News
In everyday conversations, “AI and data security” tends to blur two big ideas together: using AI to strengthen traditional security measures and applying standard protections to the vast amounts of data organizations already manage. AI data security, however, tells a more focused story. It’s about safeguarding the data that fuels AI and machine learning (ML) itself. This would encompass the training data that shapes its intelligence, the inputs it analyzes in real time, and the outputs it generates. In other words, it’s not just about keeping data safe in an AI-enabled world; it’s about protecting the very lifeblood of AI systems.
AI for security = AI improving security tools and processes
AI data security = Protecting data used by and produced by AI systems
However, security has struggled to keep pace with the rapid integration of AI across business operations. Models are being deployed faster than security frameworks can adapt, often pulling from massive, sensitive datasets without adequate controls in place. This gap has widened the attack surface, increasing the risk of data exposure and enabling more sophisticated threats. When safeguards fall behind innovation, the consequences ripple outward, creating downstream risks that include compliance violations, loss of customer trust, compromised decision-making, and long-term damage to organizational resilience. AI’s promise is powerful, but without security evolving alongside it, that promise can quickly turn into liability.
How Is Data Used in AI?
Data is central to every stage of AI growth. During training and testing, AI models learn patterns and behaviors from large datasets, which may include structured internal data like business records as well as external data such as public text, images, or sensor inputs. Once deployed, AI systems continuously process new data to generate predictions, recommendations, or automated actions in real time. Over time, additional data is used to retrain and refine models, helping them adapt to changing conditions, improve accuracy, and bias.
Learn more about how: Your AI Model Might Not Be Worth Using – Without the Right Data Security in Place
Threats to AI Data
AI data faces a growing range of threats as models become more powerful and more widely deployed. Attackers may attempt data poisoning, model inversion, or adversarial attacks to manipulate training data, extract sensitive information, or distort model behavior, while automated malware uses AI itself to scale and adapt attacks faster than traditional defenses can respond. Risks also emerge from within, as rushed deployments, weak governance, and generative AI misuse can expose sensitive data through prompts, outputs, or unintended model behavior. Combined with privacy breaches, compliance violations, and prompt injection attacks, these threats highlight why securing AI data requires more than traditional controls. AI data demands safeguards designed specifically for how AI systems learn, operate, and evolve.
Data Security Use Cases with Fortra
Fortra’s platform is a way to layer multiple data security controls, including file transfer protection, classification, encryption, email security, DLP tuning, secure collaboration, and cross‑network transfer controls. These solutions address real‑world risks like ransomware, data leakage, and compliance violations. Here are a few ways Fortra protects your data:
- Add security layers to file transfers (managed file transfer with malware scanning, redaction, and blocking of sensitive files).
- Protect and control files wherever they travel, so policies and protections follow the data, not just the device or network.
- Label, protect, and encrypt data wherever it goes using classification plus encryption and access controls.
- Send outbound emails securely, reducing the chance of sending sensitive data to the wrong people or in the wrong format.
- Improve DLP accuracy and cut false positives by enriching DLP with better classification and policy context.
- Share files only with authorized users and prevent further sharing, even in cloud collaboration environments.
- Move large, sensitive files between secure networks while checking for both data exfiltration and incoming threats.
How Are AI Models Secured?
Securing AI model training and deployed AI models requires a security‑by‑design approach that protects data at every AI stage. During training, strong posture management, encrypted data storage, and a secure AI SDLC help reduce risk from the outset. Once models are deployed, input and output validation, continuous monitoring, adversarial training, and red‑team testing are essential for detecting manipulation and misuse. Cross‑functional governance ensures these AI data security best practices remain effective as models evolve, scale, and integrate into business operations.
AI Data Security Best Practices
Regulatory compliance and ethical AI use are tightly connected, especially as AI systems increasingly handle sensitive personal data governed by laws like GDPR and CCPA. As users share more personal and confidential information with AI tools, protecting that data becomes critical — not only to meet regulatory requirements, but to maintain trust and prevent misuse. At the same time, the data an AI model is trained on and prompted with directly influences how it behaves, making strong data governance essential for ensuring AI outcomes remain fair, compliant, and ethical.
The Security of AI
AI data security is about protecting the data used by and generated from AI systems, not just using AI to improve traditional security. AI relies on data throughout its lifecycle making that data a high‑value target for attackers and growing threats such as data poisoning, model inversion, prompt injection, generative AI misuse, and AI‑powered cyberattacks. It is imperative that securing both AI model training and deployed models through practices like posture management, encryption, continuous monitoring, adversarial testing, and cross‑functional governance are implemented.
Source: Fortra
AI now plays a key role in today’s organizations, and with its adoption comes the clear need for dedicated AI security solutions. In fact, securing AI agents is a top-five priority for 93% of organizations today.
This urgency comes as it becomes more common for teams to run agentic AI workloads for analyzing data, making decisions, and taking actions inside critical systems. But the moment an AI agent acts for you, it stops just being software and becomes an identity. And like any identity, if it has too much privileged access or weakly protected secrets, attackers can use it as a shortcut into your environment.
Why Agentic AI Changes the Security Risk
AI agents do far more than provide answers. They can retrieve records, call APIs, spin up cloud resources, apply code updates, or move data between systems. This is automation with real agency and authority attached, as an agent may apply reason and take action to reach a goal, even if it is an unintended action from the user’s point of view. This is why closing the agentic AI security gap requires organizations to manage AI agent access as if they were human, going far beyond traditional perimeter defenses. Since AI workloads can run as non-human identities in cloud infrastructure and hold IAM roles, API keys, and service credentials at scale, adequately securing them requires a strategy that treats every workload as a privileged identity.
Whether your company chooses to use AWS Bedrock agents, Azure AI / OpenAI workloads, Salesforce Agentforce, ServiceNow, or even custom agentic pipelines, every agent must be identified, inventoried, risk scored, and analyzed for unintended privilege escalation. Understanding potential blast radius is critical to AI Security Posture Management.
Another key point is that many AI agents execute locally in privileged environments, like developer workstations, and therefore inherit the privileges of the user running them. This means these non-human identities (NHIs) operate within the exact same operating system privilege model as any other process, but dramatically increase NHI risk if endpoints are over-permissioned. This is why enforcing least privilege on endpoints becomes the critical control for safely containing AI-driven automation.
BeyondTrust approaches agentic AI security as an identity problem, but identity alone doesn’t create risk. Privilege does. That’s why we emphasize a privilege-centric approach that finds, controls, and protects Paths to Privilege™ across all human, non-human, and agentic AI identities.
Enabling AI Governance
Agentic AI adoption is expanding rapidly.
Altogether, this explosion of agentic AI shows just how critical it is to govern AI agent identities and prevent shadow AI, unmanaged models, and agents operating with excessive permissions. Agentic AI workloads often create a blind spot in the identity fabric, where the relationships between users, data, and autonomous processes are obscured through misconfigurations or account inclusion in nested groups
BeyondTrust Identity Security Insights® and Password Safe® close this gap by providing deep identity intelligence across the entire environment. For IT and security executives, this means:
- Agentic Workload Discovery: Automatically identifying the AI agents and service accounts that are interacting with your infrastructure.
- Identity Posture and Privilege Graphing: Identifying overprivileged agentic workloads and misconfigured IAM roles via our identity privilege graph, mapping True Privilege™ and blast radius across cloud environments.
- Securing AI Credentials: Rotating and providing lifecycle management to the secrets and credentials agentic workloads need to operate.
By consolidating this intelligence and protection, CISOs and other executives gain the clarity needed to make risk-informed decisions, helping ensure that AI deployment doesn’t come at the cost of compliance or security posture.
AI Observability and Intelligence – How BeyondTrust Identity Security Insights Helps You Understand AI Privilege Risk
One of today’s most daunting security challenges is that most organizations cannot clearly see where their AI agents are running, nor what they can do. BeyondTrust’s Identity Security Insights solution helps close this gap by providing the observability needed to govern AI identities as rigorously as human ones.
The BeyondTrust solution identifies non-human identities, including AI, across cloud, SaaS, and internal deployments. It helps teams understand which agents exist, what systems they touch, and whether their permissions match their intended purpose. Using True Privilege™ graphs and identity security intelligence, you can quickly understand and prioritize based on real-world risk. With this information, you can start to reduce unnecessary access and shrink the blast radius before something goes wrong.
Identity Security Insights also goes beyond just enumerating entitlements—it maps the effective power of each identity. Cloud and SaaS roles often hide complex inheritance chains that create unintended access paths. Our product highlights these hidden escalation paths so you can cut back standing access, prevent undesirable elevation of privilege, and ensure agents only have the privileges they need.
Identity Security Insights is part of the BeyondTrust Pathfinder platform approach to privilege-centric identity security, helping teams understand True Privilege: what any identity can actually do in practice, including hidden, inherited, and cross-system access relationships.
On top of that, Identity Security Insights provides actionable remediation guidance, with dozens of AI-specific posture recommendations. You can right-size permissions, break inheritance loops, and apply just in time access where appropriate.
The goal is simple: every AI agent should operate with the minimum required access and without dormant privileges that could be misused.
Protection – Securing the Secrets Behind AI Workloads with Password Safe
Most AI workloads rely on a set of sensitive secrets, just like a human user. These include API keys, access tokens, database passwords, cloud credentials, and service account keys. Frequently, these secrets end up embedded in code, configuration files, logs, or CI/CD pipelines. But all too often, temporary workarounds become permanent solutions, making them one of the easiest targets for attackers.
How Do You Secure AI Agents with Password Safe?
Password Safe centralizes and protects these secrets so your AI workloads don’t become an attacker’s easiest entry point. It provides a secure vault for storing all credentials used by human users and AI agents. Instead of leaving secrets scattered across the environment, they are stored in a single protected location with strict access control.
Password Safe also automates credential rotation. AI workloads are highly dynamic, so manual rotation is unrealistic and unsafe. Auto-rotation helps ensure secrets never remain valid longer than necessary.
For high-risk operations, Password Safe can integrate with ticketing systems and issue credentials only when needed and revoke them immediately after. This removes the problem of long-lived or unused secrets just waiting to be stolen.
Password Safe also provides robust monitoring and auditing. Every time an AI workload uses privileged access, the activity is logged. This is essential for detecting abnormal behavior and for post-incident analysis.
Securing AI as part of a Complete Identity Security Approach
Securing AI is not about stifling innovation and limiting value; it’s about putting the right identity controls in place so you can adopt AI safely and confidently to maximize value.
A key part of scaling agentic AI security is applying the principle of least privilege to AI agents, just as you would for privileged human administrators. Adopting new technology should not mean blindly accepting risks.
BeyondTrust Identity Security Insights gives you the visibility and intelligence to understand what AI agents exist, what they can really do, and how to reduce their standing privileges. Our Password Safe product ensures the secrets behind those agents are protected, rotated, and monitored.
When combined, the result is a secure foundation where AI workloads can operate with least privilege, minimal blast radius, and properly governed access. This maximizes the benefits of AI without increasing the identity attack surface.
Source: BeyondTrust
Many organisations take a phased approach to deploying password managers, starting with IT and security teams and planning to expand later. This approach is often shaped by practical constraints such as budgets, licensing and the need to balance competing priorities.
Partial cybersecurity coverage leaves organisations exposed to breach paths that are actively exploited. When only part of the workforce is protected, compromised credentials, shared access and unmanaged accounts become easy entry points for external attackers, malicious insiders and third-party misuse.
Teams under pressure create workarounds to keep business moving, such as sharing credentials insecurely, retaining admin rights longer than necessary or spinning up unmanaged tools and accounts. These practices increase the likelihood of credential theft, privilege escalation and lateral movement, which are common stages in modern breaches.
These situations don’t happen because security policies are ignored. They happen because security controls haven’t yet scaled to reflect how access is actually used across the organisation. Until coverage is complete, attackers can exploit inconsistencies, turning temporary gaps into breaches with lasting impact.
The downfall of partial password security coverage
Partial password coverage doesn’t reduce risk — it merely shifts it. Attackers bypass well-defended user accounts and target unmanaged or weakly governed privileged access instead. From an attacker’s perspective, areas of an organisation’s architecture that are unmanaged or only partially managed are far easier to exploit than tightly controlled administrator accounts. Without complete visibility, elevated access can quietly become the most direct path to broader system compromise.
Partial coverage helps organisations get started, but it doesn’t go far enough. Password management protects individual users, while privileged access across shared systems, infrastructure and cloud environments requires a higher level of control.
This is where KeeperPAM® becomes the natural next step. Privileged access requires more advanced controls, such as managing shared administrator accounts, enforcing time-bound access and maintaining clear audit records. Capabilities like Just-in-Time access (JIT), session recording and centralised visibility become increasingly important as environments grow.
By extending visibility across infrastructure, applications and cloud environments, KeeperPAM helps organisations close the gaps that often appear as password management programs mature.
A scalable way forward
As organisations mature, early decisions around access controls need to be revisited. Many teams are moving away from evaluating fragmented tools and toward treating identity security as a connected system. They are choosing one platform that can scale over time without adding unnecessary cost or operational complexity.
Keeper is designed to support the natural progression that comes with business growth across any industry. Keeper Enterprise Password Manager makes it easier to extend credential protection beyond IT, enabling organisations to broaden coverage while keeping deployment seamless and license provisioning straightforward. From there, KeeperPAM builds naturally on that foundation, securing privileged access to servers, databases and cloud environments without relying on shared administrator credentials.
Because KeeperPAM operates on the same zero-trust security platform, organisations can extend privileged access controls without rearchitecting their security stack or adding new infrastructure. Teams can start quickly and scale at their own pace, rolling out role-based access, session visibility and audit-ready reporting in line with phased deployments and budget requirements. By unifying password management and privileged access management, organisations close critical gaps, reduce reliance on shared credentials and strengthen audit readiness without adding complexity.
In identity security, progress doesn’t have to mean compromise. With the right foundation, organisations can evolve their programs in a way that balances cost, coverage and risk. Consolidating the tech stack and moving toward a single platform to secure credentials, secrets, connections and endpoints enables faster organisation-wide deployment and provides access to all cybersecurity tools in one unified vault.
Source: Keeper Security
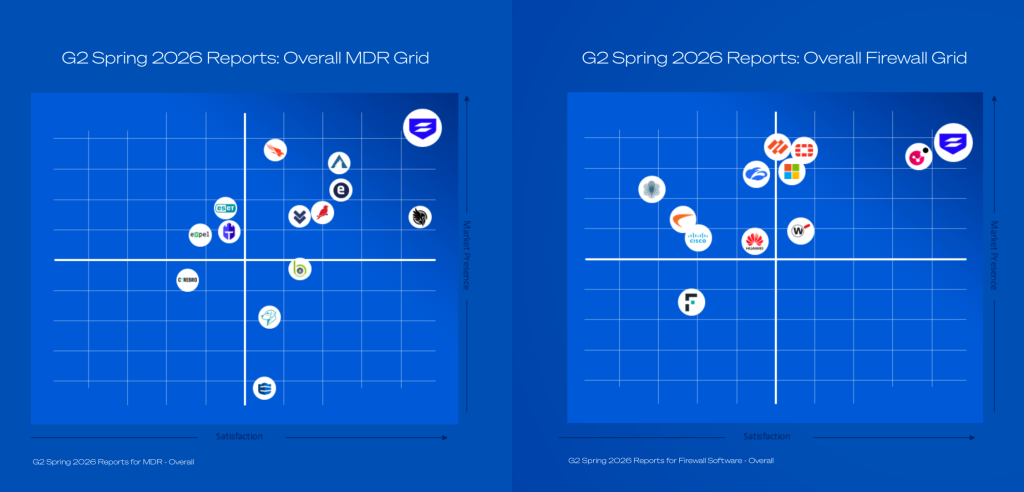
G2 has published its Spring 2026 Reports, and customers once again ranked Sophos as a top security vendor.
Sophos is ranked as the #1 Overall solution in Endpoint Protection Platforms (EPP), Managed Detection and Response (MDR), Extended Detection and Response (XDR), Endpoint Detection and Response (EDR), and Firewall Software.
Speaking to the power of our platform, Sophos is named as a Leader for the 15th consecutive time across every G2 Overall Grid® that defines modern security operations: Endpoint Protection Platforms, Endpoint Detection and Response (EDR), Extended Detection and Response (XDR), Firewall Software, and Managed Detection and Response (MDR).
These recognitions come from verified peer review and reflect what security teams value most: faster time to outcome, simpler operations, and the confidence of a platform that scales from prevention to managed response.
Managed Detection and Response
In addition to being the #1 Overall ranked MDR solution, Sophos MDR was named the #1 solution among the Enterprise and Mid-Market customer segments. Sophos MDR also earned the Best Results and Best Usability distinctions among both Enterprise and Mid-Market customers.
Endpoint
The Spring 2026 Reports marks the first time Sophos Endpoint was recognized as the #1 Overall solution across EPP, EDR, and XDR. In total, Sophos Endpoint was ranked #1 in 37 total reports across these 3 categories. The Sophos XDR platform earned the Best Usability, Best Results, Best Relationship, and Most Implementable distinctions – a testament to its industry-leading security outcomes and customer experience.
Firewall
The G2 Spring 2026 Reports marks Sophos Firewall’s 13th consecutive #1 Overall Firewall ranking. It’s also the third consecutive G2 Seasonal Report where all customer segments (Enterprise, Mid-Market and Small Business users) rated Sophos Firewall as the #1 solution. Sophos Firewall also earned the Overall Best Results, Best Usability, Best Relationship, and Most Implementable badges.
What Sophos customers are saying
“One of the most trustworthy endpoint security products” said a user in the Mid-Market segment.
“I like Sophos endpoint for its strong real time protection ransomware defense and centralized management through Sophos central” said a user in the Small Business segment.
“Total peace of mind with Sophos MDR: 24/7 security and clear alerts” said an Infrastructure Security Analyst in the Mid-Market segment.
“[Sophos MDR’s] 24/7 security coverage provides continuous monitoring and alerts us promptly to any suspicious activity, ensuring our network’s safety and allowing us to track and resolve issues efficiently” said a user in the Mid-Market segment.
“The advanced threat protection features like Intrusion Prevention, Web Filtering, and Sandstorm make Sophos Firewall a powerful tool against both known and unknown threats” said an IT Infrastructure Manager in the Mid-Market segment.
“What I like best about Sophos Firewall is its strong security features combined with an easy-to-use interface, making it simple to manage threats, monitor traffic, and protect the network without complex configuration” said a System Security Administrator in the Mid-Market segment.
For more information on our services and products, speak to your Sophos partner or representative and visit our website.
Source: Sophos
The start of a new year is always a good time to take stock. In cybersecurity, one perennial problem – the persistence of “vintage” open source vulnerabilities like Heartbleed and Shellshock – should force us to ask some hard questions. Why do so many vulnerabilities persist in Open Source (OS) tools, and how do we fix the problem?
In theory, OS tools should be more secure. In practice, it hasn’t worked out that way. The question is what needs to change to address this problem and reduce its impact on the ecosystem?
How Did We Let This Happen?
When OS tools and libraries first developed, many people thought that the resulting software would be more secure than proprietary products, thanks to the wisdom of crowds. The theory was, with so many eyes on it, how could we miss anything glaring?
In turns out, though, that the theory had a fatal flaw with respect to OS software. The crowds aren’t watching. No one is incentivized to look for flaws in OS software to fix them for the good of everyone.
Despite our idealistic dreams about the general public watching for OS flaws, the only people really incentivized to scan codebases for vulnerabilities were the attackers. And even when OS tools are fixed and libraries updated, few developers update their links to point towards the latest libraries, so we still have things like Heartbleed running around.
As a result, there are just as many OS vulnerabilities now as there were ten years ago (even major ones), and little has changed in the ecosystem despite noteworthy vulnerabilities and significant attacks.
When something is everybody’s business, it’s often nobody’s business. The question is how can we make OS vulnerability management somebody’s business?
Pass the Potato
Of course, this problem is not unique. Other activities suffer from similar problems and over time societies have developed a few different strategies for addressing them. Government would be one classic solution, but for-profit associations or non-profit organizations are also viable options.
Public Sector: Governments
Whenever market failures exist, government action is a viable option. In this case, governments have some strong incentives to address the problem.
Argument 1: Keeping Money in the Economy
First, despite the headline-making news of nation-state attacks, cybercrime is the cybersecurity problem affecting most citizens. It impacts constituents on a personal level (think phone scams, phishing emails, BEC attacks) and siphons money out of economies that could be used elsewhere. According to the latest FBI IC3 report, BEC alone cost companies billions of dollars a year. That’s a lot of corporate and taxpayer dollars.
Strengthening the cyber resilience of the underlying ecosystem to reduce OS vulnerabilities in the first place would keep money in citizens’ pockets, not attacker’s pocketbooks. Investing money in an OS vulnerability reduction initiative dedicated to finding bugs would be nominal compared to what most governments are now spending in AI advancement.
And think about it: many fast-and-loose (and even some reputable) AI companies use OS tools like candy. How much smarter would it be to ensure those investments stay safer upstream?
Argument 2: Safety of Citizens and Critical Infrastructure
When we consider public safety and the security of critical infrastructure, the argument gets even stronger. Nation-state operators often use vulnerabilities in OS code that integrates with critical infrastructure through third parties. Preventing disruption in public services and maintaining public safety definitely falls within the government’s remit.
Corporate Associations
Although governments have an incentive to reduce OS vulnerabilities, private sector companies also have reasons to address this issue. Given their coding practices, large tech companies have a vested interest in more secure upstream code. Further, many employees at these companies help create OS code. For example, Microsoft’s employees contribute more OS code than any other company.
Getting one company to commit resources to fixing OS vulnerabilities would face a lot of challenges. For one thing, a single company would be worried about others “free riding” on their work; for another, many in the OS community would not trust a single company’s motives. For these reasons, if we want large tech companies to take the lead in reducing OS vulnerabilities, the sector would need to create an independent trade association dedicated to this issue or have an existing association take on this mission.
Nonprofits
Another possible option would be a charitable nonprofit. These organizations sit between the public and private sectors, can serve as neutral ground, and, if structured properly, are free from other conflicts of interest. A dedicated nonprofit would fit well with the OS community ethos, and several models already exist. The key challenge for nonprofits is financing, so a dedicated funding model would need to be identified to make this option viable.
Making OS Security Somebody’s Business: Is It Us?
Despite all the could be’s and should be’s, most entities are not going to act unless they’ve got a personal interest. At the end of the day, the ones with the most at stake are the users. If manufacturers, retailers, defense contractors, public school systems, healthcare providers and so on raise their standards for OS code security, that change will drive changes in the ecosystem. When these players say, “we’re not accepting any OS code unless it meets these standards,” they are forcing contractors, third-party developers, and even their own internal teams to take responsibility.
Just as vulnerabilities will always exist in proprietary code, OS code will never be “bug free.” Some developers will always try to take shortcuts, and not all users will be thorough all the time. Nevertheless, we can structure the ecosystem to generate more secure OS code, while preserving the benefits that OS provides in the first place.
Source: Fortra
A recent IEEE global study revealed that 96% believe that the innovation, exploration and adoption of AI – specifically agentic AI – will continue at “lightning speed” in 2026.
What does that mean?
It means that with the cement still hardening on AI regulatory compliance and the necessary data center infrastructure to support it still five years out, we’d better learn to secure it, and fast.
AI may be the wheels on the bus that make it go round and round, but without understanding what those wheels can and cannot do by themselves, teams are in for unexpected surprises.
The Upside of Deploying Agentic AI
Agentic AI is AI taken to the next level; it can think, reason, and even act. That’s a far cry from read, summarize, and regurgitate. Agentic AI is what powers many truly time-saving AI implementations, like:
- Determining attack paths (cybersecurity)
- Autonomously resolving service issues (customer service)
- Sourcing and screening candidates (HR)
- Natural language prompt coding (“vibe coding”)
And other problem-solving, judgement-requiring tasks. It still keeps humans in the loop, but it learns from established patterns and draws connections to become better adept and self-sufficient over time.
This is wonderful for business. But it is also risky.
The Risks of Deploying Agentic AI
One doesn’t have to look far to realize the great potential, for good or ill, of an autonomous agent that can think and be only semi-controlled in your environment.
“Unlike traditional applications, agentic AI can behave in adaptive and unpredictable ways,” notes the Fortra FIRE team in its recent Secure AI Innovation guide. “Treating these systems as ‘just another app’ underestimates its capacity to evolve behavior based on feedback loops, data exposure, or experimental cues.”
Unleashing agentic AI into without the proper security controls could mean:
- It learns off the wrong behaviors if you’re not careful about its input
- It customizes itself and its responses to faulty data if that data isn’t sterilized
- It solidifies bad and experimental practices if not re-trained with the right ones
Ultimately, this comes down to the propagation of errors (bias), being subject to data poisoning, and producing unintended results due to tool misuse. You’re dealing with another entity that can “think”—it’s not static.
Similarly, as with a human junior analyst, you must ensure they’re well-trained. And prevented from doing anything dangerous.
Treating Agentic AI Like an Intern
Companies should already have policies in place to ensure that employees operate safely within their designated boundaries. Why? Because employees can act for themselves; they can’t be configured.
Agentic AI shares that similar quality. Unlike other technologies, you can’t just set it and forget it. It learns, it remembers, and it changes. That means it needs to be treated more like a human resource than a static addition to your security stack (or your CRM, HR services, or IT operations).
Fortra’s report notes that existing personnel policies like:
- Access control
- Performance oversight
- Task scope
Should be extended to agentic AI systems, and that additional ones should be added, like:
- Programmatic guardrails
- Robust logging
- Regular checkpoints
And human-in-the-loop reviews. Agentic AI might be helpful, but it’s too savvy to be trusted. To keep it in check, human reviews and audits are essential.
So, what does this look like in practice?
A Framework for AI Governance
Agentic AI has part-machine, part-human qualities. This means changing the way we govern this “technology” to include both the limitations you’d put on a free agent and the constant tune-ups you’d put on a machine.
This translates to:
- Formal Onboarding and Offboarding: Just like you’d create and secure an employee’s identity, so you create and secure the identity of every agentic AI agent. This means revoking privileges and access once it’s decommissioned.
- Continuous Security and Monitoring Protocols: Implement alert thresholds on your agentic AI agent, automate policy enforcement whenever possible, and avoid leaving any blind spots where it operates without your oversight. This means continuous monitoring and the ability to detect anomalies and respond promptly.
- DevOps Practices: Just as you would with any critical system, subject your AI agent to regular testing, version control, and output validation so results don’t deviate over time. Unlike true interns, it’s not in team meetings and can’t course correct without being told.
For the full list, download the guide.
Agentic AI: As Safe as You Make It
Agentic AI is set to revolutionize the way we do security and everything else. From how much time SOCs spend chasing down alerts to how fast retailers can answer complex customer queries, agentic AI will be infused into organizations at an unprecedented pace this coming year.
This is why, as the IEEE study notes, 44% list AI ethical practices as a “top skill” for AI-related hires in 2026. At the foundation of those ethics is the responsibility to operate safely, and without AI security, there is AI ethics.
As organizations realize the value of agentic AI for business and productivity, let’s not make the same mistake we’ve always made. Many may already be halfway in, but it’s not too late: if agentic AI adoption has outpaced AI governance in your organisation, now is the time to make a change.
Contrary to popular opinion, it will not have a net slowdown effect. Instead, implementing proper agentic AI policies now, at the start, will enable you to grow your AI initiatives with confidence and keep growing – while others stop to repair flat AI tyres along the way.
Source: Fortra
If 2024 was the year AI reshaped IT operations, 2025 was the year Autotask brought it all together.
From smarter billing and automated ticketing to a modernized interface designed for the way you work today, this year’s releases delivered some of Autotask’s most impactful improvements yet. And IT teams took notice, with top-tier recognition from G2, Capterra and Software Advice underscoring Autotask’s position as a leader in PSA software.
Here’s a look back at the innovations that made 2025 one of Autotask’s biggest years ever — and how they help teams save time, reduce friction and run more profitable, scalable IT services businesses.
A smarter way to manage client relationships: Umbrella Contracts
Managing multiple agreements for the same client has long been one of the most complex aspects of running an IT services business. In 2025, we changed that.
Umbrella Contracts, introduced in the 2025.5 release, give you one unified container for everything — managed services, time and materials, project work and more — so you can manage client agreements holistically instead of hunting across multiple contract screens.
Why customers love it
- One contract, total clarity: View every service, change and activity in one place. No more jumping between separate agreements.
- Cleaner billing with fewer errors: In-frame drawers, inline editing and advanced table filters turn contract management into a streamlined workflow, not a scavenger hunt.
- Roll out at your pace: Use Umbrella Contracts for new clients immediately while keeping existing agreements intact until you’re ready to migrate.
It’s simpler, more organized and reduces risk — which means more predictable billing and better client conversations.
A modern Autotask experience: The new UI arrives
Autotask’s biggest visual and usability transformation in more than a decade launched in 2025. Built on the Kaseya Design System, the new interface delivers a cleaner, more intuitive experience that reduces clicks, maintains context and helps technicians stay focused.
What changed
- Collapsible left navigation for more screen space and faster access
- Reorganized top navigation with simplified icons
- Improved search, with global search coming soon
- Refreshed dashboards with drag-and-drop widget resizing
- Updated Worklist panel to keep priorities front and center
The new UI eliminates friction and supports how modern service teams work. Whether you’re managing projects, reviewing tickets or billing clients, everything feels faster, clearer and more consistent across the entire IT Complete platform.
This refresh is just the first step — with more streamlined grids, inline editing, enhanced previews and bulk updates coming next.
Source: Datto
Security needs to be reevaluated in the context of AI, but not everything needs to change at once. Organizations that take a measured approach will do better, not giving into the AI hype cycle but recognizing the strategic ways AI is changing the game — and the ways it is changing security trajectories for the better.
AI is weakening defenses
AI-enabled attacks are increasing, weakening existing defenses in the process. Against this two-pronged offensive, current security tools are struggling to keep up.
We see AI leveraged to create highly believable deepfakes that lead to social engineering scams. ML tools are used to power chatbots that carry the ruse even further. AI generates code that can change mid-flight (AI-generated polymorphic malware), and instances of AI-powered password cracking and MFA evasion are becoming more prevalent.
As organizations realize that their current tools are insufficient, there is a tendency to buy into the AI trend where cybersecurity is concerned.
AI hype cycle vs. Data defense
If companies are not careful, they can believe that AI-infused security tools equal defense. But protecting sensitive data is the real litmus test, and if AI capabilities are introduced with careful consideration of data protection and access, there could be problems further down the line.
The consequence of introducing too much AI, too soon, is that AI expands the attack surface, can behave unexpectedly without proper guardrails (agentic AI, namely), consumes a lot of computational resources, and is expensive when applied on a large scale.
Michael Siegel, director of Cybersecurity at MIT Sloan, stated that “AI-powered cybersecurity tools alone will not suffice.” He argued that “a proactive, multi-layered approach — integrating human oversight, governance frameworks, AI-driven threat simulations, and real-time intelligence sharing — is critical.”
In other words, even though “fighting fire with fire” may be the buzzword against rising AI attacks, that fire needs to be used strategically.
Implementing AI securely for business
When organizations look to adopt AI, they often do it to get and stay ahead of the next business that is adopting AI.
When looking at the security of AI – that is, securing AI tools used in CRMs, chat bots, coding, predictive modeling and other business uses – various industry frameworks offer best practices.
- The NIST AI Risk Management Framework (AI RMF) advocates that companies define policies, map and measure risks, and implement risk strategies alongside every new adoption.
- The Google Secure AI Framework (SAIF) is an industry-led policy that emphasizes bringing existing security foundations into AI ecosystems, highlighting risks like data poisoning, prompt injection, and model stealing.
Safely transitioning to AI for cybersecurity
Is there a danger in applying “too much AI, too soon” in cybersecurity? Unfortunately, yes. Effective AI integration requires precision over power. There are some places where AI delivers genuine value; there are others where it does not.
For example, enterprises generate massive quantities of data that need to be analyzed. Using sophisticated LLM-powered tools for this task would be cost-prohibitive for most companies, not to mention unnecessary; this is a place where traditional data analysis tools perform better and cheaper.
Security alerts are another area where large amounts of data need to be filtered and sorted for use. Applying expensive, overly sophisticated AI tools for the sake of it drives up costs, sucks up computational power, and siphons valuable resources when other advanced tools will do. In this case, tools like Fortra Threat Brain; which connect IOCs across the attack chain using shared intelligence and telemetry from multiple tools.
Were we safer before AI?
As we bridge the gap between AI fantasy and reality, it’s important to know where AI is needed and where it becomes an additional operational burden. When something strains resources, it spills over into straining security resources as well.
While AI can counter AI‑enabled attacks, an organization’s security will depend on its ability to use AI more effectively than the adversaries who weaponize it. Achieving this requires a disciplined approach to implementing AI safely and appropriately.
Source: Fortra
Sophos Workspace Protection is an easy, effective, and affordable way to protect remote and hybrid workers, contractors and guests – and the networks and data they access – from threats, breaches, and shadow IT, and provide consistent policy enforcement on and off the network. It also enables a variety of hot-topic use cases like safe GenAI adoption and SaaS application controls.
What’s Included:
Sophos Workspace Protection provides a unique and elegant solution to the challenge of protecting remote and hybrid workers. It integrates all the network security components needed to secure apps, data, workers, and guests – wherever they are – into a single easy-to-use and familiar app: a hardened Chromium browser.
Sophos Workspace Protection includes:
- Sophos Protected Browser – a new secure Chromium web browser that provides several security features, including control over app usage, local data controls, and web filtering. It is hardened against exploits and attacks and integrates Sophos ZTNA for access to web apps and rich SSH and RDP support.
- Sophos ZTNA – now integrated into Sophos Protected Browser, it can be used agentless or with a thin agent as before. It also works with Sophos Endpoint to provide device posture assessment and Synchronized Security Heartbeat to define device health as part of access policies. Existing Sophos ZTNA customers will automatically get access to the full Sophos Workspace Protection bundle and all the added benefits it provides as of February 28th.
- Sophos DNS Protection for Endpoints – provides an additional layer of web protection across all apps, ports, and protocols on your remote Windows devices with added visibility, security, and privacy with DNS over HTTPS.
- Email Monitoring System – a Sophos email solution that deploys alongside Google or Microsoft email solutions to monitor email traffic and provide additional insights, analysis, and detections of unwanted or malicious email, including phishing attacks.
These product components are modular, and you can deploy only what you need. Sophos Endpoint or Sophos Firewall are not required, but Sophos Workspace Protection works better together with both products, unifying protection and extending Synchronized Security to remote workers everywhere they go.
What Sophos Workspace Protection can do for you
In addition to providing an elegant and affordable solution to secure your remote and hybrid workers and the apps and data they access, Sophos Workspace Protection also enables some hot use cases that many of you have been inquiring about:
- Enable Safe GenAI Adoption
- Enable Secure SaaS App Control
- Enable Secure Access for Contractors and Guests
It’s much easier and more affordable than SASE alternatives
Sophos Workspace Protection provides significant advantages over alternative SASE or SSE cloud-delivered solutions, including:
- Affordability: With no expensive cloud infrastructure or traffic management, Sophos Workspace Protection provides much better value.
- Efficiency and performance: There’s no backhauling traffic or man-in-the-middle decryption in the cloud to slow users down or cause compatibility headaches.
- Management overhead: Having a single app to protect all other online apps – private apps, SaaS apps, web apps – reduces day-to-day IT efforts. Plus, it’s simple to add and remove users – including contractors or workers using unmanaged devices.
- Security: Sophos Workspace Protection transforms the browser from a security liability into a key security asset.
- Universality: It works everywhere – on or off the network.
Sophos Workspace Protection is the ultimate solution for remote or hybrid workers – nothing is easier or more affordable.
Licensing and purchase options
Licensing is simple: it’s licensed on a per-user basis.
Sophos Workspace Protection is available stand-alone and can be purchased with any other Sophos Product, but no other product is required.
Source: Sophos
As Artificial Intelligence (AI) agents become more autonomous by accessing critical systems and acting without real-time human oversight, they are evolving from productivity tools into active Non-Human Identities (NHIs) like service accounts or API keys that require the same oversight and controls as human users. This shift expands organizational attack surfaces, introducing new security risks related to overprivileged access and lateral movement of NHIs across cloud infrastructure. When AI agents are compromised, cybercriminals may exploit prompt injection to manipulate an agent into executing unauthorized actions, stealing credentials or moving laterally across cloud environments.
To keep up with these challenges, organizations must rethink how zero-trust security applies to autonomous AI agents. The Model Context Protocol (MCP) introduces a context-driven framework for governing how AI agents access tools and data by emphasizing identity, access and intent, helping organizations apply zero-trust principles to the forefront of every machine-driven interaction.
Continue reading to learn more about MCP, how it enables zero-trust principles and how Keeper® enables zero trust for AI agents.
What is the Model Context Protocol (MCP)?
The Model Context Protocol (MCP), an open standard introduced by Anthropic, is designed to securely govern how AI agents autonomously access tools, data and systems in enterprise environments. Instead of allowing AI agents to operate with static or broad access controls, MCP emphasizes embedding context into every request an AI agent makes. For example, rather than granting an AI agent blanket read access to an entire database, MCP can evaluate whether a specific query, at that moment and for that task, should be permitted, retrieving only the specific access role required. This structure ensures that AI actions are transparent and aligned with organizational policies and security requirements.
MCP plays an important role in contextualizing and controlling AI agent behavior in real time. By embedding context into every interaction, MCP helps organizations continuously verify NHIs with least-privilege access and risk-based decisions, mitigating modern AI-specific attack vectors. A context-aware approach enables security teams to evaluate who or what is requesting access, as well as why and how the request is being made. As a result, MCP helps transform AI agents from high-risk identities into governed entities that work within a zero-trust environment, enabling organizations to scale AI adoption without jeopardizing safety or visibility.
How MCP enables zero-trust principles in AI workflows
Traditional zero-trust security models were made for human users, not autonomous AI agents that compromised workflows can influence. Without continuous identity verification, AI agents may unknowingly act on malicious instructions, reuse exposed credentials or create ideal conditions for privilege escalation and lateral movement. The MCP extends zero-trust principles to AI-driven workflows by ensuring each action is continuously verified, tightly controlled and fully auditable. With MCP, each request an AI agent makes is assessed based on context, including identity, task and environment, to adapt to changing conditions. For example, a DevOps AI agent deploying code may be limited to a specific environment for a set period, while a customer support AI agent may access only the customer records necessary to resolve a ticket. If an agent’s task or scope changes, access can be revalidated or revoked, reinforcing continuous verification.
This approach to real-time authentication limits credential exposure, preventing AI agents from accessing systems beyond their intended purpose. Time-limited access for AI agents reduces credential exposure while enforcing least-privilege access across environments. In addition, MCP enhances visibility and accountability by enabling contextual logging of autonomous actions, which security tools can use to support session recording, auditing and incident response.
Securing AI agent workflows with KeeperPAM
Although MCP defines how context should be applied to AI interactions, organizations still need Privileged Access Management (PAM) solutions to enforce zero-trust principles. KeeperPAM® secures AI-driven workflows by combining context-aware controls, zero-knowledge encryption and policy-based automation without exposing credentials or disrupting operations.
- Context-aware secrets management and session control: KeeperPAM enables AI agents to retrieve secrets dynamically, based on identity, role and runtime context, without hard-coding credentials. With Keeper Secrets Manager, access is policy-driven and continuously evaluated to ensure every AI agent is granted least-privilege access for each task and session.
- Time-limited, credential-free access for AI agents: Keeper supports Just-in-Time (JIT) access for both human identities and NHIs, eliminating standing privileges. Credentials are issued only when necessary and expire automatically once a task is completed, reducing the attack surface.
- End-to-end encryption with zero-knowledge architecture: With end-to-end encryption, secrets are never exposed in plaintext to AI agents or to Keeper itself. This level of security allows AI agents to make decisions and execute actions without handling sensitive credentials, supporting zero-trust principles.
- CI/CD integration and ephemeral tunnels: KeeperPAM integrates with CI/CD pipelines and infrastructure automation tools while keeping secrets out of source code and configuration files. Having ephemeral access and secure tunnels allows AI agents to interact with critical systems without retaining credentials for future use.
- Support for PAM protocols in AI-driven automation: With native support for SSH, RDP and SQL, KeeperPAM enables AI agents to securely automate infrastructure management, remote access and database operations under consistently enforced policies.
- Session recording, policy enforcement and RBAC: All AI-driven privileged sessions can be monitored, recorded and enforced by Role-Based Access Controls (RBAC). This provides full visibility into autonomous actions while maintaining least-privilege access for NHIs. When high-risk activity is detected, KeeperAI automatically terminates the session.
Building AI systems you can trust
As AI agents become embedded across enterprise environments, zero-trust security is crucial for maintaining secure, autonomous, machine-driven access. The MCP introduces a foundational context layer needed to continuously verify AI agents’ identities, intents and access at scale. To enhance modern security postures, organizations need zero-trust controls within a strong PAM solution that integrates with MCP. With its MCP integration, KeeperPAM delivers the privileged access and secrets management required to securely enable AI-driven workflows without exposing credentials or losing visibility.
Start your free trial of KeeperPAM today to secure AI agents with zero-trust security across your organization.
Source: Keeper
AI is reshaping cybersecurity. Attackers are using AI to accelerate reconnaissance, generate malware, personalize phishing, and automate parts of the attack chain. Defenders now face a human‑plus‑machine problem – one that requires AI to augment analysts, accelerate decisions, and strengthen outcomes.
Sophos has been embedding AI across our portfolio for nearly a decade, and agentic AI is now a core part of that strategy.
Within Sophos Managed Detection and Response (MDR), agentic capabilities automate early‑stage triage and investigation while keeping analysts firmly in control. The result is faster detection, faster response, and a more efficient SOC.
How Sophos MDR uses Sophos AI agents
AI agents are autonomous engines that execute defined workflows without requiring human prompts. They differ from AI assistants, which respond to analyst questions.
Sophos MDR currently uses two production‑grade AI agents – both designed by our in‑house AI team and refined with our MDR analysts – to accelerate case handling and improve SOC efficiency.
Triage Agent: Reducing noise and prioritizing what matters
The Triage Agent runs continuously and activates the moment a new detection is created.
It:
- Analyzes contextual signals such as correlation IDs and historical telemetry
- Identifies benign penetration‑testing activity
- Eliminates duplicate or redundant detections
- Assigns case severity to determine whether analyst review is required
This automated triage reduces alert noise by more than 60% and ensures analysts focus on the events that truly matter.
Case Investigation Agent: Fast, explainable investigations
When a case is promoted for review, the Case Investigation Agent takes over.
It:
- Builds a behavioral timeline using runtime telemetry and correlated detections
- Enriches indicators of compromise (IoCs), performs reputation checks, and analyzes command‑line activity (including de‑obfuscation)
- Generates dynamic investigation steps tailored to the threat
- Iterates through evidence, adjusting its plan as new information emerges
- Produces a clear, explainable verdict and recommended actions
This agent reduces mean time to investigate by up to 50%, giving analysts a structured, auditable foundation for rapid decision‑making.
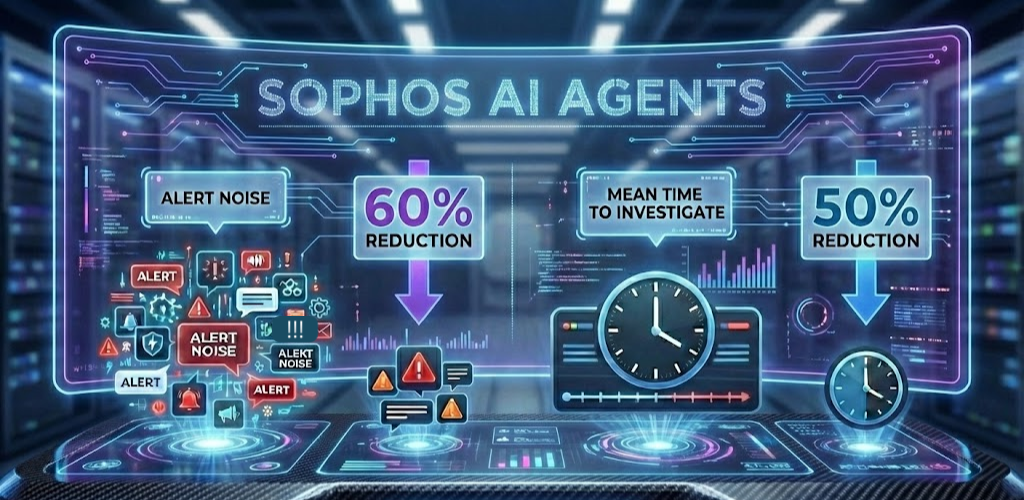
Human‑in‑the‑loop validation remains central. The agents accelerate the work, while Sophos MDR analysts confirm findings, refine conclusions, and take action.
Delivering measurable SOC outcomes
Sophos AI Agents strengthen MDR operations at every stage:
Faster analyst engagement: Routine, low‑severity events are handled automatically, allowing analysts to focus immediately on high‑impact threats.
Faster investigations: Agents surface early indicators, enrich data, and provide ready‑to‑validate conclusions.
Consistent access to expertise: Agents apply the collective knowledge of Sophos MDR’s playbooks and analyst experience at scale.
Higher analyst efficiency: Automation frees analysts to focus on complex hunts, containment, and adversary disruption.
Continuous improvement: Agents re‑trigger on new detections and re‑enrich new IoCs as investigations evolve.
These capabilities directly reduce mean time to detect (MTTD) and mean time to respond (MTTR) for Sophos MDR customers.
How the Sophos AI Agents Work
Case Triage Agent: Automating the first response
The Triage Agent performs a structured sequence of actions, including:
- Extracting entities and observables (hosts, users, processes, IoCs)
- Classifying penetration‑testing activity
- Linking related detections to prevent duplicate cases
- Assigning severity based on contextual signals
This ensures analysts spend their time on the most relevant, high‑impact threats.
Case Investigation Agent: Deep, adaptive analysis
The Case Investigation Agent uses three coordinated sub‑agents:
- Plan generation: Creates a dynamic set of investigation steps
- Execution: Runs queries, makes API calls, and retrieves results
- Analysis: Enriches IoCs, extracts entities, and updates the investigation state
The agent iterates until it has enough evidence to produce a comprehensive report including verdict, summary, IoCs, timeline, and recommended actions.
Together, these agents act as always‑on investigative partners, accelerating early case handling and delivering structured, explainable outcomes.
Agentic, but human‑centered
At Sophos, our approach to agentic AI is grounded in three principles:
- Embedded AI: AI is woven directly into MDR workflows, not bolted on.
- Transparency: Every automated action is explainable and auditable.
- Human‑in‑the‑loop: Analysts remain accountable and empowered.
These principles ensure that agentic AI amplifies human expertise rather than replacing it.
Sophos AI Agents are already delivering measurable improvements for MDR customers by reducing noise, accelerating investigations, and strengthening defenses against advanced, human‑led attacks.
The Path Forward: The agentic SOC
The MDR AI Agents are the first step toward a broader agentic SOC vision. We’re expanding agentic capabilities across the Sophos platform, including:
- Enhanced agents that generate hypotheses, gather context, and propose actions
- Expanded coverage across network, identity, email, and cloud
- AI Agents for XDR customers and partners
- Hyper‑automation through AI + SOAR
- Unified AI governance, visibility, and runtime security
This next‑generation SOC is powered by autonomous‑but‑supervised agents that scale analyst impact and deliver consistent, high‑quality security outcomes.
Learn more
Explore our AI technologies at Sophos.com/AI and learn more about Sophos MDR at Sophos.com/MDR. And our AI Principles and Responsible AI FAQs are available in the Sophos Trust Center.
Source: Sophos
Generative AI tools present both a significant opportunity and a genuine risk. While GenAI can enhance, streamline, and augment a wide range of workflows, it also introduces the potential for misuse and the exposure of sensitive or proprietary data. As a result, many organizations are struggling with GenAI adoption. GenAI is top-of-mind for many IT teams, and most are in the early stages of experimentation but lacking the governance, controls, and safeguards required to adopt GenAI safely.
Sophos Workspace Protection, provides all the controls organizations need to safely and easily embrace GenAI such as:
- Get visibility into the GenAI tools and services currently being used
- Easily setup policies to block unsanctioned GenAI sites, apps, and tools both in and out of the browser
- Optionally warn users against the use of unsanctioned services so they can self-govern
- Use data boundary controls to block, warn, or allow file uploads or downloads and copy and paste operations to prevent sensitive data mistakes
What You Need:
Safe GenAI policies are made possible thanks to a few of the key capabilities that make up Sophos Workspace Protection:
- Sophos Protected Browser integrates a secure web gateway with rich policy controls and data boundary controls that provide a transparent and familiar experience for workers
- Sophos DNS Protection for Endpoints adds an additional layer of domain-level security and control that spans across all ports, protocols, and apps on the device
- Sophos Central provides a consistent easy management experience with rich insights and reporting
These products integrate seamlessly to make safe GenAI adoption easy.
How it Works:
Watch this video for a quick demonstration of how it works, and how easy it is to set up:
One of the powerful but easy capabilities of the Sophos Protected Browser are the data boundary controls – which does what it says on the tin. It establishes boundaries around data operations such as copy and paste, upload and download, and more, to keep data within allowed applications where necessary, and prevent potentially costly data sharing mistakes:
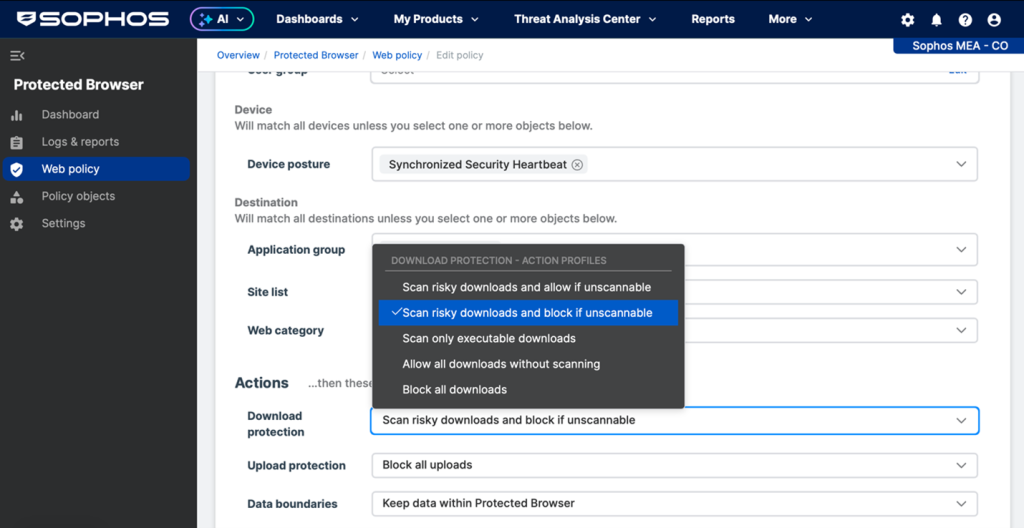
Sophos Protected Browser provides granular data boundary controls for uploads, downloads, copy and paste, and more.
Users are notified when their actions are blocked.
Get a full overview of the data boundary control options in the online documentation.
Restricting Access Through Sophos Protected Browser Only:
For organizations looking to restrict all access to GenAI webservices through the Sophos Protected Browser only, this is also very possible when combined with Sophos Endpoint App Control which can block the use of all other browsers ensuring all interaction with GenAI is done through the Sophos Protected Browser.
Learn More about Sophos Workspace Protection:
Check out all the great capabilities and use cases for Sophos Workspace Protection and be sure to participate in the early access program for the new Sophos Protected Browser.
Source: Sophos
Most IT teams are doing impressive work under difficult conditions. Tickets get closed. Systems stay online. Users are supported. On paper, everything is functioning.
And yet, there’s a persistent feeling that progress is harder than it should be.
As expectations for faster, more consistent and more scalable IT service delivery rise, many teams are starting to feel overwhelmed. Too much time is still spent on manual documentation, repetitive service tasks and disconnected processes that slow response times and pull focus away from higher-impact, proactive work.
The natural assumption is that demand exceeds the team’s ability to keep up. More endpoints, more users, more complexity — surely the answer is more people.
But for many IT organizations, the challenge isn’t just a headcount numbers game. The real limitation is how much of the day is still consumed by manual, repetitive work.
Manual workloads quietly become the bottleneck
Manual, repetitive work rarely shows up as a red flag. It blends into the background of daily IT operations. A technician copies information from one system into another. Someone searches for documentation that exists — just not where they need it.
Each instance may seem minor, or even necessary, on its own. But over time, they accumulate. As IT environments grow more complex, manual tasks multiply, context becomes increasingly fragmented and resolution paths stretch longer than they should.
What used to feel manageable starts to feel overwhelming, simply because every task takes more effort than it should. This is the tipping point where managing manual workloads stops being routine and start becoming a liability.
Why manual repetitive work becomes technical debt
As IT environments evolve, processes built for speed eventually fall behind. Teams compensate by relying on workarounds, institutional knowledge and manual effort instead of consistent systems.
The cost isn’t obvious at first. However, over time, it shows up as:
- Longer resolution times for routine issues
- Inconsistent outcomes between technicians
- Burnout among the people who know the environment best
- Increased risk from missed steps and missing context
Over time, those manual tasks become a form of technical debt that IT teams struggle to escape. Technicians feel the debt first
Technicians are on the front lines, and they feel the burden most. A significant portion of their day is often spent searching for information across fragmented systems or recreating work because documentation is missing or outdated. Instead of resolving issues, they’re stuck navigating disconnected tools and repetitive, manual tasks.
Over time, this erodes momentum. Skilled technicians spend their days executing processes instead of improving them. The job becomes about keeping up rather than moving forward.
This is usually the first signal that manual work has crossed the line from “how things are done” to “what’s holding us back.”
Managers see the impact when scale stops working
For IT operations leaders, the consequences of manual workloads surface differently.
Scaling IT effectively requires more than hiring. Leaders are under pressure to keep pace with growing demand while also giving their teams room to develop skills and improve how work gets done. Organizations must balance workload, automation and upskilling to ensure teams can operate effectively today while preparing for what’s next.
Manual workloads introduce friction at every stage of the ticket lifecycle. When prioritization and triage rely on human review, tickets wait in queues, urgency is misjudged and critical issues are often buried behind lower-impact requests. As volumes grow, teams spend more time sorting and routing work than resolving it.
Why fixing individual tasks won’t solve the problem
When teams start to feel the weight of manual work, the first instinct is usually to automate pieces of it. A script here. A rule there. Maybe a new tool to speed up one step in the process. Those changes can help — but they rarely change how the work actually feels day to day.
That’s because automating isolated tasks inside broken workflows just creates faster fragments. Technicians still have to jump between monitoring alerts, ticket queues and documentation systems to understand what’s happening. Context still lives in multiple places. And work still depends on people stitching everything together by hand.
At that point, the problem isn’t effort or expertise. It’s that service delivery itself is fractured across disconnected systems.
Real progress starts when teams step back and ask a harder question: How should this work flow from start to finish?
Where AI actually changes the equation
That question — how work should flow end to end — is where AI begins to matter in a meaningful way.
Instead of automating individual steps, AI makes it possible to connect them. When service delivery runs through an integrated, AI-driven workflow, alerts flow directly into tickets, relevant context surfaces automatically and repetitive decisions no longer require human intervention.
Issues get resolved faster and service delivery starts to feel more predictable and consistent. Teams spend less time chasing information and more time fixing issues. Processes become consistent. Outcomes become repeatable. And the operation can scale without adding complexity, headcount or burnout.
AI doesn’t solve the problem by working harder. It solves it by changing how the work fits together.
The real shift IT operations need to make
Organizations that take this step reduce operational friction, lower costs and make service delivery easier to manage. It’s time to shift gears and strategically evaluate how AI can transform your IT operations and reduce the technical debt of manual workloads.
Those that wait risk falling behind, constrained by manual processes and fragmented systems that make it harder to respond quickly to evolving market demands and technology change.
IT operations are entering a new phase. Discover how AI is becoming a game changer for IT operations — from automating documentation workflows to accelerating ticket resolution and helping teams work smarter, not harder.
Source: Kaseya
Sophos has been named a 2026 Gartner® Peer Insights™ Customers’ Choice in the 2026 Gartner® Peer Insights™ Voice of the Customer Report for Endpoint Protection Platforms . This marks our first Gartner Peer Insights Customers’ Choice distinction of 2026 and a fifth consecutive Customers’ Choice for Sophos in the EPP category. This recognition comes directly from customer feedback, and we’re truly thankful for the time customers take to share their experiences and for the trust they place in Sophos.
In the 2026 Voice of the Customer report for Endpoint Protection Platforms, Sophos’ rating is based entirely on verified customer feedback based on 286 total reviews as of 30 November 2025:
- Named a Customers’ Choice vendor for the 5th consecutive time
- 4.9 / 5.0 overall rating – the highest rating among vendors in the Customers’ Choice Quadrant
- 4.8 / 5.0 rating for Product Capabilities – the highest among vendors in the Customers’ Choice Quadrant
- 98% Willingness to Recommend – tied for the highest among vendors in the Customers’ Choice Quadrant
We believe these results reflect Sophos’ focus on delivering powerful, easy-to-manage endpoint protection that combines advanced threat prevention, detection, and response across modern work environments.
Built for Modern Workspaces and Evolving Threats
We believe Sophos’ continued recognition in the Gartner® Peer Insights™ Voice of the Customer Reports for Endpoint Protection Platforms aligns with its broader strategy to secure today’s dynamic, hybrid work environments. With capabilities that extend beyond traditional endpoint security, Sophos helps organizations protect users, devices, and data wherever work happens. The recent introduction of Sophos Workspace Protection is the ideal complement to Sophos Endpoint, Sophos MDR, and Sophos Firewall and extends and unifies these great products and services to remote and hybrid workers everywhere they go.
Recognition Driven by Real Customer Experiences
Gartner Peer Insights is a free peer review and ratings platform designed for enterprise software and services decision makers. We feel being named a Customers’ Choice reflects both high overall ratings and strong willingness to recommend, consistently validating Sophos’ commitment to customer success. We are incredibly grateful to our customers worldwide for their continued trust and feedback, which directly contribute to shaping and improving Sophos’ solutions.
Here are some examples of what customers had to say about Sophos Endpoint:
“Our overall experience with Sophos Endpoint has been exceptionally positive. It delivers enterprise-grade protection without the complexity. The seamless integration and proactive defense against emerging threats have given our IT team complete peace of mind and significantly reduced our management overhead.” – CIO in the Manufacturing Industry, $50M-$250M, Review Link
“Everything about Sophos, from their admin tools to the user experience to the support and sales team, is top-notch. We have been using Sophos Endpoint for almost 13 years now, as Endpoint protection is the bare minimum requirement of our security-minded clients and audits. Every year, we add more and more users to our Endpoint protection, scattered across our five offices located in LA, NY, Austin, London, and Tokyo” – Director, IT Security and Risk Management in the Media Industry, $50M-$250M, Review Link
To learn more about how Sophos Endpoint can help your organization, visit: https://www.sophos.com/en-us/products/endpoint
Source: Sophos
The World Economic Forum’s Global Cybersecurity Outlook 2026 delivers a clear and uncomfortable truth: cyber risk is accelerating faster than our traditional defenses can keep up. AI-driven attacks, geopolitical volatility, supply-chain fragility, and widening cyber inequity reshape the threat landscape at a systemic level.
What stands out most, however, is not just what is changing—but where defenses are consistently failing.
Across AI misuse, ransomware, fraud, supply-chain compromise, and cloud outages, identity remains the dominant attack path. Whether human or non-human, identities have become the new control plane of modern cybersecurity.
In this blog, I break down five Identity Security lessons we can learn from the research.
Lesson 1: AI has turned identity abuse into a force multiplier
According to the report, 94% of organizations identify AI as the most significant driver of cyber risk, and 87% cite AI-related vulnerabilities as the fastest-growing threat. While much attention is placed on AI models themselves, the more systemic risk lies elsewhere.
AI agents, like other identities, don’t break in—they log in.
Attackers are using AI to:
- Scale phishing and impersonation with unprecedented realism
- Automate credential harvesting and privilege escalation
- Exploit over-privileged service accounts, APIs, bots, and AI agents
The report explicitly highlights that the multiplication of identities—especially AI agents and machine identities—has outpaced governance and security controls. These non-human identities (NHIs) now outnumber human users in most environments, yet remain largely invisible, unmanaged, and implicitly trusted.

Security takeaway:
If organizations continue to protect networks and endpoints while trusting identities by default, AI will simply accelerate compromise.
This is why it’s important to apply Zero Trust principles to Identity Security. If authentication and authorization are where your security controls end, you’re likely not implementing a Zero Trust approach.
Instead, security-first approaches like adaptive MFA and risk-based access controls for all identities – whether it’s humans, service accounts, APIs, AI agents, legacy systems, and more – ensure your strategy is based on continuous validation. Rather than, “Do the credentials/access match the identity?” you should be able to answer questions like “Does this access make sense to allow based on the risk signals?”
Lesson 2: Cyber-enabled fraud is an identity problem, not a financial one
The report reveals that 73% of respondents were personally affected by cyber-enabled fraud, making it the top concern for CEOs—surpassing ransomware.
What’s driving this surge?
- AI-powered impersonation
- Credential reuse
- Lateral movement using legitimate access
- Abuse of trusted identities rather than malware
Fraud today succeeds not because systems are unpatched—but because identity verification stops too early.
Once credentials are obtained, most environments still fail to:
- Continuously validate access
- Detect abnormal identity behavior
- Apply step-up authentication dynamically
Security takeaway:
Fraud prevention and identity security are now inseparable. Fraud begins and end with identity abuse, meaning that real-time, context-aware controls are needed to stop fraudulent activity before material damage is done.
From the report, it’s also clear that CEO and CISO priorities are shifting, yet the foundation for where they can come together remains the same: through strong Identity Security.
Lesson 3: Supply-chain attacks inherit trust—and abuse it
The WEF report identifies third-party and supply-chain vulnerabilities as the top cyber resilience challenge for large organizations. Crucially, the most common supply-chain risk is not malware—it is inherited trust.
When vendors, partners, or managed services connect:
- They often authenticate via service accounts
- Credentials are long-lived and rarely rotated
- Access is broad, persistent, and poorly monitored
Attackers don’t need to breach the perimeter if they can log in through a trusted identity.
Security takeaway:
Supply-chain security failures are identity governance failures. Supply-chain breaches succeed by abusing inherited trust, not by exploiting technology gaps. Organizations should treat third-party access as an identity risk by maintaining a clear inventory of vendor identities, enforcing least-privilege and time-bound access, and eliminating standing permissions wherever possible. Strong authentication should be prioritized for high-risk vendor access, and access reviews must align with contract and business lifecycles. Even without new tools, disciplined governance can significantly reduce supply-chain exposure.
Lesson 4: Cyber resilience depends on identity visibility, not just recovery plans
While 64% of organizations claim they meet minimum cyber resilience requirements, only 19% exceed them. Highly resilient organizations share one defining trait: deep visibility and control across identities.
The report’s Cyber Resilience Compass shows that resilient organizations:
- Continuously assess AI and identity risks
- Monitor access across IT, OT, and cloud
- Reduce standing privileges
- Treat identity as a shared ecosystem risk
Yet identity remains fragmented across directories, clouds, SaaS platforms, legacy systems, and machine workloads.
Security takeaway:
You cannot be resilient if you don’t know who or what is accessing your systems—and why. That’s why it’s so important to retain a living, dynamically-evolving graph visualizing which identities exist and their access paths. This acts as a unified source of truth that can expose exploitable gaps that need closing.
Lesson 5: Cyber inequity makes identity the weakest link
The report highlights a widening cyber inequity gap, driven largely by skills shortages—particularly in identity and access management roles, which are among the top three most understaffed security functions globally.
Complex IAM implementations, agent-based controls, and application rewrites are no longer realistic for many organizations.
Security takeaway:
Identity security must become simpler, not more complex. IAM upskilling needs to happen in tandem with identity-first security solution implementation; this is how we close the gap between IAM and cybersecurity teams while reducing operational burden. Cyber inequity makes identity the most fragile control post – especially where skills are resources are limited.
Implementing security solutions designed with identity teams in mind offers many benefits. By standardizing identity policies (e.g., enforcing MFA on all remote and privileged access), organizations reduce dependency on scarce expertise, lower configuration errors, and achieve consistent risk reduction. For example, you can apply one access standard to employees, contractors, and service accounts, cutting operational overhead while measurably shrinking the attack surface.
The strategic shift: From perimeter security to identity-centric Zero Trust
The Global Cybersecurity Outlook 2026 reinforces a fundamental shift: Cybersecurity is no longer about defending a defined perimeter—it’s about securing infrastructure and access in real-time.
AI, cloud, supply chains, and geopolitics have dissolved the perimeter. Identity is what remains.
Organizations that will succeed in 2026 and beyond are those that:
- Treat identity as critical infrastructure
- Secure non-human identities with the same rigor as human users
- Enforce Zero Trust dynamically, everywhere
- Reduce implicit trust across ecosystems
Silverfort was built precisely for this moment—to secure identities wherever they exist, however they authenticate, and whatever they access.
Silverfort’s platform approach to Identity Security recognizes that identities span cloud, on-prem, legacy systems, service accounts, and non-human workloads—yet they are secured through fragmented controls. By acting as a unified enforcement layer across all authentication paths, the platform enables consistent Zero Trust policies without agents or application changes. This allows organizations to reduce identity risk holistically, rather than incrementally securing identities one system at a time.
Final thought
The WEF report concludes that cyber resilience is a shared responsibility and a strategic imperative. Identity Security is where that responsibility becomes actionable.
In the age of AI-driven threats, every breach is an identity breach first.
The question for organizations is no longer if identity should be central to their security strategy—but how quickly they can make it so.
Source: SIlverfort
Multi-factor authentication (MFA) remains a cornerstone of cybersecurity, but attackers have learned to find workarounds.
As identity-driven attacks continue to rise, organizations must go beyond MFA to build resilience. Sophos experts and recent Gartner research agree: It’s time for an identity-first security strategy backed by continuous detection and response. For many organizations, keeping pace with identity threats feels overwhelming, especially as hybrid environments expand. But there’s a clear path forward.
Identity is now the primary attack surface
Chris Yule, director of threat intelligence for the Sophos X-Ops Counter Threat Unit, notes that more than 60% of incidents his team investigates stem from identity-related weaknesses. Phishing, stolen credentials, and social engineering are common entry points — methods that allow attackers to infiltrate without deploying traditional malware.
“The number one threat facing our customers today continues to be ransomware, both in terms of the number of incidents that we see and the impact that it can have when it hits,” Yule explained during a recent webinar. “Classic ransomware cases consistently show identity compromise as the critical first step.”
As organizations expand across hybrid and cloud environments, each new integration, from software-as-a-service (SaaS) apps to service accounts, becomes another entry point. Yet, as Yule noted, there will often be cyberattacks where there’s “very little malicious code in use.” Rather, they mainly use “privilege and trust to gain access to the environment and cause as much damage with that trust as possible.”
Why MFA alone isn’t enough
MFA is essential, but it’s not enough. Attackers have evolved, and identity-based threats now bypass even strong authentication. Organizations need continuous detection and response to stay ahead. In multiple business email compromise (BEC) cases, adversaries bypassed MFA using adversary-in-the-middle (AiTM) phishing kits.
An AiTM attack goes beyond traditional phishing. Instead of simply stealing credentials, the attacker intercepts and relays the victim’s login session in real time. When a user clicks a phishing link and enters their credentials on a fake site, the attacker forwards those details to the legitimate service and captures the entire authentication flow, including MFA responses, allowing them to hijack the session.
This reality aligns with findings that Gartner outlines in their report “CISOs Must Integrate IAM to Strengthen Cybersecurity Strategy .” This report notes that credential compromise remains the leading cause of breaches and that “sophisticated attackers are now targeting the [identity access management] IAM infrastructure itself.”
Gartner further cautions that while prevention is essential, “there is no such thing as fail-proof prevention.” Security teams must be prepared to detect and respond when identity defenses are bypassed.
Identity-first security: The next evolution
According to Gartner, cybersecurity leaders should “embrace identity threat detection and response (ITDR) and adopt identity-first security to enable zero trust and optimize the organization’s cybersecurity posture.”
Identity-first security reframes protection around who and what is connecting, rather than where they’re connecting from. Instead of static perimeter controls, it focuses on continuous trust assessment and adaptive access. In practice, this means:
- Monitoring identity posture continuously, not just enforcing login controls.
- Detecting and responding to abnormal behaviors like privilege escalation or lateral movement.
- Reducing the attack surface by addressing misconfigurations and overprivileged accounts.
Detection for the identity layer
Yule emphasized that Sophos built our Identity Threat Detection and Response (ITDR) service precisely to fill this gap.
“Historically, identity and access management and security operations have always been largely separate things,” Yule said. “And so, what we’ve tried to do with ITDR is look at the overlap of those.”
By continuously assessing identity posture, Sophos ITDR monitors for:
- Stolen or exposed credentials on the dark web.
- Accounts with excessive or unusual permissions.
- Application misconfigurations that enable privilege abuse.
This proactive approach complements Sophos Managed Detection and Response (MDR) and Extended Detection and Response (XDR), ensuring organizations can detect threats in action while also reducing the risk of identity exploitation before attacks begin.
Identity has become the cornerstone of modern cybersecurity, and building resilience starts with treating it as a core discipline. Together, ITDR, MDR, and XDR create a security fabric that is continuous, adaptive, and resilient.
“As we increase trust in different things, things become more complicated, things become more opaque, and it becomes harder to know and identify these micro vulnerabilities that could be exploited by somebody who is smart enough to figure it out,” Yule said.
Organizations that adopt identity-first security strategies gain the agility to detect and neutralize threats before they escalate.
Explore how Sophos Identity Threat Detection and Response (ITDR) helps organizations preempt and neutralize identity-based threats before they become breaches.
Source: Sophos
Managed Service Providers (MSPs) are third-party companies that typically handle a portfolio of other organizations’ IT operations or day-to-day activities. This puts MSPs on the front lines of cybersecurity for numerous businesses, often in highly regulated industries, handling some of their most sensitive data. Even the most experienced MSPs struggle to securely manage passwords, credentials, sensitive files and privileged access across dozens of client environments.
Many MSPs still manage client passwords using shared spreadsheets, sticky notes or unsecured browsers. This makes it difficult to track access, audit usage or enforce strong password policies across critical systems. Without centralized visibility, MSPs face inconsistent access controls, delayed incident response and increased exposure to credential-based attacks. To stay secure and efficient, MSPs need an easy, centralized way to protect client environments and enforce strong password practices at scale.
The need for MSPs to strengthen security
MSPs are increasingly adopting stronger security and password management practices to protect clients and improve operational efficiency. LEAP Managed IT, a North America-based MSP headquartered in Indiana, serves clients across the Midwest, including government agencies, financial institutions, law firms, nonprofits, healthcare organizations and more. The team needed a way to simplify password sharing among internal staff and managed clients while maintaining compliance with industry standards such as CMMC, PCI, HIPAA, ISO, GovRAMP and FedRAMP.
TeamLogic IT in West Denver, which supports 20 clients and 275 end users, faced similar challenges. Many clients relied on insecure methods, such as spreadsheets or email, to share passwords. The lack of centralized control made it difficult to revoke access or track changes when employees left.
Every second spent resetting passwords or tracking down credentials is time taken away from supporting clients and growing the business. A streamlined, secure approach allows MSPs to deliver faster service, reduce risk and demonstrate value in every client interaction.
What KeeperMSP® delivers
KeeperMSP is a Privileged Access Management platform built specifically for MSPs. Core functionality of the platform includes password and secrets management to prevent password-related data breaches and cyber attacks. It helps MSPs protect their own operations while delivering stronger security for every client they manage.
Designed to meet the unique needs of MSPs, KeeperMSP provides complete visibility into end users’ password habits through robust reporting and auditing tools that help enforce security and compliance requirements. This includes Role-Based Access Control (RBAC), Multi-Factor Authentication (MFA), SIEM event reporting and regulatory and industry compliance with the CCPA, GDPR and other standards.
Purpose-built for MSPs, backed by success
For LEAP Managed IT, integrating KeeperMSP with Microsoft Entra ID enabled the team to quickly roll out the platform to 50 employees and hundreds of client users. The company gained real-time visibility into password security and compliance, while technicians in the field could securely access credentials through Keeper’s browser extension and mobile app.
TeamLogic IT experienced similar benefits. Like many MSPs, the company supports dozens of businesses with diverse IT needs. Using KeeperMSP’s role-based access controls and One-Time Share feature transformed the way the team collaborates with clients. The company can now grant or revoke access instantly and share credentials securely without relying on outdated spreadsheets or PDFs.
Across both organizations, unified password management is delivering measurable results. With KeeperMSP, Leap Managed IT and TeamLogic IT continue to improve compliance reporting, reduce credential-related service tickets, streamline credential management best practices and strengthen client relationships.
Managing credentials at scale
According to a 2025 report by Global Market Insights, the MSP market is projected to increase from $69.68 billion to $115.83 billion by 2034, averaging a Compound Annual Growth Rate (CAGR) of 5.8%. MSPs are expected to continue offering highly compliant cloud services, particularly solutions that streamline necessary business functions while providing stronger protection against cyber threats. According to data compiled from Infrascale, cybersecurity threats remain the leading concern for MSPs, with 59.7% identifying it as their top challenge.
In a multi-client environment, MSPs face unique challenges that traditional password managers can’t solve. A purpose-built solution empowers MSPs to secure every client and maintain trust across industries and regulatory requirements. With the right platform, MSPs can reduce risk, streamline operations and deliver stronger security outcomes for every customer they support. Keeper enables MSPs to secure every client account with zero-trust architecture, intuitive management tools and scalable efficiency.
Start a free trial of KeeperMSP today to secure your clients’ most sensitive data, increase visibility and streamline credential management across your organization. Read the full Keeper + LEAP Managed IT Case Study to learn more.
Source: Keeper
AI has dominated cybersecurity headlines for years, but as we enter 2026, the conversation is shifting from hype to hard realities. Across incident response, threat intelligence, and security operations, Sophos experts see clearer signals of where AI is truly making an impact. For IT teams already stretched thin, this isn’t theoretical — it’s reshaping daily decisions.
Defenders are having to deal with the speed and unpredictability of AI adoption inside their organizations. Sophos survey data shows IT leaders are increasingly worried about unmanaged use, data exposure, and how AI-enabled tools can amplify small mistakes. The question is no longer whether to use AI, but how to apply it responsibly to reduce noise and operational strain.
Industry signals reinforce this shift. The Gartner® Hype Cycle™ for Security Operations, in our assessment, shows AI-powered capabilities — such as AI SOC agents, predictive modeling, and cybersecurity assistants — moving out of pure experimentation and toward more practical, augmentation-focused use cases. The emphasis is less on “autonomous AI” replacing humans, and more on AI accelerating triage, improving prioritization, and helping overstretched teams act faster and with greater confidence.
Looking ahead, Sophos experts expect AI’s real impact to be measured by outcomes, not novelty — a theme reflected in their predictions for the year ahead.
DPRK IT workers extend the use of AI for fraudulent employment
“North Korean IT workers could use Agentic AI to enhance the survivability of their fake personas, improve the responsiveness to remote requests, and conduct remote taskings more effectively.” – Rafe Piling, Director of Threat Intelligence, Sophos X-Ops Counter Threat Unit
AI will supercharge threat actor scale and sophistication
“In 2026, attackers will continue to use AI as a force multiplier. AI will make it easier to weaponize known vulnerabilities, orchestrate attack campaigns, lowering the barrier for basic hacking and enabling broad, rapid exploitation across the internet.
Payloads will be customized faster than ever, and social engineering will become increasingly tailored, including phishing that reflects open-source knowledge of individual targets. Deepfake audio and video will make BEC campaigns more convincing and far more credible, making them easier to succumb to.
AI will shift the balance of power by helping even low-skill threat actors operate with speed and precision once reserved for more experienced threat actors.” – John Peterson, Chief Development Officer
The real attack surface: Your AI application
“We’re likely to see major breaches from prompt injection attacks within the next year. For years, security teams have worked to shrink their internet footprint, knowing that anything exposed increases risk.
Firewalls, VPNs, and ZTNA all aimed to reduce that exposure. Now, almost overnight, we’ve created a new attack surface: rapidly deployed AI applications. Many are internet-facing, often unauthenticated, and connected to data many businesses would consider sensitive or confidential. Even more concerning, these applications are being granted the ability to take actions on behalf of the organization.
The speed of AI adoption is driving huge efficiency gains, but unless organizations slow down and assess these risks, they’ll reopen exposures we’ve spent decades trying to close.” – Tom Gorup, Vice President of SOC Operations
The next insider is your AI
“Organizations are racing to deploy LLMs and agents, even the ones they approve internally. By feeding these tools massive volumes of corporate data, they’re creating a new class of insider threat. When that data leaks, who’s responsible? Is the AI an ‘employee,’ and who carries the liability when it goes rogue, is compromised, or misconfigured?” – Chris O’Brien, Vice President of Security Operations
Customers will turn to channel partners to resolve the AI vs. Security priority gap
“In 2026, customers will wrestle with the tension between AI investment vs. core security investment vs. broader IT investments. They’ll be asking: ‘How much time, money and resources should I spend on AI?’ ‘Where do AI and security overlap?’ ‘What are the initial use cases that I trust AI to do?’
While SMBs and enterprises will answer those questions very differently, both will rely on vendors and partners as their trusted advisor. With more tools flooding the market and budgets under pressure, partners who help customers make sense of the noise and rationalize their stack will prevail.
The channel’s role is no longer about sourcing tools; it’s about guiding customers through complex decisions around risk, budget, security and AI strategy trade-offs across the entire customer lifecycle.” – Chris Bell, Senior Vice President of Global Channel, Alliances and Corporate Development
Trusting MDR when the analysts are AI
“In 2026, the Managed Detection and Response (MDR) market will reach an inflection point. The line between a managed detection service and an AI-driven tool will blur until customers can no longer tell which they’re buying. Vendors will market software as full MDR offerings, leaning on AI to compensate for limited human depth.
That shift will create real challenges: customers won’t know where human judgment ends, what’s automated, or who is actually monitoring their environment around the clock. Trust will become harder to calibrate when the ‘team’ behind your security is mostly code. As this ambiguity grows, buyers will struggle to evaluate competence, accountability, and reliability, forcing the industry to confront whether MDR is still a service, a tool, or something in between.” – Tom Gorup, Vice President of SOC Operations, Sophos
Source: Sophos
Sophos introduced Synchronized Security in 2015 with the ability for Sophos Firewall and Sophos Endpoint to share information and work together to automatically respond to threats. This pioneering approach, which transformed cybersecurity from a collection of point products to a security ecosystem, has been successfully reducing cyber risk and elevating security outcomes in the face of real-world threats for over a decade.
We’ve steadily expanded and evolved Synchronized Security since that initial launch, including interconnecting a broad range of products and services, extending response actions, and synchronizing our threat intelligence. Today, Sophos Workspace Protection becomes the latest addition to the Synchronized Security portfolio.
Security Heartbeat
Three key capabilities come together to enable Sophos solutions to work together:
- Security Heartbeat™ is a constantly beating device health status indicator that shows Red, Amber, or Green to reflect its real-time state.
- The Sophos Central platform, which enables Sophos solutions to share threat, health, and security information in real-time, including Security Heartbeat status.
- Sophos solutions are engineered to automatically take actions based on a device’s Security Heartbeat status.
By enabling Sophos solutions to work together, Synchronized Security and the Security Heartbeat capability reduce response time from minutes or hours to just seconds. They also extend the powerful risk reduction capabilities provided by individual Sophos solutions with an additional defense layer only available when security solutions work together.
And it’s free. Synchronized Security is included and enabled automatically at no extra charge for all Sophos customers.
Enabling a coordinated, automated response to threats
Step 1: Detect. If Sophos Endpoint detects a threat on a user’s device, it automatically changes the device’s Security Heartbeat status to Red and shares the new health status with the wider ecosystem.
Step 2: Isolate. Sophos Firewall and Sophos ZTNA immediately limit the Red status device’s access to network resources and applications, preventing data loss. Sophos Firewall can also block traffic from the compromised device to all healthy (Green status) endpoints on the network – including those on the same switch – eliminating the possibility of lateral movement even within the same LAN segment.
Step 3: Restore. Once the affected device is cleaned up, Sophos Endpoint automatically changes the Security Heartbeat status to Green, which instantly triggers Sophos Firewall and Sophos ZTNA to re-enable access.
What about middle-of-the-night attacks?
Synchronized Security is a powerful tool at any time of the day or night, but is particularly helpful outside standard working hours, when in-house resource availability is often reduced. With 88% of ransomware incidents starting during evenings, nights, and weekends, it’s also prime time for adversaries to launch an attack.
So, what happens if an attacker hacks into one of your servers late on a Friday? In a non-Sophos-protected environment, the adversary will have full access to the network over the entire weekend – giving them ample time to exfiltrate data, install backdoors, and deploy ransomware.
But in a Sophos-protected organization, any malicious activity detected on the server by Sophos Endpoint automatically triggers a Red Security Heartbeat health status, causing Sophos Firewall to effectively cut off the server from the rest of the network until it can be cleaned up – without anyone having to do anything.
Once the compromised server has been cleaned up, Sophos Endpoint will return its Security Heartbeat to Green, and full system access and connectivity will be restored automatically.
More than threat response
In addition to automatically responding to threats, Synchronized Security can share application information between Sophos Endpoint and Sophos Firewall. This enables Sophos Firewall to route, prioritize, or block application traffic it might not otherwise be able to identify.
For example, if you have a custom application that needs prioritization, most firewalls won’t recognize it and leave it at the mercy of all the other traffic on your network. With Sophos Firewall and Sophos Endpoint working together, traffic from your custom app can be easily identified and prioritized.
Sophos Endpoint can also share authenticated user information with Sophos Firewall to simplify user-based policy enforcement.
And it doesn’t stop there. For example, if a compromised device starts sending spam or phishing emails, it will trigger a Red health status, causing Sophos Email to automatically block messages before they reach users.
Another great example of Synchronized Security in action is Active Threat Response, which extends Synchronized Security to security operations teams. With Active Threat Response, an analyst working for Sophos as part of our MDR service, or your own analysts working with Sophos XDR, can trigger a Synchronized Security response using the new threat feed capability built into Sophos Firewall. Synchronized Security then acts on this information to identify any compromised host on the network and isolate it automatically until it can be cleaned up. Active Threat Response is also available for Sophos switches and AP6 access points.
The latest addition: Sophos Workspace Protection
Sophos Workspace Protection is an integrated bundle of security solutions that protects apps, data, workers, and guests easily and affordably – wherever they are. It includes Sophos ZTNA, which now supports Security Heartbeat, enabling you to automatically prevent compromised devices from connecting to important networked applications and data. This unique, automated threat response capability greatly limits the ability of a compromised device belonging to a remote worker from becoming an entry point for an attacker to the broader network.
Synchronized Security and Security Heartbeat are key reasons why Sophos ZTNA is a critically important security solution for remote access. Traditional VPN solutions have no way of knowing if a device has been breached and will allow any compromised device full access to the network. Sophos ZTNA, on the other hand, not only enforces multi-factor authentication to prevent breaches from compromised credentials, it also includes Synchronized Security to prevent devices from connecting when in a compromised state.
How to get Synchronized Security
Security Heartbeat is automatically included with Sophos Firewall, Sophos Endpoint, Sophos Email, Sophos Mobile, and now Sophos Workspace Protection. No extra products or solutions are required, no additional subscriptions to purchase.
Sophos Central takes care of all the data sharing. You simply need to set up the Security Heartbeat conditions in your policies to take advantage of it. It’s that easy. It’s one of the reasons many customers choose Sophos for their cybersecurity – you won’t find this anywhere else.
Source: Sophos
We’re excited to announce the latest addition to the Sophos portfolio: Sophos Workspace Protection. It’s an easy, effective, and affordable way to protect remote and hybrid workers, contractors and guests – and the networks and data they access – from threats, breaches, and shadow IT, and provide consistent policy enforcement on and off the network.
The challenge – Why Sophos Workspace Protection?
The traditional network perimeter has been disappearing in recent years, with applications, data, and users everywhere. This shift has made protecting remote and hybrid workers a significant challenge for IT teams.
In response, cloud-delivered network security solutions like Secure Web Gateways (SWG), Cloud Access Security Brokers (CASB), and cloud firewalls – often collectively known as SASE or SSE solutions – have emerged to try and solve this issue. However, these solutions come with their own set of challenges related to back-hauling and encrypted traffic, latency, and cost effectiveness that have made them unworkable options for many smaller and mid-sized organizations.
At the same time, many organizations are grappling with both shadow IT and the need to safely adopt and integrate generative AI technology and services into their workflows without exposing proprietary information or sensitive data. There’s been no easy way to solve these issues, particularly with a remote or hybrid workforce.
Most organizations have been waiting for a better way.
A better solution: Sophos Workspace Protection
Sophos Workspace Protection provides a unique and elegant solution to the challenge of protecting remote and hybrid workers. It integrates all the network security components needed to secure apps, data, workers, and guests – wherever they are – into a single easy-to-use and familiar app: a hardened Chromium browser.
Sophos Workspace Protection includes:
- Sophos Protected Browser – a new secure Chromium web browser powered by Island.io that provides several security features, including control over app usage, local data controls, and web filtering, and that is hardened against exploits and attacks. It also integrates Sophos ZTNA for access to web apps and rich SSH and RDP support.
- Sophos ZTNA – now integrated into Sophos Protected Browser, it can be used agentless or with a thin agent as before. It also works with Sophos Endpoint to provide device posture assessment and Synchronized Security Heartbeat to define device health as part of access policies. Existing Sophos ZTNA customers will automatically get access to the full Sophos Workspace Protection bundle and all the added benefits it provides.
- Sophos DNS Protection for Endpoints – provides an additional layer of web protection across all apps, ports, and protocols on your remote Windows devices with added visibility, security, and privacy with DNS over HTTPS.
- Email Monitoring System – a Sophos email solution that deploys alongside Google or Microsoft email solutions to monitor email traffic and provide additional insights, analysis, and detections of unwanted or malicious email, including phishing attacks.
Much easier and more affordable than alternatives
Sophos Workspace Protection provides significant advantages over alternative SASE or SSE cloud-delivered solutions, including:
- Affordability: With no expensive cloud infrastructure or traffic management, Sophos Workspace Protection enables you to get more from your security budget.
- Efficiency and performance: There’s no backhauling traffic or man-in-the-middle decryption in the cloud to slow your users down.
- Management overhead: Having a single app to protect all other online apps – private apps, SaaS apps, web apps – reduces day-to-day IT efforts. Plus, it’s simple to add and remove users – including contractors or workers using unmanaged devices.
- Security: Sophos Workspace Protection transforms the browser from a security liability into a key security asset.
- Universality: It works everywhere – on or off the network.
Sophos Workspace Protection is the ultimate solution for remote or hybrid workers – nothing is easier or more affordable.
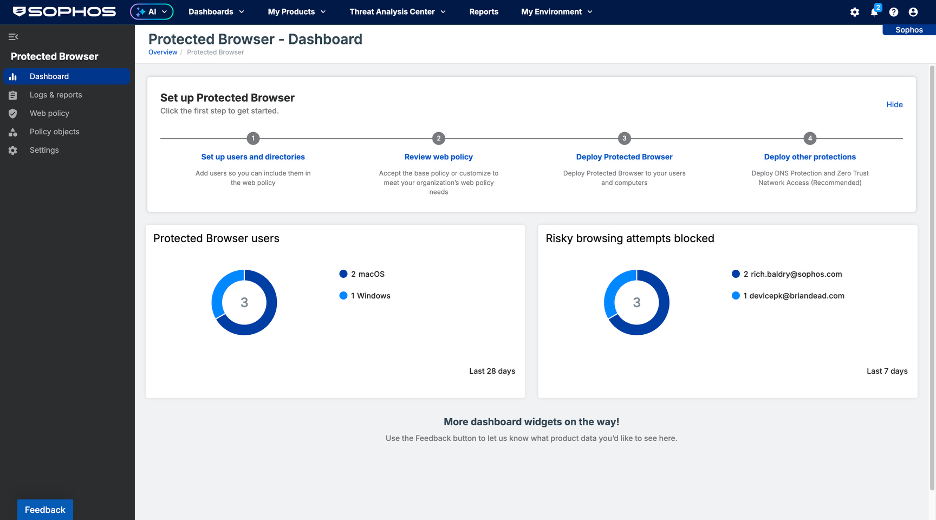
When is it available
Sophos Workspace Protection will be released in late February. If you have a current project, your local Sophos representative can help you get a quote from Sophos today, and Sophos Protected Browser and Sophos DNS Protection for Endpoints are available now in Early Access.
Details:
- Sophos Protected Browser and DNS Protection for Endpoints are available in early access via Sophos Central. If you’re already a Sophos customer, you can simply log into your Sophos Central account to get started. Note, you must have a licensed Sophos product to access the program. Please provide your feedback via the Sophos Community.
- Sophos ZTNA will be included with Sophos Workspace Protection from the general availability date (GA). Existing Sophos ZTNA customers will get full access to the new Workspace Protection bundle capabilities, including Sophos Protected Browser, Sophos DNS Protection for Endpoints, and Sophos Email Monitoring System. If you’re not already a ZTNA customer, you can start a free trial within Sophos Central, or sign up for a free trial Sophos Central account.
- Sophos Email Monitoring System is available now as a free trial in Sophos Central. Sophos customers can activate a trial directly within the Sophos Central console. If you don’t already have a Sophos Central account, get started here.
- A free trial option for Sophos Workspace Protection will be available from GA in late February.
Licensing and purchase options
Sophos Workspace Protection bundles four tightly integrated products into a single high-value bundle licensed on a simple per-user basis.
- Sophos Protected Browser
- Sophos ZTNA
- Sophos DNS Protection for Endpoints
- Sophos Email Monitoring System
The components are modular, allowing you to deploy just what you need.
Sophos Workspace Protection is available on term subscriptions or via monthly MSP Flex, making it an ideal choice for any size of organization.
Sophos customers get even more value
Sophos Workspace Protection is the ideal complement to Sophos Endpoint, Sophos MDR, and Sophos Firewall – extending and unifying these great products and services to remote and hybrid workers everywhere they go. It also extends Synchronized Security Heartbeat to application access policies for users everywhere. To learn more about Synchronized Security, check out this article.
Partnering with Island.io on Sophos Protected Browser
Sophos has partnered with an industry-leading Enterprise Browser vendor, Island.io, to deliver the Sophos Protected Browser in Sophos Workspace Protection. Island has been developing its Enterprise Browser product since 2000 and is widely recognized for its expertise in this space.
With the Sophos Protected Browser, Island provides the core Chromium browser technology and policy enforcement engine in the browser, while Sophos provides the Sophos Central management, logging, and reporting experience, as well as our industry-leading threat intelligence for web and content inspection.
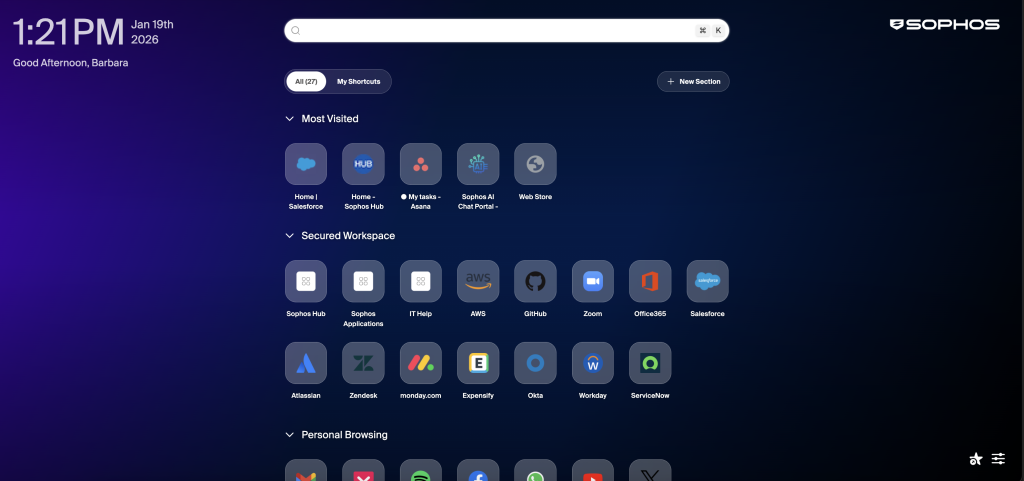
Source: Sophos