News
For almost 20 years, stolen credentials have been the most common route for attackers into organizations, according to the Verizon Data Breach Investigations Report (DBIR). But that’s no longer the case.
According to the newly published 2026 report, exploitation of vulnerabilities has overtaken credential theft as the leading vector for hackers to gain their initial access — accounting for 31% of all security breaches.
And what’s the likely reason? AI is helping attackers find and weaponize known flaws far faster than defenders can patch them.
The uncomfortable truth is that the window between a vulnerability being disclosed and it being actively exploited has shrunk from months to hours.
Verizon’s report further claims that only around a quarter of disclosed vulnerabilities ever get fully patched, and on average it takes 43 days to fix half of them — a timeline that is slipping, not improving.
Anyone hoping that simply patching their systems faster is a workable strategy is going to be sorely disappointed. The sheer volume of problems is making that impossible.
But this is far from the only headline from this year’s Verizon DBIR.
Phishing Targeting Mobile Devices
Clued-up workers are becoming increasingly wise to the risk of malicious emails arriving in their inboxes, and so attackers have switched channels.
Increasingly, social engineering attacks like fraudulent SMS messages and voice calls are launching successful attacks at a rate 40% higher than traditional email phishing.
Employees are far less likely to scrutinize a sender’s number on a small screen than they are to double-check the veracity of an email on their desktop. Cyber-criminals know that users are often most distracted when on their mobile phones, and are exploiting the weakness with success.
Shadow AI Is the New Shadow IT
For years companies have known that unsanctioned web applications and software-as-a-service tools were a security headache, but Verizon has found that frequent use of AI tools by employees has surged from 15% to 45% in a single year.
75% of those using AI in the workplace are doing so by accessing unsanctioned services, mostly through personal accounts.
This use of “Shadow AI” is now the third most common source of non-malicious data leakage, according to the report. And the risks are real. Because every time an employee pastes a contract, a customer list, or source code into a chatbot accessed via their personal account, the data effectively leaves the organization.
The Supply Chain Keeps Getting Longer
Breaches involving a third party are up 60% compared to the previous year, and now make up 48% of all breaches.
Organizations are increasingly relying on external vendors, contractors, and service providers. Cyber-criminals are wise to the fact that the weakest link which will provide access to a company’s systems or data might be a different vendor entirely.
Ransomware Is Proving Less Profitable
It’s not all bad news. Although ransomware is now involved in approximately 48% of confirmed data breaches, fewer of its victims are paying their extortionists. The proportion of organizations refusing to pay has risen from 65% to 69% according to the report, and the average ransom payment continues to fall.
Conclusion
What is clear from the advice contained within the DBIR is that you can do a lot to defend your company simply by getting the fundamentals right.
Reduce your attack surface, understand what parts of your business are at risk and reduce your exposure, don’t bolt AI into your systems but instead integrate it carefully and securely, take vulnerability management seriously and keep yourself briefed on the latest threats.
Source: Fortra
Sophos has been named a Leader in the 2026 Gartner® Magic Quadrant™ for Endpoint Protection. This marks the 17th consecutive report in which Sophos has been recognized as a Leader in this category.
We believe this continued recognition reflects both the durability of Sophos’ endpoint protection strategy and the progress we have made in helping organizations defend against a rapidly changing threat landscape, including the rise of AI-powered attacks.
For security teams, endpoint protection is no longer simply about stopping attacks on a device. It is about detecting, understanding, and responding to threats that move across users, identities, endpoints, networks, cloud environments, email, and browsers.
Click here to read the report.
From endpoint tools to coordinated cyber defense
In our view, 17 consecutive recognitions as a Leader represent more than consistency. We believe it demonstrates Sophos’ continued ability to evolve and innovate in line with the broader market shift away from standalone endpoint products and toward integrated security systems that can defend across the full attack surface.
Today’s defenders need security controls that work together, share context, and act with speed. That is why Sophos continues to invest in a cyber defense system that connects protection, detection, investigation, and response across the environments where attacks unfold.
We feel this recognition is consistent with our continued focus on:
- Coordinated protection across endpoint, identity, network, email, cloud, and browser
- AI-assisted detection and response workflows that help analysts move faster, and with confidence
- A cyber defense system designed to scale from mid-market organizations to enterprise environments
Defending in the AI-on-AI era
Cybersecurity has entered an AI-on-AI era. Attackers are using automation and AI to accelerate reconnaissance, generate convincing social engineering, adapt malware, and move through environments faster than traditional defenses can often respond.
That speed changes what organizations need from endpoint security.
The endpoint remains one of the most important control points in the enterprise, but attacks rarely begin and end there. Modern adversaries move across identities, devices, networks, cloud workloads, inboxes, and browsers. They exploit gaps between tools, disconnected telemetry, and slow handoffs between teams.
Defenders need a defense system, not a collection of fragmented products. When every layer of defense shares intelligence and strengthens the others, organizations are better equipped to detect coordinated activity, focus on the right signals, and respond before an incident becomes a breach.
This is the model behind the Sophos AI-Native Cybersecurity Defense System: integrated technologies, services, and threat intelligence working together to detect, correlate, and respond to threats in real time.
Recognition across protection, detection, and response
We believe Sophos’ recognition in the 2026 Gartner Magic Quadrant for Endpoint Protection is part of a broader pattern of industry validation throughout endpoint protection, extended detection and response (XDR), managed detection and response (MDR), and firewall solutions:
- Sophos is named a 2026 Gartner® Peer Insights™ Customers’ Choice in the 2026 Gartner® Peer Insights™ Voice of the Customer Report for Endpoint Protection
- Sophos is named a 2025 Gartner® Peer Insights™ Customers’ Choice in the 2025 Gartner® Peer Insights™ Voice of the Customer Report for Extended Detection and Response
- Sophos is ranked as the #1 Overall solution in Endpoint Protection (EPP), Managed Detection and Response (MDR), Extended Detection and Response (XDR), Endpoint Detection and Response (EDR), and Firewall Software in the G2 Spring 2026 Grid® Reports
- Sophos achieved 100% detection coverage in the MITRE ATT&CK® Enterprise 2025 Evaluation
Together, we feel these recognitions reinforce what Sophos is focused on delivering: security that works as a system, adapts with the threat landscape, and helps organizations strengthen their defenses without adding unnecessary complexity.
Strong endpoint protection remains critical. But in today’s AI-driven threat environment, it’s most powerful when it’s part of a broader, coordinated defense.
For more information about Sophos Endpoint, visit sophos.com/endpoint.
Source: Sophos
G2 has published its Summer 2026 Reports, and customers once again ranked Sophos as a top security vendor.
For the second consecutive G2 Seasonal Report, customers rated Sophos as the #1 Overall solution in Endpoint Protection Platforms (EPP), Managed Detection and Response (MDR), Extended Detection and Response (XDR), Endpoint Detection and Response (EDR), and Firewall Software.
Speaking to the power of our platform, Sophos is named as a Leader for the 16th consecutive time across every G2 Overall Grid® that defines modern security operations: Endpoint Protection Platforms, Endpoint Detection and Response (EDR), Extended Detection and Response (XDR), Firewall Software, and Managed Detection and Response (MDR).
These recognitions come from verified peer reviews and reflect what security teams value most: faster time to outcome, simpler operations, and the confidence of a platform that scales from prevention to managed response.
Managed Detection and Response
The G2 Summer 2026 Reports marks the eighth consecutive G2 Seasonal Report where Sophos was ranked as the #1 Overall MDR solution. Additionally, Sophos MDR was named the #1 solution among the Enterprise and Mid-Market customer segments. Sophos MDR also earned the Best Results and Best Usability distinctions among both Enterprise and Mid-Market customers.
Endpoint
The Summer 2026 Reports marks the second consecutive G2 Seasonal Report where Sophos Endpoint was recognized as the #1 Overall solution across EPP, EDR, and XDR. In total, Sophos Endpoint was ranked #1 in 26 total reports across these three categories. Sophos Endpoint also received the Best Results and Best Usability distinctions in the Endpoint Protection Platforms category, highlighting the strong user outcomes from deploying our industry-leading protection.
Firewall
The G2 Spring 2026 Reports marks Sophos Firewall’s fourteenth consecutive #1 Overall Firewall ranking. It’s also the fourth consecutive G2 Seasonal Report where all customer segments (Enterprise, Mid-Market and Small Business users) rated Sophos Firewall as the #1 solution. Sophos Firewall also earned the Overall Best Results, Best Usability, Best Relationship, and Most Implementable badges.
What Sophos customers are saying
“One of the most trustworthy endpoint security products” said a user in the Mid-Market segment
“I like Sophos endpoint for its strong real time protection ransomware defense and centralized management through Sophos central” said a user in the Small Business segment
“What I like most about Sophos MDR is the proactive threat detection and rapid response capabilities. The service’s ability to quickly identify and mitigate potential security threats before they can cause significant harm is invaluable” said a Head of IT in the Mid-Market segment
“[Sophos MDR’s] 24/7 security coverage provides continuous monitoring and alerts us promptly to any suspicious activity, ensuring our network’s safety and allowing us to track and resolve issues efficiently” said a user in the Mid-Market segment
“The advanced threat protection features like Intrusion Prevention, Web Filtering, and Sandstorm make Sophos Firewall a powerful tool against both known and unknown threats” said an IT Infrastructure Manager in the Mid-Market segment
“What I like best about Sophos Firewall is its strong security features combined with an easy-to-use interface, making it simple to manage threats, monitor traffic, and protect the network without complex configuration” said a System Security Administrator in the Mid-Market segment
For more information on our services and products, speak to your Sophos partner or representative and visit our website.
Source: Sophos
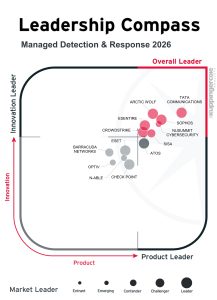
Sophos has been named an Overall Leader in the 2026 KuppingerCole Analysts Leadership Compass for Managed Detection and Response (MDR). The recognition reflects Sophos’ focus on delivering real-world security outcomes through expert-led detection, investigation, and response across hybrid environments.
The KuppingerCole Analysts Leadership Compass for MDR 2026 evaluates MDR providers based on their ability to provide continuous monitoring, validated detections, and coordinated response actions in an increasingly complex threat landscape, and recognizes Sophos in four categories: Overall Leadership, Product Leadership, Innovation Leadership, and Market Leadership.
A balance of maturity and innovation
According to KuppingerCole Analysts, Overall Leaders combine proven service execution with ongoing innovation. These providers deliver reliable MDR outcomes while continuing to evolve their capabilities to address new customer needs and emerging threats.
The report highlights how Sophos pairs established MDR operations with ongoing innovation through Sophos X-Ops and AI-supported investigation workflows. The report also points to Sophos’ simplified, all-inclusive service approach, which includes full incident response coverage designed to provide operational assurance.
Leadership across product, innovation, and market
Sophos was also recognized as a Product Leader for the breadth and completeness of its MDR capabilities, which include 24/7 monitoring, validated detection, threat hunting, incident response, automation, and integration with existing security technologies.
KuppingerCole Analysts note that Sophos MDR supports visibility across endpoint, network, cloud, and identity telemetry, with strong interoperability across both Sophos and third-party security tools delivered through the Sophos Central platform.
As an Innovation Leader, Sophos is recognized for advancing how MDR services are delivered, with a focus on analyst effectiveness and investigation quality. The report highlights Sophos’ use of GenAI and agentic AI supported investigation workflows, alongside the role of Sophos X-Ops, and notes Sophos’ PRIME initiative, which applies AI-driven quality assurance to improve analyst case clarity, investigation depth, and consistency across MDR engagements.
Agentic AI within Sophos MDR delivers the speed, consistency and scale to protect against AI-driven attacks, with full human accountability. The goal is simple: reduce noise, investigate faster, and deliver strong, consistent security outcomes for all customers.
Sophos is further recognized for Market Leadership, citing Sophos’ global presence and established channel‑led model as key contributors to its position in the MDR market.
Customer recognition
This focus on real‑world outcomes is also reflected in customer‑driven recognition. Sophos was recently named a 2026 Gartner Peer Insights Customers’ Choice for Managed Detection and Response, based on direct feedback from verified MDR customers.
Sophos MDR also earned top recognition in the G2 Spring 2026 Reports, ranking as the #1 Overall MDR solution based on verified customer reviews, further reinforcing Sophos’ position as a trusted MDR provider.
Learn more
To learn more about the evaluation criteria and findings, download the KuppingerCole Analysts Leadership Compass for Managed Detection and Response 2026.
For additional details on Sophos MDR, visit sophos.com/mdr.
Source: Sophos
Claude Mythos Preview and similar AI models feel different, not because they’ve uncovered a new category of attack, but because they dramatically accelerate familiar ones. Research results show that AI can assist in identifying previously unknown vulnerabilities at a speed and scale that simply wasn’t possible before. At the same time, AI shortens the gap to exploitation, allowing even less-skilled adversaries to weaponize vulnerabilities far more quickly.
That combination – faster discovery and faster weaponization – is what has captured attention across governments, enterprises, and the security industry. Even where exploitation remains difficult, incremental gains in attacker speed matter when defenders are already operating under tight constraints.
What actually changes for network security
The most important shift isn’t that AI will suddenly exploit everything or that everything AI discovers can be exploited. It’s that through the use of AI, the gap between exposure and adversary action is narrowing.
AI-assisted attackers can scan environments faster, identify weak points more consistently, and move from reconnaissance to action with less effort. At the same time, most organizations still face patch windows, time-consuming change management processes, and limited security resources.
This mismatch increases pressure at the network edge. Firewalls, edge devices, and remote access services are often internet-facing, highly privileged, and always on, making them attractive targets when attackers are moving at machine speed.
Why this matters beyond Mythos itself
Claude Mythos Preview should be viewed as a leading indicator, not an outlier. AI-assisted vulnerability discovery will become cheaper, more common, and more widely available over time.
Whether a specific model is restricted or widely released matters less than the broader trend: defenders should assume attackers will continue to gain speed, scale, and efficiency.
Practical guidance for network security teams
This isn’t a moment for panic, but it is a moment to reassess assumptions.
First, stop planning for perfect patching. Patch delays are inevitable due to testing, downtime windows, and operational risk. Security strategies (and products) that rely on flawless timing break down under AI-driven pressure.
Second, focus on reducing exposure by default. Limiting exposed services, hardening configurations, and removing unnecessary access paths reduces risk before an attacker ever shows up. This includes decommissioning all unsupported or end-of-life products on the network that present an easy target for attackers.
Third, prioritize detection and response speed. When prevention fails, rapid visibility and containment determine impact.
Why Sophos Firewall and Secure by Design matter in the Mythos era
AI‑accelerated threats don’t just demand more firewall features – they demand a different design philosophy. At the network edge, where devices are internet‑facing, highly privileged, and always on, security has to be built in, not bolted on.
Sophos Firewall is designed around Secure by Design principles that assume vulnerabilities, misconfigurations, and patch delays will happen, and focuses on reducing exposure and operational risk by default. This includes hardened defaults, strict privilege separation, a hardened OS and control plane, and automated, zero‑downtime security updates that shorten the window in which known issues can be exploited – without waiting for maintenance windows or perfect administration.
It also includes integrity monitoring across the full Sophos install base using the Sophos XDR Linux sensor, enabling early detection of tampering or suspicious activity on any firewall that benefits the whole Sophos Firewall community.
Prevention alone isn’t enough at the edge, which is why Sophos Firewall also automates response. Through Synchronized Security and Active Threat Response, the firewall can react immediately when suspicious activity is detected, isolating affected systems, blocking lateral movement, and cutting off command‑and‑control traffic without waiting for manual intervention. This matters most for internet‑facing infrastructure, where compromise can translate directly into network‑wide impact.
What’s more, these automated responses aren’t limited to Sophos signals. Sophos Firewall can also act on intelligence from third‑party threat feeds, enabling consistent detection and containment even when threats are identified outside the Sophos ecosystem, helping organizations standardize response across complex, multi‑vendor environments.
The takeaway
Claude Mythos is important because it highlights a reality defenders were already facing: attackers are moving faster, at greater scale, and with less friction than before.
In this environment, network security must assume that zero-days will occur, patch delays will exist, and configurations won’t always be perfect. The real question isn’t whether AI will change the threat landscape – it already has. The question is whether your network defenses are designed for that reality.
Source: Sophos
The prospect that your business may be targeted maliciously is sadly no longer an edge case but an everyday reality facing any modern business. No matter your size or profile, bad actors will exploit opportunities to take your business hostage for financial gain.
In part one we discussed how NIS2 legislation places a large importance on business continuity[AF1] and how the right processes and backup tools can help in response to ransomware and other cybersecurity incidents.
However, there is another crucial part of any security response and that’s the need to potentially report the breach to authorities. Here we look at some of those obligations.
While it may be tempting to prioritise resolving the breach, the countdown often begins the moment you realise your systems have been compromised. Timelines can be stringent, so it’s not something that can be worked out during the response. It needs to be embedded as part of your processes with clear expectations on who will carry out the required reporting.
The clock is ticking — it’s time to report the breach
It’s important to remember that in some cases you need to notify the relevant body within 24 hours of discovering an incident, and in some scenarios, as little as four.
Here is key legislation that may affect your organisation.
GDPR/UK GDPR – 72 hours
Who: Any data controller doing business within the EU or UK respectively.
If you find a breach that looks like it will be a risk to individual data, then the relevant authority needs to be notified within 72 hours of you discovering the issue.
That may be an intentional breach of your systems that gave access to customer data, or an accidental issue such as a hard drive being lost that contains data. The key judgement is if individuals may be adversely affected by the consequences.
If you’re in doubt of whether your incident reaches the reporting threshold, it’s best to begin the countdown anyway and err on the side of caution. Be sure to record everything you do as a part of your response, then be sure to make the contact before the 72 hours is up.
NIS2 – 24 hours
Who: NIS2 is EU legislation focused on companies that it deems “critical” or “important,” to minimise disruption to vital sectors and infrastructure. However, you may be indirectly affected if you are a key part of a company’s supply chain that does fall under NIS2 regulation.
For significant data breaches, an initial notification must be made within 24 hours to the member state’s CSIRT (computer security incident response team). A full incident notification needs then be made within 72 hours, and a full report within a month.
If you are a provider in a supply chain to a NIS2 company, you don’t have a requirement to report an incident to the authorities, but you should let your customer know and the timeframe to do so may be specified in your contract.
The UK also has its own NIS regulation, with a report required to the ICO within 72 hours for any incident that has a substantial impact on the provision of a company’s services.
DORA – 4 hours
Who: Any financial organisations doing business within the EU. That includes (but is not limited to) banks, insurers and payment institutions. However, much like NIS2 can extend beyond companies under its remit, DORA also counts critical third-party IT providers as part of its remit.
If a company under DORA legislation detects a breach it has to make an initial report within 24 hours from detection. However, once investigated if it is classed as a major incident then the reporting window shrinks to just four hours (or whatever is left within the 24-hour window).
An intermediate report is then due within 72 hours, and a full report within a month.
Other legislation
There are other regional requirements, with countries such as the UAE and Saudi Arabia each having their own Personal Data Protection Law (PDPL). It highlights the need to understand the legislation in whatever countries you are operating in, and that responses may differ depending on location.
The potential trifecta of reporting
For some companies it may be that you need to report a breach to the GDPR, NIS2 and DORA authorities. Each has a different reporting pathway, and different timescales.
This highlights the very real need to have clear processes, with clear responsibilities outlining who does what and when. The ramifications of not doing so could be costly.
Remember, the authorities are there to help
While they can impose hefty fines for serious and wide-reaching breaches, it’s important to not see the relevant authorities solely as enforcement bodies. By notifying them quickly, they can help you navigate potential implications and mitigate damage. For countries in the EU, the relevant bodies can also help cross-border coordination.
As the ICO explains for GDPR breaches, “It’s understandable if you’re concerned about what happens next. But we’re here to help you understand what happened and to prevent it happening again.”
It’s all part of incident management
All these reporting requirements form the core of effective incident management. They ensure all team members are on the same page, facilitate rapid decision-making and help track the progress of incident resolution.
If a breach is reported to an authority, then you may be called upon to demonstrate everything you did, step by step, as part of identifying the issue and resolving it. You may also be asked to show evidence of what you did in the months leading up to the incident as well.
As such, you need the right tools in place to document processes and systems — and not only demonstrate that you have the data required, but also how you use it to manage risk within your business. Find out how IT Glue, with its robust documentation capabilities, can help you navigate your response to an incident.
Source: Kaseya
Modern cyber threats don’t wait for teams to be ready. They exploit gaps when resources are stretched thin, evolve faster than most organizations can adapt, and frequently strike outside normal business hours.
Many security teams find themselves balancing the need to strengthen defenses proactively while ensuring expert help will be available when an incident occurs. Proactive testing, readiness exercises, and expert assessments are essential for reducing risk, yet they’re often delayed or deprioritized as day‑to‑day demands take over.
When a serious incident happens, organizations often scramble to find help under pressure, with limited time and little certainty around response availability or cost.
Introducing the Sophos Security Services Retainer
The Sophos Security Services Retainer is designed to change that dynamic. This new offering brings together proactive, readiness, professional, and emergency incident response services in a single, easy‑to‑consume service, giving organizations a practical way to plan, prepare, and respond with confidence.
The Sophos Security Services Retainer provides flexible access to services that uncover weaknesses and strengthen defenses, plus guaranteed emergency incident response coverage with defined service‑level agreements.
Through a service‑unit model, organizations can plan and prioritize proactive security activities throughout the year rather than relying on ad‑hoc engagements. If a major incident occurs, experienced Sophos incident responders are ready to act quickly, without delays caused by procurement hurdles or uncertainty around response availability.
This approach helps organizations move away from reactive, last‑minute decisions and toward a more intentional security strategy.
Strengthening coverage across the security lifecycle
The Security Services Retainer is built to support organizations across the full security lifecycle:
- Service Units can be used for a wide range of expert-led proactive services, such as penetration testing, web application security assessments, tabletop exercises, and professional services that help organizations maximize the value of their security investments.
- When a cyberattack strikes, the retainer ensures rapid access to Sophos Emergency Incident Response – with defined SLAs for response and pre-negotiated discounted hourly rates – providing organizations confidence that threats can be quickly investigated, contained, and neutralized.
A smarter way to plan, prepare, and respond to threats
By bringing preparedness and response together, the Security Services Retainer removes the artificial divide between “before” and “during” an incident. Proactive security becomes planned and predictable, not optional or sporadic. Emergency response becomes assured, not uncertain.
The result is a more balanced approach to cybersecurity, one that helps reduce operational stress, improve stakeholder assurance, and demonstrate a strong, end‑to‑end security posture to executives, regulators, and cyber insurance providers alike.
Speak to an expert today or visit sophos.com/retainer to learn more.
Source: Sophos
In today’s interconnected world, one company’s outage can affect the delivery of a country’s vital services and even impact the wider economy, as was evidenced by the cyberattack on Jaguar Land Rover, which negatively impacted the UK’s GDP.
At the heart of NIS2 is a desire for business continuity. It encourages companies to properly document their processes, plan for eventualities and identify weaknesses in their supply chains.
Importantly, NIS2 makes cybersecurity and resilience a board room responsibility, with potential penalties for business leaders. In other words, leaving security solely to IT is no longer enough.
With that in mind, strengthening your ability to respond to security incidents — and, importantly, recover from them — must form a core part of every business’s security approach.
In the first part of this guide, we’ll take a look at your internal readiness. Then, in part two, we’ll discuss how to deal with the various regulatory reporting requirements in the event of an incident.
“Ransomware is the single biggest threat to organisations online”
Those are not our words. The statement comes from the Centre for Cybersecurity in Belgium, which reported that ransomware attacks more than doubled between 2021 and 2024.
Ransomware remains one of the most disruptive forms of cyberattack, disabling your systems and disrupting your business unless a ransom is paid. Even if your company were to pay, recovery is not guaranteed. Not all attacks are necessarily destructive, however. A data breach, for example, may not impact your ability to carry on business as usual, but the reputational damage and potential financial penalties can have significant long-term consequences.
The reality is that no matter how much you secure your business, some level of risk always remains — and that risk exists 24/7/365, even when your team is offline.
Get your recovery plan in place – and make sure it works
In our Mastering modern recovery: New essentials for IT managers, we cover the three fundamentals of disaster recovery planning:
- Assess risks and identify critical systems. A thorough risk assessment helps identify the most critical systems that need immediate attention during a disaster scenario and helps prioritise them according to their importance to business operations.
- Create a step-by-step recovery plan. Develop recovery procedures for different disaster scenarios, including cyberattacks, natural disasters or hardware failures. Each scenario should have a clear, step-by-step plan for recovery with clear responsibilities.
- Test and maintain the plan. A recovery plan is only as good as its execution. Regular testing, updates and audits are critical to ensuring long-term viability and adapting to evolving threats, technologies and infrastructure changes.
The good news is that anyone following this approach is already well placed to meet some NIS2 requirements, such as risk analysis and information security, incident handling and business continuity measures.
If you’re struggling to get senior leaders’ buy-in, aligning your IT goals with NIS2 objectives is a good way to underline the importance of proper disaster recovery planning.
Backups form an essential part of NIS2 compliance
The widely accepted approach to backup strategy has traditionally followed the 3-2-1 rule:
- 3 copies of data (to protect against data loss)
- 2 different formats (stored on at least two media types)
- 1 off-site copy (to protect against physical disasters)
However, it’s now recommended to add two more measures for true backup efficacy:
- 1 immutable copy (ensuring ransomware-proof backups)
- 0 doubt you can recover (regular testing guarantees reliability)
The importance of immutable backups was made abundantly clear in April 2026 when an AI agent not only deleted a company’s entire customer database, but recent backups as well, impacting customers for days and making international headline news.
This shows how getting it right is of paramount importance: a matter of business continuity, regulatory compliance — and keeping your company out of the headlines.
Ensuring confidence in recovery
NIS2 emphasises the need for policies that assess operational effectiveness. Just having backups is not enough. You need to be confident in your ability to restore systems and get your business back online quickly.
While you should be running disaster recovery tests on a regular basis, this can be augmented by tools that offer automated testing of backups.
When monitored and reported alongside metrics such as RPO and RTO, these capabilities provide greater confidence in your backup posture and also demonstrate the required level of reporting.
Don’t back up bad data
The possibility of ransomware creeping into your backups is a cause for concern. It’s also important to understand the health of the data that you are backing up.
As part of your backup automation, you can use machine learning to identify behaviour symptomatic of a ransomware infection. By continually running and analysing every backup, it can look out for infected backups and stop the issue before it becomes a problem.
Make sure your backups are region-appropriate
Your data is not universally accessible. Different regions have different sovereignty laws, so it’s important to understand where backups are stored and whether they can be restored legally from that territory. Regulations such as GDPR continue to apply during recovery operations, so it’s important to understand that the tools you use and the location of your data remain compliant.
Meeting your regulatory requirements
Kaseya offers businesses peace of mind, ensuring that their valuable data is safe, compliant, and most importantly, recoverable. Read our guide to mastering modern recovery to learn more about building a resilient recovery strategy.
But recovery planning is only part of the equation. During a security incident, organisations must also manage their legal and regulatory reporting obligations. In part two, we’ll delve into NIS2 and GDPR and the various reporting requirements in EMEA.
Source: Kaseya
In the modern cybersecurity landscape, the traditional network perimeter has dissolved. Today, identity as a perimeter keeps getting stronger and stronger.
As organizations accelerate cloud adoption and integrate AI systems, the number of digital identities, both human and non-human, has grown exponentially. Each credential, API key, and service account now represents a potential entry point for adversaries.
 To understand the scale of this shift, we conducted a survey to examine the impact of identity threats. The survey consisted of 5,000 IT and cybersecurity leaders across 17 countries and 14 industries. Of those organizations, 71% were hit by identity-related breaches in the last year. So the findings reveal that identity-related breaches are no longer outliers; they’re now a primary challenge for modern defense.
To understand the scale of this shift, we conducted a survey to examine the impact of identity threats. The survey consisted of 5,000 IT and cybersecurity leaders across 17 countries and 14 industries. Of those organizations, 71% were hit by identity-related breaches in the last year. So the findings reveal that identity-related breaches are no longer outliers; they’re now a primary challenge for modern defense.
Click here to access the full report now or continue reading for some highlights.
Identity breaches are the new normal
The research shows that identity-related security breaches are pervasive across all sectors.
- 71% of organizations experienced at least one identity-related breach in the past 12 months
- Affected organizations were hit by an average of three identity attacks within the year
- Geographically, Switzerland reported the highest breach rate at 89%, followed by Mexico at 83%
- The energy, oil/gas, and utilities sector saw the highest breach rate at 80%, while IT and technology organizations reported the lowest at 63%
The identity-to-ransomware pipeline
One of the most critical findings is the direct link between identity compromise and ransomware. Attackers are increasingly using stolen credentials as their primary mechanism for delivery.
Two-thirds of ransomware victims (67%) reported that their ransomware incident was directly tied to their most significant identity attack. This establishes a clear pipeline where a single compromised account can lead to full-scale business paralysis.
The rising risk of non-human identities
While human error remains a top contributor to breaches, the mismanagement of non-human identities (NHIs) has emerged as an escalating threat. NHIs – including API keys, service accounts, and AI agents – often outnumber human identities by ratios as high as 100:1.
- Weak NHI management was a root cause in 41% of successful identity breaches
- Agentic AI is a major driver of this risk, as AI agents can autonomously create new credentials and demand broad, persistent access without human oversight
- Despite the risk, only 34% of organizations regularly audit or rotate service accounts and NHIs
The financial toll of failure
When identity defenses fail, the financial impact is severe. The average cost to rectify a successful identity breach is $1.64 million, with nearly half of all victims suffering data theft or ransomware as a direct consequence.
The data also highlights a resource gap: smaller organizations (100–250 employees) were nearly twice as likely to fail to detect an identity attack compared to organizations with over 1,000 employees.
Read the report
The 2026 data serves as a reminder that identity security is a continuous operational discipline, not a one-time project. To defend against these evolving threats, organizations must move beyond basic hygiene and implement multi-layered defenses, such as enforcing MFA for all accounts and adopting a Zero Trust security model.For a deeper dive into industry-specific data and comprehensive security recommendations, you can read the full State of Identity Security 2026 report.
Source: Sophos
A zero-day attack leverages a previously unknown vulnerability — one that hasn’t been detected by developers or security experts. Because the vulnerability is unknown, there is typically no existing patch or fix, leaving systems temporarily vulnerable until a solution can be developed and deployed. The term “zero-day” refers to the fact that defenders have “zero days” of warning before the attack hits, making these attacks particularly difficult to stop.
In the realm of email security, zero-day attacks often come through cleverly disguised phishing emails or malicious attachments, which can exploit unknown software vulnerabilities, bypass detection, and deliver malware into an organization’s network. This could lead to devastating outcomes, such as data theft, system hijacking, or ransomware attacks.
How Zero-Day Threats Are Executed Via Email
Zero-day attacks can be executed in several ways, including:
- Malicious Attachments: Attackers may craft a malicious attachment that exploits zero-day vulnerability in email clients or document readers. When recipients open the attachment, malware installs itself on the device and begins its damaging process, often without any visual cues or warnings.
- Malicious Links: Sometimes, attackers embed links in emails that lead to compromised websites. The site may exploit a browser vulnerability unknown to the security community, allowing malware to be downloaded onto the victim’s device when they visit the site.
- Spear Phishing & Social Engineering: Attackers carefully research their targets and craft emails that appear legitimate and credible. These emails might not even contain any detectable malicious elements, but leverage social engineering tactics to prompt action that inadvertently exposes recipients to zero-day exploits.
How to Prevent Zero-Day Attacks
- Advanced Email Threat Protection Solutions: Advanced email threat protection solutions use sophisticated data science, AI, and machine learning to detect unusual patterns in email traffic. These tools often employ behavioral analysis and sandboxing to observe how email attachments and links behave in a controlled environment, identifying potentially malicious activities without directly exposing your network.
- Attachment Protection: Using sandboxing provides a safe, isolated environment where email attachments can be executed and analyzed without risking the broader network at large. This approach allows security teams to observe how attachments behave in a controlled setting, detecting malware or zero-day exploits that might be disguised as innocuous files.
- URL Protection: URL analysis would scan all incoming emails for any suspicious malicious URLs, and thus would prevent zero-day exploits from being executed.
Cloud Based Defenses that Block Zero-Day Attacks
Cloud based defenses block zero‑day attacks by analyzing email behavior in real time rather than relying on known signatures. Using AI‑driven detection, sandboxing, and browser isolation, these solutions can safely inspect unknown attachments and links, stopping malicious activity before it reaches users or endpoints. Because protections are continuously updated in the cloud, organizations gain faster, scalable defenses against newly emerging threats.
Behavioral and AI-Driven Threat Detection
Behavioral and AI‑driven threat detection monitors how emails, links, and attachments behave rather than relying on known signatures. By spotting anomalies in user behavior and message patterns, it can identify and stop zero‑day threats that traditional controls miss.
Sandboxing and Dynamic Analysis
Sandboxing and dynamic analysis safely open attachments and execute code in an isolated environment to observe malicious behavior. This allows security teams to detect zero‑day exploits before they ever reach end users or production systems.
Browser Isolation
Browser isolation separates web content from the user’s device by executing potentially risky sessions in a secure, remote environment. Even if a zero‑day exploit is present, the threat is contained and prevented from accessing local systems or data.
Realtime URL, Domain, and Identity Verification
Realtime URL, domain, and identity verification continuously analyzes links, sender reputation, and authentication signals at the moment of click. This helps block newly created malicious domains and spoofed identities commonly used in zero‑day email attacks.
CPU Level Zero-Day Blocking
CPU level zero-day blocking stops exploit techniques at the hardware or execution level before malicious code can run. By enforcing protections below the operating system, it can prevent entire classes of unknown exploits from succeeding.
Common Types of Zero-Day Email Threats
Zero‑day email threats exploit previously unknown email vulnerabilities to deliver malware or gain unauthorized access before defenses can be updated. These attacks often arrive through trusted‑looking messages that disguise malicious activity until it’s too late.
Zero-Day Malware
Zero‑day malware uses unknown exploits to bypass traditional signature‑based defenses and infect systems through email attachments or links. Once executed, it can steal data, establish persistence, or deploy additional payloads such as ransomware.
Zero-Day Exploit Kits
Zero‑day exploit kits are collections of attack tools designed to automatically scan for and exploit unknown vulnerabilities. Delivered via phishing emails or malicious links, they enable attackers to compromise systems with little user interaction.
Zero-Day Remote Code Execution Attacks
Zero‑day remote code execution attacks allow attackers to run malicious code on a victim’s system without authorization. When delivered through email, these attacks can fully compromise devices by exploiting unpatched application flaws or operating system flaws.
Zero-Day Browser Exploits
Zero‑day browser exploits take advantage of unknown weaknesses in web browsers or browser plugins. A single click on a malicious email link can trigger the exploit, enabling malware installation or session hijacking.
Zero-Day Document-Reader Exploits
Zero‑day document reader exploits target vulnerabilities in applications like PDF or word processors. Malicious attachments appear legitimate but execute hidden code when opened, often without any visible warning to the user.
Best Practices for Cloud Email Protection
Effective cloud email security combines layered defenses such as AI‑driven detection, sandboxing, and strong authentication to stop both known and unknown threats. Regularly updating policies, enabling DMARC and identity checks, and educating users on phishing tactics help reduce risk and improve resilience against zero‑day email attacks.
How Fortra’s Cloud Email Security Protects Against Zero-Day Vulnerabilities
Fortra Cloud Email Security protects against zero‑day vulnerabilities by analyzing email behavior instead of relying on static signatures. Using advanced AI, real‑time inspection, and isolation techniques, Fortra can detect and stop unknown threats before they reach users or compromise systems.
FAQs About Email Security and Zero-Day Threat Protection
- What is a zero‑day email attack?
A zero‑day email attack exploits a previously unknown vulnerability in software, browsers, or email clients before a patch is available. These attacks often arrive through phishing emails, malicious links, or attachments designed to evade traditional detection. - Why are zero‑day threats difficult to detect with traditional email security?
Traditional email security relies heavily on known signatures and threat intelligence. Zero‑day attacks bypass these controls because there is no existing signature or prior knowledge of the exploit. - How does cloud email security help stop zero‑day attacks?
Cloud email security analyzes behavior in real time using AI, sandboxing, and isolation rather than relying on static rules. This allows it to detect suspicious activity and stop unknown threats before they reach users. - Can zero‑day attacks lead to data breaches or ransomware?
Yes, successful zero‑day email attacks can result in credential theft, account takeover, ransomware deployment, or full system compromise. Early detection and containment are critical to preventing widespread damage. - What steps can organizations take to reduce zero‑day email risk?
Organizations should deploy layered, cloud‑based email defenses, enable strong authentication like DMARC, and regularly train users to recognize phishing and social engineering tactics. These measures reduce exposure even when new vulnerabilities emerge.
Source: Fortra
For decades, passwords have been the standard method for protecting access to systems and accounts. However, passwords can be compromised or stolen via tactics such as brute-force attacks, phishing attacks, and infostealer malware. The shift to multi-factor authentication (MFA) added another layer of security by requiring additional authentication to verify the user’s identity – some combination of something you know, own, or (in the case of biometrics) are. While MFA is stronger than passwords alone, threat actors have discovered ways to circumvent it, including adversary-in-the-middle (AiTM) attacks, session hijacking, MFA fatigue, and social engineering to reset or disable MFA. Passkeys were introduced as a phishing-resistant MFA solution.
How passkeys work
Passkeys are built on FIDO2 public key cryptography, generating a unique public-private keypair for each user and service. The public key is sent to the server; the private key is stored in a credential manager (sometimes called the sync fabric) or on a hardware security key. During sign in, the server sends a random challenge to the user’s device. When the user provides their established verification (e.g., biometric input, PIN), the device signs the challenge with the private key. The server verifies the signature against the stored public key. No credentials are transmitted, so they cannot be intercepted by attackers or malware. Because passkeys are cryptographically bound to the origin, traditional phishing (e.g., soliciting credentials via fake login pages) is ineffective.
Benefits
Passkeys benefit organizations and employees. The following are some of the primary advantages:
- Enhanced security – Replacing passwords with passkeys reduces the risk of credential-based attacks (e.g., brute-force attacks, infostealers, phishing). These attacks can lead to operational disruptions, substantial recovery costs, and reputational damage.
- Convenience and time savings – Users do not have to worry about selecting, maintaining, and protecting system passwords. They also don’t have to determine if they need to enter a code or approve a push notification. The login process is simpler and faster, and the reduced friction is especially beneficial during security-critical and time-sensitive scenarios. A combination of passkeys and single sign-on for internal resources can streamline access even further. While some resources and websites will still require passwords or other authentication mechanisms, reducing the number of logins and reauthentication requests makes employees’ lives easier.
- Fewer help desk requests – While the adoption of passkeys will not eliminate access problems, it can significantly reduce the number of tickets related to password errors, reset requests, lost or malfunctioning authenticator devices, and delayed or missing verification codes due to poor mobile signal. Support teams can redirect the time typically consumed by these tickets to focus on other issues.
Considerations and caveats
Most organizations will not need to build passkey infrastructure from scratch. Major identity providers such as Microsoft, Google, and Okta offer passkey support as part of their existing authentication platforms. The implementation decision is less about selecting a standalone passkey product and more about how to enable and enforce passkeys within your current identity stack. Prior to evaluating various solutions, organizations need to have a firm understanding of their environment and must consider the implications for employees’ personal devices if applicable. Some solutions may not be compatible with all operating systems or with older versions. Organizations also need to consider where passkeys will be stored (e.g., directly on the user’s laptop, in a cloud-based password manager, on a physical token such as a YubiKey) and how to restore access if a passkey is lost, deleted, or corrupted. Our FAQ document addresses additional considerations.
Note that while passkeys provide a strong authentication option, they are not infallible. Overall security hygiene is important, including ensuring that appropriate security controls are in place, regularly auditing privileges and accesses, and keeping systems and software patched against known vulnerabilities. Organizations should also educate users about safeguarding access and how to recognize social engineering attempts.
Success factors for passkey implementation
Based on our passkey journey and advice published by other industry experts, successful implementation requires elements such as internal partnerships, proper planning, and clear communication. We identified the following factors that can ease the transition. These factors are covered in more detail in the implementation guide.
- Involve the right teams
- Keep users in mind
- Explain the benefits
- Own your past mistakes
- Diversify early adopters
- Counter resistance with facts and assurances
- Send clear communications at an appropriate cadence
- Write support scripts and train support teams early
- Listen to users
How we can help
During our passkey implementation, we encountered known and unexpected challenges. To help other organizations who are considering or embarking on the transition, we created a playbook containing an implementation guide, an FAQ, a downloadable passkey rollout template that can be used by project managers, and downloadable overview slides.
Source: Sophos
In cybersecurity, “zero day” is frequently diluted and used as a catch-all for any unpatched vulnerability. This article breaks down the three mandatory elements of a true zero day, illustrating why the distinction between a zero day and a known, but unpatched, flaw is critical for effective defense.
Getting This Cybersecurity Terminology Right is a Defensive Necessity
Words matter in cybersecurity. The language we use shapes how boards allocate budget, how regulators write policy, how journalists frame incidents, and how organizations prioritize risk. Throughout the history of cybersecurity, arguably no term has been more abused, diluted, or misapplied than “zero day.”
It has become a headline accelerant, a marketing crutch, a faux message of urgency, and a convenient shortcut for discussing complex problems. Bluntly, when we get the definition wrong, we get the response wrong, and when we get the response wrong, we react with knee-jerk impulses that take focus away from what really matters.
Defining zero day vulnerabilities: It’s not a “new” flaw
To be clear, a zero day vulnerability is not a synonym for “unpatched” or “critical vulnerability.” It is also not interchangeable with a “new” vulnerability or one that simply lacks a fix. A zero day is a very specific condition for multiple states of a vulnerability and associated exploitation and deserves precision when mentioned by a vendor or the media.
What is a zero day vulnerability?
Straight Forwardly: A zero-day vulnerability is a previously unknown flaw in software or hardware that is potentially being actively exploited regardless of its severity, where the vendor (or responsible open-source community) has had “zero days” to develop and release a patch at the time of public disclosure. The emphasis on three elements: the threat is unknown to the vendor, it is potentially being exploited, and it is disclosed to the public. If you remove any one of these elements, it is no longer a zero day. For example, if the vulnerability has been patched—even if active exploitation is occurring—it is no longer a zero day but a known vulnerability following responsible public disclosure. Misusing the term—or creating hybrid phrases like “undisclosed” or “unknown” zero day—only muddies the waters for risk prioritization.
Why the industry confuses zero days with known vulnerabilities
This distinction matters because the industry routinely collapses three very different concepts into one overloaded term:
- Known, but unpatched, vulnerabilities: The industry sees CVEs reserved all the time for these situations. These flaws are publicly or privately disclosed, often cataloged, sometimes scored, and frequently prioritized for remediation by the vendor, based on severity and complexity to resolve. They are dangerous, but they are not zero days.
- Newly disclosed vulnerabilities: These may lack a patch, but are not yet known to be exploited in the wild. These are serious, but without a working exploit, they aren’t categorized as zero days.
- True zero days: These are the vulnerabilities defenders didn’t know existed until threat actors demonstrated that knowledge through active exploitation (zero day exploit) before a patch was available.
The cost of sensationalism
Why does this confusion persist and why do cybersecurity professionals and the media still get this wrong? Simply put, “zero day” sounds catastrophic. It implies an inevitability that fuels sensationalism. For the media, it suggests that no defense could have worked, creating a sense of extreme urgency to drive engagement. For organizations explaining a breach, it can sound like absolution—an excuse that nothing could have thwarted the attack and subsequent breaches. For vendors selling tools, it creates an artificial, absolute need for their specific solutions to be secured regardless of the moment of time.
For cybersecurity professionals, the cost of this misuse is not academic. When the term is used excessively, real zero days lose their urgency and budget. Security teams become desensitized and lose focus. Boards will begin to assume that breaches are unavoidable acts of nature rather than failures of control, hygiene, or prioritization. Regulators then struggle to distinguish genuine negligence from unforeseeable risk. Over time, the term loses its meaning.
The reality of modern zero-day exploitation
Today, true zero days are rare and expensive. They are usually not wasted on low-value targets. Instead, they are typically chained with other weaknesses, like identity-based attack vectors, delivered through trusted pathways and executed with stealth precision.
Nation states and top-tier cybercrime syndicates do not “burn” zero days casually. They use them only when the return justifies the cost of development and risk of public exposure. Once the vulnerability is disclosed and patched, their advantage as a weapon is lost. That reality alone tells us how careful we must be when invoking the term.
A proper understanding of zero days also changes the conversation around cyber defense. You cannot patch what you do not know exists; this is why disclosure is a part of the definition. However, you can reduce the impact of what you cannot patch or threats that have not been disclosed through cybersecurity best practices:
- Least Privilege: Limits what exploit code or malware can interact with at the operating system and application level.
- Segmentation: Prevents lateral movement after an initial exploitation.
- Identity Controls: Limits the ability of an attacker to impersonate legitimate users.
These aren’t just theoretical mitigations, they are the difference between a contained incident and a systemic failure when a zero day is truly exploited in an environment. Getting the definition right also forces honesty in post-incident analysis. These questions are uncomfortable, but necessary if organizations want to mature, rather than just repeat misunderstood terms:
- Was the vulnerability truly unknown at the time of exploitation, or was it known but deprioritized?
- Was exploitation confirmed, or merely assumed?
- Was the absence of a patch the root cause, or was it the absence of compensating controls?
Clarity is a defensive capability
We must be disciplined. Reserve the term “zero day” for what it actually is—a vulnerability unknown to the vendor and organizations alike, actively exploited, with zero days to patch because remediation simply doesn’t exist yet. Every other state has its own name and terminology: known vulnerability, unpatched vulnerability, misconfiguration, excessive privileges, or advanced persistent threat. These may sound less dramatic, but they are far more accurate when establishing the state of a threat.
In cybersecurity, clarity is a defensive capability. Threat actors thrive on confusion, obfuscation, whether technical, operational, or linguistic. If we cannot accurately define our threats, we cannot prioritize them intelligently and efficiently communicate the results to stakeholders. If we react loudly to the wrong things, we will inevitably ignore the risks that matter most. The definition of a zero day is not a semantic exercise. It is the line between sensationalism and effective prioritization.
Source: BeyondTrust
A new report claims that the cost of insider security incidents has surged 20% in two years, reaching an average of US $19.5 million per organization annually, with no sign that the alarming figure is flattening.
That is one of the findings of the “Cost of Insider Risks Global Report” for 2026 from the Ponemon Institute and DTEX, which claimed that the main culprit is not malicious employees.
According to the study, which polled 8,750 IT practitioners at 354 organizations that had experienced one or more material insider-related incidents, the average annual cost of insider risk security incidents was US $16.2 million in 2023, rising to $17.4 million, and now $19.5 million.
On average, each company suffered 25 such incidents per year.
Of the 7,490 incidents reported from the study group in 2025, 53% were caused by negligent or mistaken employees. In other words, ordinary people make ordinary mistakes.
As Infosecurity reports, that category alone accounts for US $10.3 million of the average annual loss for each company, up 17% year-on-year.
Malicious insiders, by comparison, are costing US $4.7 million per year according to the report.
The difference in the figures is easy to explain: negligence is far more frequent than malice.
According to the report, shadow AI is the fastest-growing reason for this insider negligence. Workers across industries are sharing internal documents, source code, legal materials, and strategy plans with AI tools without approval or proper safeguards.
Meanwhile, AI-powered meeting assistants are generating records of sensitive internal discussions and sometimes leaving them publicly accessible.
The driver for this appears to be well-intentioned employees attempting to get more work done at speed, unaware that they may be exposing company secrets.
The study reports that some 92% of organizations acknowledge that AI has fundamentally changed how their staff handles information, and yet only 18% have formally integrated AI governance into their insider risk programs.
The good news is that investment is improving response times. As insider risk budgets have grown from 8.2% of IT security spend in 2023 to 19% in 2025, the average time to contain a breach (stopping or limiting damage once an insider incident has been identified) has decreased from 86 days to 67 days.
That, of course, is still far from ideal. The report notes that incidents resolved within 30 days average US $14.2 million per year, while those that drag past 90 days average US $21.9 million. Currently, only 13% of incidents are contained within 30 days.
With costs rising 20% in two years and the shadow AI problem still largely being poorly governed (if governed at all), the gap between organizations with mature programs and those without is only going to get wider.
Source: Fortra
Sophos Firewall v22 bolstered Secure by Design, taking it to a whole new level with major updates to the architecture and new features like the Health Check to help identify high-risk configurations.
Sophos Firewall v22 MR1 adds several enhancements, including additional Secure by Design capabilities along with a new set of NDR detections for active threats – significantly enhancing both the proactive protection of Sophos Firewall as well as Detection and Response capabilities to identify and stop active threats.
Secure by Design
Sophos Firewall v22 introduced a new Sophos XDR Linux sensor as part of our Secure by Design initiative to enable better telemetry gathering for our proactive monitoring to detect elements such as file tampering.
MR1 extends this sensor’s detection capabilities to include compromises resulting from interactive or reverse shell access and blocks related TCP or UDP command and control activity, and it is now integrated across the full XGS Series lineup.
Detection and response: NDR Active Threat Intelligence
Sophos Firewall v22 MR1 also introduces iSensor IPS technology from the SecureWorks Taegis platform. This new NDR Active Threat Intelligence provides additional curated IPS detection patterns to help identify malicious traffic and active adversaries operating on the network, enabling more effective investigations for XDR and MDR analysts.
Enable these new NDR Active Threat Intelligence detections in the Active threat response > NDR tab (screen shot below) and then add the detections to your firewall rules by checking the box next to the IPS settings in each rule.
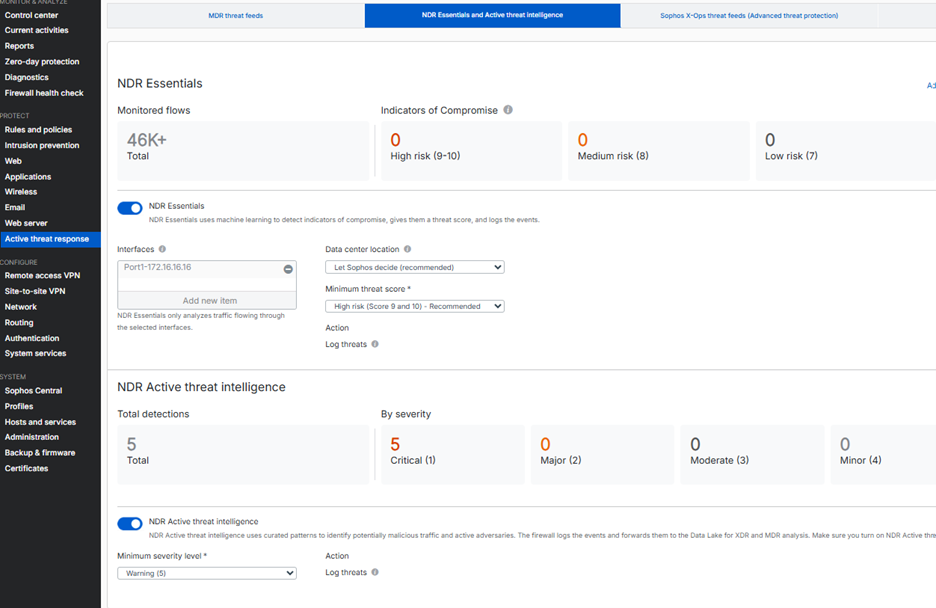
Here are some other notable MR1 enhancements.
NDR Essentials now available on all Sophos Firewall platforms
- NDR Essentials now supports all Sophos Firewall platforms, including virtual, cloud, and software, in addition to all XGS Series supported at launch.
Audit and compliance enhancements
- For configuration changes made to a single firewall through Sophos Central, the Sophos Central user identity is logged. This provides audit traceability and supports NIS2 and similar compliance requirements. The audit information is available in the Sophos Firewall log viewer and in Sophos Central logs and reports.
VPN improvements
- VPN stability fixes: Resolved policy-based IPsec VPN issues identified in SFOS 22.0 GA, including fixes for NC-177450, NC-174800, NC-177136, NC-174304, NC-172504, NC-173054, and NC-176083.
- Remote access IPsec (legacy): Legacy remote access IPsec VPN has been retired and is no longer supported. You won’t be able to upgrade firewalls using this legacy configuration to SFOS 22.0 MR1 and later. If you are still using this legacy IPsec VPN, take action as outlined in this KB article: Retirement of the legacy IPsec remote access VPN in SFOS 22.0 MR1.
- Sophos Connect: You can now establish remote access SSL VPN connections on macOS devices using Sophos Connect 2.0 for macOS. Sophos Connect release notes.
Storage and network enhancements
- Optimized SSD usage and write operations to improve SSD lifespan for long-term use.
- Support for updating the MTU and MSS values of Wi-Fi interfaces using existing CLI commands.
Sophos Firewall Config Studio V2
(Formerly known as Sophos Firewall Configuration Viewer)
Sophos Firewall Config Studio is the latest version of our very popular browser-based tool, which simplifies viewing, comparing, and now editing firewall configurations.
- Configuration report: View all rules, policies, and settings in a single configuration report.
- Compare configurations: Compare two configurations and identify added, removed, modified, and unchanged items.
- Configuration editor: Add configurations directly or import firewall configurations and edit them in the tool. Download the configurations and import them into the firewall or copy them in API or curl formats for use with these methods.
Access it here: Sophos Firewall Config Studio.
Updated CIS benchmark for v22
We are also pleased to announce that the CIS benchmarks used as a basis for security configuration best practices by the Sophos Health Check feature introduced in v22 have been updated and are available to download on the CIS website.
Release notes
Check out the full release notes for more details and a list of fixes.
Keep your firmware up to date
It’s extremely important to ensure your firewall firmware is kept date as every release integrates important security and stability fixes. Since all firmware updates are free for licensed Sophos Firewall customers with a valid support license (included with the Xstream Protection bundle), there’s no reason not to take advantage of all the great enhancements in every release.
Source: Sophos
Secure by Design is a software development philosophy that treats security as a foundational requirement rather than an afterthought.
Instead of building a product first and bolting on security fixes later, Secure by Design demands that security considerations are embedded into every stage of the development lifecycle — from architecture and design through coding, testing, deployment, and maintenance.
The core idea is straightforward: If you build something securely from the ground up, your users are protected by default rather than only when they know how to flip the right settings or when security gaps are fixed after the fact.
In practical terms, this means adopting several core security principles:
- Least privilege ensures that processes, agents — AI or otherwise — containers, and system services receive only the minimum access they need.
- Secure defaults make sure products ship with the safest configuration enabled out of the box.
- Defense in depth layers multiple security controls so no single failure becomes catastrophic.
And organizations can further strengthen resilience by eliminating entire classes of vulnerabilities through safer languages, frameworks, and design patterns.
Why was the Secure by Design approach introduced?
For decades, many players in the technology industry operated under a “ship fast, patch later” model. One consequence of that legacy is that cybersecurity can be seen as just a cost center — something that slows releases and frustrates developers. The impacts are playing out in real time: constant vulnerability disclosures, rushed emergency patches, and breaches that drain billions from organizations while exposing the personal data of hundreds of millions of people.
The Ivanti Connect Secure vulnerabilities, the Log4Shell exploit in a ubiquitous open-source library, and the MOVEit Transfer vulnerabilities all demonstrated that reactive security simply cannot keep pace with determined adversaries.
Recognizing this imbalance, the U.S. Cybersecurity and Infrastructure Security Agency (CISA) — together with international partners — published formal Secure by Design guidance in 2023, urging technology manufacturers to take ownership of their customers’ security outcomes.
Secure by Design principles argue that the burden of security should rest with the vendors who build technology products, not the end users who deploy them. This requires vendors to rethink how they prioritize speed and additional features, and to treat security as a core design requirement rather than a bolt-on enhancement. The shift moves the industry away from blaming users for failing to patch promptly and toward holding manufacturers accountable for shipping products that are secure from day one — even if that means slowing feature delivery or re‑engineering legacy approaches to reduce systemic risk.
Why Secure by Design matters most for cybersecurity solutions
It’s a striking reminder that even security tools can sometimes become the entry point for an attack. Yet it happens with alarming regularity.
This highlights a critical weakness for many organizations: Once a perimeter device is exposed, attackers will keep coming back to it repeatedly until it is fully secured. Firewalls and other edge systems can remain vulnerable even after a fix is available. Across all confirmed exploited vulnerabilities in recent analysis of incidents Sophos remediated, the median time between a vendor publishing an advisory or patch and an attacker exploiting that flaw was 322 days — almost a full year of opportunity for adversaries. Cybersecurity vendors can’t assume users are going to patch immediately.
The privileged position problem
Cybersecurity tools operate in the most sensitive and privileged parts of an organization’s infrastructure. Endpoint detection agents run with kernel-level access. SIEM platforms ingest logs from every system. Identity providers hold the keys to every account. Firewalls sit at the boundary between trusted and untrusted networks.
When security products sit at the heart of an organization’s defenses, they carry a heightened responsibility to follow Secure by Design principles. Vendors in our industry play a critical role in protecting customers, and that trust comes with expectations around how products are engineered.
This privileged position means that a vulnerability in a security product doesn’t just expose itself, it exposes everything it was designed to protect. An attacker who compromises an endpoint detection and response (EDR) agent doesn’t just own one tool — they own the endpoint with the highest privileges. A flaw in a VPN appliance doesn’t just break remote access, it hands an adversary a direct tunnel past every perimeter control.
What happens when Secure by Design is ignored?
The consequences of neglecting Secure by Design principles are well-documented and, if not followed properly, leave businesses, users, and the internet as a whole less safe.
- Escalating breach costs. When vulnerabilities are discovered post-release, fixing them is exponentially more expensive than addressing them during development.
- Erosion of trust. Customers, regulators, and partners lose confidence in organizations that suffer repeated security incidents. Reputation damage can outlast the technical remediation by years.
- Regulatory and legal exposure. Governments worldwide are tightening cybersecurity regulations. The European Union’s Cyber Resilience Act, for example, will impose mandatory security requirements on products with digital elements sold in Europe. Organizations that ignore Secure by Design principles risk non-compliance, fines, and market exclusion.
- National security risks. Critical infrastructure — power grids, water treatment, healthcare systems — increasingly relies on internet-connected devices and systems. Insecure-by-default products in these environments create openings for state-sponsored adversaries and ransomware operators, with potential consequences that could upend someone’s everyday life.
- Perpetual patch fatigue. Without secure foundations, organizations are trapped in a reactive loop: scanning for vulnerabilities, prioritizing patches, testing updates, and deploying fixes — repeatedly. This drains resources that could be spent on deeper cybersecurity investigations.
Sophos’ commitment to Secure By Design
On May 8, 2024, Sophos became one of the first organizations to commit to CISA’s Secure by Design initiative, which focuses on seven core pillars of technology and product security:
- Multi-factor authentication.
- Default passwords.
- Reducing entire classes of vulnerability.
- Security patches.
- Vulnerability disclosure policy.
- CVEs.
- Evidence of intrusions.
Aligned with our core organizational values around transparency, Secure by Design has been a guiding force as we continually evaluate and improve our security practices.
We published our pledges for improvement and publicly share the progress we are making against the seven core pillars of the Secure by Design framework. Of course, cybersecurity is constantly evolving and the job is never “done.” Continuing to refine and enhance the application of Secure by Design principles across our portfolio is an ongoing — and central — part of our ethos.
In just one example, the latest version (v22) of Sophos Firewall further extends the Secure by Design capabilities of the solution, including:
- A new Health Check feature to reduce the risk of a misconfiguration leading to a potential attack.
- An all-new containerized control plane re-architected for maximum security and scalability that eliminates a whole class of vulnerabilities.
- The addition of a Sophos XDR Linux Sensor enables real-time monitoring of the system integrity of our entire customer base by our own security teams to identify and respond to attacks more quickly.
- Firmware updates that are encrypted and certificate-pinned for authenticity.
Together, the changes in v22 and previously delivered capabilities in Sophos Firewall strengthen forensic visibility, logging, and protective monitoring. These enhancements also support closer alignment with many of the areas covered by the U.K.’s National Cyber Security Centre’s guidance for network devices.
Additionally, our work in the Pacific Rim campaign gave us a front‑row view into how determined, well‑resourced threat actors operate — and what it really takes to defend against them. The campaign reinforced that adversaries aren’t waiting for weaknesses to appear; they’re actively hunting for design shortcuts, configuration gaps, and unpatched systems across global infrastructure. That experience directly shaped our Secure by Design approach.
It underlined that modern defenses must start with reducing the attack surface at the product level, building in strong defaults, tightening authentication paths, and eliminating opportunities for misuse long before a vulnerability ever makes it into the wild.
The path forward
Secure by Design doesn’t eliminate all vulnerabilities, nor does it absolve organizations from ongoing vigilance. But it has become a fundamental foundation to cybersecurity for reducing the attack surface. The question is no longer whether Secure by Design is a good idea. It is how quickly it is adopted.
Source: Sophos
In our industry, trust isn’t an abstract concept. It’s the currency of cybersecurity – the foundation of every partnership we build and every protection we provide.
However, a recent independent, vendor-agnostic survey of 5,000 cybersecurity decision-makers across 17 countries reveals a stark reality: we’re facing a trust crisis.
According to our findings in Sophos’ Cybersecurity Trust Reality 2026 report, only 5% of respondents say that both they and their organization have full trust in their cybersecurity vendors.
That’s a number that should serve as a wake-up call for our entire industry.
The high cost of low trust
Assessing trust is inherently difficult. Our research shows that 79% of organizations find it challenging to assess the trustworthiness of new cybersecurity partners, and 62% struggle even with their existing vendors.
The consequences of this uncertainty are tangible. When trust is absent, anxiety fills the void.
We found that 51% of leaders believe a lack of trust leads to anxiety that their organization is more likely to experience a significant cyber incident. Furthermore, 45% say it increases their propensity to switch vendors, and 42% cite an increased requirement for oversight.
What actually drives trust?
To bridge this gap, we’ve got to understand what actually builds confidence. The survey identified the top drivers of trust for both IT teams and senior leadership, and the results were clear. It’s not about marketing claims, it’s about evidence.
- Verifiable artifacts: The number one driver of trust is the presence of verifiable artifacts indicative of cybersecurity maturity, such as an active bug bounty program, a Trust Center with security advisories, and third-party certifications.
- Transparency in crisis: The second most critical factor is transparency and timely communications during incidents and disclosures.
- Expertise and delivery: Following closely are expert commentary during major cyber events, the consistent delivery of high-quality services, and validation through analyst reports.
Our commitment to you
At Sophos, we understand that trust is built, not claimed. We’re committed to earning that trust through transparency, integrity, and a steadfast commitment to protecting your security and privacy.
We’ve aligned our operations directly with these drivers of trust:
Transparency by default: We believe in radical transparency. A prime example: our “Pacific Rim” research, where we provided a full, detailed disclosure of a five-year investigation into China-based threats targeting perimeter devices. We disclosed the timeline, the attack vectors, and exactly how we responded at every stage.
Verifiable maturity: We maintain a comprehensive Trust Center to provide you with the artifacts you need to assess our security posture. We also adhere to leading compliance standards, including ISO, SOC, and PCI DSS.
Secure by Design: We’ve outlined our progress and public commitments under CISA’s Secure by Design pledge, which focuses on seven core pillars including MFA, eliminating default passwords, reducing classes of vulnerabilities, and more. This initiative is an ongoing, industry-wide shift rather than a one-time effort, and we commit to providing regular, open updates on our progress and areas for improvement.
Trust is hard to earn and easy to lose. By prioritizing transparency, third-party validation, and consistent execution, we aim to ensure that when you partner with Sophos, you can do so with complete confidence.
I invite you to review the full findings of our research and visit our Trust Center to see exactly how we’re working to secure your world.
Source: Sophos
Fortra, a global cybersecurity software and services provider, announced today the acquisition of Zero-Point Security, a specialized cybersecurity training firm based in Warrington, UK. This will expand Fortra’s offensive security education capabilities, bringing additional expertise in red team operations, adversary emulation, and penetration testing training. Zero‑Point Security is widely recognized for its trusted red team operations training and has built a strong reputation delivering its high-demand, self-paced courses to individuals and businesses seeking advanced offensive operations skills.
“Becoming part of Fortra means we can expand the global reach of our training programs and introduce new opportunities to empower red teamers with practical, adversary-focused training,” said Daniel Duggan, Founder and Director of Zero-Point Security. “Working more closely with the Cobalt Strike, Outflank, and Core Impact teams, we’ll create programs that raise the standard for offensive security training worldwide.”
Zero-Point Security’s well-known courses include Red Team Operations I and II, both which meet the high standards to be certified by the Council of Registered Ethical Security Testers (CREST). Successful completion of these programs helps participants achieve Certified Red Team Operator (CRTO) status, an industry-respected credential that validates expertise in offensive security techniques.
“We have worked with Daniel and Zero-Point for years, collaborating on Cobalt Strike training and other initiatives. We’re excited to take this to the next level, putting more advanced Cobalt Strike Certified Operator trainings, Core Impact trainings, and training for Outflank Security Tooling on the roadmap for the near future,” said Pieter Ceelen, Cobalt Strike product owner and Outflank founder.
Fortra CEO Matthew Reck explained that the acquisition of Zero‑Point Security reflects Fortra’s commitment to advancing offensive security, a critical component of modern cyber resilience. Guided by Duggan’s expertise, he said, “Zero-Point Security will play a pivotal role in shaping an enhanced training portfolio, enabling Fortra to help organizations worldwide upskill their teams in adversary-focused techniques, and adopt a purple-team mindset for stronger, more complete protection.”
Source: Fortra
Organizations today operate under a substantial number of IT and cybersecurity compliance obligations. By defining requirements for areas such as access control, incident response, encryption, governance, and vendor management, compliance standards help reduce the likelihood and impact of cyberattacks, support regulatory and legal obligations, and build trust in digital ecosystems.
5,000 IT and cyber leaders share their compliance experiences
To shine a light on the IT and cybersecurity compliance reality facing organizations today, Sophos commissioned an independent survey of 5,000 IT and cybersecurity leaders across 17 countries and a broad range of public and private sector industries. Conducted in early 2026, key findings include:
- Multiple regulatory obligations: Respondents report adhering to 5 compliance standards on average (median), underscoring the breadth of regulatory obligations across regions and industries.
- Widespread non-compliance concerns: 82% of leaders are concerned that their organization may not be fully compliant with all necessary regulations and requirements, with almost a quarter (24%) very concerned. Just 18% report being unconcerned about their compliance status.
- Significant resourcing overhead: 39% of the IT and cybersecurity team’s time is spent on compliance-related activities.
- Difficulties keeping up: 79% of organizations find it challenging to keep with changes in compliance requirements, with 19% saying it is “very challenging.”
- Smaller businesses are disproportionately impacted: Smaller companies facing a similar volume of compliance frameworks as larger ones but with fewer resources and expertise to deliver them.
Industry and geography play a role
Across 17 countries in the Americas, EMEA and Asia Pacific and 15 different industries, the most cited regulations include:
- ISO 27001/2: 51.2% of respondents
- GDPR: 40.4% of respondents
- CIS: 29.7% of respondents
- NIST CSF: 23.8% of respondents
- PCI DSS: 23.1% of respondents
- HIPAA: 21.7% of respondents
- DORA: 19.8% of respondents
- NIS2: 16.1% of respondents
While these represent the most frequently cited standards overall, adoption varies significantly by industry and region.
For example, 66% of organizations in the distribution and transport sector cited ISO 27001/2, compared with 38% in state and local government. Similarly, 60% of businesses in Spain aim to comply with ISO 27001/2, compared with 35% in Mexico, and 30% of organizations in the U.S. comply with NIST CSF, compared to 13% in Australia.
Compliance today: Three key takeaways
The survey findings show that the compliance burden on organizations is high and maintaining compliance is an ongoing challenge. Key takeaways for IT and cybersecurity leaders include:
Compliance complexity is outpacing IT capacity
Maintaining compliance with one regulatory standard is tough, managing compliance across five is a huge task for any organization. Many frameworks require similar information, resulting in high levels of duplicative work for those involved. And with eight in 10 organizations (79%) finding it challenging to stay up to date with changes in compliance requirements, it’s clear that IT and cybersecurity teams are struggling to keep up.
Compliance has a major impact on resourcing
Compliance‑related activities can range from understanding regulatory requirements and implementing required controls, to reporting adherence status. With two fifths of the typical IT and cybersecurity team’s time dedicated to compliance efforts, it’s essential that organizations put in place the right level of resourcing to meet their compliance obligations and the wider IT and cybersecurity needs of the business.
Lack of visibility creates compliance and security blind spots
It’s not enough to think you are compliant — you need to know that you are. However, with 82% of IT and cybersecurity leaders concerned that they may not be fully compliant with all necessary regulations and requirements, it’s clear that teams are lacking the visibility they need to be sure of their compliance status. Without full visibility, organizations also run the risk of being blind to security and operational gaps that increase their risk of experiencing cyber incidents and data loss.
Maintaining ongoing compliance with multiple regulatory and compliance standards is a major undertaking for all organizations, and particularly for smaller businesses who are disproportionately impacted by the financial overhead of hiring in additional headcount to manage multiple, evolving regulations. With compliance requirements likely to grow in volume and complexity, organizations should consider how best to support their ongoing compliance obligations, including the possibility of working with external specialists who can provide expertise and resourcing support.
Source: Sophos
Sophos has been named a 2026 Gartner® Peer Insights™ Customers’ Choice in the 2026 Gartner® Peer Insights™ Voice of the Customer for Managed Detection and Response (MDR).
This marks our second Gartner Peer Insights Customers’ Choice distinction of 2026, coming off the heels of Sophos’ fifth consecutive Customers’ Choice for Endpoint Protection Platforms in January 2026. 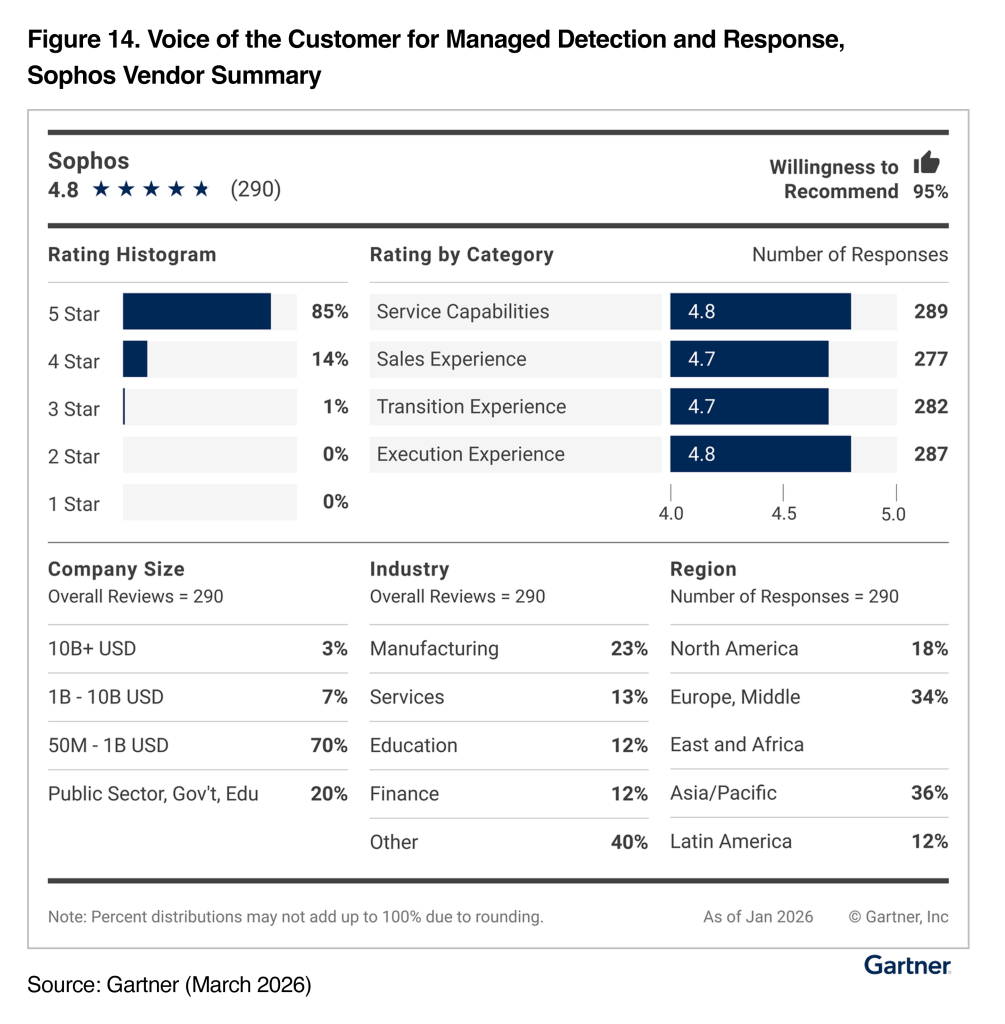
Since Gartner began generating Voice of the Customer (VoC) reports for the MDR category, Sophos has been recognized as a Customers’ Choice vendor in every iteration of the report. This recognition is based directly on customer feedback, and we’re truly thankful to our customers for taking the time to share their experiences.
In the 2026 VoC report for MDR, Sophos has an overall rating of 4.8 / 5.0 based on 290 reviews, making Sophos the most-reviewed vendor in the report. To go with this, customers rated Sophos with a 95% Willingness to Recommend score.
We believe these results reflect Sophos’ mission to deliver superior cybersecurity outcomes for our customers through powerful, comprehensive end-to-end solutions.
Recognition driven by real customer experiences
Gartner Peer Insights is a free peer review and ratings platform designed for enterprise software and services decision makers. We feel being named a Customers’ Choice reflects both high overall ratings and strong willingness to recommend, consistently validating Sophos’ commitment to customer success.
We are incredibly grateful to our customers worldwide for their continued trust and feedback, which directly contribute to shaping and improving Sophos’ solutions.
Here are some examples of what customers had to say about Sophos MDR:
“Our overall experience with Sophos MDR has been very positive. The team monitors our infrastructure 24×7 and alerts us to any malicious activity. This service is not only helping us to stay protected but also reducing the burden on our internal team.” –Cloud Support Engineer in the Software Industry (review link).
“Sophos MDR has dramatically reduced our cyber risk by cutting incident response times from days to hours. The 24x7x365 monitoring and remediation service has proven its worth multiple times, identifying and stopping active attacks before any damage can be done.” –IT Manager in the Manufacturing Industry (review link).
“The Sophos MDR service is an exceptionally great product altogether. It is extremely suitable in these tough times of cybersecurity issues which are growing and getting more and more complex.” –IT Manager in the IT Services Industry (review link).
“We have been using Sophos MDR to protect our organization’s endpoints and servers and it has been a game changer. Their team is constantly monitoring, quickly identifying issues and fixing them. They make my job easier.” -Manager of IT Services in the Government Industry, Gov’t/PS/ED (review link).
Source: Sophos
In everyday conversations, “AI and data security” tends to blur two big ideas together: using AI to strengthen traditional security measures and applying standard protections to the vast amounts of data organizations already manage. AI data security, however, tells a more focused story. It’s about safeguarding the data that fuels AI and machine learning (ML) itself. This would encompass the training data that shapes its intelligence, the inputs it analyzes in real time, and the outputs it generates. In other words, it’s not just about keeping data safe in an AI-enabled world; it’s about protecting the very lifeblood of AI systems.
AI for security = AI improving security tools and processes
AI data security = Protecting data used by and produced by AI systems
However, security has struggled to keep pace with the rapid integration of AI across business operations. Models are being deployed faster than security frameworks can adapt, often pulling from massive, sensitive datasets without adequate controls in place. This gap has widened the attack surface, increasing the risk of data exposure and enabling more sophisticated threats. When safeguards fall behind innovation, the consequences ripple outward, creating downstream risks that include compliance violations, loss of customer trust, compromised decision-making, and long-term damage to organizational resilience. AI’s promise is powerful, but without security evolving alongside it, that promise can quickly turn into liability.
How Is Data Used in AI?
Data is central to every stage of AI growth. During training and testing, AI models learn patterns and behaviors from large datasets, which may include structured internal data like business records as well as external data such as public text, images, or sensor inputs. Once deployed, AI systems continuously process new data to generate predictions, recommendations, or automated actions in real time. Over time, additional data is used to retrain and refine models, helping them adapt to changing conditions, improve accuracy, and bias.
Learn more about how: Your AI Model Might Not Be Worth Using – Without the Right Data Security in Place
Threats to AI Data
AI data faces a growing range of threats as models become more powerful and more widely deployed. Attackers may attempt data poisoning, model inversion, or adversarial attacks to manipulate training data, extract sensitive information, or distort model behavior, while automated malware uses AI itself to scale and adapt attacks faster than traditional defenses can respond. Risks also emerge from within, as rushed deployments, weak governance, and generative AI misuse can expose sensitive data through prompts, outputs, or unintended model behavior. Combined with privacy breaches, compliance violations, and prompt injection attacks, these threats highlight why securing AI data requires more than traditional controls. AI data demands safeguards designed specifically for how AI systems learn, operate, and evolve.
Data Security Use Cases with Fortra
Fortra’s platform is a way to layer multiple data security controls, including file transfer protection, classification, encryption, email security, DLP tuning, secure collaboration, and cross‑network transfer controls. These solutions address real‑world risks like ransomware, data leakage, and compliance violations. Here are a few ways Fortra protects your data:
- Add security layers to file transfers (managed file transfer with malware scanning, redaction, and blocking of sensitive files).
- Protect and control files wherever they travel, so policies and protections follow the data, not just the device or network.
- Label, protect, and encrypt data wherever it goes using classification plus encryption and access controls.
- Send outbound emails securely, reducing the chance of sending sensitive data to the wrong people or in the wrong format.
- Improve DLP accuracy and cut false positives by enriching DLP with better classification and policy context.
- Share files only with authorized users and prevent further sharing, even in cloud collaboration environments.
- Move large, sensitive files between secure networks while checking for both data exfiltration and incoming threats.
How Are AI Models Secured?
Securing AI model training and deployed AI models requires a security‑by‑design approach that protects data at every AI stage. During training, strong posture management, encrypted data storage, and a secure AI SDLC help reduce risk from the outset. Once models are deployed, input and output validation, continuous monitoring, adversarial training, and red‑team testing are essential for detecting manipulation and misuse. Cross‑functional governance ensures these AI data security best practices remain effective as models evolve, scale, and integrate into business operations.
AI Data Security Best Practices
Regulatory compliance and ethical AI use are tightly connected, especially as AI systems increasingly handle sensitive personal data governed by laws like GDPR and CCPA. As users share more personal and confidential information with AI tools, protecting that data becomes critical — not only to meet regulatory requirements, but to maintain trust and prevent misuse. At the same time, the data an AI model is trained on and prompted with directly influences how it behaves, making strong data governance essential for ensuring AI outcomes remain fair, compliant, and ethical.
The Security of AI
AI data security is about protecting the data used by and generated from AI systems, not just using AI to improve traditional security. AI relies on data throughout its lifecycle making that data a high‑value target for attackers and growing threats such as data poisoning, model inversion, prompt injection, generative AI misuse, and AI‑powered cyberattacks. It is imperative that securing both AI model training and deployed models through practices like posture management, encryption, continuous monitoring, adversarial testing, and cross‑functional governance are implemented.
Source: Fortra