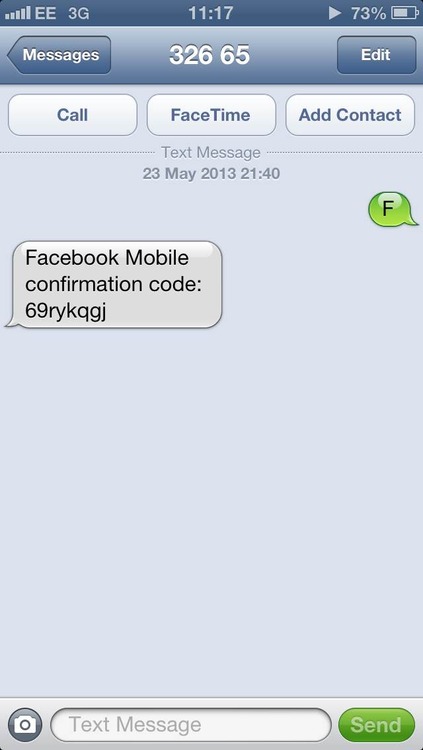
As it is, Whitten explains, Facebook gives users the option of linking their mobile numbers with their accounts. Users then can receive updates via SMS and can also login using their phone number rather than their email address. Whitten found that when sending the letter F to Facebook’s SMS shortcode – which is 32665 in the UK – Facebook returned an 8-character verification code. After submitting the code into the activation box and fiddling with the profile_id form element, Facebook sent Whitten back a _user value that was different from the profile_id that Whitten modified.
Whitten says that trying the exploit might have led to having to reauthorize after submitting the request, but he could do that with his own password instead of trying to guess at his target’s password.

After that point, Facebook was sending an SMS confirmation. From there, Whitten said, an intruder could initiate a password reset request on his targeted user’s account and get the code back, again via SMS. After a reset code is sent via SMS, the account is hijacked, Whitten wrote: We enter this code into the form, choose a new password, and we’re done. The account is ours.

Facebook closed the security hole by no longer accepting the profile_id parameter from users. This could have been a valuable flaw were it to fall into the hands of attackers who might have used it to steal personal data or send out spam. As it is, one commenter on Whitten’s post who obviously didn’t understand the “it’s now fixed” part of the story made the bug’s value clear with his or her eagerness to figure out how to exploit it: ›khalil0777 • a day ago
someone explain me how to exploit it i am realyy need it i wait your helps friends :/
:/ oh well, ›khalil0777, looks like you’re too late for that party.
I’d say better luck next time, but perhaps instead I’ll save my good wishes for Mr. Whitten.
May he enjoy his $20,000.
It was well-earned, and it’s a bargain for Facebook even were the reward to be doubled, considering the grief that could have been caused by such an easy exploit.
Click here to see the original article.