do you know what the malware did to your machine before it was stopped? Sophos Clean technology is used within Endpoint Exploit Prevention to detect the remains of malware and perform a deep system clean. The technology records forensic-level audit logging, tracking every change and cleaning the hidden malware.
Managed by Sophos Enterprise Console
Endpoint Exploit Prevention requires no new agent deployment for existing Sophos Endpoint Protection customers who are using Enterprise Console. The addition of the license unlocks new policy capabilities and automatically deploys agent components. Looking for Root Cause Analysis attack visualizations, in addition to protection? Switch to Intercept X and manage your endpoints from Sophos Central, our cloud-based platform.
The field of cyber forensics is getting much more attention lately, mostly because of the keen debate over Russia’s hacking of U.S. political party networks. The public, media and politicians all demand “evidence” of the hacking. Fortunately, sophisticated cyber-security forensics tools are available to assist with this. We cannot pretend to know what evidence the U.S. intelligence agencies have uncovered, but at least we know that they do have the technology and the cyber security experts to get at least close to the truth (even if they won’t or can’t share it publicly).
However, when it comes to Distributed Denial of Service (DDoS) attacks, based on political or other motives, forensic evidence is typically much harder to come by. Tracing the origins of such attacks is difficult because the source is either a legitimate third-party server, running a service which has been leveraged by an attacker as part of a reflection/amplification attack, or is a direct flood attack from a single device, or a botnet of many devices in which the IP source addresses are easily spoofed to ones which cannot be associated with the attacker.
For this reason, it is critical to have a DDoS protection solution that not only blocks all types of DDoS attacks, but also identifies the type of attack vectors, analyzes the digital fingerprint, and gathers intelligence to prepare against emerging threats.
The Corero SecureWatch Analytics portal, part of the SmartWall Threat Defense System, does exactly that, by capturing and indexing data on all the traffic the system sees when under attack, and during peacetime, to enable detailed analysis of any security incidents. It continuously records traffic for subsequent analysis of network flows and trends, providing detailed visibility into detected threats and patterns over time.
As sophisticated threats continue to evolve, effective security analysis requires continuous visibility into the traffic flowing between the protected network and the Internet. Analysis of past events is valuable to help prepare for future threats. You don’t need merely attack mitigation, you need visibility into attacks.
You can read the original article, here.
A recent TripWire study highlights the growing problem of cyberattacks, and whether IT staff feel that their companies have the right combination of skills and technology to cope with various types of cyber threats. Top concerns were (in order of importance) ransomware, distributed denial of service (DDoS) attacks, malicious insiders, phishing and vulnerability exploits.
According to the study, 60% of IT professionals surveyed felt that they have the right skills to defend against distributed denial of service (DDoS) attacks, and 63% felt they have the right technology to handle such attacks. That’s a slim majority of the sample; given the increasing prevalence of DDoS attacks, it’s not very reassuring to think that 40% of IT security professionals feel ill-equipped to handle a DDoS attack. One wonders how their customers would feel if they knew that.
Granted, some companies are more vulnerable to DDoS attacks than others. Internet Service Providers and Hosting Providers typically experience DDoS attacks on a daily basis, partly because they have such large surface areas for attacks, and partly because an attack on them can affect multiple downstream customers (sort of like “killing two birds with one stone.”) However, regardless of one’s profile or attack surface, every network is vulnerable to a DDoS attack. Hackers have many motives, but essentially their goal is to either steal your sensitive data or crash your website.
DDoS attacks come in all sizes, great and small. Most companies fear the large, volumetric attacks that can crash a website or network. However, such attacks are relatively uncommon. More common are the short, sub-saturating attacks that can mask a security breach. Because most companies possess some form of sensitive data—whether it is customer credit card information, email addresses, social security numbers, or intellectual property—most companies should be concerned about DDoS attacks because they can open the door to security breaches.
Companies face a myriad of cyber threats, but DDoS attacks are both a web availability threat and a security threat. If 40% of companies lack the skills or technology to handle a DDoS attack, that’s cause for concern, for both the companies and their customers. (A Corero survey indicates that loss of customer trust and brand reputation are consequences of DDoS attacks.)
You can read the original article, here.
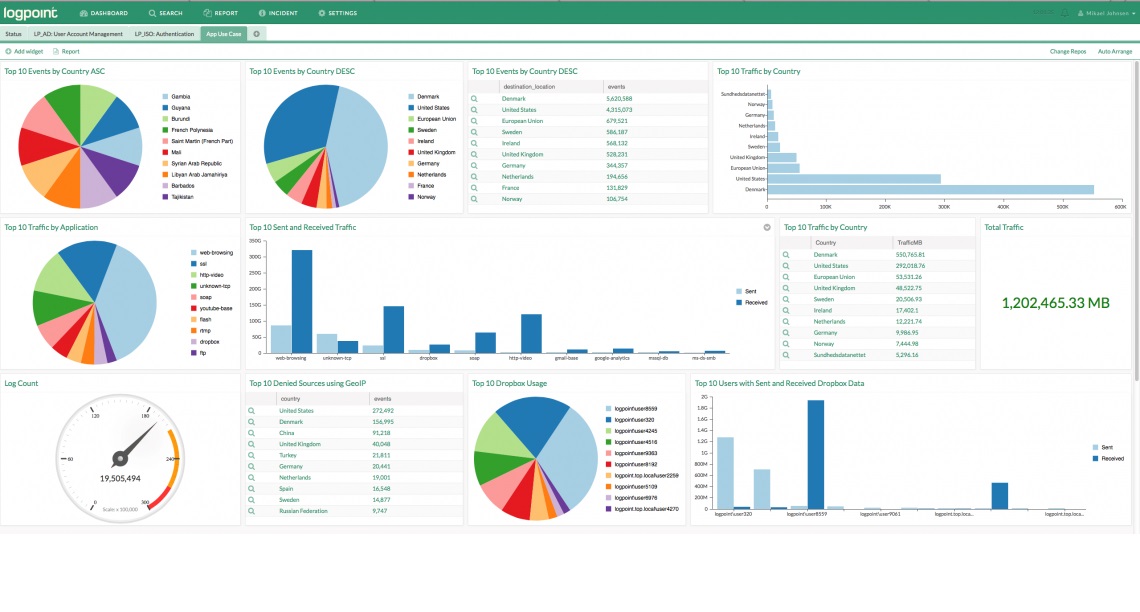
Ransomware is doubtless a rising threat nowadays, putting all small, medium-sized and large businesses at risk. Our IT and security professionals at LogPoint are constantly working to help our clients withstand such attacks. When fighting ransomware, planning and forethought are crucial so you can limit the impact and quickly recover with minimal disruption. Keep in mind that ransomware variants are constantly changing, and it’s hard to thwart every attack without the help of a real power tool. After all it’s better to be safe than sorry.
The queries and examples used, assumes the environment relies on an EMC backend but works for every kind of storage solution.
Objective
Acquisition of unusual data activity on storage systems within a certain period of time often indicates ransomware activities. With the help of ransomware detection, the organization receives an alarm via email each time suspicious activity is detected. There is a wide variety of suspicious activities, however, the cases when data is deleted, created, or modified in high volumes should always be a warning sign.
Dashboards
The dashboard represents the top 30 users, that showed the highest activity during the past 10 minutes:
Query: label=EMC userSid=*|rename userSid as objectSid| chart count() by objectSid order by count() DESC limit 30| process lookup (LDAP,objectSid)|fields displayName, sAMAccountName, objectSid, count()

Paths, that generate high volumes of data activity by nature (e.g.: Citrix or Xen) are excluded from the search so they cannot distort the results.
Additionally, there is a list called Whitelist which consists of reliable users. The list is auto-generated based on UserSID. Furthermore, there is an in-house scale containing “normal” data activity so the system can capture any activity deviating from that.

Users are assigned to userSIDs by matching with Active Directory. The results are stored in a table from where, data can be permanently used for further analysis.

Alarming
Query: label=EMC -“bytesWritten”=”0” -“bytesWritten”=”0x0″ event=”0x80” flag=0x2 userSid=*| chart count() as handle by userSid, clientIP | search handle>200
The alarm is triggered and an e-mail is sent to the person in charge, whenever a suspicious data activity, effecting more than 200 files (in-house baseline) is detected. Paths and applications which are labelled as trustworthy are excluded from this rule.
While this is just scratching the surface of how we can fight ransomware at LogPoint, this use case can serve as a great starting point for further discussions about the next steps to take in order to protect your organization.
You can read the original article, here.
SophosLabs has released a malware forecast to coincide with the start of RSA Conference 2017. Typically, our research papers focus on Windows, which has traditionally been the largest battleground. While some of the report does indeed look at Microsoft-specific challenges, we decided to focus more on the increasing malware threats directed at platforms where the risks are often not as well understood, specifically Linux, MacOS and Android devices.
SophosLabs has identified four trends that gained steam in 2016 and will likely remain challenges in 2017:
1. Linux malware that exploits vulnerabilities in Internet of Things (IoT) devices
The report starts by looking at how Linux is increasingly being used to target and infect IoT devices that include everything from webcams to household appliances that connect to the internet. Default passwords, out-of-date versions of Linux and a lack of encryption will continue to make these devices ripe for abuse.
2. The pervasiveness of Android malware
Next, the report looks at the top 10 malware families targeting Android devices, the most pervasive being Andr/PornClk: more than 20% of the cases SophosLabs analyzed in 2016 were from this family. It makes money through advertisements and membership registrations, and it is persistent – taking advantage of root privilege and requesting “Device Android administrators”. It downloads Android Application Packages (APKs), drops shortcuts on home screens and collects such information as the device ID, phone number and other sensitive details.
The report also looks at ransomware SophosLabs identified as Andr/Ransom-I, which pretends to be an update for the operating system and such applications as Adobe Flash and Adult Player. When downloaded, it is used to hijack the victim’s phone. While this malware is not nearly as widespread as the others, accounting for only 1% of all samples and didn’t even make our top 10 list, it is still noteworthy because it targets devices running Android 4.3, which is still used by 10% of Android owners – roughly 140m users worldwide.
3. MacOS malware that spreads potentially unwanted applications (PUA)
The report then goes on to look at MacOS malware that is designed to drop password-stealing code, including ransomware such as OSX/KeRanger-A and a variety of badly behaved adware. Though it continues to see fewer malware and ransomware infections than Windows, MacOS saw its fair share in 2016, and we expect that trend to continue.
4. Microsoft Word Intruder malware that is now expanding its targets beyond Office
Finally, the report looks at Windows-based malware kits that have historically targeted Word but are now expanding their horizons to abuse Flash.
The full report, in PDF form, can be downloaded from here.
You can read the original article, here.
Sophos, a global leader in network and endpoint security, today announced it has entered into an agreement to acquire Invincea, a visionary provider of next-generation malware protection. Invincea’s endpoint security portfolio is designed to detect and prevent unknown malware and sophisticated attacks via its patented deep learning neural-network algorithms. It has been consistently ranked as among the best performing machine learning, signature-less next-generation endpoint technologies in third-party testing and rated highly both for high detection and low false-positive rates.
Headquartered in Fairfax, Va., Invincea was founded by chief executive officer Anup Ghosh to address the rapidly growing zero-day security threat from nation states, cyber criminals and rogue actors. Invincea’s flagship product X by Invincea uses deep learning neural networks and behavioral monitoring to detect previously unseen malware and stops attacks before damage occurs. With a focus on the U.S. government, healthcare and financial services sectors, Invincea has been deployed in some of the most targeted networks in the world.
“By adding Invincea to our portfolio, Sophos is executing on its vision to assemble the most powerful technologies to provide the very best, cutting-edge defenses for our customers,” commented Kris Hagerman, chief executive officer at Sophos. “Invincea is leading the market in machine learning-based threat detection with the combination of superior detection rates and minimal false positives. Invincea will strengthen Sophos’ leading next-gen endpoint protection with complementary predictive defenses that we believe will become increasingly important to the future of endpoint protection and allow us to take full advantage of this significant new growth opportunity. We are proud to welcome the Invincea team to Sophos and look forward to introducing the benefits of this advanced technology to our customers and partners worldwide.”
Sophos is recognized as a leader in endpoint protection today with an expanding set of next-generation technologies such as the signature-less anti-malware, anti-exploit and anti-ransomware technology in Intercept X and the behavior-based analytics, Malicious Traffic Detection and Application Reputation in Sophos Endpoint Protection. The Invincea machine learning malware detection and prevention technology will be fully integrated into the Sophos endpoint protection portfolio, further strengthening Sophos’ leadership in this fast-growing market. The availability of Invincea technology through the Sophos Central security management platform will further enhance the Sophos synchronized security portfolio and real-time intelligence sharing.
“We started Invincea with the vision of using non-signature based technologies, including machine learning, in innovative ways to protect organizations against the most advanced forms of cyber-attack,” commented Anup Ghosh, founder and chief executive officer at Invincea. “X by Invincea represents a new generation in antivirus technology based on deep learning and behavioral monitoring. Joining forces with Sophos presents the perfect opportunity to take our proven, advanced technology to a global audience and make it part of a comprehensive synchronized security system. Sophos is leading the industry in adopting and bringing to market this disruptive new vision for complete, advanced, and integrated security, and we are delighted to join the team and help make it happen.”
Norm Laudermilch, chief operating officer and head of product development at Invincea added, “Invincea set out to disrupt the traditional approach to antivirus, and even now no single technology is enough to fully protect customers. I share the Sophos vision for bringing together a powerful ensemble of next-gen technologies to dramatically improve the overall effectiveness of endpoint protection. Along with our world-class technical team at Invincea, I’m looking forward to joining Sophos and helping deliver on this ambitious and exciting vision.”
The Invincea endpoint security portfolio including X by Invincea will continue to be supported and sold by Invincea and available via Invincea’s network of registered partners. Sophos has agreed to acquire Invincea from its current shareholders for a cash consideration of $100 million with a $20 million earn-out. Sophos will retain the company’s office in Fairfax. Invincea CEO Anup Ghosh and COO Norm Laudermilch will join Sophos in key leadership positions.
You can read the original article, here.